Are you over 18 and want to see adult content?
More Annotations

A complete backup of newdealdesign.com
Are you over 18 and want to see adult content?

A complete backup of limogesjewelry.com
Are you over 18 and want to see adult content?
A complete backup of bulletproofautomotive.com
Are you over 18 and want to see adult content?
A complete backup of lawanddisorder.org
Are you over 18 and want to see adult content?

A complete backup of 521qiangwweisizu.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://randomhistory.com
Are you over 18 and want to see adult content?
A complete backup of https://nokut.no
Are you over 18 and want to see adult content?

A complete backup of https://ispu.org
Are you over 18 and want to see adult content?
A complete backup of https://eureporter.co
Are you over 18 and want to see adult content?
A complete backup of https://realite-virtuelle.com
Are you over 18 and want to see adult content?
A complete backup of https://itbrief.com.au
Are you over 18 and want to see adult content?
A complete backup of https://claudi-vegan.de
Are you over 18 and want to see adult content?

A complete backup of https://t-a-s-c.com
Are you over 18 and want to see adult content?
A complete backup of https://gikostart.cz
Are you over 18 and want to see adult content?

A complete backup of https://kuehne-nagel.com
Are you over 18 and want to see adult content?
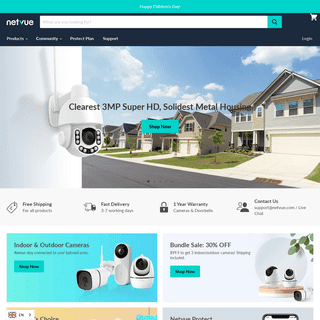
A complete backup of https://netvue.com
Are you over 18 and want to see adult content?
Text
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014 To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
HOWTO: MAKE YOUR OWN CERT WITH OPENSSL ON WINDOWS set RANDFILE=c:\demo\.rndset OPENSSL_CONF=C:\OpenSSL-Win32\bin\openssl.cfg. Now you can start OpenSSL, type: c:\OpenSSL-Win32\bin\openssl.exe: And from here on, the commands are the same as for my “Howto: Make Your Own Cert With OpenSSL”. First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key: !EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: WANNACRY’S MUTEX IS I've seen reports that WannaCry uses a mutex with name Global\MsWinZonesCacheCounterMutexA. The samples I analyzed all use another mutex: Global\MsWinZonesCacheCounterMutexA0. That's a digit zero at the end. I have not found a sample that uses mutex Global\MsWinZonesCacheCounterMutexA (e.g. without digit zero at theend). Update 1: I
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014 To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
HOWTO: MAKE YOUR OWN CERT WITH OPENSSL ON WINDOWS set RANDFILE=c:\demo\.rndset OPENSSL_CONF=C:\OpenSSL-Win32\bin\openssl.cfg. Now you can start OpenSSL, type: c:\OpenSSL-Win32\bin\openssl.exe: And from here on, the commands are the same as for my “Howto: Make Your Own Cert With OpenSSL”. First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key: !EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: WANNACRY’S MUTEX IS I've seen reports that WannaCry uses a mutex with name Global\MsWinZonesCacheCounterMutexA. The samples I analyzed all use another mutex: Global\MsWinZonesCacheCounterMutexA0. That's a digit zero at the end. I have not found a sample that uses mutex Global\MsWinZonesCacheCounterMutexA (e.g. without digit zero at theend). Update 1: I
DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: searchPDF STREAM OBJECTS
A PDF stream object is a sequence of bytes. There is a virtually unlimited number of ways to represent the same byte sequence. After Names and Strings obfuscation, let’s take a look at streams.. A PDF stream object is composed of a dictionary (>), the keyword stream, a sequence of bytes and the keyword endstream.All streams must beindirect objects.
HOWTO: MAKE YOUR OWN CERT WITH OPENSSL ON WINDOWS set RANDFILE=c:\demo\.rndset OPENSSL_CONF=C:\OpenSSL-Win32\bin\openssl.cfg. Now you can start OpenSSL, type: c:\OpenSSL-Win32\bin\openssl.exe: And from here on, the commands are the same as for my “Howto: Make Your Own Cert With OpenSSL”. First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key: QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
QUICKPOST: CREATING A SIMPLE FLOW GRAPH WITH GNU RADIO Double click the “RTL-SDR Source” block, and edit the Ch0 Frequency: 100.6e6 is 100600000 or 100.6 MHz (e6 is the exponent notation for 1000000, 6 zeroes). We can now save the flow graph. A flow graph has to be saved before it can be executed, if it is not saved, GNU Radio Companion will display a save dialog box when youexecute the flow
HOWTO: MAKE YOUR OWN CERT AND REVOCATION LIST WITH OPENSSL Here is a variant to my "Howto: Make Your Own Cert With OpenSSL" method. This time, I needed a signing cert with a Certificate Revocation List (CRL) extension and an (empty) CRL. I used instructions from this post. Adding a CRL extension to a certificateis not
QUICKPOST: WANNACRY’S MUTEX IS I've seen reports that WannaCry uses a mutex with name Global\MsWinZonesCacheCounterMutexA. The samples I analyzed all use another mutex: Global\MsWinZonesCacheCounterMutexA0. That's a digit zero at the end. I have not found a sample that uses mutex Global\MsWinZonesCacheCounterMutexA (e.g. without digit zero at theend). Update 1: I
QUICKPOST: ADDING CERTIFICATES TO THE CERTIFICATE STORE A couple of people asked me how to get self-signed certificates recognized by Windows. For example, when you check the digital signature of one of my programs (like ariad.exe), you'll see this: The digital signature is valid, but the root certificate used in the signature is not trusted. This is because this root certificate is INTEGRITY LEVELS AND DLL INJECTION Microsoft introduced a new kernel security feature with Windows Vista: Integrity Levels. Each process has an integrity level: Low, Medium, High or System. A process with a lower integrity level can't write to an object with a higher integrity level. For processes, this means that a process with low integrity level can't open a handleDIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 1 In this first example, I show how to decrypt a TLS stream with Wireshark. I made my example as such, that the encryption in this example is done with keys derived from a master secret. This master secret is derived from a pre-master secret, which is securely exchanged between the client and server using RSA WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014 To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead BPMTK | DIDIER STEVENS Filed under: bpmtk, Hacking, My Software, PDF, Update — Didier Stevens @ 19:32. There are no real changes in this new version of bpmtk, only a new DLL (hook-createprocess.dll) was added. You can use this DLL to protect your Windows machine from getting infected by the current malicious documents found in-the-wild. USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
NEW TOOL: XORSTRINGS New Tool: XORStrings. Filed under: Forensics, My Software, Reverse Engineering — Didier Stevens @ 0:00. XORStrings is best described as the combination of my XORSearch tool and the well-known strings command. XORStrings will search for strings in the (binary) file you provide it, using the same encodings as XORSearch (XOR, ROL, ROT andSHIFT).
SETDLLCHARACTERISTICS setdllcharacteristics. Filed under: My Software, Windows 7, Windows Vista — Didier Stevens @ 20:39. The PE-file format specifies flags to enable DEP and ASLR. You can set these flags with a hex-editor or a PE-file editor. Because I need to set DEP and ASLR flags in a script, I wrote a C-program to read, set or clear these flags (together with QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 1 In this first example, I show how to decrypt a TLS stream with Wireshark. I made my example as such, that the encryption in this example is done with keys derived from a master secret. This master secret is derived from a pre-master secret, which is securely exchanged between the client and server using RSA WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014 To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead BPMTK | DIDIER STEVENS Filed under: bpmtk, Hacking, My Software, PDF, Update — Didier Stevens @ 19:32. There are no real changes in this new version of bpmtk, only a new DLL (hook-createprocess.dll) was added. You can use this DLL to protect your Windows machine from getting infected by the current malicious documents found in-the-wild. USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
NEW TOOL: XORSTRINGS New Tool: XORStrings. Filed under: Forensics, My Software, Reverse Engineering — Didier Stevens @ 0:00. XORStrings is best described as the combination of my XORSearch tool and the well-known strings command. XORStrings will search for strings in the (binary) file you provide it, using the same encodings as XORSearch (XOR, ROL, ROT andSHIFT).
SETDLLCHARACTERISTICS setdllcharacteristics. Filed under: My Software, Windows 7, Windows Vista — Didier Stevens @ 20:39. The PE-file format specifies flags to enable DEP and ASLR. You can set these flags with a hex-editor or a PE-file editor. Because I need to set DEP and ASLR flags in a script, I wrote a C-program to read, set or clear these flags (together with QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 2 In blog post "Decrypting TLS Streams With Wireshark: Part 1", I explain how to decrypt TLS streams with a specific type of encryption (pre-master secret exchanged via RSA) using the web server's private key. In this blog post, we will use the client to get the necessary information to decrypt TLS streams. We do this WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search DIDIER STEVENS SUITE Fyi, Palo Alto Wildfire blocked download of zip due to AnalyzePESig-crt-auto-x86.exe detected as malware. Comment by Anonymous — Friday 25 November 2016 @ 13:47 OBTAINING MALWARE SAMPLES FOR ANALYSIS Obtaining Malware Samples for Analysis. Filed under: Announcement, Malware — Didier Stevens @ 0:00. In my malware analysis blog posts and videos, I always try to include the hash or VirusTotal link of the sample (s) I analyze. If I don’t, it means I’m not at liberty toshare the hash.
THE CASE OF THE MISSING DIGITAL SIGNATURES TAB The title of this post is inspired by Mark Russinovich's posts. I explain why there is a category of executables with a digital signature that don't show a “Digital Signatures” tab in the properties dialog, and I release a tool to manipulate digital signatures. Executables (PE files) can have a digital signature, Microsoft calls this QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can DECRYPTING TLS STREAMS WITH WIRESHARK: PART 1 In this first example, I show how to decrypt a TLS stream with Wireshark. I made my example as such, that the encryption in this example is done with keys derived from a master secret. This master secret is derived from a pre-master secret, which is securely exchanged between the client and server using RSA WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014 To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead BPMTK | DIDIER STEVENS Filed under: bpmtk, Hacking, My Software, PDF, Update — Didier Stevens @ 19:32. There are no real changes in this new version of bpmtk, only a new DLL (hook-createprocess.dll) was added. You can use this DLL to protect your Windows machine from getting infected by the current malicious documents found in-the-wild. USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
NEW TOOL: XORSTRINGS New Tool: XORStrings. Filed under: Forensics, My Software, Reverse Engineering — Didier Stevens @ 0:00. XORStrings is best described as the combination of my XORSearch tool and the well-known strings command. XORStrings will search for strings in the (binary) file you provide it, using the same encodings as XORSearch (XOR, ROL, ROT andSHIFT).
SETDLLCHARACTERISTICS setdllcharacteristics. Filed under: My Software, Windows 7, Windows Vista — Didier Stevens @ 20:39. The PE-file format specifies flags to enable DEP and ASLR. You can set these flags with a hex-editor or a PE-file editor. Because I need to set DEP and ASLR flags in a script, I wrote a C-program to read, set or clear these flags (together with QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014ADD EXCEL STRINGEXCEL STRING FIND To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
!EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWSWINDOWS LSASSPROCESS
I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014ADD EXCEL STRINGEXCEL STRING FIND To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
!EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWSWINDOWS LSASSPROCESS
I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
QUICKPOST: CREATING A SIMPLE FLOW GRAPH WITH GNU RADIO Double click the “RTL-SDR Source” block, and edit the Ch0 Frequency: 100.6e6 is 100600000 or 100.6 MHz (e6 is the exponent notation for 1000000, 6 zeroes). We can now save the flow graph. A flow graph has to be saved before it can be executed, if it is not saved, GNU Radio Companion will display a save dialog box when youexecute the flow
USING METASPLOIT ON WINDOWS hello, lovely post but I can’t follow. this is the location of my metasploit C:\metasploit-framework, even here there is nothing but 3 folders, Bin, embedded and liscense. HOWTO: MAKE YOUR OWN CERT WITH OPENSSL ON WINDOWS set RANDFILE=c:\demo\.rndset OPENSSL_CONF=C:\OpenSSL-Win32\bin\openssl.cfg. Now you can start OpenSSL, type: c:\OpenSSL-Win32\bin\openssl.exe: And from here on, the commands are the same as for my “Howto: Make Your Own Cert With OpenSSL”. First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key: QUICKPOST: BROWSERS & CONTENT-DISPOSITION A quick check confirmed that response header Content-Disposition can direct browsers to display or save a file. I used my tcp-honeypot.py to serve 3 HTTP responses: HTTP/1.1 200 OK Content-Disposition: inline Line 1 Line 2 Line 3 HTTP/1.1 200 OK Content-Disposition: attachment Line 1 Line 2 Line 3 HTTP/1.1 200 OK Content-Disposition: attachment; SETDLLCHARACTERISTICS setdllcharacteristics. Filed under: My Software, Windows 7, Windows Vista — Didier Stevens @ 20:39. The PE-file format specifies flags to enable DEP and ASLR. You can set these flags with a hex-editor or a PE-file editor. Because I need to set DEP and ASLR flags in a script, I wrote a C-program to read, set or clear these flags (together with QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
PRACTICE NTDS.DIT FILE PART 3: PASSWORD CRACKING WITH Now we will use hashcat and the rockyou wordlist to crack the passwords for the hashes we extracted in part 2. With this command we let hashcat work on the LM hashes we extracted: hashcat-3.00\hashcat64.exe -a 0 -m 3000 --potfile-path hashcat-rockyou-lm.pot --username lm.ocl.out rockyou.txt Option -a 0 instructs hashcat to perform a straight attack.DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014ADD EXCEL STRINGEXCEL STRING FIND To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
!EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWSWINDOWS LSASSPROCESS
I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
DIDIER STEVENS
Filed under: My Software, Update — Didier Stevens @ 0:00. This new version of base64dump.py supports a new encoding: NETBIOS Name encoding. NETBIOS Name encoding is very similar to hexadecimal encoding: in stead of hexadecimal digits 0-9 and a-f, letters A-P are used. I encountered this in DNS TXT records of a Cobalt Strike DNSstager.
UPDATE: CMD.DLL VERSION 0.0.5 Update: cmd.dll Version 0.0.5. Filed under: My Software, Update — Didier Stevens @ 15:24. I noticed that I didn’t post the latest version of my cmd.dll program. And I looked into moving this code to the new ReactOS builder, but that still does not offer 64-bit builds, thus I’m postponing this migration. cmd-dll_v0_0_5.zip ( https) CRACKING VBA PROJECT PASSWORDS VBA projects can be protected with a password. The password is not used to encrypt the content of the VBA project, it is just used as protection by the VBA IDE: when the password is set, you will be prompted for the password. Tools like oledump.py are not hindered by a VBA password, they can WEBDAV TRAFFIC TO MALICIOUS SITES I observed WebDAV traffic to malicious sites in the past (in proxy logs), and recently I took some time to take a closer look.. TL;DR: when files are retrieved remotely with the file:// URI scheme on Windows, Windows will fallback to WebDAV when SMB connections can not be established.. I did my tests with 2 Windows 7 VMs on the same subnet, one Windows 7 machine with IIS/WebDAV, and the EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by QUICKPOST: USER-AGENT: MICROSOFT OFFICE EXCEL 2014ADD EXCEL STRINGEXCEL STRING FIND To start: there is no version 2014 of Microsoft Office. That's why I was intrigued when I saw User Agent String "Microsoft Office Excel 2014" appearing in Wireshark when I did some tests with Excel's data importing features. With Excel 2019, when I get data from a CSV file and provide an URL (in stead USING METASPLOIT ON WINDOWS In my previous post “Reading Memory Of 64-bit Processes” I used the Windows version of Metasploit so that I could do all tests with a single machine: running the Meterpreter client and TEST FILE: PDF WITH EMBEDDED DOC DROPPING EICAR Over at the SANS ISC diary I wrote a diary entry on the analysis of a PDF file that contains a malicious DOC file. For testing purposes, I created a PDF file that contains a DOC file that drops the EICAR test file. The PDF file contains JavaScript that extracts and opens the DOCfile
!EXPLOITABLE CRASH ANALYZER Regularly when I use Microsoft MSEC’s !exploitable WinDbg extension, it doesn’t load because the correct VC runtime is not installed (vcredist 2012) on the machine I'm debugging on. Since it’s open-source, I decided to recompile it with a statically linked C runtime, making it independent of the installed runtime(s). I used Visual Studio 2017 and QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWSWINDOWS LSASSPROCESS
I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
EICARGEN | DIDIER STEVENS EICARgen is just a program that creates the EICAR Anti-Virus test file. The EICAR Anti-Virus test file is 68 bytes long, and it will cause all Anti-Virus software to trigger a virus alert. Of course, this EICAR file is not a virus, it's just an industry-standard test file. The EICAR file is only detected by ANALYZING .DWG FILES WITH EMBEDDED VBA MACROS AutoCAD's drawing files (.dwg) can contain VBA macros. The .dwg format is a proprietary file format. There is some documentation, for example here. When VBA macros are stored inside a .dwg file, an OLE file is embedded inside the .dwg file. There's a quick-and-dirty way to find this embedded file inside the .dwg file: search QUICKPOST: USING CLAMAV ON WINDOWS This is how I deploy and configure ClamAV on Windows: I download the portable Windows x64 version in a ZIP file (clamav-0.99.2-x64.zip). I extract the content of this ZIP file to folder c:\portable\, this will create a subfolder ClamAV-x64 containing ClamAV. Then I copy the 2 samples for the config files: copy c:\portable\ClamAV-x64\conf_examples\clamd.conf.samplec:\portable\ClamAV
QUICKPOST: CREATING A SIMPLE FLOW GRAPH WITH GNU RADIO Double click the “RTL-SDR Source” block, and edit the Ch0 Frequency: 100.6e6 is 100600000 or 100.6 MHz (e6 is the exponent notation for 1000000, 6 zeroes). We can now save the flow graph. A flow graph has to be saved before it can be executed, if it is not saved, GNU Radio Companion will display a save dialog box when youexecute the flow
USING METASPLOIT ON WINDOWS hello, lovely post but I can’t follow. this is the location of my metasploit C:\metasploit-framework, even here there is nothing but 3 folders, Bin, embedded and liscense. HOWTO: MAKE YOUR OWN CERT WITH OPENSSL ON WINDOWS set RANDFILE=c:\demo\.rndset OPENSSL_CONF=C:\OpenSSL-Win32\bin\openssl.cfg. Now you can start OpenSSL, type: c:\OpenSSL-Win32\bin\openssl.exe: And from here on, the commands are the same as for my “Howto: Make Your Own Cert With OpenSSL”. First we generate a 4096-bit long RSA key for our root CA and store it in file ca.key: QUICKPOST: BROWSERS & CONTENT-DISPOSITION A quick check confirmed that response header Content-Disposition can direct browsers to display or save a file. I used my tcp-honeypot.py to serve 3 HTTP responses: HTTP/1.1 200 OK Content-Disposition: inline Line 1 Line 2 Line 3 HTTP/1.1 200 OK Content-Disposition: attachment Line 1 Line 2 Line 3 HTTP/1.1 200 OK Content-Disposition: attachment; SETDLLCHARACTERISTICS setdllcharacteristics. Filed under: My Software, Windows 7, Windows Vista — Didier Stevens @ 20:39. The PE-file format specifies flags to enable DEP and ASLR. You can set these flags with a hex-editor or a PE-file editor. Because I need to set DEP and ASLR flags in a script, I wrote a C-program to read, set or clear these flags (together with QUICKPOST: SELECTMYPARENT OR PLAYING WITH THE WINDOWS I read something very interesting in "Windows via C/C++" today: starting with Windows Vista, CreateProcess can start a program where you specify the parent process! This is something forensic investigators must be aware of when they analyse processes running on a Windows machine. Normally the parent process of a new process is theprocess that
PRACTICE NTDS.DIT FILE PART 3: PASSWORD CRACKING WITH Now we will use hashcat and the rockyou wordlist to crack the passwords for the hashes we extracted in part 2. With this command we let hashcat work on the LM hashes we extracted: hashcat-3.00\hashcat64.exe -a 0 -m 3000 --potfile-path hashcat-rockyou-lm.pot --username lm.ocl.out rockyou.txt Option -a 0 instructs hashcat to perform a straight attack. You will be redirected to my blog http://blog.DidierStevens.com in 30seconds.
* My company http://DidierStevensLabs.com * My blog http://blog.DidierStevens.com * My software http://blog.didierstevens.com/my-software * Didier Stevens Suite http://blog.didierstevens.com/didier-stevens-suite/ * My YouTube channel https://youtube.com/dist67 * My videoblog http://videos.DidierStevens.com * My GitHub https://github.com/DidierStevens * About me http://blog.DidierStevens.com/about * Email didier.stevens@gmail.com -----BEGIN PGP PUBLIC KEY BLOCK----- Version: GnuPG v1.4.7 (MingW32) mQGiBEcg+PERBAC7Zex85WF3yfmGOfGjAMLsNx6y39rrmUjtNeGdHaFOS+RO2KQ9 19sXx5V42BVtsDae5qGFkAfdYi9uWiTiPHI4C3JXSnsVx1IHd4/Hr4vC/rncSwe/ emajuorUJwAB3FmWQm2lzSuS6FJNzpARGMH4X15O+dFy0pr0nJ79IFPO8wCghM5S yA8vcSvCDJ8bsKHruIpyN6MD/0GMNI3wK3Pb5OVJFDxVWQLrMaA8gdQBTiZ42aW+ 2rsyr1d61e94Nvurs0FwohzllfPyjX+NuiWcjlho2jnpkUO/iC/HcNzCAi3qN2Vv q6EfL8r7XVy/lG+OGhvYSnQU2GZjJyIltYjyKyhHD5P2GlBu9BSqN06bFgOdXcmB Bgb4A/9BqxOx8a+X3GiV1H+dnNfL7jS2CoH43Z3aXYCWgqMxEuvXvIrIPa6XAYNo /F5UGkONknBjxC/Pr9w/jORC8oW0AYZJlHmpTQOHedgsrCBPXmyYSu/pafS6O2V9 w5BGLpkmTQAX/Hr/DuGD0JGqVcOvGhVAgcrdBxDfEMNti+Lbw7QpRGlkaWVyIFN0 ZXZlbnMgPGRpZGllci5zdGV2ZW5zQGdtYWlsLmNvbT6IYAQTEQIAIAUCRyD48QIb AwYLCQgHAwIEFQIIAwQWAgMBAh4BAheAAAoJEHdz1uvbYxaW5iwAnRJp2jEfQ6h7 cvv4VT86VG6QzBzzAJ9l1FLWhOHDofRUAhZdYSLZjnURSbkCDQRHIPjxEAgAt21C uJWdsVbhnOOO/bfMuQOUrceh0DUDuO76QWrQSxz/vFSrVxBtSKct9GTICEk+3GXQ I1pmuxkAYcr3J1G36bKoPnMyX7x/+tJC+WkoroKzTVMlahdFjmI04Tc8iBYTwROn 8i6J5l9hoaNKLKfdV6Xmw0Y7A9w9wVRo09NkJiSzff3iQbis0mrh/jxup1coa4L+ 4FBjIHztt+7LXfwqKqBM1OnXvLPlSTJT4/KjRnCdNDy+zxz6g6Yzy4NNTcP0+EFr CijuE7/jLZho6P79Qt2nfe2O9BTQW6jIFaF2guvGMsEqgX9MtWxnd+P7KSz+1CtL sYkfiEdF8qp8ubHiswADBQf/XuRea1pMXKUs3f//Y7GRWtm2s9jPY5uSYqY7XaOm lsEflToedo8KxfymgA3axyI2QwxTEBnanPJQdPPd/vBSBCKmp5ihsFcKO30AKtbC J5SFRzTJmjwtaSRjI4CMZbIJCjb7uCSzF6ylEGIBypt+MbBXEhmGsv886Sm5PpR/ vXfZdtzFxMILJ8wgxSh5wtQ+rZHZUsPRszb45fUuaSPquStpndqp/Stx14s1LfGg Inpxn3eh+sz6iksaIb9mDZ5jcuRTx9rH43TkZRpdvk3WIHBo/6YFdOZUEhzKLYnO Fmjssq5wXIt2inj+C6H9kgLOYhb+bj8+GbdNhQT5oXH4EIhJBBgRAgAJBQJHIPjx AhsMAAoJEHdz1uvbYxaWAWoAoIH4MxPReBq32E2gmqrzOXXcL6BkAJ9L6FXNh9pH x7z8V6php7uMJQX6UA===8AJk
-----END PGP PUBLIC KEY BLOCK-----Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0