Are you over 18 and want to see adult content?
More Annotations

A complete backup of visitaikensc.com
Are you over 18 and want to see adult content?

A complete backup of arnoldfoundation.org
Are you over 18 and want to see adult content?
A complete backup of makingsenseofcents.com
Are you over 18 and want to see adult content?

A complete backup of educationnorthwest.org
Are you over 18 and want to see adult content?
A complete backup of articlecounty.com
Are you over 18 and want to see adult content?
A complete backup of apartmentcareers.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://nightline.ac.uk
Are you over 18 and want to see adult content?
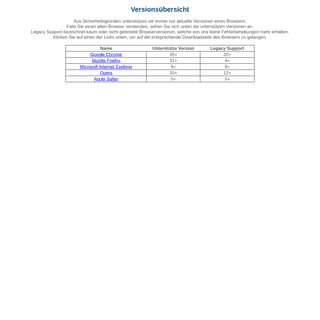
A complete backup of https://handy-signatur.at
Are you over 18 and want to see adult content?

A complete backup of https://v-like.ru
Are you over 18 and want to see adult content?

A complete backup of https://olivercabell.com
Are you over 18 and want to see adult content?

A complete backup of https://simonhearne.com
Are you over 18 and want to see adult content?
A complete backup of https://kallandet.se
Are you over 18 and want to see adult content?
A complete backup of https://fileden.com
Are you over 18 and want to see adult content?
A complete backup of https://cedgreentech.com
Are you over 18 and want to see adult content?
A complete backup of https://giampsproject.com
Are you over 18 and want to see adult content?

A complete backup of https://genericmedsbuy.com
Are you over 18 and want to see adult content?

A complete backup of https://relaxlikeaboss.com
Are you over 18 and want to see adult content?
Text
ETUTORIALS.ORG
TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
BUILDING YOUR FIRST COMPONENT :: CHAPTER 9: WRITING DELPHI Building Your First Component. Building components is an important activity for Delphi programmers. Basically, any time you need the same behavior in two different places in an application, or in two different applications, you can place the shared code in a class—or, even better, in a component. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API PELTIER MODULES :: CHAPTER 11: PROBLEMS WITH USING Here, q is the electric charge (q = I × t), and P is the so-called Peltier factor, the value of which depends both on the properties of the dissimilar materials carrying the current and on their temperatures. Peltier heat is positive if it is released; otherwise, it is negative. In the experiment conducted as shown in Fig. 11.1, the same Joule heat will be released in each calorimeter if both DELPHI'S WEBBROKER TECHNOLOGY :: CHAPTER 20: WEB Delphi's WebBroker Technology. The CGI code snippet I've shown you demonstrates the plain, direct approach to this protocol. I could have provided similar low-level examples for ISAPI or Apache modules, but in Delphi it's more interesting to use the WebBroker technology. UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. PRIVILEGED EXEC ACCESS :: CHAPTER 3. ACCESSING A ROUTER The level keyword specifies the level of access that you assign to the command(s). This can be from 0 to 15, where 1 is user EXEC and 15 is privileged EXEC, by default. Instead of specifying the level keyword, you can use reset; this keyword resets the privilege level of the command(s) to the default privilege level and removes the privilege command from the router's configuration. USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
BUILDING YOUR FIRST COMPONENT :: CHAPTER 9: WRITING DELPHI Building Your First Component. Building components is an important activity for Delphi programmers. Basically, any time you need the same behavior in two different places in an application, or in two different applications, you can place the shared code in a class—or, even better, in a component. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API PELTIER MODULES :: CHAPTER 11: PROBLEMS WITH USING Here, q is the electric charge (q = I × t), and P is the so-called Peltier factor, the value of which depends both on the properties of the dissimilar materials carrying the current and on their temperatures. Peltier heat is positive if it is released; otherwise, it is negative. In the experiment conducted as shown in Fig. 11.1, the same Joule heat will be released in each calorimeter if both DELPHI'S WEBBROKER TECHNOLOGY :: CHAPTER 20: WEB Delphi's WebBroker Technology. The CGI code snippet I've shown you demonstrates the plain, direct approach to this protocol. I could have provided similar low-level examples for ISAPI or Apache modules, but in Delphi it's more interesting to use the WebBroker technology. UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. PRIVILEGED EXEC ACCESS :: CHAPTER 3. ACCESSING A ROUTER The level keyword specifies the level of access that you assign to the command(s). This can be from 0 to 15, where 1 is user EXEC and 15 is privileged EXEC, by default. Instead of specifying the level keyword, you can use reset; this keyword resets the privilege level of the command(s) to the default privilege level and removes the privilege command from the router's configuration. USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY AND An RF signal is an electromagnetic wave that communications systems use to transport information through air from one point to another. RF signals have been in use for many years. They provide the means for carrying music to FM radios and video to televisions. In fact, RF signals are the most common means for carrying data over a wirelessnetwork.
ASSOCIATION CLASS :: CHAPTER 6. CLASS DIAGRAMS: ADVANCED Association Classes Uml. Association classes allow you to add attributes, operations, and other features to associations, as shown in Figure 6-14.. Figure 6-14. Association Class. We can see from the diagram that a Person may work for a single Company. TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. 6.10 CUSTOM ACTIONS :: CHAPTER 6. SETUP AND DEPLOYMENT If you have supplied an .exe, .dll, or script file for the sole purpose of providing a custom install action, it is not necessary to copy the file to the target machine as part of the installation.Although the file must be present in the File System view to be used as a custom action, CHAPTER 3: SOURCES OF INACCURATE DATA :: PART I Chapter 3: Sources of Inaccurate Data Before we can assess data correctness we need to understand the various ways inaccurate values get into databases. There are many sources of data inaccuracies, and each contributes its own part to the total data quality problem. CHAPTER 2. LAN SWITCH ARCHITECTURE :: LAN SWITCHING Chapter 2 introduces many of the concepts behind LAN switching common to all switch vendors. The chapter begins by looking at how data are received by a switch, followed by mechanisms used to switch data as efficiently as possible, and concludes with forwarding data toward their destinations. These concepts are not specific to Cisco and are BGP EXTENDED COMMUNITY ATTRIBUTE :: CHAPTER 9. MPLS/VPN Figure 9-6 illustrates this concept, and shows a site connected to two separate PE-routers and the behavior of the PE-router when a route is received that contains a SOO extended community that matches the one configured for the VRF. WIRELESS LAN COMPONENTS :: CHAPTER 5. WIRELESS LANS Wireless LANs consist of components similar to traditional Ethernet-wired LANs. In fact, wireless LAN protocols are similar to Ethernet and comply with the same form factors. RELATIONSHIP BETWEEN WI-FI AND IEEE 802.11 :: CHAPTER 7 The Institute of Electrical and Electronics Engineers (www.IEEE.org) operates a group called the Standards Association (SA). Among many other standards, the IEEE-SA is responsible for the IEEE 802 family: "Local Area and Metropolitan Area Networks." UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
BUILDING YOUR FIRST COMPONENT :: CHAPTER 9: WRITING DELPHI Building Your First Component. Building components is an important activity for Delphi programmers. Basically, any time you need the same behavior in two different places in an application, or in two different applications, you can place the shared code in a class—or, even better, in a component. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API PELTIER MODULES :: CHAPTER 11: PROBLEMS WITH USING Here, q is the electric charge (q = I × t), and P is the so-called Peltier factor, the value of which depends both on the properties of the dissimilar materials carrying the current and on their temperatures. Peltier heat is positive if it is released; otherwise, it is negative. In the experiment conducted as shown in Fig. 11.1, the same Joule heat will be released in each calorimeter if both DELPHI'S WEBBROKER TECHNOLOGY :: CHAPTER 20: WEB Delphi's WebBroker Technology. The CGI code snippet I've shown you demonstrates the plain, direct approach to this protocol. I could have provided similar low-level examples for ISAPI or Apache modules, but in Delphi it's more interesting to use the WebBroker technology. UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. PRIVILEGED EXEC ACCESS :: CHAPTER 3. ACCESSING A ROUTER The level keyword specifies the level of access that you assign to the command(s). This can be from 0 to 15, where 1 is user EXEC and 15 is privileged EXEC, by default. Instead of specifying the level keyword, you can use reset; this keyword resets the privilege level of the command(s) to the default privilege level and removes the privilege command from the router's configuration. USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
BUILDING YOUR FIRST COMPONENT :: CHAPTER 9: WRITING DELPHI Building Your First Component. Building components is an important activity for Delphi programmers. Basically, any time you need the same behavior in two different places in an application, or in two different applications, you can place the shared code in a class—or, even better, in a component. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API PELTIER MODULES :: CHAPTER 11: PROBLEMS WITH USING Here, q is the electric charge (q = I × t), and P is the so-called Peltier factor, the value of which depends both on the properties of the dissimilar materials carrying the current and on their temperatures. Peltier heat is positive if it is released; otherwise, it is negative. In the experiment conducted as shown in Fig. 11.1, the same Joule heat will be released in each calorimeter if both DELPHI'S WEBBROKER TECHNOLOGY :: CHAPTER 20: WEB Delphi's WebBroker Technology. The CGI code snippet I've shown you demonstrates the plain, direct approach to this protocol. I could have provided similar low-level examples for ISAPI or Apache modules, but in Delphi it's more interesting to use the WebBroker technology. UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. PRIVILEGED EXEC ACCESS :: CHAPTER 3. ACCESSING A ROUTER The level keyword specifies the level of access that you assign to the command(s). This can be from 0 to 15, where 1 is user EXEC and 15 is privileged EXEC, by default. Instead of specifying the level keyword, you can use reset; this keyword resets the privilege level of the command(s) to the default privilege level and removes the privilege command from the router's configuration. USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY AND An RF signal is an electromagnetic wave that communications systems use to transport information through air from one point to another. RF signals have been in use for many years. They provide the means for carrying music to FM radios and video to televisions. In fact, RF signals are the most common means for carrying data over a wirelessnetwork.
ASSOCIATION CLASS :: CHAPTER 6. CLASS DIAGRAMS: ADVANCED Association Classes Uml. Association classes allow you to add attributes, operations, and other features to associations, as shown in Figure 6-14.. Figure 6-14. Association Class. We can see from the diagram that a Person may work for a single Company. TYPES OF SECURITY THREATS :: CHAPTER 1. SECURITY THREATS Unstructured and Structured Threats. General methods of security threats fall under two categories: Unstructured threats. Structured threats. An unstructured security threat is one created by an inexperienced person who is trying to gain access to your network?awannabe hacker.
UNDERSTANDING DB2 QUERY ACCESS PLANS :: CHAPTER 6. THE DB2 The total execution time is for all executions of the statement. Even though a statement may have a total execution time of 5,000 seconds, if it was run 20,000 times, this is not excessive. 6.10 CUSTOM ACTIONS :: CHAPTER 6. SETUP AND DEPLOYMENT If you have supplied an .exe, .dll, or script file for the sole purpose of providing a custom install action, it is not necessary to copy the file to the target machine as part of the installation.Although the file must be present in the File System view to be used as a custom action, CHAPTER 3: SOURCES OF INACCURATE DATA :: PART I Chapter 3: Sources of Inaccurate Data Before we can assess data correctness we need to understand the various ways inaccurate values get into databases. There are many sources of data inaccuracies, and each contributes its own part to the total data quality problem. CHAPTER 2. LAN SWITCH ARCHITECTURE :: LAN SWITCHING Chapter 2 introduces many of the concepts behind LAN switching common to all switch vendors. The chapter begins by looking at how data are received by a switch, followed by mechanisms used to switch data as efficiently as possible, and concludes with forwarding data toward their destinations. These concepts are not specific to Cisco and are BGP EXTENDED COMMUNITY ATTRIBUTE :: CHAPTER 9. MPLS/VPN Figure 9-6 illustrates this concept, and shows a site connected to two separate PE-routers and the behavior of the PE-router when a route is received that contains a SOO extended community that matches the one configured for the VRF. WIRELESS LAN COMPONENTS :: CHAPTER 5. WIRELESS LANS Wireless LANs consist of components similar to traditional Ethernet-wired LANs. In fact, wireless LAN protocols are similar to Ethernet and comply with the same form factors. RELATIONSHIP BETWEEN WI-FI AND IEEE 802.11 :: CHAPTER 7 The Institute of Electrical and Electronics Engineers (www.IEEE.org) operates a group called the Standards Association (SA). Among many other standards, the IEEE-SA is responsible for the IEEE 802 family: "Local Area and Metropolitan Area Networks." UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
UPDATING THE DATA :: CHAPTER 15: WORKING WITH ADO :: PART However, with a little knowledge and ingenuity you can implement a suitable ADOUpdatesPending function. The necessary knowledge is that ADO datasets have a property called FilterGroup, which is a kind of filter.Unlike a dataset's Filter property, which filters the data based on a comparison of the data against a condition, FilterGroup filters based on the status of the record. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API 2.5 JAVA SOURCE FILE STRUCTURE :: CHAPTER 2. LANGUAGE The structure of a skeletal Java source file is depicted in Figure 2.2. A Java source file can have the following elements that, if present, must be specified in the following order: CREATING A DLL IN DELPHI :: CHAPTER 10: LIBRARIES AND Your First Delphi DLL. As a starting point in exploring the development of DLLs in Delphi, I'll show you a library built in Delphi. The primary focus of this example will be to show the syntax you use to define a DLL in Delphi, but it will also illustrate a few considerations involved in passing string parameters. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. THE ROLE OF HEADING STYLES AND OUTLINE LEVELS IN OUTLINING To understand outlining, you must understand three concepts: heading styles, outline levels, and body text. Heading styles are built-in styles that Word provides for each level of heading in your document, from Heading 1 to Heading 9. These styles don't just carry formatting information; they also carry information about where the text fits in the hierarchy of your document. 6.5 PROJECT PROPERTIES AND CONDITIONS :: CHAPTER 6. SETUP It is often necessary for one stage of the installation process to pass information to a later stage. For example, the data collected from the user prior to installation usually needs to be available to the installation phase. REVIEW QUESTIONS :: CHAPTER 5. CONTROL FLOW, EXCEPTION 5.24: Assuming assertions are enabled, which of these assertion statements will throw an error? Select the two correct answers. asserttrue : true;
UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
UPDATING THE DATA :: CHAPTER 15: WORKING WITH ADO :: PART However, with a little knowledge and ingenuity you can implement a suitable ADOUpdatesPending function. The necessary knowledge is that ADO datasets have a property called FilterGroup, which is a kind of filter.Unlike a dataset's Filter property, which filters the data based on a comparison of the data against a condition, FilterGroup filters based on the status of the record. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API 2.5 JAVA SOURCE FILE STRUCTURE :: CHAPTER 2. LANGUAGE The structure of a skeletal Java source file is depicted in Figure 2.2. A Java source file can have the following elements that, if present, must be specified in the following order: CREATING A DLL IN DELPHI :: CHAPTER 10: LIBRARIES AND Your First Delphi DLL. As a starting point in exploring the development of DLLs in Delphi, I'll show you a library built in Delphi. The primary focus of this example will be to show the syntax you use to define a DLL in Delphi, but it will also illustrate a few considerations involved in passing string parameters. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. THE ROLE OF HEADING STYLES AND OUTLINE LEVELS IN OUTLINING To understand outlining, you must understand three concepts: heading styles, outline levels, and body text. Heading styles are built-in styles that Word provides for each level of heading in your document, from Heading 1 to Heading 9. These styles don't just carry formatting information; they also carry information about where the text fits in the hierarchy of your document. 6.5 PROJECT PROPERTIES AND CONDITIONS :: CHAPTER 6. SETUP It is often necessary for one stage of the installation process to pass information to a later stage. For example, the data collected from the user prior to installation usually needs to be available to the installation phase. REVIEW QUESTIONS :: CHAPTER 5. CONTROL FLOW, EXCEPTION 5.24: Assuming assertions are enabled, which of these assertion statements will throw an error? Select the two correct answers. asserttrue : true;
6.10 CUSTOM ACTIONS :: CHAPTER 6. SETUP AND DEPLOYMENT If you have supplied an .exe, .dll, or script file for the sole purpose of providing a custom install action, it is not necessary to copy the file to the target machine as part of the installation.Although the file must be present in the File System view to be used as a custom action, CHAPTER 1. NETWORKING BASICS :: LAN SWITCHING FIRST-STEP Lan switching first-step. Chapter 1. Networking Basics. What You Will Learn. On completing this chapter, you will be able to: List the basic characteristics of a network. List the major physical and logical components of a network. Describe three modes of data transmission. Describe the three basic types of logical networks. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. CHAPTER 9. ACTIVITY DIAGRAMS :: UML The activity diagram describes the sequencing of activities, with support for both conditional and parallel behavior. An activity diagram is a variant of a state diagram in which most, if not all, the states are activity states. Thus, much of the terminology follows that of state diagrams. Conditional behavior is delineated by branches andmerges.
USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. CONCURRENT STATE DIAGRAMS :: CHAPTER 8. STATE DIAGRAMS Concurrent state diagrams are useful when a given object has sets of independent behaviors. Note, however, that you should not get too many concurrent sets of behaviors occurring in a single object. If you have several complicated concurrent state diagrams for an object, you should consider splitting the object into separate objects. DEFINING THE MISSION OBJECTIVES :: CHAPTER 5. STARTING THE To expand upon the overview in the previous chapter, mission objectives are statements that represent the general tasks supported by the data maintained in the database. Each mission objective represents a single task. These mission objectives provide informationthat
CHAPTER 18: DNS AND NIS :: PART III: INTERNETWORKING WITH Overview. Secrets in This Chapter. Using the Domain Name System (DNS) Understanding Hierarchical Domain Names. Learning More about DNS and BIND. Understanding named-the BIND Name Server RECIPE 17.6 PRINT AN ACCESS REPORT FROM .NET WINDOWS FORM Double-click the cmdRunReport button control to jump to the code editor window. Select Project Add Reference to display the Visual Studio .NET Add Reference dialog box.. Click the COM tab, select "Microsoft Access 11.0 Object Library" from the upper listbox, and click the Select button as WHY KEYS ARE IMPORTANT :: CHAPTER 8. KEYS :: PART II: THE Keys are crucial to a table structure for the following reasons: They ensure that each record in a table is precisely identified. As you already know, a table represents a singular collection of UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
UPDATING THE DATA :: CHAPTER 15: WORKING WITH ADO :: PART However, with a little knowledge and ingenuity you can implement a suitable ADOUpdatesPending function. The necessary knowledge is that ADO datasets have a property called FilterGroup, which is a kind of filter.Unlike a dataset's Filter property, which filters the data based on a comparison of the data against a condition, FilterGroup filters based on the status of the record. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API 2.5 JAVA SOURCE FILE STRUCTURE :: CHAPTER 2. LANGUAGE The structure of a skeletal Java source file is depicted in Figure 2.2. A Java source file can have the following elements that, if present, must be specified in the following order: CREATING A DLL IN DELPHI :: CHAPTER 10: LIBRARIES AND Your First Delphi DLL. As a starting point in exploring the development of DLLs in Delphi, I'll show you a library built in Delphi. The primary focus of this example will be to show the syntax you use to define a DLL in Delphi, but it will also illustrate a few considerations involved in passing string parameters. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. THE ROLE OF HEADING STYLES AND OUTLINE LEVELS IN OUTLINING To understand outlining, you must understand three concepts: heading styles, outline levels, and body text. Heading styles are built-in styles that Word provides for each level of heading in your document, from Heading 1 to Heading 9. These styles don't just carry formatting information; they also carry information about where the text fits in the hierarchy of your document. 6.5 PROJECT PROPERTIES AND CONDITIONS :: CHAPTER 6. SETUP It is often necessary for one stage of the installation process to pass information to a later stage. For example, the data collected from the user prior to installation usually needs to be available to the installation phase. REVIEW QUESTIONS :: CHAPTER 5. CONTROL FLOW, EXCEPTION 5.24: Assuming assertions are enabled, which of these assertion statements will throw an error? Select the two correct answers. asserttrue : true;
UNDERSTANDING RF SIGNALS :: CHAPTER 3. RADIO FREQUENCY ANDSEE MORE ONETUTORIALS.ORG
UPDATING THE DATA :: CHAPTER 15: WORKING WITH ADO :: PART However, with a little knowledge and ingenuity you can implement a suitable ADOUpdatesPending function. The necessary knowledge is that ADO datasets have a property called FilterGroup, which is a kind of filter.Unlike a dataset's Filter property, which filters the data based on a comparison of the data against a condition, FilterGroup filters based on the status of the record. RECIPE 3.7 CREATE A PAGE TOTAL :: CHAPTER 3. REPORTS 3.7.1 Problem. Access allows you to create a group total in the group footer on a report or a report total on the report footer, but you can't find a way to create a page total in the page footer. MASTERING DELPHI 7 :: PROGRAMMING :: ETUTORIALS.ORG Unusual Techniques: Alpha Blending, Color Key,and the Animate API 2.5 JAVA SOURCE FILE STRUCTURE :: CHAPTER 2. LANGUAGE The structure of a skeletal Java source file is depicted in Figure 2.2. A Java source file can have the following elements that, if present, must be specified in the following order: CREATING A DLL IN DELPHI :: CHAPTER 10: LIBRARIES AND Your First Delphi DLL. As a starting point in exploring the development of DLLs in Delphi, I'll show you a library built in Delphi. The primary focus of this example will be to show the syntax you use to define a DLL in Delphi, but it will also illustrate a few considerations involved in passing string parameters. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. THE ROLE OF HEADING STYLES AND OUTLINE LEVELS IN OUTLINING To understand outlining, you must understand three concepts: heading styles, outline levels, and body text. Heading styles are built-in styles that Word provides for each level of heading in your document, from Heading 1 to Heading 9. These styles don't just carry formatting information; they also carry information about where the text fits in the hierarchy of your document. 6.5 PROJECT PROPERTIES AND CONDITIONS :: CHAPTER 6. SETUP It is often necessary for one stage of the installation process to pass information to a later stage. For example, the data collected from the user prior to installation usually needs to be available to the installation phase. REVIEW QUESTIONS :: CHAPTER 5. CONTROL FLOW, EXCEPTION 5.24: Assuming assertions are enabled, which of these assertion statements will throw an error? Select the two correct answers. asserttrue : true;
6.10 CUSTOM ACTIONS :: CHAPTER 6. SETUP AND DEPLOYMENT If you have supplied an .exe, .dll, or script file for the sole purpose of providing a custom install action, it is not necessary to copy the file to the target machine as part of the installation.Although the file must be present in the File System view to be used as a custom action, CHAPTER 1. NETWORKING BASICS :: LAN SWITCHING FIRST-STEP Lan switching first-step. Chapter 1. Networking Basics. What You Will Learn. On completing this chapter, you will be able to: List the basic characteristics of a network. List the major physical and logical components of a network. Describe three modes of data transmission. Describe the three basic types of logical networks. 7.6 MICROSOFT REMOTE DESKTOP PROTOCOL :: CHAPTER 7 Table 7-6. Remotely exploitable Microsoft Terminal Services bugs; CVE name. Date. Notes. CVE-2000-1149. 08/11/2000. RegAPI.DLL overflow in Windows NT 4.0 Terminal Server allows remote attackers to execute arbitrary commands via a long username. CHAPTER 9. ACTIVITY DIAGRAMS :: UML The activity diagram describes the sequencing of activities, with support for both conditional and parallel behavior. An activity diagram is a variant of a state diagram in which most, if not all, the states are activity states. Thus, much of the terminology follows that of state diagrams. Conditional behavior is delineated by branches andmerges.
USING THE MONTHCALENDAR CONTROL :: CHAPTER 15: ADVANCED Two controls are available to enable the user to select the time and date. In this section, we’ll examine the MonthCalendar control; in the next section, we’ll look at the DateTimePicker control. The MonthCalendar control displays a calendar page that enables the user to select one or more dates. The user can scroll to additional months by using arrow buttons located at the top of the control. CONCURRENT STATE DIAGRAMS :: CHAPTER 8. STATE DIAGRAMS Concurrent state diagrams are useful when a given object has sets of independent behaviors. Note, however, that you should not get too many concurrent sets of behaviors occurring in a single object. If you have several complicated concurrent state diagrams for an object, you should consider splitting the object into separate objects. DEFINING THE MISSION OBJECTIVES :: CHAPTER 5. STARTING THE To expand upon the overview in the previous chapter, mission objectives are statements that represent the general tasks supported by the data maintained in the database. Each mission objective represents a single task. These mission objectives provide informationthat
CHAPTER 18: DNS AND NIS :: PART III: INTERNETWORKING WITH Overview. Secrets in This Chapter. Using the Domain Name System (DNS) Understanding Hierarchical Domain Names. Learning More about DNS and BIND. Understanding named-the BIND Name Server RECIPE 17.6 PRINT AN ACCESS REPORT FROM .NET WINDOWS FORM Double-click the cmdRunReport button control to jump to the code editor window. Select Project Add Reference to display the Visual Studio .NET Add Reference dialog box.. Click the COM tab, select "Microsoft Access 11.0 Object Library" from the upper listbox, and click the Select button as WHY KEYS ARE IMPORTANT :: CHAPTER 8. KEYS :: PART II: THE Keys are crucial to a table structure for the following reasons: They ensure that each record in a table is precisely identified. As you already know, a table represents a singular collection ofToggle navigation
×
search
Custom Search
Sort by:
Relevance
Relevance
Date
WELCOME TO ETUTORIALS.ORG - your source for thousands online tutorials, useful tips, articles, and researched recommendations. You can surf through our collection of free online tutorials. Just choose the language or section you are interested in learning in the left nav, or use the site search bar at the very top to find a lesson andenjoy!
We have scoured the internet to bring you an extensive collection of developer tutorials. You will find tutorials and lessons on most languages you want to learn how to program with here. We have Visual Basic, VB.NET, Java, J2EE, C, C++, C#, ASP, ASP.NET, Perl, JavaScript, Web Services, and XML tutorials. Most of the tutorials are either beginner or intermediate level but we have included a few advanced tutorials as well. Also you will find a few tutorials covering PHP, Cold Fusion, .NET Framework, HTML, and Python. BROWSE E-TUTORIALS BY CATEGORY Adobe Macromedia Programming SQL Server Administration Networking Microsoft Products Mac OS Linux systems Mobile devices XML Certification Misc All tutorials, products or service names listed on this website are the property of their respective owners. REMEMBER THE NAME: ETUTORIALS.ORG Advertise on eTutorials.org Copyright eTutorials.org 2008-2021. All rights reserved. AddThis Sharing Sidebar Share to FacebookFacebook , Number of sharesShare to TwitterTwitterShare to PrintPrintShare to EmailEmailMore AddThis Share optionsAddThis , Number of shares271Hide
Show
Close
AddThis
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0