Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://thefashionoutlet.nl
Are you over 18 and want to see adult content?

A complete backup of https://maisondepax.com
Are you over 18 and want to see adult content?
A complete backup of https://wright-brothers.org
Are you over 18 and want to see adult content?

A complete backup of https://pension-guide.de
Are you over 18 and want to see adult content?

A complete backup of https://tmay.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://mcccmd.com
Are you over 18 and want to see adult content?

A complete backup of https://copinh.org
Are you over 18 and want to see adult content?

A complete backup of https://radical.net
Are you over 18 and want to see adult content?
A complete backup of https://agilie.com
Are you over 18 and want to see adult content?
A complete backup of https://auteursrecht.nl
Are you over 18 and want to see adult content?
A complete backup of https://z8games.com
Are you over 18 and want to see adult content?
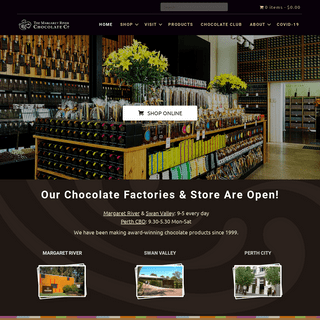
A complete backup of https://chocolatefactory.com.au
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://attacmadrid.org
Are you over 18 and want to see adult content?

A complete backup of https://pay-for-essay.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://maximarkets.club
Are you over 18 and want to see adult content?
A complete backup of https://tresorberlin.com
Are you over 18 and want to see adult content?

A complete backup of https://nokenny.com
Are you over 18 and want to see adult content?

A complete backup of https://slik-interior.be
Are you over 18 and want to see adult content?

A complete backup of https://mabanque.bnpparibas
Are you over 18 and want to see adult content?

A complete backup of https://bmwe34.net
Are you over 18 and want to see adult content?
A complete backup of https://navegg.com
Are you over 18 and want to see adult content?
A complete backup of https://maylammat.org
Are you over 18 and want to see adult content?
A complete backup of https://aegistrust.org
Are you over 18 and want to see adult content?
A complete backup of https://pianodisorento.com
Are you over 18 and want to see adult content?
Text
ELEMENTS OF IOT
Industrial IoT. Welcome to Industry 4.0: The convergence of network architecture and smart manufacturing systems. By enabling data sharing and removing boundaries across the factory floor, industrial firms are seeing improved equipment efficiency, market agility, and laborproductivity.
9 IMMUTABLE LAWS OF NETWORK DESIGN 1. Know, Don’t Guess. Two phrases uttered frequently during network design are “I’m pretty sure” and “I think.”. As a professional tasked with discovering, researching and documenting client networks, I can tell you those phrases don’t cut it in ourorganization, and
NETDEVOPS: APPLYING DEVOPS PRACTICES IN NETWORKING NetDevOps is defined as an intersection of DevOps and Networking. NetDevOps automates manual and traditional network processes by using Infrastructure as Code (IaC). IaC enables you to provision and manage data center resources like computers and connectivity. Infrastructure as Code is based on machine-readable configuration files, rather than ANSIBLE FOR NETWORK AUTOMATION TUTORIAL The following commands will configure the Personal Package Archives ( PPA) and install Ansible. Here are the basic commands, in the same order they are needed for the installation of Ansible: $ sudo apt-get update. $ sudo apt-get install software-properties-common. $ sudo apt-add-repository ppa:ansible/ansible. $ sudo apt-get update. 10 PLACES TO FIND FREE ONLINE IT TRAINING 10 Places to Find Free Online IT Training. These websites offer excellent resources for IT infrastructure professionals looking to expand their knowledge. This YouTube channel specializes in "free community-generated educational videos and podcasts for people working with virtualization, storage, DevOps, and cloud technologies."SDN LIMITATIONS
SDN Limitations. Software-defined networking is touted as a panacea for data centers, but the combination of faster networking speeds and virtualization restricts what it can do. If you listen to the hype, software-defined networking and other software-defined technology will solve all data center problems and allow your computing gear to be an 8 COMMON NETWORK ANALYTICS DATA SOURCES Simple Network Management Protocol (SNMP) SNMP polling has been a major method for monitoring networks for the past several decades. It works by sending a request (poll) to network devices for specific information on the health of the device as well as statistics on the data passing through it. IS YOUR NETWORK OPTIMIZED FOR WIFI CALLING? WiFi calling through smartphones has been around for a few years. But despite it being a common feature on Android and iOS devices, many don't realize that it’s disabled by default. Still, looking at the numbers, more mobile users are indeed enabling WiFi calling.So, if your organization embraces BYOD, you’re going to want to make sure your network is optimized for voice communications. FIVE CONSIDERATIONS FOR A WI-FI 6 DEPLOYMENT PLAN The saying: “Proper preparation, prevents poor performance,” holds true for technology deployments. Whether you’re ready for an upgrade to the next version of Wi-Fi in your enterprise or venue or not, a plan for Wi-Fi 6 (aka 802.11ax), is only as good as the effort IT managers put into it. ROUTING DESIGN: OSPF OR EIGRP? CCDE wisdom is that EIGRP is better at hub and spoke, OSPF is better (with tweaks) for full mesh situations. With EIGRP in hub and spoke, filtering to only advertise 0/0 (and/or “corporate default 10/8”) out of the hub may well be possible to really reduce advertisements and enhance scalability.ELEMENTS OF IOT
Industrial IoT. Welcome to Industry 4.0: The convergence of network architecture and smart manufacturing systems. By enabling data sharing and removing boundaries across the factory floor, industrial firms are seeing improved equipment efficiency, market agility, and laborproductivity.
9 IMMUTABLE LAWS OF NETWORK DESIGN 1. Know, Don’t Guess. Two phrases uttered frequently during network design are “I’m pretty sure” and “I think.”. As a professional tasked with discovering, researching and documenting client networks, I can tell you those phrases don’t cut it in ourorganization, and
NETDEVOPS: APPLYING DEVOPS PRACTICES IN NETWORKING NetDevOps is defined as an intersection of DevOps and Networking. NetDevOps automates manual and traditional network processes by using Infrastructure as Code (IaC). IaC enables you to provision and manage data center resources like computers and connectivity. Infrastructure as Code is based on machine-readable configuration files, rather than ANSIBLE FOR NETWORK AUTOMATION TUTORIAL The following commands will configure the Personal Package Archives ( PPA) and install Ansible. Here are the basic commands, in the same order they are needed for the installation of Ansible: $ sudo apt-get update. $ sudo apt-get install software-properties-common. $ sudo apt-add-repository ppa:ansible/ansible. $ sudo apt-get update. 10 PLACES TO FIND FREE ONLINE IT TRAINING 10 Places to Find Free Online IT Training. These websites offer excellent resources for IT infrastructure professionals looking to expand their knowledge. This YouTube channel specializes in "free community-generated educational videos and podcasts for people working with virtualization, storage, DevOps, and cloud technologies."SDN LIMITATIONS
SDN Limitations. Software-defined networking is touted as a panacea for data centers, but the combination of faster networking speeds and virtualization restricts what it can do. If you listen to the hype, software-defined networking and other software-defined technology will solve all data center problems and allow your computing gear to be an 8 COMMON NETWORK ANALYTICS DATA SOURCES Simple Network Management Protocol (SNMP) SNMP polling has been a major method for monitoring networks for the past several decades. It works by sending a request (poll) to network devices for specific information on the health of the device as well as statistics on the data passing through it. IS YOUR NETWORK OPTIMIZED FOR WIFI CALLING? WiFi calling through smartphones has been around for a few years. But despite it being a common feature on Android and iOS devices, many don't realize that it’s disabled by default. Still, looking at the numbers, more mobile users are indeed enabling WiFi calling.So, if your organization embraces BYOD, you’re going to want to make sure your network is optimized for voice communications. FIVE CONSIDERATIONS FOR A WI-FI 6 DEPLOYMENT PLAN The saying: “Proper preparation, prevents poor performance,” holds true for technology deployments. Whether you’re ready for an upgrade to the next version of Wi-Fi in your enterprise or venue or not, a plan for Wi-Fi 6 (aka 802.11ax), is only as good as the effort IT managers put into it. ROUTING DESIGN: OSPF OR EIGRP? CCDE wisdom is that EIGRP is better at hub and spoke, OSPF is better (with tweaks) for full mesh situations. With EIGRP in hub and spoke, filtering to only advertise 0/0 (and/or “corporate default 10/8”) out of the hub may well be possible to really reduce advertisements and enhance scalability. 10 FREE NETWORK MANAGEMENT TOOLS Other essential tools include KeePass, PuTTY and WinMerge. Continue on to learn about 10 free tools that provide a range of network management and troubleshooting functions for a variety of network infrastructure scenarios. Nagios Core. One of the key responsibilities of any network administrator is to monitor the network and fix issuesthat
NETDEVOPS: APPLYING DEVOPS PRACTICES IN NETWORKING NetDevOps is defined as an intersection of DevOps and Networking. NetDevOps automates manual and traditional network processes by using Infrastructure as Code (IaC). IaC enables you to provision and manage data center resources like computers and connectivity. Infrastructure as Code is based on machine-readable configuration files, rather than 10 PLACES TO FIND FREE ONLINE IT TRAINING 10 Places to Find Free Online IT Training. These websites offer excellent resources for IT infrastructure professionals looking to expand their knowledge. This YouTube channel specializes in "free community-generated educational videos and podcasts for people working with virtualization, storage, DevOps, and cloud technologies." IS YOUR NETWORK OPTIMIZED FOR WIFI CALLING? WiFi calling through smartphones has been around for a few years. But despite it being a common feature on Android and iOS devices, many don't realize that it’s disabled by default. Still, looking at the numbers, more mobile users are indeed enabling WiFi calling.So, if your organization embraces BYOD, you’re going to want to make sure your network is optimized for voice communications. SMART SECURITY STRATEGIES FOR THE WORLD OF SOCIAL MEDIA As a way to avoid risks, social media security is vital for every business or enterprise in blocking targeted attacks, securing corporate accounts from compromise, fighting scams, and frauds. NETWORK TROUBLESHOOTING: CONSIDER THE LOAD BALANCER Troubleshooting network issues can be tricky, and adding a load balancer into the mix creates additional challenges. Trying to discern if the load balancer is simply dropping packets, changing the packets in some way, or adding more latency can be difficult. IT CHIMES IN: HOW EFFECTIVE IS FACIAL RECOGNITION As results, performance factors, and challenges of using facial recognition systems come to light, interest spreads for IT managers. SINGLE POINT OF FAILURE: THE INTERNET No matter how well you architect for redundancy and availability, there will certainly be single points of failure (SPOF) that you can't account for. The SPOF, in all of its forms, can make application mobility via VDI, cloud services, and netbooks like Google's Chromebook less attractive computing options when compared to fat clients, fat servers, and boring but reliable storage. HACKERS TARGETING ROUTER DEVICES: IS YOUR HOUSEHOLD Millions of households are currently at risk of cyber attacks from hackers because they're running outdated and unpatched routers.NORMAN LEWIS
Norman Lewis is an experienced Data Scientist with a demonstrated history of working in the big data and machine learning industry. Skilled in R, Python (programming language), machine learning, artificial intelligence, algorithms development, mathematical modeling, and data analysis. Skip to main contentInforma
Network Computing is part of the Informa Tech Division of Informa PLC* Informa PLC
* About us
* Investor relations* Talent
This site is operated by a business or businesses owned by Informa PLC and all copyright resides with them. Informa PLC's registered office is 5 Howick Place, London SW1P 1WG. Registered in England and Wales.Number 8860726.
Network Computing
Subscribe
Toggle User Menu Toggle Search* Sign In
* Join
SEARCH FORM
Search
Toggle navigation
Menu
* Topics
* Careers and Certifications * Cloud Infrastructure* Data Centers
* Network Security
* Networking
* Wireless Infrastructure* Resources
* Events
* Reports
* Slideshows
* Webinars
* Whitepapers
* Our IT Network
* Interop
* InformationWeek
* Dark Reading
* About
* About Network Computing* Advertise
SHORTAGE-PROCESSOR-3079887_640.JPGNetworking
Semiconductor Shortage Hurts Network Equipment Makers and Customers Semiconductors are scarce, and so are many types of network gear. The wait for things to get back to normal may be a long one. MESH-NETWORK-1246209_640.JPG Cloud Infrastructure Can OpenTelemetry Fix the Microservices Mess? OpenTelemetry combined with analysis that produces actionable insights will go a long way toward making microservices more manageable. CYBER-SECURITY-3400555_640.JPGNetwork Security
The Time is Now for Remote Browser Isolation By preventing the enemy from gaining a foothold in your organization from which they can move laterally within your network, RBI lets you take the high ground and gain control of the cyber...See All Articles
EXPERT INSIGHTS
Are You Ready to Support the “Branch Office of One”?Jonathan Nguyen-Duy
June 04, 2021
With a unified and integrated approach to security and networking, digital innovation can proceed uninterrupted, enabling users to... Four Factors Driving 100 Gbps Network UpgradesRon Stein
June 03, 2021
As with all generational changes and upgrades, plan carefully, make sure that the monitoring fabric is an integral part of that plan, andput...
For Massive Analytics: Precompute or Virtualize?Li Kang
June 02, 2021
Data virtualization or precomputation? In the cloud era, where literally every operation has an associated cost, it is important toknow the...
Sponsored ContentRansomware Remains a Top Threat. Are BusinessesPrepared?
To stay ahead of attacks, take a proactive approach to your cybersecurity strategy and invest in solutions that can identify malicious behavior and facilitate a rapid response within networkinfrastructure.
Brought to you by LogRhythm, Inc. What is the Zoned Namespace Specification?David Woolf
June 01, 2021
The Zoned Namespace specification (ZNS) brings a new command set for host systems to use when accessing SSDs and to get more out ofthose...
3 Reasons to Process Closer to the EdgeJim Demetrius
May 28, 2021
Being able to increase processing speeds will inevitably improve productivity and efficiency, but more importantly, edge computing willhelp...
Matching 5G Demands with the Right TechnologyJeff Morris
May 27, 2021
The push for 5G-enabled apps reveals the need for data platforms to sync and scale across diverse networks. Are your applications readyto...
REPORTS
SASE's Pandemic Boost Likely to Stick Secure Access Service Edge (SASE) is one framework that combines networking and security functions into a single, cloud-native environment that helps IT professionals to manage multiple point solutions across a myriad of IT domains. Download this report to readmore!
DOWNLOAD NOW!
Planning Your Digital Transformation RoadmapMORE REPORTS
THE DEFINITIVE GUIDE TO AN EFFECTIVE IT AUTOMATION STRATEGY Explore the options available to IT leaders to better understand not only ways to automate, but also how to intelligently plan the strategy to avoid costly overruns and complexities in implementation. After all, winging it or automating piecemeal processes or departments without a careful and comprehensive plan can ironically lead to business slowdowns and soaring expenses.JUNE 15, 2021
OnlineJoin Us
Bob Wallace
Taking a Closer Look at Facial Recognition Sports Industry Execs Share Challenges and Approaches to CreatingAnalytics
Planning for a Rural Broadband Breakout Advances Speed Time to Massive IoT Asset Tracking and Monitoring First Statewide Public IoT Network to Span Digital Divide in NYSee All Articles
John Edwards
Semiconductor Shortage Hurts Network Equipment Makers and Customers Why IT Leaders Should Make Cloud Training a Top Priority New Storage Trends Promise to Help Enterprises Handle a DataAvalanche
Finding the Right Balance of On-Site and At-Home IT Workers VPN's Days Are Numbered: Here Comes Zero-Trust SecuritySee All Articles
Andrew Froehlich
Do Private Data Centers Make Sense Anymore? Understanding the 3 Key Edge Deployment Options How SASE Architectures Can Reach Beyond Cybersecurity Using the Cloud as WAN Transport Seamlessly Merging Private Mobile Networks with Corporate LANsSee All Articles
SUBSCRIBE TO OUR NEWSLETTERS Stay informed! Sign up to get expert advice and insight delivered direct to your inboxSign Up
CAREERS AND CERTIFICATIONS POWER-OUTAGE-FLASH-3604917_640.JPG A Near Miss and a Total Loss: Lessons from 2021 in Data CenterResiliency
Tom Kiblin
May 14, 2021
CLOUD-COMPUTING-3385323_640.JPG Why IT Leaders Should Make Cloud Training a Top PriorityJohn Edwards
April 22, 2021
CODING-COMPUTER-1873831_640.PNG App Modernization Goes Mainstream AgainLori MacVittie
March 09, 2021
BINARY-3725324_1280
BizOps: Powering Data-Driven Decision MakingSerge Lucio
January 06, 2021
See All Careers and Certifications ArticlesNETWORKING
WORK-FROM-HOME-4987741_640.PNG Are You Ready to Support the “Branch Office of One”?Jonathan Nguyen-Duy
June 04, 2021
DATA-CENTER-CABLING-BOARD-1161969_640.JPG Four Factors Driving 100 Gbps Network UpgradesRon Stein
June 03, 2021
FLASH-DATA-2899901_640.JPG What is the Zoned Namespace Specification?David Woolf
June 01, 2021
5G DATA CENTER.JPG
Matching 5G Demands with the Right TechnologyJeff Morris
May 27, 2021
See All Networking Articles WIRELESS INFRASTRUCTURE5G DATA CENTER.JPG
Matching 5G Demands with the Right TechnologyJeff Morris
May 27, 2021
5G-TECHNOLOGY-5348129_640.JPG And Again, About 5G Network SecurityDavid Balaban
April 27, 2021
5G-CONVERGED-MAP-5457622_640.PNG Realizing the Full Potential of 5G Requires Converged NetworkingJonathan Nguyen-Duy
April 15, 2021
5G DATA CENTER.JPG
Five Disruptive Features of Tomorrow’s 6G NetworksMichael Peeters
April 09, 2021
See All Wireless Infrastructure Articles RECOMMENDED RESOURCESWEBINARS
* 4 Practical Tips for Building a Data Lake * FREE Virtual Event: Multi-Cloud Architecture and Mgmt * Multi-Cloud Data Management for Modern ApplicationsSee all Webinars
WHITEPAPERS
* Ransomware Security Breach Summary: Food Production * 2021 Email Threat Report * Threat Intel Challenges of Next-Gen Firewalls See all Whitepapers in the Tech LibrarySee All Videos
TOP VIDEOS
*
INTEROP DIGITAL KEYNOTE: DEMOCRATIZING DATAFebruary 12, 2021
Microsoft’s Alysa Taylor talks about democratizing data and shares use cases where it can help IT have a major impact on businessresults.
*
INTEROP DIGITAL KEYNOTE: IT LEADERSHIP CHALLENGESFebruary 12, 2021
FedEx CIO Rob Carter offers insights on overcoming infrastructure challenges and how the right culture is critical to success.*
INTEROP DIGITAL KEYNOTE: CLOUD COMPUTING AND SECURITYFebruary 11, 2021
Microsoft’s Gunter Ollmann discusses the growing reliance on AI to meet cloud-driven security and networking demands.*
INTEROP DIGITAL KEYNOTE: ENABLING INNOVATION WITHOUT DISRUPTIONFebruary 11, 2021
VMware’s Greg Lavender shares the secrets to balancing long term vision with the practical needs to get things done today.*
IT MANAGEMENT AUTOMATION SPECTRUMMay 18, 2020
IT organizations are deploying technologies that take manual work out of the picture and replace them with processes that automatenetwork...
*
DUST: THE SILENT IT EQUIPMENT KILLERSeptember 22, 2019
Tony Fortunato shows you how to prevent IT equipmment downtime and performance problems due to dust. Read the full article here.*
INTEROP 2019 FIRESIDE CHAT: REVAMPING IT INFRASTRUCTURE AFTER A MERGERJuly 15, 2019
Kathy Kountze discusses how Eversource Energy revamped its IT systems after a merger - adopting cloud and SaaS apps - to elevate the...*
ADDRESSING SECURITY CHALLENGES IN DECENTRALIZED ORGANIZATIONSJuly 08, 2019
Interop 2019 Fireside Chat with Stacey Halota : How to make “privacy by design” a reality and IT asset management less painful. Inthis...
*
INTEROP 2019: SHAPING THE FUTURE OF IT CIO LIGHTNING SERIESJuly 01, 2019
CIOs from the NCAA, the City of Detroit, and Hitachi Vantara share a 5-minute lightning talk on what they think is the most critical(and...
*
AN (IR)RATIONAL APPROACH TO INTEROPERABILITY - INTEROP 2019 KEYNOTEJune 26, 2019
In his Interop19 keynote address, Brian McCarson, Vice President & Senior Principal Engineer, Industrial Solutions Division Internetof...
*
CONTAINERS VS. PAAS: A TOUGH CHOICEFebruary 27, 2018
What abstraction layer should IT infrastructure teams provide developers? Containers or Platform-as-a-Service solutions like CloudFoundry...
*
IS LIFT AND SHIFT A VIABLE CLOUD MIGRATION STRATEGY?February 14, 2018
In the rush to the cloud, organizations may be tempted to simply move applications from their private data centers to the public cloud.In...
* Previous
* Next
INTEROP DIGITAL KEYNOTE: DEMOCRATIZING DATAFebruary 12, 2021
INTEROP DIGITAL KEYNOTE: IT LEADERSHIP CHALLENGESFebruary 12, 2021
INTEROP DIGITAL KEYNOTE: CLOUD COMPUTING AND SECURITYFebruary 11, 2021
INTEROP DIGITAL KEYNOTE: ENABLING INNOVATION WITHOUT DISRUPTIONFebruary 11, 2021
Discover more from Informa Tech* Interop
* IT Pro Today
* InformationWeek
* Data Center Knowledge* Dark Reading
* Data Center World
Working With Us
* Contact us
* About Us
* Advertise
* Reprints
Follow Network Computing on Social* __
* __
* __
* __
* Home
* Cookies
* CCPA: Do not sell my personal info* Privacy
* Terms
Copyright © 2021 Informa PLC. Informa PLC is registered in England and Wales with company number 8860726 whose registered and head office is 5 Howick Place, London, SW1P 1WG.×
×
X
This site uses cookies to provide you with the best user experience possible. By using Network Computing, you accept our use of cookies.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0
