Are you over 18 and want to see adult content?
More Annotations
A complete backup of simplybucharest.ro
Are you over 18 and want to see adult content?
A complete backup of rollrasen-preis.at
Are you over 18 and want to see adult content?
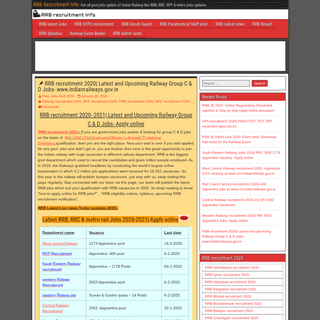
A complete backup of rrbrecruitmentinfo.in
Are you over 18 and want to see adult content?
A complete backup of dark-matter-media.com
Are you over 18 and want to see adult content?
A complete backup of allensnaturally.com
Are you over 18 and want to see adult content?
A complete backup of maisestilosa.com
Are you over 18 and want to see adult content?
A complete backup of lacocinadelentula.wordpress.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://cersilindonesia.wordpress.com/TT-05/
Are you over 18 and want to see adult content?
A complete backup of https://list.shotasekai.net/manga/sparkle-03/
Are you over 18 and want to see adult content?
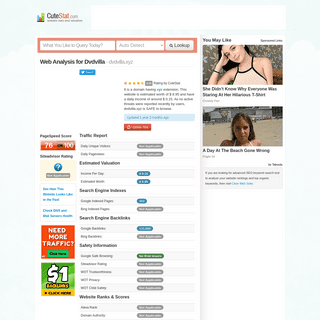
A complete backup of https://dvdvilla.xyz.cutestat.com/
Are you over 18 and want to see adult content?
A complete backup of https://en.wikipedia.org/wiki/Djuras_Ilijic
Are you over 18 and want to see adult content?

A complete backup of https://7strangers.com/
Are you over 18 and want to see adult content?

A complete backup of http://www.ccmixter.org/
Are you over 18 and want to see adult content?

A complete backup of https://www.jet2holidays.com/destinations/turkey
Are you over 18 and want to see adult content?
Text
Science.
BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malwarePUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not) A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEMTHE HACKERS EDC BAG
The Bag. Alright, so, what’s an EDC bag without the bag part?! Personally, I don’t think you need an expensive, super high tech backpackNow, with that said, I prefer the Razer tactical pro backpack ($159.99). It’s got pockets for all your tech, and a main compartment for a laptop with room for more tech. Plus, there’s an underside compartment with a weather proof cover for the bag. HOW TO MAKE A REVERSE TCP BACKDOOR IN PYTHON In our walk in linux, there comes a point where we need to hack ( pentest ) in a safe environment. The first thing we usually do is install Virtualization Softwares and install all the distros our system can take. In stages of hacking, to compromise the victim machine, we need some sort of program to infect the system. The down-side is, AntiVirus products have signatures of favourite0X00SEC.ORG
You are being redirected.0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ 0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware or 0X00SEC - THE HOME OF THE HACKERELFPARTNERSSOCIALPIRATING ILLEGALLYHACKTHEBOX MACHINES FOR BEGINNERS The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malwarePUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not) A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEMTHE HACKERS EDC BAG
The Bag. Alright, so, what’s an EDC bag without the bag part?! Personally, I don’t think you need an expensive, super high tech backpackNow, with that said, I prefer the Razer tactical pro backpack ($159.99). It’s got pockets for all your tech, and a main compartment for a laptop with room for more tech. Plus, there’s an underside compartment with a weather proof cover for the bag. HOW TO MAKE A REVERSE TCP BACKDOOR IN PYTHON In our walk in linux, there comes a point where we need to hack ( pentest ) in a safe environment. The first thing we usually do is install Virtualization Softwares and install all the distros our system can take. In stages of hacking, to compromise the victim machine, we need some sort of program to infect the system. The down-side is, AntiVirus products have signatures of favourite0X00SEC.ORG
You are being redirected.0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ 0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware orPUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not)INTRODUCING AXIOM
Introducing Axiom - The Dynamic Pwnstation Orchestrator Hello, 0x00ers! In this article, I’m going to discuss my new tool Axiom, a few of the concepts around the project, and some potential use cases. I’ve tried to build Axiom to be as extendable as possible so that power users can really use this new tool as an abstraction to use cloud computing systems into their workflows. The CHALLENGE COLLECTION: REVERSE ENGINEERING AND CRACKME Reverse Engineering and Crackme challenges. This topic is an aggregation of Crackme and reverse engineering challenges developed for 0x00sec. Please discuss the challenges in the thread they were originally posted or on IRC in #challenges. This curation is based entirely on my own whim and not a complete aggregation of all RE/Crackme challenges posted on the forum. CHALLENGES - 0X00SEC - THE HOME OF THE HACKER The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
USING URI TO POP SHELLS VIA THE DISCORD CLIENT Introduction Myself and a fellow researcher: Styx were the leads on this research and we were backed up by CyberSecStu, and 5w0rdFish from The Many Hats Club. We discovered a vulnerability within the Discord client that enabled an attacker to call local programs on a target system. We then took this flaw and used it to pivot through MS-Word macros to start a reverse TCP shell automatically PE FILE INFECTION PART II The most common way is to find the PEB of the running executable which can be found at fs:30h, then we can simply find and iterate the list of modules in the process, i.e. we can find the base addresses of kernel32.dll and ntdll.dll. From there, we simply parse the module’s file like any other PE file and iterate the exported functions table MATERIAL FOR LEARNING EXPLOIT DEVELOPMENT When I started studying and learning about exploit development, one of the biggest issues I ran in to was finding a good starting point. I am by no means an expert in this field, but here is a list of some of the material I found helpful while learning (I still am learning and will always be) to research vulnerabilities and develop exploits. I figured I would put this list out there to help THE WOLF: NOTHING IS SAFE Greetings, 0x00sec! After much discussion, the 0x00sec mods and admins have put together a new program, a Bounty Program. How it Works This very post will be a Wiki. A BRIEF INTRODUCTION TO PROXYCHAINS Hello everyone of 0x00! I figured why not make my first contribution, so heres a quick one 🍻 Today, im going to brush the topic of proxies, followed by how to set up ProxyChains to make being tracked a bit harder. So first things first. What is a proxy? In computer networks, a proxy server is a server (a computer system or an application) that acts as an intermediary for requests from A SIMPLE RUNTIME CRYPTER Hey Mates, I think everyone of you has had the dream of building his own crypter; I know I have (for about a year, now). Everyone has heard of this “black magic” (as @dtm mentioned in his post). But, maybe some of you, like me, were unsuccessful in programming one. A crypter in C# is not as useful as one in C++, but that’s besides the point. C++: Complex, but handles the low-level stuff 0X00SEC - THE HOME OF THE HACKERELFPARTNERSSOCIALPIRATING ILLEGALLYHACKTHEBOX MACHINES FOR BEGINNERS The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
PUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not)PE FILE INFECTION
A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEMTHE HACKERS EDC BAG
The Bag. Alright, so, what’s an EDC bag without the bag part?! Personally, I don’t think you need an expensive, super high tech backpackNow, with that said, I prefer the Razer tactical pro backpack ($159.99). It’s got pockets for all your tech, and a main compartment for a laptop with room for more tech. Plus, there’s an underside compartment with a weather proof cover for the bag.0X00SEC.ORG
You are being redirected.0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ ERROR : VOLATILITY.DEBUG : THE REQUESTED FILE DOESN'T This topic was automatically closed after 30 days. New replies are nolonger allowed.
0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware or 0X00SEC - THE HOME OF THE HACKERELFPARTNERSSOCIALPIRATING ILLEGALLYHACKTHEBOX MACHINES FOR BEGINNERS The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
PUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not)PE FILE INFECTION
A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEMTHE HACKERS EDC BAG
The Bag. Alright, so, what’s an EDC bag without the bag part?! Personally, I don’t think you need an expensive, super high tech backpackNow, with that said, I prefer the Razer tactical pro backpack ($159.99). It’s got pockets for all your tech, and a main compartment for a laptop with room for more tech. Plus, there’s an underside compartment with a weather proof cover for the bag.0X00SEC.ORG
You are being redirected.0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ ERROR : VOLATILITY.DEBUG : THE REQUESTED FILE DOESN'T This topic was automatically closed after 30 days. New replies are nolonger allowed.
0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware or REVERSE ENGINEERING 101 Continuing the discussion from Cracking Your First Program: As requested by @pry0cc, this is a crash course on reverse engineering. Before reading this, you should try to solve @dtm challenge: If you didn’t manage or you want to see somebody else solution keep reading. Our Target I will start writing our target program. You can try what is described in this paper againstPUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not) BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malware CHALLENGES - 0X00SEC - THE HOME OF THE HACKER The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
THE WOLF: NOTHING IS SAFE Greetings, 0x00sec! After much discussion, the 0x00sec mods and admins have put together a new program, a Bounty Program. How it Works This very post will be a Wiki. PE FILE INFECTION PART II The most common way is to find the PEB of the running executable which can be found at fs:30h, then we can simply find and iterate the list of modules in the process, i.e. we can find the base addresses of kernel32.dll and ntdll.dll. From there, we simply parse the module’s file like any other PE file and iterate the exported functions table MY HACKTHEBOX CTF METHODOLOGY If your credentials are successful, you will be dropped into an interactive prompt similar to that of FTP and you’ll be able to navigate files and download files. You can also use the SMB script that comes with nmap, nmap -p445 -sV --script smb-enum-services USING URI TO POP SHELLS VIA THE DISCORD CLIENT Introduction Myself and a fellow researcher: Styx were the leads on this research and we were backed up by CyberSecStu, and 5w0rdFish from The Many Hats Club. We discovered a vulnerability within the Discord client that enabled an attacker to call local programs on a target system. We then took this flaw and used it to pivot through MS-Word macros to start a reverse TCP shell automatically CONFUSED ABOUT MALWARE DEVELOPMENT Hi folks I been confused lately about malware development, I am familiar with python and use it for web development however I know that it’s not the right language for malware development. The reason that I picked python at first place was because I was told “It’s a general purpose programming language & you can do anything with it”. The moment I became an intermediate programmer, I0X00SEC.ORG
You are being redirected. 0X00SEC - THE HOME OF THE HACKERELFPARTNERSSOCIALPIRATING ILLEGALLYHACKTHEBOX MACHINES FOR BEGINNERS The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malwarePUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not)PE FILE INFECTION
A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEM PE FILE INFECTION PART II The most common way is to find the PEB of the running executable which can be found at fs:30h, then we can simply find and iterate the list of modules in the process, i.e. we can find the base addresses of kernel32.dll and ntdll.dll. From there, we simply parse the module’s file like any other PE file and iterate the exported functions table0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ ERROR : VOLATILITY.DEBUG : THE REQUESTED FILE DOESN'T This topic was automatically closed after 30 days. New replies are nolonger allowed.
0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware or 0X00SEC - THE HOME OF THE HACKERELFPARTNERSSOCIALPIRATING ILLEGALLYHACKTHEBOX MACHINES FOR BEGINNERS The Home of the Hacker - Malware, Reverse Engineering, and ComputerScience.
BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malwarePUBLIC DISCORD
pry0cc (Leader & Offsec Engineer & Forum Daddy) pinned globally September 3, 2019, 8:42pm #2. BL4CKH47H4CK3R September 3, 2019, 9:26pm #3. If possible open a Telegram Chatting Group. Because most of the people like us are now using Telegram. Confused about https://t (dot) me/ir0x00sec (Official/Not)PE FILE INFECTION
A BLUE TEAM GUIDE TO AZURE & OFFICE 365 MONITORING A few weeks ago I thought that 0x00sec didn’t have enough Blue Team focused posts. Yet, detection of potential threats is incredibly important in any organization. Because Azure and Office 365 are widely used, I decided to start with this. I hope you will find it useful because unfortunately, there is a lack of good resources other than Microsoft when it comes to monitoring Azure with a SIEM PE FILE INFECTION PART II The most common way is to find the PEB of the running executable which can be found at fs:30h, then we can simply find and iterate the list of modules in the process, i.e. we can find the base addresses of kernel32.dll and ntdll.dll. From there, we simply parse the module’s file like any other PE file and iterate the exported functions table0X00SEC INIT
$ cat /home/0x00sec/partners.txt ### Partners Hackthebox - https://hackthebox.eu/ pwnDefend - https://www.pwndefend.com/ Binary Ninja - https://binary.ninja/ $ pwd0X00SEC INIT
$ pwd /home/0x00sec/ $ ls forum.txt partners.txt $ ERROR : VOLATILITY.DEBUG : THE REQUESTED FILE DOESN'T This topic was automatically closed after 30 days. New replies are nolonger allowed.
0X00SEC - THE HOME OF THE HACKER - LATEST TOPICS Like on windows there are exe (compiled from python, C or C++ assembly), VBS, bat extensions to name a few that can be dangerous. But if Linux malware was to be made that could spread or do damage what would be its source extension? and this very question is why Linux has little malware or 0X00SEC - THE HOME OF THE HACKER hacking. 2. 1926. April 6, 2021. Threat Hunting and Mitigation in *Nix/macOS Environments. (Please comment and tell me what I'm missing. This is initial work) Linux. linux , hacking , malware. REFLECTIVE DLL INJECTION Reflective DLL Injection Process. Here is a brief summary of the stages that will be undergone to map a DLL into an external process: The DLL payload must be retrieved, The DLL must then be mapped into memory, After mapping it to memory, its import table must be rebuilt, The base relocation table must be parsed to fix addresses due to the BEST LANGUAGE FOR WRITE MALWARE n33ds0n (n33ds0n) April 5, 2021, 6:05pm #5. There is no best language for writing malware you can use any computer programming language to write malware. But most malware coder go with compile language such as C/C++ golang, C# and more but malware can also be written in scripting language like python, ruby and JavaScript infact lots of malware THE WOLF: NOTHING IS SAFE Greetings, 0x00sec! After much discussion, the 0x00sec mods and admins have put together a new program, a Bounty Program. How it Works This very post will be a Wiki. MY HACKTHEBOX CTF METHODOLOGY If your credentials are successful, you will be dropped into an interactive prompt similar to that of FTP and you’ll be able to navigate files and download files. You can also use the SMB script that comes with nmap, nmap -p445 -sV --script smb-enum-services A COMPLETE BEGINNER FRIENDLY GUIDE TO THE DIGISPARK BADUSB The thesis I presented for my diploma was about physical security, with BadUSB devices taking the most amount of pages. I saw there’s already a pretty good post on how to make your own BadUSB starting from a vulnerable stick (click) but I’d like to make another contribution in the same subject by presenting a complete guide on how to use a very cheap programmable microcontroller HOW TO MAKE A REVERSE TCP BACKDOOR IN PYTHON In our walk in linux, there comes a point where we need to hack ( pentest ) in a safe environment. The first thing we usually do is install Virtualization Softwares and install all the distros our system can take. In stages of hacking, to compromise the victim machine, we need some sort of program to infect the system. The down-side is, AntiVirus products have signatures of favourite USING URI TO POP SHELLS VIA THE DISCORD CLIENT Introduction Myself and a fellow researcher: Styx were the leads on this research and we were backed up by CyberSecStu, and 5w0rdFish from The Many Hats Club. We discovered a vulnerability within the Discord client that enabled an attacker to call local programs on a target system. We then took this flaw and used it to pivot through MS-Word macros to start a reverse TCP shell automaticallyTHE HACKERS EDC BAG
The Bag. Alright, so, what’s an EDC bag without the bag part?! Personally, I don’t think you need an expensive, super high tech backpackNow, with that said, I prefer the Razer tactical pro backpack ($159.99). It’s got pockets for all your tech, and a main compartment for a laptop with room for more tech. Plus, there’s an underside compartment with a weather proof cover for the bag. SELF-DESTRUCTING PYTHON SCRIPT Self-Destructing Python Script. Programming. python. EnergyWolf August 9, 2016, 7:37pm #1. This is short, and hopefully not completely uninteresting etc. I just wanted to be able to do this, and thought it would be pretty neat. The self-destruction of the file is achieved by it securely deleting itself.Init Partners
Sign UpLog In
*
*
*
all categories
*
all tags
* Latest
* Top
* Categories
*
TOPIC
REPLIES
VIEWS
ACTIVITY
Public Discord - Again (Late 2019 Update) 0x00sec Announcementsirc discord
Hey 0x00ers! So we have discussed it and we have decided to make the 0x00sec Discord now public. You can join here https://discord.gg/c6BHVfn Looking forward to chatting with all ofyou!
13
4.1k
18d
Cyborg Builder Ransomware V2.0.1 By Cyber SpLiTTerMalware
malware
0
55
4h
(Better) USB Injection with RawcoonHardware
injection badusb pentesting0
73
4h
Exploit CVE-2019-0211 apache 2.4.25 privilege escalationLinux
4
176
8h
Hackarmy Backdoor Client - Denial of ServiceExploit Development
malware
2
907
8h
I have awoken from my deep lairUncategorized
0
213
17h
Random Thoughts After Nearly 9 years Pentesting/Red Teaming: 2019Pentesting
hacking
12
8.7k
3d
Tricks of the Trade from 5+ years in Offensive Cyber SecurityPentesting
vagrant docker osinttricks zsh
14
8.0k
6d
Surfing the V01D
Anonymity
linux hacking
7
1.4k
7d
Monitoring what users does in their appsPhone Hacking
4
1.2k
8d
OSINT / OPSec: First Lessons (My Way)Reconnaissance
recon opsecbro osint5
1.1k
9d
Python adventures 01Challenges
8
3.8k
9d
Tips / Commands / HackingPentesting
1
3.2k
11d
Cyber Security AwarenessAnonymity
hacking
1
1.1k
12d
My HackTheBox CTF Methodology - From fresh box to root!CTF
ctf root methodologyhackthebox
20
26.2k
12d
Reversing HackEx - An android gameReverse Engineering
android
14
12.9k
13d
HackTheBox Machines for beginnersBeginner Guides
hacking hackthebox
9
3.2k
14d
CrackMe Challenge - Introduction / Very Easy PasswordMechanism (Python)
Challenges
27
8.1k
22d
CrackMe Challenge - Hardcoded Password (C#)Challenges
11
6.2k
22d
ReversingHero: Learn Reverse Engineering (x64)Reverse Engineering
challenge reverseengineering3
2.3k
23d
Explaining Server Side Template InjectionsWeb Hacking
ctf web python hacking3
4.9k
24d
Conference Meetups
Social
networking
22
5.9k
26d
Disinformation demystifiedSocial Engineering
6
1.7k
28d
Virtual-reality project - grand-theft-socket payloadProgramming
4
1.8k
29d
Orchestration
Operations
docker
0
1.1k
Sep 11
Docker Certified AssociateOperations
docker
0
1.3k
Sep 11
Con, anyone?
Social
1
1.2k
Sep 11
CrackMe #1
Challenges
5
5.6k
Sep 9
HackTheBox Writeup: BastionHackthebox Writeups
3
1.8k
Sep 8
My CrackMe solving
Challenges
1
1.5k
Sep 5
Invalid date Invalid dateDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0