Are you over 18 and want to see adult content?
More Annotations

A complete backup of handcraftedmodelships.com
Are you over 18 and want to see adult content?
A complete backup of pastoralninezyjuventud.org
Are you over 18 and want to see adult content?

A complete backup of blackandmissinginc.com
Are you over 18 and want to see adult content?
A complete backup of catclinicatcherryhill.net
Are you over 18 and want to see adult content?

A complete backup of adambosworth.net
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of www.cbssports.com/nba/news/warriors-vs-suns-odds-line-spread-2020-nba-picks-feb-12-predictions-from-advance
Are you over 18 and want to see adult content?
A complete backup of www.goldenstateofmind.com/2020/2/12/21133685/nba-2020-preview-warriors-visit-the-suns-get-one-last-shot-at-
Are you over 18 and want to see adult content?

A complete backup of www.rmf.fm/magazyn/news
Are you over 18 and want to see adult content?
Text
Features.
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IO BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IO RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
RDP AND BLUEKEEP
RDP and Bluekeep - not just 3389. A couple of weeks ago a new vulnerability that affects the RDP protocol was announced. This vulnerability was soon dubbed "Bluekeep" by @Gossithedog and has since been used widely in the industry.. At the time of this writing, multiple parties have now remote code execution using this vulnerability, which means they can directly get vulnerable machinesto run
IMAGE SEARCH
You can also try instead field.keyword:"value". The first one will search for any occurrence of any of the words in value, while the second one will search for an exact match of the string. Finally, in the case of some special symbols, you might require escaping in order to make the query valid. MQTT - BINARYEDGE API DOCUMENTATION MQTT. Grab MQTT information, including messages and topics. This module connects to MQTT brokers and grabs data it. The module listens for 30 seconds for the first BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IO BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IO RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
RDP AND BLUEKEEP
RDP and Bluekeep - not just 3389. A couple of weeks ago a new vulnerability that affects the RDP protocol was announced. This vulnerability was soon dubbed "Bluekeep" by @Gossithedog and has since been used widely in the industry.. At the time of this writing, multiple parties have now remote code execution using this vulnerability, which means they can directly get vulnerable machinesto run
IMAGE SEARCH
You can also try instead field.keyword:"value". The first one will search for any occurrence of any of the words in value, while the second one will search for an exact match of the string. Finally, in the case of some special symbols, you might require escaping in order to make the query valid. MQTT - BINARYEDGE API DOCUMENTATION MQTT. Grab MQTT information, including messages and topics. This module connects to MQTT brokers and grabs data it. The module listens for 30 seconds for the first BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan" PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878 MODULES - BINARYEDGE API DOCUMENTATION service-simple. The Service-Simple module attempts to connect to a remote server and identify service / product information by sending various payloads and analysing how the server responds. This module is much faster than the service module, since it doesn't perform any moreactions than this.
JARM - BINARYEDGE API DOCUMENTATION JARM. The JARM module attempts to actively fingerprint an SSL/TLS server via a series of TLS Client Hello packets to extract specific responses that can be used toSENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive: JOIN THE BINARYEDGE COMMUNITY ON SLACK! BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878 MODULES - BINARYEDGE API DOCUMENTATION service-simple. The Service-Simple module attempts to connect to a remote server and identify service / product information by sending various payloads and analysing how the server responds. This module is much faster than the service module, since it doesn't perform any moreactions than this.
SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive: JOIN THE BINARYEDGE COMMUNITY ON SLACK! BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below. BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878 MODULES - BINARYEDGE API DOCUMENTATION service-simple. The Service-Simple module attempts to connect to a remote server and identify service / product information by sending various payloads and analysing how the server responds. This module is much faster than the service module, since it doesn't perform any moreactions than this.
SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive: JOIN THE BINARYEDGE COMMUNITY ON SLACK! BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below. BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IO BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. MODULES - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOAPI V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878IMAGE SEARCH
You can also try instead field.keyword:"value". The first one will search for any occurrence of any of the words in value, while the second one will search for an exact match of the string. Finally, in the case of some special symbols, you might require escaping in order to make the query valid.SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive:HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below.TORRENTS SEARCH
For the best results and performance, try to be as specific as you can. If you need to use regular expressions, specify the field you want to search in. E.g. field:/.*microsoft.. {2}/. String fields: if the string is expected to have spaces, some kind of punctuation in the middle, or special symbols, try quoting the search terms, i.e. instead MQTT - BINARYEDGE API DOCUMENTATION MQTT. Grab MQTT information, including messages and topics. This module connects to MQTT brokers and grabs data it. The module listens for 30 seconds for the first DATA, TECHNOLOGIES AND SECURITY Data, Technologies and Security - Part 1. A lot of technologies present themselves as solutions for multiple challenges. At BinaryEdge, we are big adepts of analyzing all the different technologies until we see what correctly adapts and fits ourenvironment.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan" BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. HOW ARE USERS CHOOSING THEIR PASSWORDS ON THE INTERNET? How are users choosing their passwords on the internet? BinaryEdge collects in its platform 40fy different types of OSINT (Open Source Intelligence) information. One of the types of data that we collect is dataleaks that we find on the internet, which we clean up and importinto our platform.
HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive:TORRENTS SEARCH
For the best results and performance, try to be as specific as you can. If you need to use regular expressions, specify the field you want to search in. E.g. field:/.*microsoft.. {2}/. String fields: if the string is expected to have spaces, some kind of punctuation in the middle, or special symbols, try quoting the search terms, i.e. instead BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below.SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive:TORRENTS SEARCH
For the best results and performance, try to be as specific as you can. If you need to use regular expressions, specify the field you want to search in. E.g. field:/.*microsoft.. {2}/. String fields: if the string is expected to have spaces, some kind of punctuation in the middle, or special symbols, try quoting the search terms, i.e. instead HOW ARE USERS CHOOSING THEIR PASSWORDS ON THE INTERNET? How are users choosing their passwords on the internet? BinaryEdge collects in its platform 40fy different types of OSINT (Open Source Intelligence) information. One of the types of data that we collect is dataleaks that we find on the internet, which we clean up and importinto our platform.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
BINARYEDGEHOMEDATA/FEATURESPRICINGABOUT USCONTACTSBLOG Our Data. We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data andFeatures.
PRODUCT - BINARYEDGE HoneyPots / Sensors. Our distributed honeypot network collects events worldwide across residential and enterprise providers to give BinaryEdge clients a realtime view of what is happening on the Internet. We collect payloads, sources and classify these events, i.e. Malicious, Botnets, database scanners. We also provide a fullyautomated anomaly
BINARYEDGE PORTAL
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science.BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. PRICING - BINARYEDGE We scan the internet and acquire data that can be transformed into threat intelligence feeds or security reports. Focus on Cybersecurity, Data science and Machine learning. ATTACK SURFACE MONITORING Attack surface enumeration. Not only does ASM allow an organization to understand their own attack surface, it was also designed to monitor the entire partner, vendor or supply chain of an organization. Tens of thousands of companies can be monitored by ASM. CONTACT SALES TODAY! sales@binaryedge.io. Full Name *.API V1 (ENTERPRISE)
API V1 - Enterprise Accounts only. To get access, please get in touch with . If you are using app.binaryedge.io -> Use API V2 API V2 - BINARYEDGE API DOCUMENTATIONSEE MORE ON DOCS.BINARYEDGE.IOBINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCHENGINE
JOIN THE BINARYEDGE COMMUNITY ON SLACK!BINARYEDGE AGBINARYEDGE NINJABINARYEDGE SEARCH ENGINE BinaryEdge Enter your email below to join BinaryEdge on Slack! BinaryEdge Enter your email below to join BinaryEdge on Slack!ASHLEY MADISON
An average female user claims to have 50-60 kg weight, a height of 1.60-1.70 m and also an average/medium bodytype. One other variable on the database was the ethnicity: Although almost half of Ashley Madison users claims to be white, about 34.4% preferred not to reveal theirethnicity.
ABOUT US - BINARYEDGE The Register . Misconfigured Big Data apps are leaking data like sieves BinaryEdge concludes that it found close to 1,175 terabytes (or 1.1 petabytes) of data exposed online, after looking into just four technologies as part of an online scan"BINARYEDGE
BinaryEdge. We are a multifunctional team that focus its effort on acquiring, analyzing and classifying internet wide data, by combining efforts in the areas of Cybersecurity, Engineering and Data Science. RATE MY IP - BINARYEDGE IP Risk out of 100 The higher the risk, the higher the vulnerability/ exposure level This tool will check our database for data regarding your IP address, rather than actively scan you. BINARYEDGE API DOCUMENTATION BinaryEdge’s API Documentation About. BinaryEdge is Cybersecurity/Data Science company that focuses its effort on acquiring, analyzing and classifying internet wide data. We have developed a platform - 40fy that allows us and our customers to gather several data points from exposed servers online. The API provides access to that scanning platform, for your own usage, along withaccess to our
BINARYEDGE - SCIENCE AND TECHNOLOGY BinaryEdge - Science and Technology. 29 May 2020. ASM - Attack Surface Monitoring. When we joined Coalition we became responsible for monitoring thousands of companies everyday. As part. Read More. 02 Mar 2020. Webv2 - HTTP (s) scanning revamped. For the longest time there has been one common request that we've gotten from the. CONTACTS - BINARYEDGE Business Contact. BinaryEdge AG Witellikerweg 10 8702 Zollikon Switzerland info@binaryedge.io Registration Number: CHE-376.026.878HOST SEARCH
Host Search Parameters. The API has endpoints for querying our data in which you can use free text search together with one or more of the filters listed below.SENSORS DATA
Sensors Data Introduction. We have a distributed network of Sensors (Honeypots), that are "listen-only" machines, collecting data of every connection they receive:TORRENTS SEARCH
For the best results and performance, try to be as specific as you can. If you need to use regular expressions, specify the field you want to search in. E.g. field:/.*microsoft.. {2}/. String fields: if the string is expected to have spaces, some kind of punctuation in the middle, or special symbols, try quoting the search terms, i.e. instead HOW ARE USERS CHOOSING THEIR PASSWORDS ON THE INTERNET? How are users choosing their passwords on the internet? BinaryEdge collects in its platform 40fy different types of OSINT (Open Source Intelligence) information. One of the types of data that we collect is dataleaks that we find on the internet, which we clean up and importinto our platform.
Toggle navigation
* Home
* Data/Features
* Pricing
* About Us
* Contacts
* Blog
* Login
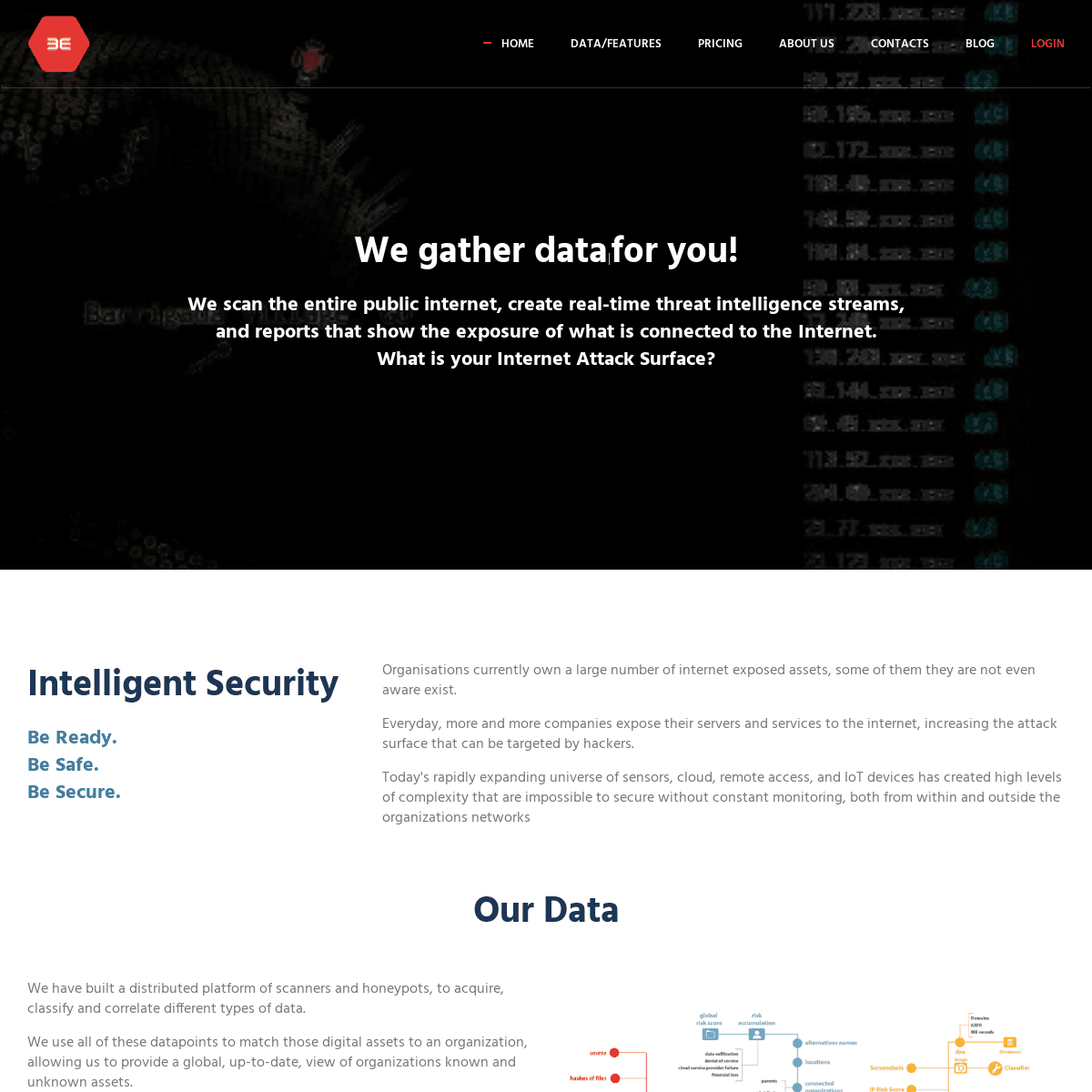
WE GATHER DATA|FOR YOU! WE SCAN THE ENTIRE PUBLIC INTERNET, CREATE REAL-TIME THREAT INTELLIGENCE STREAMS, AND REPORTS THAT SHOW THE EXPOSURE OF WHAT IS CONNECTED TO THEINTERNET.
WHAT IS YOUR INTERNET ATTACK SURFACE? INTELLIGENT SECURITYBE READY.
BE SAFE.
BE SECURE.
Organisations currently own a large number of internet exposed assets, some of them they are not even aware exist. Everyday, more and more companies expose their servers and services to the internet, increasing the attack surface that can be targeted byhackers.
Today's rapidly expanding universe of sensors, cloud, remote access, and IoT devices has created high levels of complexity that are impossible to secure without constant monitoring, both from within and outside the organizations networksOUR DATA
We have built a distributed platform of scanners and honeypots, to acquire, classify and correlate different types of data. We use all of these datapoints to match those digital assets to an organization, allowing us to provide a global, up-to-date, view of organizations known and unknown assets. Read More about our Data and FeaturesEVERY MONTH
2,000,000,000
EVENTS
200
PORTS SCANNED
+
1,000,000
TORRENTS MONITORED
ACCESS
Sign-Up for a
Free Account
API AND WEB ACCESS
Our Portal Service allows you to query the data gathered in a easy and convenient way.Get in Touch
ENTERPRISE
Want access to our Realtime DataStreams, On-Demand Custom Scanning, or High Volume requests? -------------------------* __Twitter
* __Facebook
* __Linkedin
* __info@binaryedge.io A Coalition Inc. Company Jobs - Imprint - Portal- BinaryEdge
Top
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0