Are you over 18 and want to see adult content?
More Annotations

A complete backup of juliusdesign.net
Are you over 18 and want to see adult content?
A complete backup of ralphlaurenoutletuk.org.uk
Are you over 18 and want to see adult content?

A complete backup of thespacereview.com
Are you over 18 and want to see adult content?
A complete backup of tabletable.co.uk
Are you over 18 and want to see adult content?

A complete backup of oralb-blendamed.de
Are you over 18 and want to see adult content?

A complete backup of fortuneseafoods.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://skyroam.com
Are you over 18 and want to see adult content?
A complete backup of https://proofreadingpal.com
Are you over 18 and want to see adult content?
A complete backup of https://rumahhokie.com
Are you over 18 and want to see adult content?
A complete backup of https://interbev.fr
Are you over 18 and want to see adult content?
A complete backup of https://helipal.com
Are you over 18 and want to see adult content?
A complete backup of https://kwnyc.com
Are you over 18 and want to see adult content?
A complete backup of https://cosector.com
Are you over 18 and want to see adult content?

A complete backup of https://appellationbeer.com
Are you over 18 and want to see adult content?
A complete backup of https://animalequality.org.uk
Are you over 18 and want to see adult content?

A complete backup of https://tsne.org
Are you over 18 and want to see adult content?
A complete backup of https://annuity.org
Are you over 18 and want to see adult content?
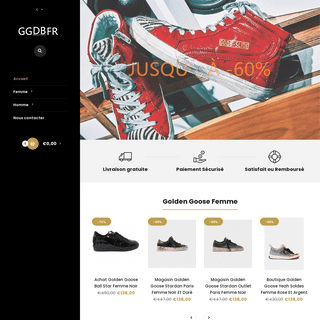
A complete backup of https://boutiquegoldengoose.com
Are you over 18 and want to see adult content?
Text
ARCHIVES
SetACL Studio. Manage Windows permissions from an intuitive UI ( documentation) Download SetACL Studio 1.2.4 for 32-bit and 64-bit Windows, multilingual. Use the following license key to convert the downloaded product to an unrestricted version: RUMH5R-PREMM7-W38EA5-QTSQZ1-1HA1A6-CTXHUQ. SETACL - AUTOMATE PERMISSIONS AND MANAGE ACLS • HELGE KLEIN It copies permissions between users or even domains. It can be used to hunt down unwanted permissions and mercilessly remove them. SetACL is the driving force in countless scripts, tested and proven. It is valued by administrators and developers alike. SetACL has been downloaded more than 400,000 times. Read about SetACL’s feature set.SETACL STUDIO
SetACL Studio is a management tool for Windows permissions. It combines powerful features with an extremely intuitive user interface. It works with files, folders, registry keys, printers, network shares, services and WMI objects. It supports very long file system paths and bypasses security to display information about the remotest corner of DISKLED • HELGE KLEIN DiskLED. DiskLED is a small tool that displays performance counter data using an animated system tray icon. It comes with a graphical configuration dialog that lets you choose from all performance counters available on the local system – you can monitor networkthroughput just
DELPROF2: USER PROFILE DELETION TOOL • HELGE KLEIN Delprof2 by Helge Klein (https://helgeklein.com) Delprof2 deletes inactive Windows user profiles (profiles that are not currently loaded). Delprof2 is syntax compatible with the original Delprof by Microsoft. Unlike the original it works on all modern versions of Windows. If possible, Delprof2 uses the backup and restore privilegesto bypass
WINDOWS SETUP USB FLASH DRIVE NOT SHOWING UP IN BIOS LIST The basic principle is simple: Create a bootable Windows Setup USB flash drive, either with Windows 10 Media Creation Tool or with Rufus . Connect the USB flash drive to the PC or laptop. Power on the device. During the BIOS initialization phase, press ESC/F12 to bring up the list of boot devices (here is a handy list of hotkeys coveringmost
SETACL COMMAND LINE-VERSION (SETACL.EXE) BLOCKING OFFICE MACROS, MANAGING WINDOWS & MACOS VIAINTUNE OFFICE 365UPDATES
How to centrally manage essential security settings of self-managed devices. This is a guest post by Martin Kretzschmar, customer success engineer at vast limits, the uberAgent company.. One thing I especially like about my everyday working life is the flexibility itoffers.
LEAKED TOKEN HANDLES PREVENTING RDS SESSION ID REUSE Getting RDS Session IDs to be Reused. I wanted to prove that the open token handles shown above are indeed what keeps an RDS session ID from being reused, so I closed them one by one starting with the first svchost instance: C:\>handle -c 48C -y -p 1064 48C: Token HK\test01:17c025 Handle closed. This reduced the list of open handlesby one:
HELGE KLEIN • TOOLS & KNOWLEDGE FOR IT PROSBLOGSETACLDELPROF2DOWNLOADDOCUMENTATIONEXAMPLES End-to-End-Encrypted Team Communication & Collaboration Tools. This post is a collection of my notes about my search for secure collaboration and communication tools for smaller organizations, specifically vast limits. I will update it from time to Read more. by Helge Klein on April 15, 2020. Applications. DOWNLOAD DELPROF2, SETACL (STUDIO) • HELGE KLEINFAQWINDOWS GENERALARCHIVES
SetACL Studio. Manage Windows permissions from an intuitive UI ( documentation) Download SetACL Studio 1.2.4 for 32-bit and 64-bit Windows, multilingual. Use the following license key to convert the downloaded product to an unrestricted version: RUMH5R-PREMM7-W38EA5-QTSQZ1-1HA1A6-CTXHUQ. SETACL - AUTOMATE PERMISSIONS AND MANAGE ACLS • HELGE KLEIN It copies permissions between users or even domains. It can be used to hunt down unwanted permissions and mercilessly remove them. SetACL is the driving force in countless scripts, tested and proven. It is valued by administrators and developers alike. SetACL has been downloaded more than 400,000 times. Read about SetACL’s feature set.SETACL STUDIO
SetACL Studio is a management tool for Windows permissions. It combines powerful features with an extremely intuitive user interface. It works with files, folders, registry keys, printers, network shares, services and WMI objects. It supports very long file system paths and bypasses security to display information about the remotest corner of DISKLED • HELGE KLEIN DiskLED. DiskLED is a small tool that displays performance counter data using an animated system tray icon. It comes with a graphical configuration dialog that lets you choose from all performance counters available on the local system – you can monitor networkthroughput just
DELPROF2: USER PROFILE DELETION TOOL • HELGE KLEIN Delprof2 by Helge Klein (https://helgeklein.com) Delprof2 deletes inactive Windows user profiles (profiles that are not currently loaded). Delprof2 is syntax compatible with the original Delprof by Microsoft. Unlike the original it works on all modern versions of Windows. If possible, Delprof2 uses the backup and restore privilegesto bypass
WINDOWS SETUP USB FLASH DRIVE NOT SHOWING UP IN BIOS LIST The basic principle is simple: Create a bootable Windows Setup USB flash drive, either with Windows 10 Media Creation Tool or with Rufus . Connect the USB flash drive to the PC or laptop. Power on the device. During the BIOS initialization phase, press ESC/F12 to bring up the list of boot devices (here is a handy list of hotkeys coveringmost
SETACL COMMAND LINE-VERSION (SETACL.EXE) BLOCKING OFFICE MACROS, MANAGING WINDOWS & MACOS VIAINTUNE OFFICE 365UPDATES
How to centrally manage essential security settings of self-managed devices. This is a guest post by Martin Kretzschmar, customer success engineer at vast limits, the uberAgent company.. One thing I especially like about my everyday working life is the flexibility itoffers.
LEAKED TOKEN HANDLES PREVENTING RDS SESSION ID REUSE Getting RDS Session IDs to be Reused. I wanted to prove that the open token handles shown above are indeed what keeps an RDS session ID from being reused, so I closed them one by one starting with the first svchost instance: C:\>handle -c 48C -y -p 1064 48C: Token HK\test01:17c025 Handle closed. This reduced the list of open handlesby one:
TOP 10 IT SECURITY TIPS FOR INDIVIDUAL USERS • HELGE KLEIN 7. Antivirus: Windows Defender is Good Enough. 8. Offsite Backups. 9. Encrypt Your Laptop’s Disk Drive. 10. Protect Your Email Account. This is a list of simple things that will protect you from nearly all the real-world IT security issues affecting individuals and SOHOusers.
FREE AND POWERFUL EQUALIZER FOR WINDOWS 10 • HELGE KLEIN Peter’s Equalizer API Configuration Extension (Peace) is pretty easy to use while offering powerful features: Slider changes have an immediate effect. Settings can be applied to invididual devices only. Great flexibility. Saved configurations. Easy backup and restore ofconfigurations.
HOW TO LIST ALL INSTALLED APPLICATIONS FROM THE COMMAND This article describes how to list all installed MSI packages. A more comprehensive listing of all applications displayed in Programs and Features can be obtained through our monitoring and analytics product uberAgent.. How to easily create a list of all programs and (MSI) packages installed on a system for later processing? CITRIX XENAPP/XENDESKTOP API HOOKING EXPLAINED • HELGE KLEIN Citrix’ Way of Hooking. Remoting applications and desktops is no small feat, and Citrix needs many different hooks in order to pull it off. To simplify management a single hook DLL, Mfaphook.dll is added to the AppInit_DLLs registry value when the XenApp/XenDesktop VDA is installed. Actually, two hook DLLs are added: WINDOWS SETUP USB FLASH DRIVE NOT SHOWING UP IN BIOS LIST The basic principle is simple: Create a bootable Windows Setup USB flash drive, either with Windows 10 Media Creation Tool or with Rufus . Connect the USB flash drive to the PC or laptop. Power on the device. During the BIOS initialization phase, press ESC/F12 to bring up the list of boot devices (here is a handy list of hotkeys coveringmost
HOW TO ENABLE BITLOCKER HARDWARE ENCRYPTION WITH SSDS The computer is a Lenovo W540 laptop. The main points are: Update your RST driver to at least version 13.2.4.1000. Wipe the disk with diskpart clean. Use Samsung Magician to switch the Encrypted Drive status to ready to enable. Reboot. Initialize and format the drive. Enable BitLocker. The following sections explain the process in moredetail.
HOWTO: REACLING A FILE SERVER IN A DOMAIN MIGRATION WITH When you are planning a migration of user accounts between domains one tasks always pops up pretty quickly: reassigning the permissions of the users in the source domain to the corresponding users in the target domain, in other words reACLing the file server. CREATING AN APPLICATION CRASH DUMP • HELGE KLEIN Helge Klein (ex CTP, MVP and vExpert) worked as a consultant and developer before founding vast limits, the uberAgent company. Helge applied his extensive knowledge in IT infrastructure projects and architected the user profile management product whose successor is now available as Citrix Profile Management. HOW GROUP POLICY IMPACTS LOGON PERFORMANCE #3: WMI FILTERS This article is based on my Citrix Synergy 2015 session and is the third in a mini-series on Group Policy performance. All measurements by uberAgent on Windows Server 2012 R2 with Citrix XenApp 7.6 in a steady state. Please start reading with the first article.. Filtering CITRIX XENAPP 7.6 LOGON SLOW Update 2015-04-28: Citrix provides the limited release hotfix ICATS760WX64009 that fixes this issue. More information below. During the research for my session about the XenApp 7.6 logon process, to be presented at Citrix Synergy and BriForum London, I noticed that the logon to my XenApp 7.6 lab server was taking a bit long.Longer, in fact, than the combined durations of the main logon Please enable cookies.PLEASE WAIT...
WE ARE CHECKING YOUR BROWSER... HELGEKLEIN.COM Please stand by, while we are checking your browser...Redirecting...
PLEASE TURN JAVASCRIPT ON AND RELOAD THE PAGE. Please enable Cookies and reload the page. WHY DO I HAVE TO COMPLETE A CAPTCHA? Completing the CAPTCHA proves you are a human and gives you temporary access to the web property. WHAT CAN I DO TO PREVENT THIS IN THE FUTURE? If you are on a personal connection, like at home, you can run an anti-virus scan on your device to make sure it is not infected withmalware.
If you are at an office or shared network, you can ask the network administrator to run a scan across the network looking for misconfigured or infected devices. Another way to prevent getting this page in the future is to use Privacy Pass. You may need to download version 2.0 now from the ChromeWeb Store
.
Cloudflare Ray ID: 65A9F68E2A1ACA67 • Your IP: 52.60.208.173 • Performance & security by CloudflareDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0