Are you over 18 and want to see adult content?
More Annotations
The Skinny Dipping Report
Are you over 18 and want to see adult content?

Корма для собак и кошек Пурина – официальный сайт производителя – Purina.ru
Are you over 18 and want to see adult content?

A complete backup of beautyinstitutecanada.com
Are you over 18 and want to see adult content?
Banden voor personenwagens in heel België | Q Team
Are you over 18 and want to see adult content?

MomoBud - Online Premium Fruits Delivery in Singapore
Are you over 18 and want to see adult content?
A complete backup of gesundheits-universum.de
Are you over 18 and want to see adult content?

When we share, everyone wins - Creative Commons
Are you over 18 and want to see adult content?
Home - Lake Mountain Alpine Resort
Are you over 18 and want to see adult content?

simplemente maravilloso
Are you over 18 and want to see adult content?
Favourite Annotations
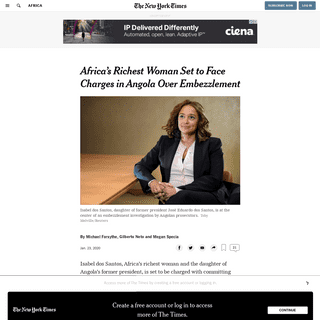
A complete backup of apnews.com/0b4c2fbbc8df65bd9f0431db3d853bc5
Are you over 18 and want to see adult content?

A complete backup of www.rtbf.be/sport/moteurs/rallye/wrc/detail_neuville-une-belle-revanche-apres-une-belle-bagarre-et-une-vict
Are you over 18 and want to see adult content?

A complete backup of www.milliyet.com.tr/gundem/mucize-doktor-20-yeni-bolum-fragmaninda-berhayat-hastanesi-karantinaya-aliniyor-
Are you over 18 and want to see adult content?
Text
proactive.
33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM SIG Goals/Deliverables. CVSS is currently at version 3.1. Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the standard without assuming any prior CVSS experience.MEMBERSHIP FEES
INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the CVSS V3.1 SPECIFICATION DOCUMENT Common Vulnerability Scoring System v3.1: Specification Document. Also available in PDF format (469KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. DOCUMENT RECORD RETENTION AND DESTRUCTION POLICY A. General Policy Statement. It is the policy of FIRST to retain all documents based on FIRST's record retention schedule. When the retention period is complete, documents will be destroyed. Except as otherwise indicated, documents shall be retained for the number of years indicated in Part C. FIRST is to maintain complete, accurate andhigh
FIRST - IMPROVING SECURITY TOGETHERMEMBERSHIP APPLICATIONABOUT FIRSTINITIATIVESSTANDARDS & PUBLICATIONSEVENTSEDUCATION FIRST is the global Forum of Incident Response and Security Teams. FIRST is the premier organization and recognized global leader in incident response. Membership in FIRST enables incident response teams to more effectively respond to security incidents reactive as well asproactive.
33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM SIG Goals/Deliverables. CVSS is currently at version 3.1. Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the standard without assuming any prior CVSS experience.MEMBERSHIP FEES
INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the CVSS V3.1 SPECIFICATION DOCUMENT Common Vulnerability Scoring System v3.1: Specification Document. Also available in PDF format (469KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. DOCUMENT RECORD RETENTION AND DESTRUCTION POLICY A. General Policy Statement. It is the policy of FIRST to retain all documents based on FIRST's record retention schedule. When the retention period is complete, documents will be destroyed. Except as otherwise indicated, documents shall be retained for the number of years indicated in Part C. FIRST is to maintain complete, accurate andhigh
COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the BEST PRACTICES GUIDE (BPGL) FIRST Best Practice Guide Library (BPGL) Also maintained by FIRST: the FIRST Security Reference Index. It is a complicated, arduous, and time-consuming task for even experienced system administrators to know what a reasonable set of security settings is for any operating system. Thus, the FIRST Best Practice Guide Library intends to assistMEMBERSHIP FEES
Annual membership fee. Type of membership. Cost (2020) Full member annual membership. US$ 2000. Liaison member annual membership. US$ 100. The membership fee is subject to change each year. The membership fee is not refundable upon membership termination. TRAFFIC LIGHT PROTOCOL (TLP) 1. Introduction. The Traffic Light Protocol (TLP) was created in order to facilitate greater sharing of information. TLP is a set of designations used to ensure that sensitive information is shared with the appropriate audience. It employs four colors to indicate expectedsharing
CONFLICT OF INTEREST POLICY Conflict of Interest Policy. Version 1.0. Also available as PDF (120Kb). Article I – Purpose. The purpose of the conflict of interest policy is to protect the FIRST's (Organization) interest when it is contemplating entering into a transaction or arrangement that might benefit the private interest of an officer or director of the Organization or might result in a possible excess benefit CVSS V3.1 USER GUIDE Common Vulnerability Scoring System v3.1: User Guide. Also available in PDF format (408KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. CVSS V3.0 USER GUIDE 1. Introduction. This guide supplements the formal CVSS v3.0 specification document by providing additional information, highlighting relevant changes from v2.0,MILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours. LOGS FOR INCIDENT RESPONSE Monday, June 23, 2008 Mitigating Risk. Automating Compliance. Confidential | 3 Goals {Learn/refresh about logs and logging{Refresh our knowledge of incident response practices {Learn how various logs are used at various stages of incident response {Learn ADTIMELINE ACTIVE DIRECTORY FORENSICS WITH REPLICATION AD replication metadata–msDS-ReplValueMetaData Replication metadata for linked attributes: Pairs of attributes in which the system calculates the values of one attribute (the back link e.g. MemberOf) based on the values set on the other attribute (the forward link e.g. Member) throughout the forest. In the case of group objects, the member attribute has the same information as 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address FIRST - IMPROVING SECURITY TOGETHER FIRST is the global Forum of Incident Response and Security Teams. FIRST is the premier organization and recognized global leader in incident response. Membership in FIRST enables incident response teams to more effectively respond to security incidents reactive as well asproactive.
TRAFFIC LIGHT PROTOCOL (TLP) 1. Introduction. The Traffic Light Protocol (TLP) was created in order to facilitate greater sharing of information. TLP is a set of designations used to ensure that sensitive information is shared with the appropriate audience. It employs four colors to indicate expectedsharing
COMMON VULNERABILITY SCORING SYSTEM SIG Goals/Deliverables. CVSS is currently at version 3.1. Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the standard without assuming any prior CVSS experience. INCIDENT RESPONSE HALL OF FAME INDUCTEES Incident Response Hall of Fame Inductee (FIRST) 2020. Membership Committee (FIRST) Since 2017 Member. Until 2012 Member (since its inception) Metrics (SIG) Participant. Program Committee (Conference) 1999 Program Chair for the 1999 FIRST Conference in Brisbane,Australia.
PSIRT SERVICES FRAMEWORK 1.1 PSIRT Services Framework. Also available in PDF.. Purpose. The Services Frameworks are high level documents detailing possible services that computer incident response teams (CSIRTs) and product incident response teams (PSIRTs) may provide. They are developed by recognized experts from the FIRST community. FIRST strives to include feedback from all sectors, including CSIRTs with a nationalFIRST.ORG, INC.
Join the Global Security Conference: Save the Date for the 33rd Annual FIRST Conference - Virtual Edition, June 6-11, 2021. CVSS V3.1 SPECIFICATION DOCUMENT Common Vulnerability Scoring System v3.1: Specification Document. Also available in PDF format (469KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. CVSS V2 COMPLETE DOCUMENTATION CVSS consists of 3 groups: Base, Temporal and Environmental. Each group produces a numeric score ranging from 0 to 10, and a Vector, a compressed textual representation that reflects the values used to derive the score. The Base group represents the intrinsic qualities ofa vulnerability.
DOCUMENT RECORD RETENTION AND DESTRUCTION POLICY A. General Policy Statement. It is the policy of FIRST to retain all documents based on FIRST's record retention schedule. When the retention period is complete, documents will be destroyed. Except as otherwise indicated, documents shall be retained for the number of years indicated in Part C. FIRST is to maintain complete, accurate andhigh
FREQUENTLY ASKED QUESTIONS A: There are six Base Metrics which represent the most fundamental, immutable qualities of a vulnerability. a) Access Vector measures how remote an attacker can be to attack a target. Local: Exploiting the vulnerability requires either physical access 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address FIRST - IMPROVING SECURITY TOGETHER FIRST is the global Forum of Incident Response and Security Teams. FIRST is the premier organization and recognized global leader in incident response. Membership in FIRST enables incident response teams to more effectively respond to security incidents reactive as well asproactive.
TRAFFIC LIGHT PROTOCOL (TLP) 1. Introduction. The Traffic Light Protocol (TLP) was created in order to facilitate greater sharing of information. TLP is a set of designations used to ensure that sensitive information is shared with the appropriate audience. It employs four colors to indicate expectedsharing
COMMON VULNERABILITY SCORING SYSTEM SIG Goals/Deliverables. CVSS is currently at version 3.1. Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the standard without assuming any prior CVSS experience. INCIDENT RESPONSE HALL OF FAME INDUCTEES Incident Response Hall of Fame Inductee (FIRST) 2020. Membership Committee (FIRST) Since 2017 Member. Until 2012 Member (since its inception) Metrics (SIG) Participant. Program Committee (Conference) 1999 Program Chair for the 1999 FIRST Conference in Brisbane,Australia.
PSIRT SERVICES FRAMEWORK 1.1 PSIRT Services Framework. Also available in PDF.. Purpose. The Services Frameworks are high level documents detailing possible services that computer incident response teams (CSIRTs) and product incident response teams (PSIRTs) may provide. They are developed by recognized experts from the FIRST community. FIRST strives to include feedback from all sectors, including CSIRTs with a nationalFIRST.ORG, INC.
Join the Global Security Conference: Save the Date for the 33rd Annual FIRST Conference - Virtual Edition, June 6-11, 2021. CVSS V3.1 SPECIFICATION DOCUMENT Common Vulnerability Scoring System v3.1: Specification Document. Also available in PDF format (469KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. CVSS V2 COMPLETE DOCUMENTATION CVSS consists of 3 groups: Base, Temporal and Environmental. Each group produces a numeric score ranging from 0 to 10, and a Vector, a compressed textual representation that reflects the values used to derive the score. The Base group represents the intrinsic qualities ofa vulnerability.
DOCUMENT RECORD RETENTION AND DESTRUCTION POLICY A. General Policy Statement. It is the policy of FIRST to retain all documents based on FIRST's record retention schedule. When the retention period is complete, documents will be destroyed. Except as otherwise indicated, documents shall be retained for the number of years indicated in Part C. FIRST is to maintain complete, accurate andhigh
FREQUENTLY ASKED QUESTIONS A: There are six Base Metrics which represent the most fundamental, immutable qualities of a vulnerability. a) Access Vector measures how remote an attacker can be to attack a target. Local: Exploiting the vulnerability requires either physical access 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address 33RD ANNUAL FIRST CONFERENCE The 32nd Annual FIRST Conference: Where Defenders Share, held November 16-18, 2020 saw over 2,500 online registrants from over 111 countries. The second virtual FIRST conference aims to be more thoughtful and engaging than the last! The 33rd Annual FIRST Conference: Crossing Uncertain Times, will once again be presented virtually and will be EXPLOIT PREDICTION SCORING SYSTEM (EPSS)SEE MORE ON FIRST.ORG INFORMATION EXCHANGE POLICY (IEP)SEE MORE ON FIRST.ORG COMMON VULNERABILITY SCORING SYSTEM VERSION 3.1 Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the COMMON VULNERABILITY SCORING SYSTEM VERSION 3.0 CALCULATOR Common Vulnerability Scoring System Version 3.0 Calculator. Hover over metric group names, metric names and metric values for a summary of the information in the official CVSS v3.0 Specification Document. The Specification is available in the list of links on the left, along with a User Guide providing additional scoring guidance, an Examples TRAFFIC LIGHT PROTOCOL (TLP) CVSS V2 COMPLETE DOCUMENTATIONMUP CERT - FIRST
Team Contact Information; Regular telephone number +381113617814: Emergency telephone number +381113617814: E-mail address: cert@mup.gov.rs: Facsimile numberMILCERT AT - FIRST
Rossauer Lände 1 1090 Wien. Business Hours. Timezone. CET. Description of business hours. Mo-Fr: 0800-1600. How to contact outside business hours.DELOITTE ECC
Team Contact Information; Regular telephone number +34914381284: Emergency telephone number +34914381284: E-mail address: desk@cybersoc.deloitte.es: Postal address FIRST - IMPROVING SECURITY TOGETHER FIRST is the global Forum of Incident Response and Security Teams. FIRST is the premier organization and recognized global leader in incident response. Membership in FIRST enables incident response teams to more effectively respond to security incidents reactive as well asproactive.
TRAFFIC LIGHT PROTOCOL (TLP) 1. Introduction. The Traffic Light Protocol (TLP) was created in order to facilitate greater sharing of information. TLP is a set of designations used to ensure that sensitive information is shared with the appropriate audience. It employs four colors to indicate expectedsharing
COMMON VULNERABILITY SCORING SYSTEM SIG Goals/Deliverables. CVSS is currently at version 3.1. Links on the left lead to CVSS version 3.1's specification and related resources. A self-paced on-line training course is available for CVSS v3.1. It explains the standard without assuming any prior CVSS experience. INCIDENT RESPONSE HALL OF FAME INDUCTEES Incident Response Hall of Fame Inductee (FIRST) 2020. Membership Committee (FIRST) Since 2017 Member. Until 2012 Member (since its inception) Metrics (SIG) Participant. Program Committee (Conference) 1999 Program Chair for the 1999 FIRST Conference in Brisbane,Australia.
PSIRT SERVICES FRAMEWORK 1.1 PSIRT Services Framework. Also available in PDF.. Purpose. The Services Frameworks are high level documents detailing possible services that computer incident response teams (CSIRTs) and product incident response teams (PSIRTs) may provide. They are developed by recognized experts from the FIRST community. FIRST strives to include feedback from all sectors, including CSIRTs with a nationalFIRST.ORG, INC.
Join the Global Security Conference: Save the Date for the 33rd Annual FIRST Conference - Virtual Edition, June 6-11, 2021. CVSS V3.1 SPECIFICATION DOCUMENT Common Vulnerability Scoring System v3.1: Specification Document. Also available in PDF format (469KiB).. The Common Vulnerability Scoring System (CVSS) is an open framework for communicating the characteristics and severity of software vulnerabilities. CVSS V2 COMPLETE DOCUMENTATION CVSS consists of 3 groups: Base, Temporal and Environmental. Each group produces a numeric score ranging from 0 to 10, and a Vector, a compressed textual representation that reflects the values used to derive the score. The Base group represents the intrinsic qualities ofa vulnerability.
DOCUMENT RECORD RETENTION AND DESTRUCTION POLICY A. General Policy Statement. It is the policy of FIRST to retain all documents based on FIRST's record retention schedule. When the retention period is complete, documents will be destroyed. Except as otherwise indicated, documents shall be retained for the number of years indicated in Part C. FIRST is to maintain complete, accurate andhigh
FREQUENTLY ASKED QUESTIONS A: There are six Base Metrics which represent the most fundamental, immutable qualities of a vulnerability. a) Access Vector measures how remote an attacker can be to attack a target. Local: Exploiting the vulnerability requires either physical accessSign in
* About FIRST
* Mission Statement
* History
* Organization
* Board of Directors * Executive Director* Secretariat
* Committees
* Annual General Meeting * Annual Reports and Tax Filings* FIRST Policies
* Anti-Corruption Policy* Antitrust Policy
* Bylaws
* Board duties
* Bug Bounty Program* Code of Conduct
* Conflict of Interest Policy * Document Record Retention and Destruction Policy * FIRST Press Policy * General Event Registration Refund Policy * Guidelines for Site Selection for all FIRST events * Identity & Logo Usage* Media Policy
* Privacy Policy
* Standards Policy
* Translation Policy* Travel Policy
* Uniform IPR Policy * Whistleblower Protection Policy* Partnerships
* Partners
* Friends of FIRST
* FIRST Supporters
* Newsroom
* What's New
* Press Releases
* In the News
* Podcasts
* Newsletters
* FIRST Press Policy* Procurement
* Jobs
* Contact
* Membership
* Becoming a Member
* Benefits
* Membership Process * Full Member Form (App A) * Liaison Form (App B)* Membership Fees
* FIRST Teams
* FIRST Liaisons
* Members around the world * Membership Application * Team Membership Application * Liaison Membership Application* Initiatives
* Special Interest Groups (SIGs) * Academic Security SIG* Big Data SIG
* Common Vulnerability Scoring System (CVSS-SIG)* Calculator
* Specification Document* User Guide
* Examples
* CVSS v3.1 Documentation & Resources * CVSS v3.1 Calculator * CVSS v3.1 Specification Document * CVSS v3.1 User Guide * CVSS v3.1 Examples * CVSS v3.1 Calculator Use & Design* CVSS v3.0 Archive
* CVSS v3.0 Calculator * CVSS v3.0 Specification Document * CVSS v3.0 User Guide * CVSS v3.0 Examples * CVSS v3.0 Calculator Use & Design* CVSS v2 Archive
* CVSS v2 Complete Documentation* CVSS v2 History
* CVSS-SIG team
* SIG Meetings
* Frequently Asked Questions* CVSS Adopters
* CVSS Links
* CVSS v1 Archive
* Introduction to CVSS * Frequently Asked Questions * Complete CVSS v1 Guide * JSON & XML Data Representations * CVSS On-Line Training Course * Identity & logo usage * CSIRT Framework Development SIG * Cyber Insurance SIG * Cyber Insurance SIG Webinars * Cyber Threat Intelligence SIG* Curriculum
* Introduction
* Introduction to CTI as a General topic * Methods and Methodology * Source Evaluation and Information Reliability* Threat Modelling
* Training
* Standards
* Glossary
* DNS Abuse SIG
* Ethics SIG
* Ethics for Incident Response Teams * Exploit Prediction Scoring System (EPSS)* The EPSS Model
* Related Papers
* Industrial Control Systems SIG (ICS-SIG) * Information Exchange Policy SIG (IEP-SIG) * Information Sharing SIG * Malware Information Sharing Platform* Malware Analysis
* Malware Analysis Resources* Metrics SIG
* Metrics SIG Webinars * Passive DNS Exchange* PSIRT SIG
* Full Incident Management Coordination Working Group* Red Team SIG
* Retail and Consumer Packaged Goods (CPG) SIG * Security Lounge SIG* SIGs Framework
* Threat Intel Coalition SIG * Membership Requirements and Veto Rules * Traffic Light Protocol (TLP-SIG) * Vulnerability Coordination * Multi-Party Vulnerability Coordination and Disclosure * Guidelines and Practices for Multi-Party Vulnerability Coordinationand Disclosure
* Vulnerability Reporting and Data eXchange SIG (VRDX-SIG) * Vulnerability Database Catalog* Women of FIRST
* Internet Governance* IR Database
* Fellowship Program* Application Form
* IR Hall of Fame
* Hall of Fame Inductees * Volunteers at FIRST* FIRST Volunteers
* Volunteer Contribution Record * Previous Activities * Best Practices Contest * Standards & Publications* Standards
* Common Vulnerability Scoring System (CVSS-SIG) * Traffic Light Protocol (TLP) * Service Frameworks * CSIRT Services Framework * PSIRT Services Framework * Information Exchange Policy (IEP)* IEP 2.0 Framework
* IEP 2.0 JSON Specification * Standard IEP Policies * IEP TLP Policy File * IEP Unknown Policy File* IEP 1.0 Archive
* Passive DNS Exchange * Exploit Prediction Scoring System (EPSS)* Publications
* Best Practices Guide (BPGL) * Security Reference Index * Contribute to the Library* Events
* Events Calendar
* FIRST Events
* Annual Conferences * Network Privacy Statement and Conference Monitoring * Technical Colloquia & Symposia * Training & Workshops * Webinars & Virtual Events* Education
* Training Courses
* For Trainers
* Blog
EVENTS AT SPOTLIGHT
*
*
*
*
FIRST IS THE GLOBAL FORUM OF INCIDENT RESPONSE AND SECURITY TEAMS FIRST is the premier organization and recognized global leader in incident response. Membership in FIRST enables incident response teams to more effectively respond to security incidents reactive as well asproactive.
FIRST brings together a variety of computer security incident response teams from government, commercial, and educational organizations. FIRST aims to foster cooperation and coordination in incident prevention, to stimulate rapid reaction to incidents, and to promote information sharing among members and the community at large. Apart from the trust network that FIRST forms in the global incident response community, FIRST also provides value added services. Some ofthese are:
* access to up-to-date best practice documents * technical colloquia for security experts* hands-on classes
* annual incident response conference * publications and web services * special interest groups Currently FIRST has more than 500 members , spread over Africa, the Americas, Asia, Europe and Oceania.CURRENT FIRST SIGS
*
ACADEMIC SECURITY SIG Space for discussion in order to reflect on our collective experiences, focus on current challenges and envision strategies on how we could work together to improve security in academicenvironments.
*
BIG DATA SIG
Incident Detection and Response at Scale.*
CSIRT FRAMEWORK DEVELOPMENT SIG The SIG will seek to involve experts interested in that work and provide a community to discuss improvements in need, existing gaps and (potential) new developments.*
CVSS SIG: COMMON VULNERABILITY SCORING SYSTEM For a global approach towards scoring metrics for vulnerabilities.*
CYBER INSURANCE SIG
To coordinate cyber insurance actuarial and modelling work with professional incident response and digital forensic teams.*
CYBER THREAT INTELLIGENCE SIG To define Threat Intelligence in the commercial space.*
DNS ABUSE SIG
Understanding the international customary norms applicable for detecting and mitigating DNS abuse from the perspective of the global incident response community is critical for the open Internet’s stability, security and resiliency.*
ETHICS SIG
The Ethics SIG seeks to further the professionalization of the FIRST Community and improve the global understanding of SIRTs through the development of an ethical code for FIRST Members.*
EXPLOIT PREDICTION SCORING SYSTEM (EPSS) The Exploit Prediction Scoring System (EPSS) is an open, data-driven effort for predicting when software vulnerabilities will be exploited.*
ICS SIG: INDUSTRIAL CONTROL SYSTEMS In ICS-SIG we bring together expertise from several sectors to create processes, best practices and incident response support recommendations and package useful open source tools for the ICSenvironments.
*
IEP SIG: INFORMATION EXCHANGE POLICY The initial goals of this SIG are to collaboratively develop an extensible framework for defining information exchange policy and a set of standard definitions for most common aspects.*
INFORMATION SHARING SIG The core mission is to support existing and new FIRST members to practice information sharing and acquire feedback from the members to improve the information sharing practices.*
MALWARE ANALYSIS
This SIG will advocate and promote the sharing of malware analysis tools and techniques to enable CSIRTs to combat and analyze maliciouscode.
*
METRICS SIG
To improve CSIRT incident management practices within the FIRSTcommunity.
*
PASSIVE DNS EXCHANGE Develops and maintains a standard for exchanging passive DNS information between organizations.*
PSIRT SIG
Drive the evolution of PSIRT practices by developing and maturingproduct response.
*
RED TEAM SIG
The Red Team SIG provides a forum for practitioners to discuss the state of the art for tools, technologies, processes and methodologies for red team activities and to share experiences and best practices.*
RETAIL AND CONSUMER PACKAGED GOODS (CPG) SIG Share the need to get together as incident responders and cyber threat management professionals, in order to share experiences, best practices and challenges to better protect our organizations.*
SECURITY LOUNGE SIG
Designs, develops, and conducts security challenge and competition exercises for the FIRST.org community.*
THREAT INTEL COALITION SIG To improve civil society organization’s access to threat intelligence, and help coordinate mitigation efforts to civil society organizations targeted by threat actors where possible.*
TLP SIG: TRAFFIC LIGHT PROTOCOL The TLP SIG governs the standard definition of TLP for the benefit of the worldwide CSIRT community and its operational partners.*
VULNERABILITY COORDINATION SIG Develop and execute a strategy for improving vulnerability coordination globally.*
VULNERABILITY REPORTING AND DATA EXCHANGE SIG Primarily chartered to research and recommend ways to identify and exchange vulnerability information across disparate vulnerabilitydatabases.
WHAT'S NEW
ICASI INTEGRATES INTO FIRST PSIRT SIG BOLSTERING THE INCIDENT RESPONSE AND SECURITY TEAM INDUSTRY Tue, 01 Jun 2021 13:00 +0000 JUNE 1ST, 2021 – ICASI – the Industry Consortium for Advancement of Security on the Internet was officially integrated into the Forum of Incident Response and Security Teams (FIRST) on May 28, 2021. Established in 2008, ICASI’s purpose was to strengthen the global security landscape by driving excellence and innovation in security response practices; facilitating collaboration among members to analyze, mitigate, and resolve multi-stakeholder, global security challenges. This role will continue but as part of the existing FIRST PSIRT SIG, expand and improve the community’s ability to respond to vulnerabilities across multiple vendors. Founded in 1990, FIRST is the global leader in incident response. FIRST POST: MARCH 2021 Wed, 31 Mar 2021 00:00 +0000 33rd FIRST Annual Conference: Crossing Uncertain Times; Mark your calendars: FIRST reveals 2021 events calendar; FIRST welcomes its 97th country and member 562: Benin bjCSIRT; FIRST, ITU and Equals launches Women in Cyber Mentorship Program for Arab and Africa Regions; Get your nominations in for the third edition of The Incident Response Hall of Fame; New Podcast - FIRST Impressions - is launched! THANK YOU FIRST COMMUNITY FOR HELPING TEAM CYMRU REACH A NEW CSIRT ASSISTANCE PROGRAM MILESTONE Thu, 28 Jan 2021 17:00 +0000 Together, We’re Creating Better Threat Intelligence Sharing for theWorld
WHAT IS FIRST TO YOU? Contact | Copyright © 2015—2021 by Forum of Incident Response and Security Teams, Inc. All Rights Reserved. Found a bug? E-mail us at first-website@first.orgDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0