Are you over 18 and want to see adult content?
More Annotations
A complete backup of www.nikkei.com/article/DGXMZO55448090Q0A210C2MM0000/
Are you over 18 and want to see adult content?
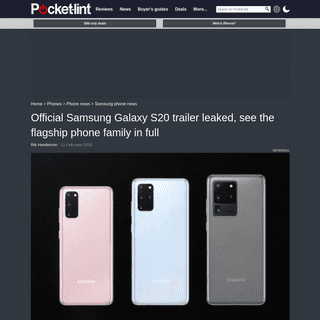
A complete backup of www.pocket-lint.com/phones/news/samsung/151042-official-samsung-galaxy-s20-trailer-leaked-see-the-flagship-
Are you over 18 and want to see adult content?
A complete backup of www.nieuwsblad.be/cnt/dmf20200211_04843540
Are you over 18 and want to see adult content?
Favourite Annotations

Open-Source Routing and Network Simulation |
Are you over 18 and want to see adult content?
Fotoğrafçı Haberleri ve Arşiv Paylaşım | Fotonistan
Are you over 18 and want to see adult content?
Custom Bespoke Software Development Company - UK | Rezaid
Are you over 18 and want to see adult content?
Kingsland Media Center - Home page
Are you over 18 and want to see adult content?
Text
COMPL...
Bulletproof’s engaging Cyber Awareness Training is available in both online and on-site training packages to ensure that every organisation can benefit from the increased security our training programme delivers. This flexibility is especially useful for larger organisations as well as those who have staff that work remotely or onshift patterns.
TARGET DEFENSE
Target Defense is a feature-rich SaaS security management solution. It integrates easily into any size organisation providing you with instant access to a scalable suite of best-in-class cyber security tools. Each core feature below is provided through a single, easy-to-use portal. Threat & Remediation Dashboard. ThreatIntelligence Feed.
OUTSOURCED DPO SERVICES From £595 /month. (ex VAT) From £995 /month. (ex VAT) £POA. Note: A GDPR Gap analysis is required for Medium and Large Businesses before the DPO service can commence. *Notification service coming soon. Please speak to your Bulletproof account manager for more information.Get a quote.
WHAT IS PECR AND WHEN DOES IT APPLY? What is PECR? PECR is a data privacy regulation which, like the GDPR, sets out rules on what marketing activities businesses can and cannot do without consent, and also dictates how businesses must deal with personal and corporate data.In plain language, PECR applies to all organisations that do at least one of these: MANAGED SIEM SECURITY INFORMATION & EVENT MANAGEMENT Our Security Information and Event Management (SIEM) service is a complete (24/7) threat monitoring solution for your infrastructure, network and systems. BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT … 7 Bulletproof Annual Cyber Security Industry Report 2020 A good penetration tester has to be part cutting-edge researcher and part technical historian. INTRUSION DETECTION SYSTEM Typically, an Intrusion Detection System (IDS) is combined with other security measures to protect a company's network. With firewalls, antivirus, and malware software in place, IDS provides a second line of defence. An IDS only warns of any suspicious activity that is BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT Bulletproof is a trusted provider of innovative cyber security products and people-centric services. We help simplify and solve thecyber security
THE ECONOMY OF HACKING: HOW DOES A HACKER MAKE MONEY WannaCry alone is known to have earned hackers at least £108,000 in Bitcoin. This is a tidy sum, but the cost to businesses is of course much higher than this, as they must suffer loss of sales and cost of recovery. £100k is a good haul, so hackers are unlikely to let it go. YOUR BEST DEFENCE AGAINST CYBER THREATS Our own 24/7 UK Security Operations Centre. All Bulletproof services are run from our in-house UK Security Operations Centre (SOC), where we blend state-of-the-art technology with real-world security experience. Good security is second-nature to our cyber experts, who are independently certified by recognised industry bodies. ENGAGING CYBER SECURITY AWARENESS TRAINING FOR BUSINESSESDOES MY ORGANISATION NEED CYBER AWARENESS TRAINING?WITH HACKERS OPERATING 24/7 AROUND THE WORLD, EVERY BUSINESS IS A TARGET. CYBER CRIMINALS DON’T CARE ABOUT THE SIZE OR NATURE OF YOUR BUSINESS, INS...DO ALL EMPLOYEES NEED SECURITY AWARENESS TRAINING?CYBER CRIMINALS WILL USE ANY METHOD TO ATTACK YOUR BUSINESS, INCLUDING A SIMPLE EMAIL. THAT’S WHY IT’S ESSENTIAL THAT EVERY MEMBER OF STAFF KNOWS T...HOW OFTEN SHOULD I HAVE CYBER SECURITY TRAINING?BULLETPROOF RECOMMENDS ANNUAL CYBER SECURITY TRAINING COURSES. BY TAKING ANNUAL REFRESHER COURSES, YOUR STAFF ARE KEPT UP-TO-DATE WITH CURRENT AND...SHOULD I CHOOSE ON-SITE OR VIRTUAL CYBER AWARENESS TRAINING?FOR MAXIMUM ENGAGEMENT AND KNOWLEDGE RETENTION, WE RECOMMEND ON-SITE SECURITY AWARENESS TRAINING WHERE POSSIBLE. WHERE THIS ISN’T PRACTICAL, BULLET...CAN I COMBINE SECURITY AWARENESS TRAINING WITH COMPLIANCE TRAINING?GOOD CYBER SECURITY TRAINING IS A CORE COMPONENT OF MANY COMPLIANCE STANDARDS, INCLUDING GDPR AND ISO 27001. COMBINING SECURITY TRAINING WITHCOMPL...
Bulletproof’s engaging Cyber Awareness Training is available in both online and on-site training packages to ensure that every organisation can benefit from the increased security our training programme delivers. This flexibility is especially useful for larger organisations as well as those who have staff that work remotely or onshift patterns.
TARGET DEFENSE
Target Defense is a feature-rich SaaS security management solution. It integrates easily into any size organisation providing you with instant access to a scalable suite of best-in-class cyber security tools. Each core feature below is provided through a single, easy-to-use portal. Threat & Remediation Dashboard. ThreatIntelligence Feed.
OUTSOURCED DPO SERVICES From £595 /month. (ex VAT) From £995 /month. (ex VAT) £POA. Note: A GDPR Gap analysis is required for Medium and Large Businesses before the DPO service can commence. *Notification service coming soon. Please speak to your Bulletproof account manager for more information.Get a quote.
WHAT IS PECR AND WHEN DOES IT APPLY? What is PECR? PECR is a data privacy regulation which, like the GDPR, sets out rules on what marketing activities businesses can and cannot do without consent, and also dictates how businesses must deal with personal and corporate data.In plain language, PECR applies to all organisations that do at least one of these: MANAGED SIEM SECURITY INFORMATION & EVENT MANAGEMENT Our Security Information and Event Management (SIEM) service is a complete (24/7) threat monitoring solution for your infrastructure, network and systems. BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT … 7 Bulletproof Annual Cyber Security Industry Report 2020 A good penetration tester has to be part cutting-edge researcher and part technical historian. INTRUSION DETECTION SYSTEM Typically, an Intrusion Detection System (IDS) is combined with other security measures to protect a company's network. With firewalls, antivirus, and malware software in place, IDS provides a second line of defence. An IDS only warns of any suspicious activity that is BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT Bulletproof is a trusted provider of innovative cyber security products and people-centric services. We help simplify and solve thecyber security
THE ECONOMY OF HACKING: HOW DOES A HACKER MAKE MONEY WannaCry alone is known to have earned hackers at least £108,000 in Bitcoin. This is a tidy sum, but the cost to businesses is of course much higher than this, as they must suffer loss of sales and cost of recovery. £100k is a good haul, so hackers are unlikely to let it go. EDR - ENDPOINT DETECTION AND RESPONSE GUIDE - BULLETPROOF How Does Endpoint Detection and Response Work? EDR security solutions vary in features, functionality, and interface, however, the goal is to provide a comprehensive centralised security platform that monitors all of an organisation's endpoints and takes action accordingly. 24/7 CYBER PROTECTION FROM A TRUSTED MANAGED SOC Key Features. The Bulletproof managed SOC provides 24/7 log monitoring with real-time alerting. Trusted detection and response to threats using advanced, industry-leading correlation engines. Bulletproof provides a host of additional innovative cyber defence services as part of our S.W.A.T. Defence® service. MANAGED DETECTION & RESPONSE SERVICES Managed Detection and Response (MDR) is an enhanced security service designed to offer low-touch, high-value cyber defences for an entire organisation. Bulletproof MDR combines cutting-edge security tooling with rock-solid runbooks and expert security analysts GAIN YOUR CYBER ESSENTIALS CERTIFICATION Enquire or Buy Now. * Cyber Essentials certificate is valued at £295 total of package cost. 1 Free cyber insurance available to UK companies with a turnover of less than £20M. 2 Remote support limited to ½ day via telephone, email or video conferencing. Additional days are available at our standard rate. COMPREHENSIVE PENETRATION TESTING A vulnerability assessment, or VA scan, is the use of an automated tool to scan a network or application for known vulnerabilities, which can then be patched. A penetration test is a lot more involved and encompasses many aspects, providing you with a more comprehensive overview of your overall security. A vulnerability scan may well beused in
HIDS A GUIDE TO HOST BASED INTRUSION DETECTION SYSTEMS What is an Intrusion Detection System? There are two types of Intrusion Detection Systems: Host-Based and Network-Based IDS. In this article, we will discuss host-based systems, but we will also explore the difference between the two. NIDS - A GUIDE TO NETWORK INTRUSION DETECTION SYSTEMS Intrusion Detection Systems (IDS) An intrusion detection system is designed to continually monitor a network or host device to detect threats. Any suspicious activity or security policy violation that is flagged will be reported to the system administrator. DETECTING AND COUNTERING INSIDE CYBER SECURITY THREATS Dangers from within. Typically security measures put in place to detect and counter cyber attacks focus on outside threats. While the faceless enemy from outside your organisation is undoubtedly a risk, the danger can just as easily come from within – but not from an anonymous attacker, from an employee that you know or trust. INTRUSION DETECTION SYSTEM Typically, an Intrusion Detection System (IDS) is combined with other security measures to protect a company's network. With firewalls, antivirus, and malware software in place, IDS provides a second line of defence. An IDS only warns of any suspicious activity that is EVERYTHING YOU NEED TO KNOW ABOUT A DPO A DPO has many responsibilities in an organisation including: 1. Acting as the liaison between the company, the data subjects and regulatory bodies. The DPO acts as the contact point for both the data subjects and the supervisory authority (in YOUR BEST DEFENCE AGAINST CYBER THREATS Our own 24/7 UK Security Operations Centre. All Bulletproof services are run from our in-house UK Security Operations Centre (SOC), where we blend state-of-the-art technology with real-world security experience. Good security is second-nature to our cyber experts, who are independently certified by recognised industry bodies. OUTSOURCED DPO SERVICES From £595 /month. (ex VAT) From £995 /month. (ex VAT) £POA. Note: A GDPR Gap analysis is required for Medium and Large Businesses before the DPO service can commence. *Notification service coming soon. Please speak to your Bulletproof account manager for more information.Get a quote.
TARGET DEFENSE
Target Defense is a feature-rich SaaS security management solution. It integrates easily into any size organisation providing you with instant access to a scalable suite of best-in-class cyber security tools. Each core feature below is provided through a single, easy-to-use portal. Threat & Remediation Dashboard. ThreatIntelligence Feed.
WHAT IS PECR AND WHEN DOES IT APPLY? What is PECR? PECR is a data privacy regulation which, like the GDPR, sets out rules on what marketing activities businesses can and cannot do without consent, and also dictates how businesses must deal with personal and corporate data.In plain language, PECR applies to all organisations that do at least one of these: MANAGED SIEM SECURITY INFORMATION & EVENT MANAGEMENT Our Security Information and Event Management (SIEM) service is a complete (24/7) threat monitoring solution for your infrastructure, network and systems. BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT Bulletproof is a trusted provider of innovative cyber security products and people-centric services. We help simplify and solve thecyber security
PENETRATION TESTING STATISTICS Bulletproof’s penetration tests in numbers. A picture is worth a thousand words, so the saying goes. So we’ve put a few together in the form of a shiny new infographic showing Bulletproof’s penetration test stats from 2018. It was a busy year for our penetration testers, with over a thousand vulnerabilities discovered and hundreds of credentials phished. THE ECONOMY OF HACKING: HOW DOES A HACKER MAKE MONEY WannaCry alone is known to have earned hackers at least £108,000 in Bitcoin. This is a tidy sum, but the cost to businesses is of course much higher than this, as they must suffer loss of sales and cost of recovery. £100k is a good haul, so hackers are unlikely to let it go. 5 THINGS A HACKER DOESN’T WANT YOU TO KNOW 5 Things a Hacker Doesn’t Want You to Know. Bulletproof shares insights into how hackers operate and the practical steps you can take to protect your business. Concluding with a Q&A with our cyber security experts. A hacker will find you online in just 32 milliseconds – regardless of your company size. WHAT'S DWELL TIME, AND HOW CRITICAL IS IT TO CYBER If many of the recent threat reports are to be believed, we can assume that, on the whole, businesses are not improving when it comes to detecting a network breach. In those isolated cases where improvement can be seen, the improvement is small. The Mandiant M-Trends 2018 report states that the median global dwell time sat at 101 days (in2017).
YOUR BEST DEFENCE AGAINST CYBER THREATS Our own 24/7 UK Security Operations Centre. All Bulletproof services are run from our in-house UK Security Operations Centre (SOC), where we blend state-of-the-art technology with real-world security experience. Good security is second-nature to our cyber experts, who are independently certified by recognised industry bodies. OUTSOURCED DPO SERVICES From £595 /month. (ex VAT) From £995 /month. (ex VAT) £POA. Note: A GDPR Gap analysis is required for Medium and Large Businesses before the DPO service can commence. *Notification service coming soon. Please speak to your Bulletproof account manager for more information.Get a quote.
TARGET DEFENSE
Target Defense is a feature-rich SaaS security management solution. It integrates easily into any size organisation providing you with instant access to a scalable suite of best-in-class cyber security tools. Each core feature below is provided through a single, easy-to-use portal. Threat & Remediation Dashboard. ThreatIntelligence Feed.
WHAT IS PECR AND WHEN DOES IT APPLY? What is PECR? PECR is a data privacy regulation which, like the GDPR, sets out rules on what marketing activities businesses can and cannot do without consent, and also dictates how businesses must deal with personal and corporate data.In plain language, PECR applies to all organisations that do at least one of these: MANAGED SIEM SECURITY INFORMATION & EVENT MANAGEMENT Our Security Information and Event Management (SIEM) service is a complete (24/7) threat monitoring solution for your infrastructure, network and systems. BULLETPROOF ANNUAL CYBER SECURITY INDUSTRY REPORT Bulletproof is a trusted provider of innovative cyber security products and people-centric services. We help simplify and solve thecyber security
PENETRATION TESTING STATISTICS Bulletproof’s penetration tests in numbers. A picture is worth a thousand words, so the saying goes. So we’ve put a few together in the form of a shiny new infographic showing Bulletproof’s penetration test stats from 2018. It was a busy year for our penetration testers, with over a thousand vulnerabilities discovered and hundreds of credentials phished. THE ECONOMY OF HACKING: HOW DOES A HACKER MAKE MONEY WannaCry alone is known to have earned hackers at least £108,000 in Bitcoin. This is a tidy sum, but the cost to businesses is of course much higher than this, as they must suffer loss of sales and cost of recovery. £100k is a good haul, so hackers are unlikely to let it go. 5 THINGS A HACKER DOESN’T WANT YOU TO KNOW 5 Things a Hacker Doesn’t Want You to Know. Bulletproof shares insights into how hackers operate and the practical steps you can take to protect your business. Concluding with a Q&A with our cyber security experts. A hacker will find you online in just 32 milliseconds – regardless of your company size. WHAT'S DWELL TIME, AND HOW CRITICAL IS IT TO CYBER If many of the recent threat reports are to be believed, we can assume that, on the whole, businesses are not improving when it comes to detecting a network breach. In those isolated cases where improvement can be seen, the improvement is small. The Mandiant M-Trends 2018 report states that the median global dwell time sat at 101 days (in2017).
YOUR BEST DEFENCE AGAINST CYBER THREATS Our own 24/7 UK Security Operations Centre. All Bulletproof services are run from our in-house UK Security Operations Centre (SOC), where we blend state-of-the-art technology with real-world security experience. Good security is second-nature to our cyber experts, who are independently certified by recognised industry bodies. EDR - ENDPOINT DETECTION AND RESPONSE GUIDE - BULLETPROOF How Does Endpoint Detection and Response Work? EDR security solutions vary in features, functionality, and interface, however, the goal is to provide a comprehensive centralised security platform that monitors all of an organisation's endpoints and takes action accordingly. MANAGED DETECTION & RESPONSE SERVICES Managed Detection and Response (MDR) is an enhanced security service designed to offer low-touch, high-value cyber defences for an entire organisation. Bulletproof MDR combines cutting-edge security tooling with rock-solid runbooks and expert security analysts CONTACT BULLETPROOF.CO.UK Contact Bulletproof to find out how we can help your business today. UK CYBER SECURITY PARTNER PROGRAM We are your clients’ best defence against cyber threats. We are bulletproof. Bulletproof is a trusted global provider of cyber security products and people-centric services. We have in-depth experience of working with public and private sector organisations toprotect
DETECTING AND COUNTERING INSIDE CYBER SECURITY THREATS Dangers from within. Typically security measures put in place to detect and counter cyber attacks focus on outside threats. While the faceless enemy from outside your organisation is undoubtedly a risk, the danger can just as easily come from within – but not from an anonymous attacker, from an employee that you know or trust. TOP CYBER SECURITY STATS YOU NEED TO KNOW FOR 2021 Forewarned is forearmed. Bulletproof has released its Annual Cyber Security Industry Report 2021, where we look at the security challenges facing businesses in 2021 and discover what organisations can do to stay ahead of the hackers.In this blog we highlight 4 key findings from the report and explore what they mean for business’ security in 2021 and beyond. WHAT IS CYBER ESSENTIALS Both Cyber Essentials and Cyber Essentials Plus demonstrate that your organisation is taking cyber security seriously and has the five technical controls in place. Cyber Essentials is a self-assessment questionnaire, verified by a certifying body (such as Bulletproof). If you have 2 or fewer major non-conformances, you pass. REPORTING A GDPR DATA BREACH What is a data breach? In order to understand how to report a data breach, we first have to know what a data breach actually is. Under the GDPR, a personal data breach is “the accidental or unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, personal data.”This covers a wide range of scenarios, some of which might be surprising. THE ECONOMY OF HACKING: HOW DOES A HACKER MAKE MONEY WannaCry alone is known to have earned hackers at least £108,000 in Bitcoin. This is a tidy sum, but the cost to businesses is of course much higher than this, as they must suffer loss of sales and cost of recovery. £100k is a good haul, so hackers are unlikely to let it go. Cookies are essential for us to deliver the best service at Bulletproof. By continuing to use this site, you agree to our cookie and our privacy policies.Accept cookies* About
* Our SOC
* Resources __
* Partners
* Events
* Careers
* Contact
01438 500 088 Get a quote* Blog
* Case Studies
* Webinars
* Industry Reports
* White Papers
* Infographics
* Penetration
Testing
* App and Infrastructure Penetration Testing * Social Engineering* Red Team
* Vulnerability
Assessments
* Vulnerability Scans* Threat Monitoring
& Protection
* Managed SIEM
* Penetration Testing ► * App and Infrastructure Penetration Testing * Social Engineering* Red Team
* Vulnerability Assessments ► * Vulnerability Scans * Threat Monitoring & Protection ►* Managed SIEM
* Compliance & Advisory ►* ISO 27001
* GDPR
* Outsourced DPO
* Cyber Essentials
* Incident Response & Forensics ► * Cyber Incident Response* Digital Forensics
* Awareness Training ►* GDPR Training
* Cyber Awareness Training* Resources ►
* Blog
* Case Studies
* Events
* Webinars
* Industry Reports
* White Papers
* Infographics
* About
* Partners
* Contact
* Careers
* Our SOC
* Compliance
& Advisory
* ISO 27001
* GDPR
* Outsourced DPO
* Cyber Essentials
* Incident Response
& Forensics
* Cyber Incident Response* Digital Forensics
* Training
& Awareness
* GDPR Training
* Cyber Awareness Training BULLETPROOF YOUR BUSINESS SECURITY Stay ahead of the hackers and protect your critical dataGet a quote
PENETRATION TESTING
Get a grip on your infrastructure and system security with our penetration testing services.Learn more
VULNERABILITY ASSESSMENTS Find weaknesses in your systems with our vulnerability scans and certified ASV scans.Learn more
MANAGED SIEM
Combine 24/7 security monitoring from our powerful SIEM for the ultimate threat monitoring and protection service.Learn more
------------------------- OUR OWN 24/7 UK SECURITY OPERATIONS CENTRE All Bulletproof services are run from our in-house UK Security Operations Centre (SOC), where we blend state-of-the-art technology with real-world security experience. Good security is second-nature to our cyber experts, who are independently certified by recognisedindustry bodies.
Read about our SOC
------------------------- END-TO-END OWNERSHIP At Bulletproof, we believe that end-to-end ownership of the service delivery drastically increases the strength of our cyber security services. Along with our in-house SOC, we also run our own data centres and private networks, with every aspect of our infrastructure regularly scanned and penetration tested. We're also certified to ISO 27001, 9001 and PCI DSS v3.2 standards, not to mention service-specific qualifications, such as CREST and Tigerscheme for penetration testing . ------------------------- TRUSTED RESEARCH TO INFORM YOUR 2021 STRATEGY The Bulletproof Annual Cyber Security Industry Report provides unique insights into why companies are struggling to keep up with the current threat landscape and how global challenges have revealed new opportunities for hackers. Download the report to help strengthen your security posture for 2021and beyond.
Get the report
OUR EXPERTS ARE THE ONES TO TRUST WHEN IT COMES TO YOUR CYBER SECURITY*
CREST approved
*
ISO 27001 and 9001 certified*
Tigerscheme qualified testers*
PCI DSS v3.2 Level 1service provider
*
24/7 on-site SecurityOperations Centre
GET A QUOTE TODAY
If you’re interested in our services, get a free, no obligation quote today by filling out the form below.Name
Phone number
Company name
Email address
Required service
Please selectPenetration TestingVulnerability ScanningManaged SIEMDDoS MitigationGDPR ComplianceOutsourced DPOCyber EssentialsPCI ComplianceISO 27001Virtual Security ManagerCyber Incident ResponseTrainingRed TeamSOCSocial EngineeringMDROther Information on your enquiry I'd like to receive Bulletproof communications about relevant servicesand events
By submitting this form, I agree to the Bulletproof privacy policy.
* Corporate Information* About us
* Careers
* Events and exhibitions* Resources
* Industry Reports
* Webinars
* White Papers
* Blog
* Social
* YouTube
* Legal
* Privacy Notice
* Cookie Policy
* Covid-19 Risk Assessment � 2021 Bulletproof.co.uk . All rights reserved. Part of the ServerChoicegroup.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0