Are you over 18 and want to see adult content?
More Annotations
A complete backup of policyproposalsforindia.com
Are you over 18 and want to see adult content?

A complete backup of nationalgeneral.com
Are you over 18 and want to see adult content?
A complete backup of aspcapetinsurance.com
Are you over 18 and want to see adult content?

A complete backup of loansforbadcredit1.com
Are you over 18 and want to see adult content?

A complete backup of aspiredomains.com
Are you over 18 and want to see adult content?
A complete backup of fundacaolasalle.org.br
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://sharezur.com
Are you over 18 and want to see adult content?
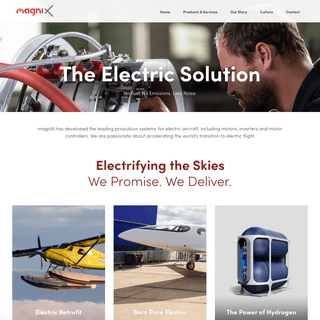
A complete backup of https://magnix.aero
Are you over 18 and want to see adult content?

A complete backup of https://sdelsol.com
Are you over 18 and want to see adult content?

A complete backup of https://slovar.cc
Are you over 18 and want to see adult content?
A complete backup of https://insafart.com
Are you over 18 and want to see adult content?

A complete backup of https://resumehelp.com
Are you over 18 and want to see adult content?
A complete backup of https://javiermegias.com
Are you over 18 and want to see adult content?

A complete backup of https://thesportsbet.xyz
Are you over 18 and want to see adult content?

A complete backup of https://bikepacking.com
Are you over 18 and want to see adult content?

A complete backup of https://web-ru.net
Are you over 18 and want to see adult content?
A complete backup of https://gametrade.jp
Are you over 18 and want to see adult content?

A complete backup of https://specialtyfabricsreview.com
Are you over 18 and want to see adult content?
Text
CYMULATE
Cymulate
CYMULATE CYCLONE
Building upon the success of the Cymulate Purple Team module, Cyclone is an exclusive offering for security service providers. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aPARTNERS CENTRAL
Together with a network of over 100 recognized global partners, Cymulate is on a mission to deliver better security for organizationsworldwide
THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in COMPROMISING A DOMAIN WITH THE HELP OF A SPOOLER Compromising a Domain With the Help of a Spooler. My job in the Cymulate Research Lab is to craft and implement attack scenarios for Cymulate customers to launch in CYBER ATTACK SIMULATION VS PEN TESTING VS VULNERABILITY Whitepaper. Organizations of all shapes and sizes are fighting the war against cyberattackers. As we have seen in recent years, cyberattacks are becoming more and more sophisticated, which makes it harder to detect and mitigate them. WHAT IS BREACH AND ATTACK SIMULATION (BAS)? Mike Talon. Mike Talon is a Solution Architect living and working in New York City. He’s assisted in disaster recovery and migration, Cloud transformation, and identity and security operations and testing for companies ranging from Mom & Pop retail shops to Fortune 100global companies.
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Cymulate's continuous security validation platform is used by security teams to determine their gaps within seconds.CYMULATE
Cymulate
CYMULATE CYCLONE
Building upon the success of the Cymulate Purple Team module, Cyclone is an exclusive offering for security service providers. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aPARTNERS CENTRAL
Together with a network of over 100 recognized global partners, Cymulate is on a mission to deliver better security for organizationsworldwide
THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in COMPROMISING A DOMAIN WITH THE HELP OF A SPOOLER Compromising a Domain With the Help of a Spooler. My job in the Cymulate Research Lab is to craft and implement attack scenarios for Cymulate customers to launch in CYBER ATTACK SIMULATION VS PEN TESTING VS VULNERABILITY Whitepaper. Organizations of all shapes and sizes are fighting the war against cyberattackers. As we have seen in recent years, cyberattacks are becoming more and more sophisticated, which makes it harder to detect and mitigate them. WHAT IS BREACH AND ATTACK SIMULATION (BAS)? Mike Talon. Mike Talon is a Solution Architect living and working in New York City. He’s assisted in disaster recovery and migration, Cloud transformation, and identity and security operations and testing for companies ranging from Mom & Pop retail shops to Fortune 100global companies.
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYBER SECURITY COMPANY OVERVIEW Making Cyber Security Simple. Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations.PARTNERS CENTRAL
Together with a network of over 100 recognized global partners, Cymulate is on a mission to deliver better security for organizationsworldwide
DATA EXFILTRATION VECTOR Cymulate’s Data Exfiltration vector challenges your Data Loss Prevention controls, enabling you to assess the security of outbound critical data before it's too late.OSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks.CYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all BAZARCALL METHOD: CALL CENTERS HELP SPREAD BAZARLOADER BazarLoader (sometimes referred to as BazaLoader) is malware that provides backdoor access to an infected Windows host. After a client is infected, criminals use this backdoor access to send follow-up malware, scan the environment and exploit other vulnerable hosts on the network. The threat actor behind BazarLoader uses different methods to distribute this malware to potential victims. InGARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. TEAMTNT USING WATCHDOG TTPS TO EXPAND ITS CRYPTOJACKING Researchers have identified indicators traditionally pointing to the WatchDog cryptojacking group, which have been incorporated in the tactics, techniques and procedures (TTPs) used by the TeamTNT cryptojacking group. The new scripts from TeamTNT are overtly copying infrastructure naming conventions and hijacking a known WatchDog C2 hosting system, 199.199.226117. Though CYBER ATTACK SIMULATION VS PEN TESTING VS VULNERABILITY Whitepaper. Organizations of all shapes and sizes are fighting the war against cyberattackers. As we have seen in recent years, cyberattacks are becoming more and more sophisticated, which makes it harder to detect and mitigate them. CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
GARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can download CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
GARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can download CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
OSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those TEAMTNT USING WATCHDOG TTPS TO EXPAND ITS CRYPTOJACKING Researchers have identified indicators traditionally pointing to the WatchDog cryptojacking group, which have been incorporated in the tactics, techniques and procedures (TTPs) used by the TeamTNT cryptojacking group. The new scripts from TeamTNT are overtly copying infrastructure naming conventions and hijacking a known WatchDog C2 hosting system, 199.199.226117. Though PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy forGARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can download BAZARCALL METHOD: CALL CENTERS HELP SPREAD BAZARLOADER BazarLoader (sometimes referred to as BazaLoader) is malware that provides backdoor access to an infected Windows host. After a client is infected, criminals use this backdoor access to send follow-up malware, scan the environment and exploit other vulnerable hosts on the network. The threat actor behind BazarLoader uses different methods to distribute this malware to potential victims. InCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYBER ATTACK SIMULATION VS PEN TESTING VS VULNERABILITY As we will see in this Whitepaper, vulnerability scans and penetration tests are useful for getting insight into the security posture of an organization at a specific moment. Although useful, they do not present the full picture; especially when it comes to sophisticated, multi-vector attacks. Download this Whitepaper to learn: The new and CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
GARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can download THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed inCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
WHAT IS BREACH AND ATTACK SIMULATION (BAS)? BAS from a First-Person Point of View. Breach and Attack Simulation (BAS) is the answer to the question of how to make sure these weaknesses are found and addressed without breaking the network or the bank. At its core, BAS is exactly what it says on the tin - a platform that is designed to perform actions that closely mimic real threatactions
CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
GARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can download THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed inCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
WHAT IS BREACH AND ATTACK SIMULATION (BAS)? BAS from a First-Person Point of View. Breach and Attack Simulation (BAS) is the answer to the question of how to make sure these weaknesses are found and addressed without breaking the network or the bank. At its core, BAS is exactly what it says on the tin - a platform that is designed to perform actions that closely mimic real threatactions
CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
THE APPROACHES OF BREACH AND ATTACK SIMULATION Whitepaper. Testing the cybersecurity posture of an organization or its cybersecurity resilience to cyberattacks, has come a long way. The demand for the latest and most comprehensive testing solutions keeps growing to face the growing cybercrime wave. TEAMTNT USING WATCHDOG TTPS TO EXPAND ITS CRYPTOJACKING Researchers have identified indicators traditionally pointing to the WatchDog cryptojacking group, which have been incorporated in the tactics, techniques and procedures (TTPs) used by the TeamTNT cryptojacking group. The new scripts from TeamTNT are overtly copying infrastructure naming conventions and hijacking a known WatchDog C2 hosting system, 199.199.226117. ThoughOSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy forGARTNER REPORT
Gartner Report. Predicts 2021: Cybersecurity Program Management and IT Risk Management. Gartner has produced impactful predictions about cybersecurity program management. This year’s predictions focus on governance, organizational structure, evolution of the role, talent and board reporting. Security and risk management leaders can downloadCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYBER ATTACK SIMULATION VS PEN TESTING VS VULNERABILITY As we will see in this Whitepaper, vulnerability scans and penetration tests are useful for getting insight into the security posture of an organization at a specific moment. Although useful, they do not present the full picture; especially when it comes to sophisticated, multi-vector attacks. Download this Whitepaper to learn: The new and CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides a CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
CYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website.PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
WEB APPLICATION FIREWALL SIMULATOR Cymulate’s Web Application Firewall (WAF) vector challenges your WAF security resilience to web payloads and assists in protecting your web apps from future attacks. Web applications, including consumer-facing applications and enterprise apps, have become a central business component, and huge amounts of money and effort are spent protecting DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy for CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides a CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
CYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website.PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
WEB APPLICATION FIREWALL SIMULATOR Cymulate’s Web Application Firewall (WAF) vector challenges your WAF security resilience to web payloads and assists in protecting your web apps from future attacks. Web applications, including consumer-facing applications and enterprise apps, have become a central business component, and huge amounts of money and effort are spent protecting DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy forCYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
WEB APPLICATION FIREWALL SIMULATOR Cymulate’s Web Application Firewall (WAF) vector challenges your WAF security resilience to web payloads and assists in protecting your web apps from future attacks. Web applications, including consumer-facing applications and enterprise apps, have become a central business component, and huge amounts of money and effort are spent protecting LATERAL MOVEMENT ATTACK SIMULATOR Once an organization’s perimeter defenses fail and endpoint security is bypassed, providing the attacker a foothold in the organization (see Endpoint Security Vector) lateral movement inside the network is a common next step in a penetration scenario.Organizations deploy numerous security solutions and controls in order to prevent suchmovement.
THE APPROACHES OF BREACH AND ATTACK SIMULATION Whitepaper. Testing the cybersecurity posture of an organization or its cybersecurity resilience to cyberattacks, has come a long way. The demand for the latest and most comprehensive testing solutions keeps growing to face the growing cybercrime wave. FULL KILL-CHAIN APT SIMULATION Instrumenting your Security with APT Simulations. Cymulate’s Full Kill-Chain APT Simulation Module solves the challenge of security effectiveness testing across the entire cyber kill chain by instrumenting your security framework in a comprehensive and easy-to-use manner. Instead of challenging each attack vector separately, organizations can TEAMTNT USING WATCHDOG TTPS TO EXPAND ITS CRYPTOJACKING Researchers have identified indicators traditionally pointing to the WatchDog cryptojacking group, which have been incorporated in the tactics, techniques and procedures (TTPs) used by the TeamTNT cryptojacking group. The new scripts from TeamTNT are overtly copying infrastructure naming conventions and hijacking a known WatchDog C2 hosting system, 199.199.226117. ThoughOSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trickCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all RECON ATTACK VECTOR, DETECT RECONNAISSANCE ATTACKS. Recon is the initial planning stage of an attack or pre-attack phase. During the recon phase, an attacker performs a comprehensive technical analysis on their target organization in addition to gathering employee and organizational intelligence that can be used CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website.CYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy for THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website.CYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy for THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed in THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
WEB APPLICATION FIREWALL SIMULATOR Cymulate’s Web Application Firewall (WAF) vector challenges your WAF security resilience to web payloads and assists in protecting your web apps from future attacks. Web applications, including consumer-facing applications and enterprise apps, have become a central business component, and huge amounts of money and effort are spent protecting IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
TEAMTNT USING WATCHDOG TTPS TO EXPAND ITS CRYPTOJACKING Researchers have identified indicators traditionally pointing to the WatchDog cryptojacking group, which have been incorporated in the tactics, techniques and procedures (TTPs) used by the TeamTNT cryptojacking group. The new scripts from TeamTNT are overtly copying infrastructure naming conventions and hijacking a known WatchDog C2 hosting system, 199.199.226117. ThoughOSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick HELLO RANSOMWARE USES UPDATED CHINA CHOPPER WEB SHELL In January, appeared a new ransomware using .hello as its extension in one of our cases that possibly arrived via a SharePoint server vulnerability. This appeared to be a new ransomware family dubbed as the Hello ransomware (aka WickrMe), named after the chat application that was used to contact the cybercriminals responsible. Previous variants were observed using .hemming and .strike RECON ATTACK VECTOR, DETECT RECONNAISSANCE ATTACKS. Recon is the initial planning stage of an attack or pre-attack phase. During the recon phase, an attacker performs a comprehensive technical analysis on their target organization in addition to gathering employee and organizational intelligence that can be used NECRO PYTHON BOT ADDS NEW EXPLOITS AND TEZOS MINING TO ITS Although the bot was originally discovered earlier this year, the latest activity shows numerous changes to the bot, ranging from different command and control (C2) communications and the addition of new exploits for spreading, most notably vulnerabilities in VMWare vSphere, SCO OpenServer, Vesta Control Panel and SMB-based exploits that were not present in the earlier iterations of the code.CYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy for THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed inCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
PURPLE TEAM SIMULATION MODULE The Purple Team module brings endless options and scale to everyone in the Security Team; Blue Team groups assessing security controls, SOC groups maintaining a watch over critical systems, and Red Team groups planning and executing attacks. The module is fully aligned to the MITRE ATT&CK framework utilizing its de-facto standard taxonomy for THREAT ACTORS USE MSBUILD TO DELIVER RATS FILELESSLY A campaign was discovered, in which threat actors used Microsoft Build Engine (MSBuild) to filelessly deliver Remcos remote access tool (RAT) and password-stealing malware commonly known as RedLine Stealer This campaign, which has low or zero detections on antivirus tools, appears to have begun in April 2021 and was still ongoing as of May 11, 2021. The malicious MSBuild files observed inCYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYBER SECURITY COMPANY OVERVIEW Cymulate was founded by an elite team of former IDF intelligence officers who identified frustrating inefficiencies during their cyber security operations. From this came their mission to empower organizations worldwide and make advanced cyber security as simple and familiar as sending an e-mail. Today, Cymulate is trusted by hundredsof
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
THE APPROACHES OF BREACH AND ATTACK SIMULATION Whitepaper. Testing the cybersecurity posture of an organization or its cybersecurity resilience to cyberattacks, has come a long way. The demand for the latest and most comprehensive testing solutions keeps growing to face the growing cybercrime wave.OSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
PHISHING AWARENESS VECTOR Cymulate’s Phishing Awareness vector is designed to evaluate your employees’ security awareness. It simulates phishing campaigns and detects weak links in your organization. Since it is designed to reduce the risk of spear-phishing, ransomware or CEO fraud, the solution can help you to deter data breaches, minimize malware-relateddowntime
DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those NECRO PYTHON BOT ADDS NEW EXPLOITS AND TEZOS MINING TO ITS Although the bot was originally discovered earlier this year, the latest activity shows numerous changes to the bot, ranging from different command and control (C2) communications and the addition of new exploits for spreading, most notably vulnerabilities in VMWare vSphere, SCO OpenServer, Vesta Control Panel and SMB-based exploits that were not present in the earlier iterations of the code.CYMULATE
Cymulate Cymulate is an award-winning SaaS-based Breach and Attack Simulation (BAS) platform that makes it simple to know and optimize your security posture any time, all CYMULATE POC PRE-REQUIREMENTS FEB 2020 2 Company Confidential & Proprietary Page 6 of 7 SOFTWARE AND WHITELISTPRE-REQUIREMENTS
CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
PHISHING AWARENESS VECTOR Cymulate’s Phishing Awareness vector is designed to evaluate your employees’ security awareness. It simulates phishing campaigns and detects weak links in your organization. Since it is designed to reduce the risk of spear-phishing, ransomware or CEO fraud, the solution can help you to deter data breaches, minimize malware-relateddowntime
CYMULATE BLOG
Cymulate’s March 2021 Cyberattacks Wrap-up Threat actors were busy during March 2021, breaching major companies such as SITA, a global IT company supporting 90% of the world’s airlines. In this case, the PII belonging to airline passengers was stolen, including their names, card numbers, and status level. DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
SOX COMPLIANCE NOW INCLUDES CYBERSECURITY SOX Compliance Includes Cybersecurity - Let Cymulate Help You To Navigate The Waters. The Sarbanes-Oxley Act (known as SOX) went into effect in 2002 to protect shareholders and the general public from accounting errors and fraudulent practices of organizations.It was also tailored to improve the accuracy of corporate disclosures. SOX was drafted to improve corporate governance and CYMULATE - THE #1 CONTINUOUS SECURITY VALIDATION PLATFORMPLATFORMCOMPANYPARTNERSRESOURCESEVENTSBLOG Know your security gaps by proactively challenging your security controls, people and processes with the most comprehensive SaaS-based security validation platform that deploys in minutes: Launch out-of-the-box, expert and threat intelligence-led risk assessments that are simple to use for all skill levels. Create and automatered/purple team
CYBERSECURITY INTEGRATIONS USING CYMULATE'S PLATFORM Qualys Vulnerability Management is a cloud-based solution that detects vulnerabilities on all networked assets, including servers, network devices (e.g. routers, switches, firewalls, etc.), peripherals (such as IP-based printers or fax machines) and workstations. Qualys can assess any device that has an IP address. Cymulate’s integration with Qualys Vulnerability Management provides aCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
PARTNERS CENTRAL
Join Our Network of Partners. Fill in your information and we will contact you to provide additional details on our Partner Program. Please select Country * Cote d'Ivoire Korea, Democratic People's Republic of Korea, Republic of Macao Isle of Man Gibraltar Afghanistan Albania Algeria Andorra Angola Antigua and Barbuda Antigua & DepsArgentina
IMMEDIATE THREAT INTELLIGENCE MODULE Cymulate’s Immediate Threat Intelligence vector is designed to inform and evaluate your organization’s security posture as quickly as possible against the very latest cyber attacks. The simulation is created by the Cymulate Research Lab which catches and analyzes threats immediately after they are launched by cybercriminals andmalicious
PHISHING AWARENESS VECTOR Cymulate’s Phishing Awareness vector is designed to evaluate your employees’ security awareness. It simulates phishing campaigns and detects weak links in your organization. Since it is designed to reduce the risk of spear-phishing, ransomware or CEO fraud, the solution can help you to deter data breaches, minimize malware-relateddowntime
CYMULATE BLOG
Cymulate’s March 2021 Cyberattacks Wrap-up Threat actors were busy during March 2021, breaching major companies such as SITA, a global IT company supporting 90% of the world’s airlines. In this case, the PII belonging to airline passengers was stolen, including their names, card numbers, and status level. DATA EXFILTRATION VECTOR The Data Exfiltration vector is designed to evaluate how well your DLP solutions and controls prevent any extraction of critical information from outside the organization. The platform tests the outbound flows of data (such as personally identifiable (PII), medical, financial and confidential business information) to validate that those THE APPROACHES OF BREACH AND ATTACK SIMULATION But that changed when Breach & Attack Simulation (BAS) technology became available. There are currently several vendors providing BAS solutions with different approaches that are gaining traction as more and more users are jumping on the BAS bandwagon. In this document you will learn about the 3 Approaches of BAS technologies and whichapproach
SOX COMPLIANCE NOW INCLUDES CYBERSECURITY SOX Compliance Includes Cybersecurity - Let Cymulate Help You To Navigate The Waters. The Sarbanes-Oxley Act (known as SOX) went into effect in 2002 to protect shareholders and the general public from accounting errors and fraudulent practices of organizations.It was also tailored to improve the accuracy of corporate disclosures. SOX was drafted to improve corporate governance andCYMULATE CYCLONE
Cymulate Cyclone enables pen-testing service providers to craft, automate and deliver purple teaming exercises that help their customers actively protect their network. Cyclone-based services optimize SOC detection capabilities, hone threat hunting skills and improve incident response processes. Building upon the success of thePurple Team
CYMULATE
Cymulate. Sign in with Single Sign-On. New Member? Register New Account. Forgot Your Password? Back to our website. USE CASES | CYMULATE BREACH AND ATTACK SIMULATION The Solution. The Cymulate Purple Team module enables blue teams to craft and launch attack flows to assess their breach detection and incident response capabilities. The platform makes Purple team exercises accessible and achievable to security teams with minimal adversarial skills by leveraging out-of-the-box attack scenarios. LATERAL MOVEMENT ATTACK SIMULATOR Once an organization’s perimeter defenses fail and endpoint security is bypassed, providing the attacker a foothold in the organization (see Endpoint Security Vector) lateral movement inside the network is a common next step in a penetration scenario.Organizations deploy numerous security solutions and controls in order to prevent suchmovement.
OSX/HYDROMAC
The chain of different stages has become very complex nowadays and the analysis phase takes more time, due to the 'malware authors' understanding of how reverse engineering is being done, but also countering the tools we wrote to decrypt their malware. A couple of weeks after OSX/Tarmac blogpost was published, new variants of OSX/Tarmac started re-surfacing implementing a trick NECRO PYTHON BOT ADDS NEW EXPLOITS AND TEZOS MINING TO ITS Although the bot was originally discovered earlier this year, the latest activity shows numerous changes to the bot, ranging from different command and control (C2) communications and the addition of new exploits for spreading, most notably vulnerabilities in VMWare vSphere, SCO OpenServer, Vesta Control Panel and SMB-based exploits that were not present in the earlier iterations of the code. THE APPROACHES OF BREACH AND ATTACK SIMULATION Whitepaper. Testing the cybersecurity posture of an organization or its cybersecurity resilience to cyberattacks, has come a long way. The demand for the latest and most comprehensive testing solutions keeps growing to face the growing cybercrime wave. CYMULATE’S MAY 2021 CYBERATTACKS WRAP-UP What were the important cyberattacks last month? Here is a summary of cybercriminal activity in May 2021. SHARPPANDA: CHINESE APT GROUP TARGETS SOUTHEAST ASIAN Check Point Research identified an ongoing surveillance operation targeting a Southeast Asian government. The attackers use spear-phishing to gain initial access and leverage old Microsoft Office vulnerabilities together with the chain of in-memory loaders to attempt and install a previously unknown backdoor on victim's machines. The investigation shows the operation was carried out by EURONEXT SECURES TRADING WITH BREACH AND ATTACK SIMULATION Case Study. Seeking a more cost-effective way to test Euronext’s security posture and complement homegrown cyber attack simulations, Euronext’s Security Operations Manager, Jorge Ruão, heard of Cymulate’s breach and attack simulation platform, and decided togive it a try.
We won't track your information when you visit our site. But in order to comply with your preferences, we'll have to use just one tiny cookie so that you're not asked to make this choice again. To find out more about the cookies we use, see our PRIVACY POLICY.
If you decline, your information won’t be tracked when you visit this website. A single cookie will be used in your browser to remember your preference not to be tracked. Accept Decline Skip to content Cymulate is now available on AWS Marketplace!* Learn more
* Platform
* Overview
* Use Cases
* Attack Vectors
* Recon Vector
* Email Gateway
* Web Gateway
* Web Application Firewall * Phishing Awareness* Endpoint Security
* Lateral Movement
* Data Exfiltration
* Immediate Threat Intelligence * Full Kill-Chain APT * Purple Team Simulation Module* Integrations
* Cymulate on AWS Marketplace* Company
* Overview
* About Us
* Leadership
* Board
* Investors
* Research
* Our Team
* Careers
* Contact Us
* Partners
* Find a Partner
* Become a Partner
* Partners Central
* Resources
* Collateral
* News, PR & Awards
* In the News
* Press Releases
* Awards
* Media Kit
* Events
* Blog
* Contact Us
* Login
* Schedule Demo
* Free trial
CONTINUOUS SECURITY VALIDATION ACROSS THE FULL KILL CHAIN Cymulate’s breach and attack simulation platform is used by security teams to determine their security gaps within seconds and remediatethem.
START YOUR FREE TRIAL*Minutes to set up.
*No credit card required. > Security leaders should engage in a continuous security posture > assessment, applied to its highest risk threat vectors “How to Respond to the 2019 Threat Landscape,” Jeremy D’Hoinne,16 August 2019
Your browser does not support the video tag. Your browser does not support the video tag.01
SIMULATE
Simulate attacks across any vector Your browser does not support the video tag.02
EVALUATE
Know where your company is exposed Your browser does not support the video tag.03
REMEDIATE
Fix your security gapsAUTOMATE
MONITOR YOUR SECURITY POSTURE CONTINUOUSLY LEARN MORE ABOUT THE PLATFORM > COMPLETE ATTACK VECTOR COVERAGE Cymulate’s full kill chain attack vectors simulations analyze all areas of your organization including for example web apps, email, phishing, and endpoints, so no threats slip through the cracks. CHECK YOUR SECURITY POSTURE NOW START YOUR FREE TRIAL *Minutes to set up. *No credit card required. LEARN MORE ABOUT CONTINUOUS SECURITY VALIDATIONUSE CASES
Learn how Cymulate makes it easy to keep all angles of your companysecure.
Read more >
WHITEPAPER
Discover the 3 approaches of Breach and Attack Simulationtechnologies.
Download >
BLOG
Read all about the latest trends and best practices to prevent cyberattacks.
Read more >
TESTIMONIALS
*
*
*
*
All case studies >
> As Euronext’s cybersecurity team, we know that cybersecurity is > always a work in progress. Cymulate allows us to fill a gap that for > a long time was not closed directly, but only indirectly with other > security controls. We recommend anyone looking for a breach and > attack simulation platform to turn to Cymulate. - Jorge Ruão, Head of Security Operations Get the Case Study > Cymulate enables me to test, reconfigure, increase our security > posture, and lower our cyber risk – adding great value to our > security program. - William Perez, Cyber Security Leader4.8
Overall Score
94%
Recommended
My experience is completely positive, the tool does its job and finds vulnerabilities and information security holes all the time. Security and Risk Management in the Transportation Industry The process vendor and the product itself were great, very efficient and fair. We saw the added value from day 1. Recommended. CISO in the Healthcare Industry Cymulate is by far the easiest tool to onboard that provides the mostvaluable reports!
Senior IT Security Analyst in the Healthcare Industry Like having a pen tester at your beck and call. Manager, I.T. Operations in the Finance Industry We enjoy using this product and testing various security postures against it to confirm that they’re effective and implementedcorrectly.
Senior Security Engineer in the Services Industry Product has been great and easy to use. Cymulate support is alwayseasily accessible.
Senior Security Analyst in the Retail Industry My experience is completely positive, the tool does its job and finds vulnerabilities and information security holes all the time. Security and Risk Management in the Transportation Industry The process vendor and the product itself were great, very efficient and fair. We saw the added value from day 1. Recommended. CISO in the Healthcare Industry Cymulate is by far the easiest tool to onboard that provides the mostvaluable reports!
Senior IT Security Analyst in the Healthcare Industry Like having a pen tester at your beck and call. Manager, I.T. Operations in the Finance IndustryOUR AWARDS
BEST BREACH & ATTACK SIMULATION PLATFORM BEST BREACH & ATTACK SIMULATION PLATFORM BEST SECURITY SOFTWARE TECH STARTUP OF THE YEAR BEST BREACH & ATTACK SIMULATION PLATFORM BEST BREACH & ATTACK SIMULATION PLATFORM BEST BREACH & ATTACK SIMULATION PLATFORM CHECK YOUR SECURITY POSTURE NOW START YOUR FREE TRIAL *Minutes to set up. *No credit card required.HOME
PLATFORM
* Overview
* Use Cases
* Attack Vectors
* Recon
* Email Security
* Web Gateway
* Web Application Firewall * Phishing Awareness* Endpoint Security
* Lateral Movement
* Data Exfiltration
* Immediate Threat Intelligence * Full Kill-Chain APT * Purple Team Simulation* Integrations
* Cymulate on AWS MarketplaceCOMPANY
* About
* Overview
* About Us
* Leadership
* Board
* Investors
* Research Unit
* Our Team
* Career
PARTNERS
* Find a Partner
* Become A Partner
* Partners Central
RESOURCES
* Collateral
* News
* In The News
* Press Releases
* Awards
* Media Kit
EVENTS
BLOG
CONTACT US
LOGIN
FREE TRIAL
SCHEDULE DEMO
� 2020 Cymulate. All Rights Reserved. Privacy Policy | Terms andConditions
*Gartner, Cool Vendors in Application and Data Security, 4 May 2018, The GARTNER COOL VENDOR badge is a trademark and service mark of Gartner, Inc., and/or its affiliates, and is used herein with permission. All rights reserved. Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s Research & Advisory organization and should not be construed as statements of fact. Gartner disclaims all warranties, express or implied, with respect to this research, including any warranties of merchantability or fitness for aparticular purpose.
GET STARTED WITH CYMULATE NOWTry it out for
yourself! FREE TRIAL Explore Cymulate with a representative! SCHEDULE A DEMODetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0