Are you over 18 and want to see adult content?
More Annotations

A complete backup of belteriajtobirodalom.hu
Are you over 18 and want to see adult content?
A complete backup of onslowcountyschools-my.sharepoint.com
Are you over 18 and want to see adult content?
A complete backup of newstitchaday.com
Are you over 18 and want to see adult content?
A complete backup of hochzeit-ruswedding.de
Are you over 18 and want to see adult content?
A complete backup of azdoberescue.org
Are you over 18 and want to see adult content?
A complete backup of owthare.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of educacionecuadorministerio.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of openground.com.au
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://smash.com
Are you over 18 and want to see adult content?

A complete backup of https://financeals.com
Are you over 18 and want to see adult content?
A complete backup of https://gamereactor.eu
Are you over 18 and want to see adult content?
A complete backup of https://drmusayeva.com
Are you over 18 and want to see adult content?

A complete backup of https://iplogger.org
Are you over 18 and want to see adult content?

A complete backup of https://skantrae.com
Are you over 18 and want to see adult content?

A complete backup of https://blackandred.es
Are you over 18 and want to see adult content?
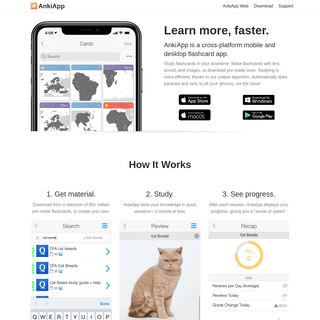
A complete backup of https://ankiapp.com
Are you over 18 and want to see adult content?

A complete backup of https://carisinyal.com
Are you over 18 and want to see adult content?
A complete backup of https://southerncurlsandpearls.com
Are you over 18 and want to see adult content?
A complete backup of https://practicallyhomemade.com
Are you over 18 and want to see adult content?

A complete backup of https://digikey.ch
Are you over 18 and want to see adult content?
Text
receiving computer.
HOW TO CONFIGURE NTP IN CISCO ROUTER This tutorial explains how to configure NTP Server and NTP Client in Cisco Router step by step with practical example. Learn basic concepts of NTP such as what NTP is, how NTP works, NTP stratum levels, meaning of synchronized and un-synchronized NTP clock in detail. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED What is the neighbor discovery? Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES Click the Services menu icon and click the DHCP Service in the left pane and select the on option in the right pane. Set the value in the DHCP Pool Options and click the Add button. The following image shows this procedure. Configure DHCP clients. To configure PCs as DHCP clients, click the PC and click the IP configuration option from the Desktop menu item and select the DHCP option. CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH This tutorial is the fifth part of the article 'DHCP (Dynamic Host Configuration Protocol) basic concepts, configurations, functions, and options Explained'. Other parts of this tutorial are the following. What DHCP is and Types of DHCP Explained How DHCP works explained withexamples
HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. IP ADDRESS, NETWORK ADDRESS, AND HOST ADDRESS EXPLAINED To separate network addresses from host addresses, IPv4 uses an additional component with IP addresses. This component is known as a subnet mask.In other words, in an IP address, how many bits are used in the network address and how many bits are left for the host address is determined by the subnet mask. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED The following image explains the data encapsulation and de-encapsulation process. The header and trailer added by a layer on the sending computer can only be removed by the peer layer on thereceiving computer.
HOW TO CONFIGURE NTP IN CISCO ROUTER This tutorial explains how to configure NTP Server and NTP Client in Cisco Router step by step with practical example. Learn basic concepts of NTP such as what NTP is, how NTP works, NTP stratum levels, meaning of synchronized and un-synchronized NTP clock in detail. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED What is the neighbor discovery? Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES Click the Services menu icon and click the DHCP Service in the left pane and select the on option in the right pane. Set the value in the DHCP Pool Options and click the Add button. The following image shows this procedure. Configure DHCP clients. To configure PCs as DHCP clients, click the PC and click the IP configuration option from the Desktop menu item and select the DHCP option. CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH This tutorial is the fifth part of the article 'DHCP (Dynamic Host Configuration Protocol) basic concepts, configurations, functions, and options Explained'. Other parts of this tutorial are the following. What DHCP is and Types of DHCP Explained How DHCP works explained withexamples
HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. CLIENT-SERVER NETWORKS MODEL EXPLAINED The peer-to-peer network model stores user accounts and passwords on the local system. The client-server network model stores user accounts and passwords on a centralized database that can be installed on a single system or a group of systems. IP ADDRESS, NETWORK ADDRESS, AND HOST ADDRESS EXPLAINED To separate network addresses from host addresses, IPv4 uses an additional component with IP addresses. This component is known as a subnet mask.In other words, in an IP address, how many bits are used in the network address and how many bits are left for the host address is determined by the subnet mask. VLAN CONFIGURATION COMMANDS STEP BY STEP EXPLAINED This tutorial explains how to create and assign VLAN, VLAN Membership (Static and Dynamic), Router on Stick and Spanning Tree Protocol (STP) in detail with practical examples in packet tracer. Learn how to create and manage VLAN in Cisco switch step by step. TAR COMMAND COMPRESS AND EXTRACT ARCHIVES To instruct the tar command to use the gzip utility to compress files before adding them to the archive, use the option g with the options cvf.To indicate that the gzip compression is used, use the extension .gz with the archive file name.. To create and compress the archive file with the bzip2 utility, use the option j with options cvf and use the file extension .bz2 with the archive file name. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. PERMANENTLY AND SECURELY DELETE FILES IN LINUX Here are some important options to use with shred command.-f:- Perform delete and overwrite operation forcefully.-v:- Display operation’s progress.-z:- Add a final overwrite with zeros to hide the act of shredding.-n:- Perform overwrite operation number of times specified with this option.-u:- Delete file/partition/drive after overwriting.. For a complete list of options with other details HOW TO CONFIGURE DHCP SERVER ON CISCO ROUTERS Router>enable Router#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Router(config)#ip dhcp excluded-address 192.168.1.0 192.168.1.10 Router(config)#ip dhcp pool Left_Network Router(dhcp-config)#default-router 192.168.1.1 Router(dhcp-config)#dns-server 192.168.1.2 Router(dhcp-config)#option 150 ip 192.168.1.3 Router(dhcp-config)#network 192.168.1.0 COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALSFIREWALLD RICH RULES EXPLAINED WITH EXAMPLESLINUX TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IP ROUTE COMMAND EXPLAINED WITH EXAMPLES This tutorial explains IP route command and its parameter, argument and options in detail with examples. Learn how to configure default route and static route with IP route command in Cisco router step by step with practical example in packet tracer. VLAN CONFIGURATION COMMANDS STEP BY STEP EXPLAINED This tutorial explains how to create and assign VLAN, VLAN Membership (Static and Dynamic), Router on Stick and Spanning Tree Protocol (STP) in detail with practical examples in packet tracer. Learn how to create and manage VLAN in Cisco switch step by step. PPP PROTOCOL AND ENCAPSULATION METHOD EXPLAINED PAP (Password Authentication Protocol) In this protocol, password is sent in clear text format that makes it less secure in comparison with CHAP. PAP authentication is a two steps process. In step one, Router that want to be authenticate will send its CISCO ROUTER SHOW COMMAND EXPLAINED WITH EXAMPLES Cisco Router Show Command Explained with Examples. This tutorial explains basic show commands (such as show ip route, show ip interfaces brief, show version, show flash, show running-config, show startup-config, show controllers, etc.) in Cisco router with examples. Learn how to use show commands in Cisco router to get specificinformation.
HOW TO CONFIGURE DHCP RELAY AGENT ON CISCO ROUTERS The 'ip helper-address' command tells the interface to forward the incoming DHCP message to the configured DHCP server. Use this command on all interfaces that are connected to the local subnets containing DHCP clients. Before we take a practical example to understand how to use this command to configure a router's interface as the DHCP relay agent, I assume that you know how a COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALSFIREWALLD RICH RULES EXPLAINED WITH EXAMPLESLINUX TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IP ROUTE COMMAND EXPLAINED WITH EXAMPLES This tutorial explains IP route command and its parameter, argument and options in detail with examples. Learn how to configure default route and static route with IP route command in Cisco router step by step with practical example in packet tracer. VLAN CONFIGURATION COMMANDS STEP BY STEP EXPLAINED This tutorial explains how to create and assign VLAN, VLAN Membership (Static and Dynamic), Router on Stick and Spanning Tree Protocol (STP) in detail with practical examples in packet tracer. Learn how to create and manage VLAN in Cisco switch step by step. PPP PROTOCOL AND ENCAPSULATION METHOD EXPLAINED PAP (Password Authentication Protocol) In this protocol, password is sent in clear text format that makes it less secure in comparison with CHAP. PAP authentication is a two steps process. In step one, Router that want to be authenticate will send its CISCO ROUTER SHOW COMMAND EXPLAINED WITH EXAMPLES Cisco Router Show Command Explained with Examples. This tutorial explains basic show commands (such as show ip route, show ip interfaces brief, show version, show flash, show running-config, show startup-config, show controllers, etc.) in Cisco router with examples. Learn how to use show commands in Cisco router to get specificinformation.
HOW TO CONFIGURE DHCP RELAY AGENT ON CISCO ROUTERS The 'ip helper-address' command tells the interface to forward the incoming DHCP message to the configured DHCP server. Use this command on all interfaces that are connected to the local subnets containing DHCP clients. Before we take a practical example to understand how to use this command to configure a router's interface as the DHCP relay agent, I assume that you know how a COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
HOT STANDBY ROUTER PROTOCOL EXPLAINED What is the HSRP? A default gateway router connects a network's local subnet to a remote subnet of the same network or another network. For backup, if an administrator wants to configure more than one default gateway router, the administrator needs to configure an FHRP protocol. ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. MAC ADDRESSES EXPLAINED WITH EXAMPLES Let’s understand this with an example. Suppose in a network three PCs; PC-A (11000ABB28FC), PC-B (00000ABB28FC) and PC-C (00000ABB28FC) are connected through a switch. NICs of PC-B and PC-C have the same MAC address 00000ABB28FC. If PC-A sends a frame to the destination MAC address 00000ABB28FC, the switch fails to deliver this frame as it STRAIGHT THROUGH AND CROSS OVER CABLE It receives data on pins 1 and 2 and transmits data from the pin 3 and 6. Based on the type of end devices, a UTP cable can be made in two ways. The first type of cable, known as the straight-through cable, connects two different types of end devices; such as PC to Switch. The second type of cable, known as the cross-over cable, connects two SHUTDOWN, REBOOT, SUSPEND AND HIBERNATE A LINUX SYSTEM The shutdown command accepts time in two formats; hh:mm and +mm where hh:mm is the time in 24 hours format and +mm the delay time in minutes. Advanced power management options. These options save the running state of the system and use the saved state to start thesystem again.
HOW TO CONFIGURE DEFAULT ROUTING IN CISCO ROUTERS Default routing practice LAB. To configure a default route from all four remote sites (RS1, RS2, RS3, and RS4) use the following global configuration command. Router (config)#ip route 0.0.0.0 0.0.0.0 If you want to use the exit-interface in the configuration, specify the name of the localinterface
CISCO IOS MODE EXPLAINED WITH EXAMPLES An IOS mode is a group of commands that are used to configure similar features or to control a particular area of the device. An IOS mode is also known as the IOS access mode or the IOS commands mode. There are five IOS modes: - user EXEC mode, privileged EXEC mode, global configuration mode, setup mode, and ROM Monitor mode. COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALSFIREWALLD RICH RULES EXPLAINED WITH EXAMPLESLINUX TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IP ROUTE COMMAND EXPLAINED WITH EXAMPLES This tutorial explains IP route command and its parameter, argument and options in detail with examples. Learn how to configure default route and static route with IP route command in Cisco router step by step with practical example in packet tracer. VLAN CONFIGURATION COMMANDS STEP BY STEP EXPLAINED This tutorial explains how to create and assign VLAN, VLAN Membership (Static and Dynamic), Router on Stick and Spanning Tree Protocol (STP) in detail with practical examples in packet tracer. Learn how to create and manage VLAN in Cisco switch step by step. PPP PROTOCOL AND ENCAPSULATION METHOD EXPLAINED PAP (Password Authentication Protocol) In this protocol, password is sent in clear text format that makes it less secure in comparison with CHAP. PAP authentication is a two steps process. In step one, Router that want to be authenticate will send its CISCO ROUTER SHOW COMMAND EXPLAINED WITH EXAMPLES Cisco Router Show Command Explained with Examples. This tutorial explains basic show commands (such as show ip route, show ip interfaces brief, show version, show flash, show running-config, show startup-config, show controllers, etc.) in Cisco router with examples. Learn how to use show commands in Cisco router to get specificinformation.
HOW TO CONFIGURE DHCP RELAY AGENT ON CISCO ROUTERS The 'ip helper-address' command tells the interface to forward the incoming DHCP message to the configured DHCP server. Use this command on all interfaces that are connected to the local subnets containing DHCP clients. Before we take a practical example to understand how to use this command to configure a router's interface as the DHCP relay agent, I assume that you know how a COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALSFIREWALLD RICH RULES EXPLAINED WITH EXAMPLESLINUX TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options IP ROUTE COMMAND EXPLAINED WITH EXAMPLES This tutorial explains IP route command and its parameter, argument and options in detail with examples. Learn how to configure default route and static route with IP route command in Cisco router step by step with practical example in packet tracer. VLAN CONFIGURATION COMMANDS STEP BY STEP EXPLAINED This tutorial explains how to create and assign VLAN, VLAN Membership (Static and Dynamic), Router on Stick and Spanning Tree Protocol (STP) in detail with practical examples in packet tracer. Learn how to create and manage VLAN in Cisco switch step by step. PPP PROTOCOL AND ENCAPSULATION METHOD EXPLAINED PAP (Password Authentication Protocol) In this protocol, password is sent in clear text format that makes it less secure in comparison with CHAP. PAP authentication is a two steps process. In step one, Router that want to be authenticate will send its CISCO ROUTER SHOW COMMAND EXPLAINED WITH EXAMPLES Cisco Router Show Command Explained with Examples. This tutorial explains basic show commands (such as show ip route, show ip interfaces brief, show version, show flash, show running-config, show startup-config, show controllers, etc.) in Cisco router with examples. Learn how to use show commands in Cisco router to get specificinformation.
HOW TO CONFIGURE DHCP RELAY AGENT ON CISCO ROUTERS The 'ip helper-address' command tells the interface to forward the incoming DHCP message to the configured DHCP server. Use this command on all interfaces that are connected to the local subnets containing DHCP clients. Before we take a practical example to understand how to use this command to configure a router's interface as the DHCP relay agent, I assume that you know how a COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. ACCESS, DISTRIBUTION, AND CORE LAYERS EXPLAINED The Cisco three-layer hierarchical model contains three layers: core, distribution, and access. The core layer is the backbone of the network. It provides a high-speed connection between different distribution layer devices. The distribution layer connects the access layer to the core layer. The access layer provides initial connectionsto end
HOT STANDBY ROUTER PROTOCOL EXPLAINED What is the HSRP? A default gateway router connects a network's local subnet to a remote subnet of the same network or another network. For backup, if an administrator wants to configure more than one default gateway router, the administrator needs to configure an FHRP protocol. ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. MAC ADDRESSES EXPLAINED WITH EXAMPLES Let’s understand this with an example. Suppose in a network three PCs; PC-A (11000ABB28FC), PC-B (00000ABB28FC) and PC-C (00000ABB28FC) are connected through a switch. NICs of PC-B and PC-C have the same MAC address 00000ABB28FC. If PC-A sends a frame to the destination MAC address 00000ABB28FC, the switch fails to deliver this frame as it STRAIGHT THROUGH AND CROSS OVER CABLE It receives data on pins 1 and 2 and transmits data from the pin 3 and 6. Based on the type of end devices, a UTP cable can be made in two ways. The first type of cable, known as the straight-through cable, connects two different types of end devices; such as PC to Switch. The second type of cable, known as the cross-over cable, connects two SHUTDOWN, REBOOT, SUSPEND AND HIBERNATE A LINUX SYSTEM The shutdown command accepts time in two formats; hh:mm and +mm where hh:mm is the time in 24 hours format and +mm the delay time in minutes. Advanced power management options. These options save the running state of the system and use the saved state to start thesystem again.
HOW TO CONFIGURE DEFAULT ROUTING IN CISCO ROUTERS Default routing practice LAB. To configure a default route from all four remote sites (RS1, RS2, RS3, and RS4) use the following global configuration command. Router (config)#ip route 0.0.0.0 0.0.0.0 If you want to use the exit-interface in the configuration, specify the name of the localinterface
CISCO IOS MODE EXPLAINED WITH EXAMPLES An IOS mode is a group of commands that are used to configure similar features or to control a particular area of the device. An IOS mode is also known as the IOS access mode or the IOS commands mode. There are five IOS modes: - user EXEC mode, privileged EXEC mode, global configuration mode, setup mode, and ROM Monitor mode. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. HOT STANDBY ROUTER PROTOCOL EXPLAINED What is the HSRP? A default gateway router connects a network's local subnet to a remote subnet of the same network or another network. For backup, if an administrator wants to configure more than one default gateway router, the administrator needs to configure an FHRP protocol. CLIENT-SERVER NETWORKS MODEL EXPLAINED The client-server network model stores user accounts and passwords on a centralized database that can be installed on a single system or a group of systems. If a device accesses a service and presents a platform to use the accessed service, the device is known as theclient.
DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. WHAT DHCP IS AND TYPES OF DHCP EXPLAINED This tutorial explains DHCP and its types in detail. Learn what the DHCP is and what are the advantages and disadvantages of having a DHCP server in the network. Each device in an IP network requires a valid IP configuration. If the network size is small, an administrator can manually provide an IP configuration to each device. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. HOT STANDBY ROUTER PROTOCOL EXPLAINED What is the HSRP? A default gateway router connects a network's local subnet to a remote subnet of the same network or another network. For backup, if an administrator wants to configure more than one default gateway router, the administrator needs to configure an FHRP protocol. CLIENT-SERVER NETWORKS MODEL EXPLAINED The client-server network model stores user accounts and passwords on a centralized database that can be installed on a single system or a group of systems. If a device accesses a service and presents a platform to use the accessed service, the device is known as theclient.
DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. WHAT DHCP IS AND TYPES OF DHCP EXPLAINED This tutorial explains DHCP and its types in detail. Learn what the DHCP is and what are the advantages and disadvantages of having a DHCP server in the network. Each device in an IP network requires a valid IP configuration. If the network size is small, an administrator can manually provide an IP configuration to each device. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options EXTENDED ACL CONFIGURATION COMMANDS EXPLAINEDSEE MORE ON COMPUTERNETWORKINGNOTES.COM DIFFERENCE BETWEEN LINUX DISTRIBUTIONS The first major difference between various Linux distributions is their target audiences and systems. For example, some distributions are customized for desktop systems, some distributions are customized for server systems, and some distributions are customized for old machines, and so on. IPV6 NEIGHBOR DISCOVERY PROTOCOL EXPLAINED Neighbor Discovery (ND) is a set of processes and messages. It is defined in RFC4861. It replaces ARP, ICMP Router Discovery, and the ICMP Redirect message used in IPv4. Besides replacing these functions of IPv4, it also provides a lot of additional functionalities that simplify network administration and management. CONFIGURE DHCP SNOOPING ON CISCO SWITCHES DHCP Snooping is a security feature of Layer 2 switches. It allows us to filter and block certain types of DHCP traffic. By using this feature, we can mitigate several security risks caused by rogue DHCP servers and attackers. DHCP snooping works on a per-VLAN basis. By default, this feature is not enabled. To use this feature, first, wehave
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. HOT STANDBY ROUTER PROTOCOL EXPLAINED What is the HSRP? A default gateway router connects a network's local subnet to a remote subnet of the same network or another network. For backup, if an administrator wants to configure more than one default gateway router, the administrator needs to configure an FHRP protocol. CLIENT-SERVER NETWORKS MODEL EXPLAINED The client-server network model stores user accounts and passwords on a centralized database that can be installed on a single system or a group of systems. If a device accesses a service and presents a platform to use the accessed service, the device is known as theclient.
DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. WHAT DHCP IS AND TYPES OF DHCP EXPLAINED This tutorial explains DHCP and its types in detail. Learn what the DHCP is and what are the advantages and disadvantages of having a DHCP server in the network. Each device in an IP network requires a valid IP configuration. If the network size is small, an administrator can manually provide an IP configuration to each device. CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
HOW TO CONFIGURE WIRELESS NETWORK IN PACKET TRACER This tutorial explains how to configure and connect wireless network in packet tracer step by step with examples. Learn how to secure a wireless network with WAP key and enable static routing in Linksys router with packet tracer lab example. CONFIGURE DHCP SERVER FOR MULTIPLE VLANS ON THE SWITCH To configure a host as the DHCP client, click the host and click the Desktop menu option and click the IP configuration option and choose the DHCP option. If the DHCP server is properly configured, the DHCP client will receive the IP configuration in a few seconds. The following image shows this procedure step by step. HOW TO ADD, INSTALL OR IMPORT IOS IN GNS3 Download or obtain the IOS file that you want to use on GNS3. Open GNS3, and click the Edit file menu, and from the sub-menu, click the Preferences option.. On the opened window, navigate to the Dynamips -> IOS routers option in the left pane and click the New button in the right pane.. Select the New Image option and click the Browse button and select the downloaded IOS image file. DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
CONFIGURE VTP SERVER AND CLIENT IN SWITCH This tutorial explains basic concepts of VTP Protocol, VTP Domain, VTP Messages and VTP modes (Server mode, Transparent mode and Client mode) in detail with practical example in packet tracer. Learn how to configure VTP Server and VTP Clients step by step. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. HOW TO CONFIGURE NTP IN CISCO ROUTER In order to deploy router R2 as NTP Server/Client router where it reads time from R1, we have to use following command in R2. R2 (config)#ntp server 100.0.0.1. Configure the NTP server IP address and save the configuration. If you don’t see the updated time CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
CONFIGURE VTP SERVER AND CLIENT IN SWITCH This tutorial explains basic concepts of VTP Protocol, VTP Domain, VTP Messages and VTP modes (Server mode, Transparent mode and Client mode) in detail with practical example in packet tracer. Learn how to configure VTP Server and VTP Clients step by step. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. HOW TO CONFIGURE NTP IN CISCO ROUTER In order to deploy router R2 as NTP Server/Client router where it reads time from R1, we have to use following command in R2. R2 (config)#ntp server 100.0.0.1. Configure the NTP server IP address and save the configuration. If you don’t see the updated time CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
OSI MODEL ADVANTAGES AND BASIC PURPOSE EXPLAINED This tutorial explains the advantages, disadvantages, and basic purposes of the OSI model in detail. Learn why the OSI Model was created along with the purposes and benefits of the OSI model. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. MAC ADDRESSES EXPLAINED WITH EXAMPLES Let’s understand this with an example. Suppose in a network three PCs; PC-A (11000ABB28FC), PC-B (00000ABB28FC) and PC-C (00000ABB28FC) are connected through a switch. NICs of PC-B and PC-C have the same MAC address 00000ABB28FC. If PC-A sends a frame to the destination MAC address 00000ABB28FC, the switch fails to deliver this frame as it LAYER 2 SWITCHING LOOPS IN NETWORK EXPLAINED In nutshell, a layer 2 switching loop creates three major problems; broadcast storm, duplicate frames, and unstable CAM table. If a loop exists, a single looped frame is sufficient to decrease the performance of the entire network by consuming the bandwidth and CPU power of the affected devices. To learn how to remove the layer 2switching loop
CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
DIFFERENCES BETWEEN BASEBAND AND BROADBAND EXPLAINED Baseband technology transmits a single data signal/stream/channel at a time while broadband technology transmits multiple data signals/streams/channels simultaneously at the same time. The following image shows an example of both technologies. To understand the basic differences between both technologies, consider the basebandas a railway
HOW TO CONFIGURE STATIC NAT IN CISCO ROUTER This tutorial explains Static NAT configuration in detail. Learn how configure static NAT, map address (inside local address, outside local address, inside global address and outside global address), debug and verify Static NAT translation step by step with practical examples inpacket tracer.
DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
CONFIGURE VTP SERVER AND CLIENT IN SWITCH This tutorial explains basic concepts of VTP Protocol, VTP Domain, VTP Messages and VTP modes (Server mode, Transparent mode and Client mode) in detail with practical example in packet tracer. Learn how to configure VTP Server and VTP Clients step by step. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. HOW TO CONFIGURE NTP IN CISCO ROUTER In order to deploy router R2 as NTP Server/Client router where it reads time from R1, we have to use following command in R2. R2 (config)#ntp server 100.0.0.1. Configure the NTP server IP address and save the configuration. If you don’t see the updated time CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
DOWNLOAD PACKET TRACER 8.0.0 AND ALL PREVIOUS VERSIONS This article provides direct downloading links to Cisco Packet Tracer. From this page, you can download the latest version (8.0.0) as well as all previous versions of Packet Tracer. PS AUX COMMAND AND PS COMMAND EXPLAINED The options A and e provide summarized overview of running processes. To print the detailed overview, use the options f (full format) and F (extra full format) with these options.. To view the same output in BSD Unix style, use the options "aux".The "ps aux" command is the most frequently used command by Linux administrators.Before we move to the next example, let's understand the options ACCESS POINTS AND WIRELESS LAN CONTROLLERS EXPLAINED To extend the coverage area, multiple access points are used together under a Wireless LAN Controller. An access point which works under the WLC is known as the LWAP (Lightweight Access Point). In WLC-LWAPs setup, the WLC controls and manages all LWAPs. A LWAP works as the bridge between the WLC and the end device. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
CONFIGURE VTP SERVER AND CLIENT IN SWITCH This tutorial explains basic concepts of VTP Protocol, VTP Domain, VTP Messages and VTP modes (Server mode, Transparent mode and Client mode) in detail with practical example in packet tracer. Learn how to configure VTP Server and VTP Clients step by step. CONFIGURE PAT IN CISCO ROUTER WITH EXAMPLES This tutorial explains how to configure port address translation (PAT) in router step by step with examples. Learn how to connect multiple devices with remote network from single IP address through PAT or NAT Overload, verify and troubleshoot PAT configuration view PAT address translation from show commands. HOW TO CONFIGURE NTP IN CISCO ROUTER In order to deploy router R2 as NTP Server/Client router where it reads time from R1, we have to use following command in R2. R2 (config)#ntp server 100.0.0.1. Configure the NTP server IP address and save the configuration. If you don’t see the updated time CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
COMPLETE COMPUTER NETWORKING NOTES GUIDES TUTORIALS This website provides a comprehensive collection of computer networking tutorials, notes and study guides for anyone who is preparing for networking certificate or working in computer networking field. Learn complex networking concepts and topics in easy language with step by step practical examples. SWITCH STACKING EXPLAINED WITH BENEFITS Benefits of the Switch Stacking. The biggest benefit of the Switch Stacking is that it allows us to incrementally add more ports in the existing switch. By doing this, we can avoid the cost of upgrading to a bigger switch. Other benefits of the Switch Stacking are the following. It reduces the management overhead. DATA ENCAPSULATION AND DE-ENCAPSULATION EXPLAINED Data Encapsulation and De-encapsulation Explained. This tutorial explains how the OSI model and TCP/IP model encapsulate and de-encapsulate the data when it passes through the layers. In a networking model, the term encapsulation refers to a process in which protocol information is added to the data. The term de-encapsulationrefers to a
OSI MODEL ADVANTAGES AND BASIC PURPOSE EXPLAINED This tutorial explains the advantages, disadvantages, and basic purposes of the OSI model in detail. Learn why the OSI Model was created along with the purposes and benefits of the OSI model. SEGMENTATION EXPLAINED WITH TCP AND UDP HEADER Key points. TCP uses segmentation while UDP does not. Both protocols use different types of header to pack the data for transmission. UDP header contains information only about the compulsory functions and it is 8 bytes in the length. TCP header contains information for both compulsory and optional functions. MAC ADDRESSES EXPLAINED WITH EXAMPLES Let’s understand this with an example. Suppose in a network three PCs; PC-A (11000ABB28FC), PC-B (00000ABB28FC) and PC-C (00000ABB28FC) are connected through a switch. NICs of PC-B and PC-C have the same MAC address 00000ABB28FC. If PC-A sends a frame to the destination MAC address 00000ABB28FC, the switch fails to deliver this frame as it LAYER 2 SWITCHING LOOPS IN NETWORK EXPLAINED In nutshell, a layer 2 switching loop creates three major problems; broadcast storm, duplicate frames, and unstable CAM table. If a loop exists, a single looped frame is sufficient to decrease the performance of the entire network by consuming the bandwidth and CPU power of the affected devices. To learn how to remove the layer 2switching loop
CONFIGURE A STATIC DEFAULT ROUTE IN CISCO PACKET TRACER The following image shows how to run this command in the packet tracer. How a default route and routing work. When a router receives a packet on its interface, it reads the destination network address of the incoming packet and locates the destination network address in therouting table.
DIFFERENCES BETWEEN BASEBAND AND BROADBAND EXPLAINED Baseband technology transmits a single data signal/stream/channel at a time while broadband technology transmits multiple data signals/streams/channels simultaneously at the same time. The following image shows an example of both technologies. To understand the basic differences between both technologies, consider the basebandas a railway
HOW TO CONFIGURE STATIC NAT IN CISCO ROUTER This tutorial explains Static NAT configuration in detail. Learn how configure static NAT, map address (inside local address, outside local address, inside global address and outside global address), debug and verify Static NAT translation step by step with practical examples inpacket tracer.
* Home
* Networking Tutorials* CCNA Study Guide
* Career Resources
* RHCE 7 Study Guide* Linux Tutorials
* Basic Linux
CCNA STUDY GUIDE
Configure DHCP Snooping on Cisco Switches This tutorial explains how to configure DHCP Snooping on Cisco switches through a packet tracer example. Learn DHCP snooping configuration in detail through examples.VIEW
How DHCP Snooping works Explained This tutorial explains the basic concept of DHCP snooping in detail. Learn what DHCP snooping is and how it works on Cisco switches.VIEW
How to Configure DHCP Relay Agent on Cisco Routers How DHCP Relay Agents work Explained How to Configure DHCP Server on Cisco Routers Configure DHCP Server for multiple VLANs on the SwitchView All Articles
LINUX TUTORIALS
Tar command Compress and Extract Archives The tutorial explains how to use the tar command to compress and extract files in Linux. Learn how to preserve the SELinux context while creating a tar archive file.VIEW
Tar command examples in Linux This tutorial presents the most useful examples of the tar command. Learn how to create, list, update, and manage an archived file inLinux.
VIEW
Tar command options and syntax explained How to use gzip and bzip2 Linux commands Explained Similarities and differences between gzip and bzip2 Vi and Vim Modes Explained through ExamplesView All Articles
NETWORKING TUTORIALS Network cable Crimping and Testing Tools This tutorial explains the most common twisted-pair network cable testing and crimping tools in detail. Learn the tools that you can use to crimp and test twisted-pair network cables.VIEW
Basic Functions of a Computer Explained This tutorial explains the basic functions, operations, and characteristics of a computer. Learn the four major functions of a computer through diagrams and examples.VIEW
Differences between Throughput and Bandwidth Explained Differences between Baseband and Broadband Explained Multiplexing and Demultiplexing Explained with Types Data Modulation in Computer NetworksView All Articles
RHCE 7 STUDY GUIDE
How to Configure and use Linux as a Router This tutorial explains how to enable IP forwarding in Linux. Learn how to use a Linux system as the router in detail through thepractical example.
VIEW
How to configure IP address in Linux This tutorial explains how to configure an IP address in Linux. Learn how to use the nmcli, nmtui and nm-connection-editor in detail withpractical examples.
VIEW
Network Configuration Files in Linux Explained Firewalld Rich Rules Explained with Examples Basic Linux Commands for Network Testing Linux System Administration Commands Explained with ExamplesView All Articles
We do not accept any kind of Guest Post. Except Guest post submission, for any other query (such as adverting opportunity, product advertisement, feedback, suggestion, error reporting and technical issue) or simply just say to hello mail us ComputerNetworkingNotes@gmail.com Computer Networking Notes and Study Guides © 2020. All RightsReserved.
* About
* Privacy Policy
* Terms and ConditionsDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0