Are you over 18 and want to see adult content?
More Annotations

A complete backup of fundacionbankinter.org
Are you over 18 and want to see adult content?

A complete backup of centennialparklands.com.au
Are you over 18 and want to see adult content?
A complete backup of futwithapero.com
Are you over 18 and want to see adult content?
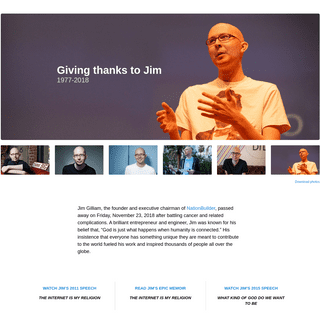
A complete backup of jimgilliam-internetismyreligion.nationbuilder.com
Are you over 18 and want to see adult content?
A complete backup of headsuphobby.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of akronchildrens.org
Are you over 18 and want to see adult content?

A complete backup of southernmarylandchronicle.com
Are you over 18 and want to see adult content?
A complete backup of themarthablog.com
Are you over 18 and want to see adult content?
Text
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
Cyberus Technology GmbH. Last week we announced our public side-channel mitigation test and benchmarking lab in light of the publication of the TAA variant of ZombieLoad. This new lab will enable us to evaluate new side-channel attacks and new mitigations and answerquestions such as:
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
Cyberus Technology GmbH. Last week we announced our public side-channel mitigation test and benchmarking lab in light of the publication of the TAA variant of ZombieLoad. This new lab will enable us to evaluate new side-channel attacks and new mitigations and answerquestions such as:
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
CYBERUS TECHNOLOGY
This series of three posts is about installing Windows 7 on an iSCSI disk. In this first article, we install it using qemu and iPXE and cover some of the pitfalls and particularities of this install method, as well as the topic of duplicating the resulting disk for use in machines of the same type.CYBERUS TECHNOLOGY
In times when working from home is ever more important there is a strong demand for video conferencing. Efficient video conferencing workloads require a lot of help from GPUs and GPU-heavy workloads have not been a lot of fun in VMs.CYBERUS TECHNOLOGY
Deep level Software and Hardware expertise for complex Software projects and enhanced cyber security. Learn now how we can help you to secure your business! Contact Cyberus Consulting. How to reach us. Cyberus Technology GmbH. service@cyberus-technology.de. +49 175 431 66 77. Zwickauer Str. 46 · 01069 Dresden · Germany.CYBERUS TECHNOLOGY
This series of three posts is about installing Windows 7 on an iSCSI disk. In this first article, we install it using qemu and iPXE and cover some of the pitfalls and particularities of this install method, as well as the topic of duplicating the resulting disk for use in machines of the same type.CYBERUS TECHNOLOGY
In times when working from home is ever more important there is a strong demand for video conferencing. Efficient video conferencing workloads require a lot of help from GPUs and GPU-heavy workloads have not been a lot of fun in VMs.CYBERUS TECHNOLOGY
In times when working from home is ever more important there is a strong demand for video conferencing. Efficient video conferencing workloads require a lot of help from GPUs and GPU-heavy workloads have not been a lot of fun in VMs.CYBERUS TECHNOLOGY
This series of three posts is about installing Windows 7 on an iSCSI disk. In this first article, we install it using qemu and iPXE and cover some of the pitfalls and particularities of this install method, as well as the topic of duplicating the resulting disk for use in machines of the same type.CYBERUS TECHNOLOGY
Volatility. Volatility is the tool to pick when analyzing physical memory, as it is not only able to determine the Windows version of the machine but can do a whole lot of things, including: creating a rough screenshot of what the desktop showed at the time the RAM was dumped: screenshot. extract the clipboard (copy/paste): clipboard.CYBERUS TECHNOLOGY
Volatility. Volatility is the tool to pick when analyzing physical memory, as it is not only able to determine the Windows version of the machine but can do a whole lot of things, including: creating a rough screenshot of what the desktop showed at the time the RAM was dumped: screenshot. extract the clipboard (copy/paste): clipboard.CYBERUS TECHNOLOGY
In times when working from home is ever more important there is a strong demand for video conferencing. Efficient video conferencing workloads require a lot of help from GPUs and GPU-heavy workloads have not been a lot of fun in VMs.CYBERUS TECHNOLOGY
Volatility. Volatility is the tool to pick when analyzing physical memory, as it is not only able to determine the Windows version of the machine but can do a whole lot of things, including: creating a rough screenshot of what the desktop showed at the time the RAM was dumped: screenshot. extract the clipboard (copy/paste): clipboard.CYBERUS TECHNOLOGY
Volatility. Volatility is the tool to pick when analyzing physical memory, as it is not only able to determine the Windows version of the machine but can do a whole lot of things, including: creating a rough screenshot of what the desktop showed at the time the RAM was dumped: screenshot. extract the clipboard (copy/paste): clipboard.CYBERUS TECHNOLOGY
In times when working from home is ever more important there is a strong demand for video conferencing. Efficient video conferencing workloads require a lot of help from GPUs and GPU-heavy workloads have not been a lot of fun in VMs. Impressum Datenschutz / Data ProtectionProducts
Consulting
Tech Blog
Press
Contact
Home Products Consulting About us Press Tech Blog__ @CyberusTech
__
RSS2.0 ATOM JSON
FEATURING TYCHO THE MALWARE LIVE ANALYSIS SUITE WE PROVIDE A WELL-INTEGRATED MALWARE LIVE-ANALYSIS PLATFORM AS A PRODUCT. PLEASE HAVE A LOOK AT OUR PRODUCT PAGE AND MAIL US AT SERVICE@CYBERUS-TECHNOLOGY.DE IF YOU HAVE ANY QUESTIONS! TYCHO PRODUCT INFORMATION INTEL CPU VULNERABILITIES DISCOVERED BY CYBERUS TECHNOLOGY Cyberus Technology co-discovered the Intel CPU vulnerabilities MELTDOWN and LAZYFP. See also our technical blog articles: * Article: One year after Meltdown of processor security * ZombieLoad vulnerability article * LazyFP vulnerability article * LazyFP vulnerability paper* Meltdown article
Cyberus Technology was founded by specialists sharing a common history in CPU design and research at Intel. If you need consulting around SECURING YOUR SOFTWARE SOLUTIONS AGAINST CPU VULNERABILITIES, or SECURE CPU DESIGN, don't hesitate to contact us!__ TEAM CYBERUS
Cyberus Technology GmbH is an innovative German IT-security company specializing on products that are based on secure virtualization technology and virtual machine introspection. Cyberus is part of the German _Alliance for Cyber-Security_.
More About Cyberus
__ TECH BLOG
Feel free to bookmark our tech blog, where we publish comprehensive information about newly discovered and published chip vulnerabilities, interesting use cases of our own products and technology, but also general auxillary technical thoughts and tutorials!Cyberus Tech Blog
CYBERUS CONSULTING SERVICES Deep level Software and Hardware expertise for complex Software projects and enhanced cyber security. LEARN NOW HOW WE CAN HELP YOU TO SECURE YOUR BUSINESS! Contact Cyberus ConsultingHow to reach us
* Cyberus Technology GmbH * __ service@cyberus-technology.de * __ +49 175 431 66 77 * __ Zwickauer Str. 46 · 01069 Dresden · GermanyNavigation
* Tycho
* Tech Blog
* Press
* About us
* Contact
* Impressum
* Datenschutz / Data ProtectionLatest posts
* General Availability of Cyberus Secure Virtualization Platform * Cyberus Technology Presents new Perspectives on Virtual Machine Introspection at Biggest German IT Security Congress * Cyberus Technology Gives Keynote at Symposium on the Science ofSecurity (HotSoS)
* Cyberus Secure Virtualization Platform: A technical perspective CYBERUS TECHNOLOGY GMBH Increasing MALWARE ANALYSTS productivity. Allrights reserved.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0