Are you over 18 and want to see adult content?
More Annotations
A complete backup of parcesta-mclland.sg
Are you over 18 and want to see adult content?

A complete backup of fasciacongress.org
Are you over 18 and want to see adult content?

A complete backup of grandcanyonairlines.com
Are you over 18 and want to see adult content?

A complete backup of galiantsolutions.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of animeblogs2016.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of rachelandjun.com
Are you over 18 and want to see adult content?
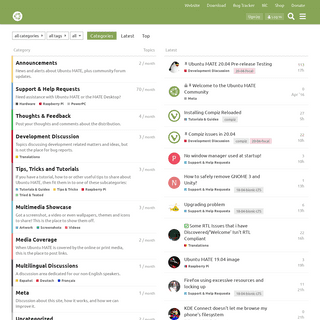
A complete backup of ubuntu-mate.community
Are you over 18 and want to see adult content?

A complete backup of entendiendoelcine.wordpress.com
Are you over 18 and want to see adult content?

A complete backup of decision-wise.com
Are you over 18 and want to see adult content?
Text
PAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. AUTOMATICALLY BACKUP MY DOCUMENTS FOLDER TO GOOGLE DRIVE Google Drive can be sync’d automatically with your My Documents. On Microsoft Windows systems My Documents (or just Documents on Vista/7/8) is the name of a special folder on the computer’s hard drive that the system commonly uses to store a user’s documents, music, pictures, downloads, and other files. FUCK THAT: A GUIDED MEDITATION 0:00. 0:00 / 2:30. Live. •. Are you stressed out? Storyteller Jason Headley provides us with a great way to relax and chill out from the everyday B.S. with a guided meditation session like no other. Best with headphones on and eyes closed. Ommmmmmmmmmmmmmmmmmmm. Check thisout
HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to DOWNLOAD TWEETS FROM TWITTER: HOW TO Download Tweets: Save As. This is the most simple method to download Tweets. From your Twitter page, or the page of anyone else, simple tell your browser to ‘Save As’ and download the page. In Chrome the easiest way to do this is to right click on the page and click ‘Save As’. A dialog box will appear and you can name the download,and
HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this WINDOWS 7 PRINTER PROBLEM: ACCESS IS DENIED, UNABLE TO Once you are in Print Management you’ll see your printer listed. If you try to delete it you get the nasty Access is Denied, Unable to Remove Device dialog box. Right click on your printer and select ‘Properties’. Once this displays you’ll see the problem your printer is listed but your account (or a group you belong to)doesn’t
COMPLETELY MEANINGLESS 'PARTIALLY PRODUCED WITH GENETIC Completely meaningless 'partially produced with genetic engineering' will soon be on food labels. Soon you will see the words “partially produced with genetic engineering” in the fine print on many food packages. Activist groups have spent millions of dollars fighting for that tiny text, and food companies have spent millions fighting back. AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005 The old skool way is to open a command prompt and type the following: rundll32.exe keymgr.dll,KRShowKeyMgr. When you do you’ll see the Stored User Names and Passwords. Just edit or remove the problematic share. The new skool way (and thisPAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. AUTOMATICALLY BACKUP MY DOCUMENTS FOLDER TO GOOGLE DRIVE Google Drive can be sync’d automatically with your My Documents. On Microsoft Windows systems My Documents (or just Documents on Vista/7/8) is the name of a special folder on the computer’s hard drive that the system commonly uses to store a user’s documents, music, pictures, downloads, and other files. FUCK THAT: A GUIDED MEDITATION 0:00. 0:00 / 2:30. Live. •. Are you stressed out? Storyteller Jason Headley provides us with a great way to relax and chill out from the everyday B.S. with a guided meditation session like no other. Best with headphones on and eyes closed. Ommmmmmmmmmmmmmmmmmmm. Check thisout
HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to DOWNLOAD TWEETS FROM TWITTER: HOW TO Download Tweets: Save As. This is the most simple method to download Tweets. From your Twitter page, or the page of anyone else, simple tell your browser to ‘Save As’ and download the page. In Chrome the easiest way to do this is to right click on the page and click ‘Save As’. A dialog box will appear and you can name the download,and
HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this WINDOWS 7 PRINTER PROBLEM: ACCESS IS DENIED, UNABLE TO Once you are in Print Management you’ll see your printer listed. If you try to delete it you get the nasty Access is Denied, Unable to Remove Device dialog box. Right click on your printer and select ‘Properties’. Once this displays you’ll see the problem your printer is listed but your account (or a group you belong to)doesn’t
COMPLETELY MEANINGLESS 'PARTIALLY PRODUCED WITH GENETIC Completely meaningless 'partially produced with genetic engineering' will soon be on food labels. Soon you will see the words “partially produced with genetic engineering” in the fine print on many food packages. Activist groups have spent millions of dollars fighting for that tiny text, and food companies have spent millions fighting back. AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005 The old skool way is to open a command prompt and type the following: rundll32.exe keymgr.dll,KRShowKeyMgr. When you do you’ll see the Stored User Names and Passwords. Just edit or remove the problematic share. The new skool way (and thisPAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. LITTLE GIRL TO STREET PREACHER: PIE HOLE SHOULD BE QUIET! In the very least she should have been taught 1) Respect your elders, and 2) Respect other peoples beliefs. I have friends who are atheist, gay, muslim, witnesses, and so on. HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this TOP 10 BEST BEATBOXERS OF ALL TIME Direct from BeatAndBombs.com comes the Top 10 Best Beatboxers Of All Time. There was no doubt in my mind that Rahzel would take the crown as the guy is simply amazing. Anyway on to the list. Beatboxing has been around in some form for thousands years. I ORDERED A CHICKEN AND AN EGG FROM AMAZON. I’LL LET YOU KNOW I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). I’m fascinated by ninjas, the Internet, and anybody who can balance objects on their nose for long periods of time. COMPLETELY MEANINGLESS 'PARTIALLY PRODUCED WITH GENETIC Completely meaningless 'partially produced with genetic engineering' will soon be on food labels. Soon you will see the words “partially produced with genetic engineering” in the fine print on many food packages. Activist groups have spent millions of dollars fighting for that tiny text, and food companies have spent millions fighting back. BATTERYBAR PRO: EVEN BATTER TASKBAR BATTERY MANAGEMENT BatteryBar Free version use is as as easy as could be. Simply right-clicking on the taskbar and choosing Toolbars -> BatteryBar from the menu. The meter button changes from blue to green when you are on battery power, and clicking on the meter button switches the display between actual time remaining or a percentage view. FRALEY V. FACEBOOK IS ACTUALLY A LEGIT LAWSUIT The crazy this is that Fraley v. Facebook is actually a legitimate filed in California against Facebook alleging misappropriation of Facebook users’ names and likenesses in advertisements called “Sponsored Stories”. The case resulted in the parties reaching a settlement. Fraley v. Facebook is a real class action suit. HOW TO ACCESS ADMINISTRATIVE SHARES ON WINDOWS 7 OR VISTA (C$) I rarely use network shares on my computers. Ok, I have a few setup for the family to use if they need to copy something from one computer to another and a share for our network storage. THE APPLICATION LOGSPROVIDER (PROCESS COM.SEC.ANDROID Intente con la opcion sugerida y funcionaba a medias, despues me pasaron esta que dejo mi teléfono funcionando a la perfeccion, se las comparto por si les pasa, a mi me salvo mis contactos, y mucho tiempoy estres
PAULSPOERRY.COM
May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. FUCK THAT: A GUIDED MEDITATION I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). 9 FUNNY AND MISLEADING WEB SITE DOMAIN NAMES Either the web masters didn’t think carefully enough about their domain names, or they purposely do this for a laugh, but there are sure some weird domains out there. HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or LOGITECH MX PERFORMANCE MOUSE FREEZES Oddly, once I paired the K800 the Logitech MX Performance mouse started freezing. It was erratic and unpredictable but gettingsupremely annoying.
NULL PRINT ERROR WITH WINDOWS UPDATE AND HOW TO RESOLVE I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this HOW TO: SYNC BROWSER SESSIONS BETWEEN MULTIPLE COMPUTERS Stable channel: This channel has gotten the full testing and blessing of the Chrome test team, and is the best bet to avoid crashes and other issues. It’s updated roughly every two-three weeks for minor releases, and every 6 weeks for major releases. Beta channel: If you are interested in seeing what’s next, with minimal risk, Beta channel is the place to be. AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005 I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased).PAULSPOERRY.COM
May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. FUCK THAT: A GUIDED MEDITATION I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). 9 FUNNY AND MISLEADING WEB SITE DOMAIN NAMES Either the web masters didn’t think carefully enough about their domain names, or they purposely do this for a laugh, but there are sure some weird domains out there. HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or LOGITECH MX PERFORMANCE MOUSE FREEZES Oddly, once I paired the K800 the Logitech MX Performance mouse started freezing. It was erratic and unpredictable but gettingsupremely annoying.
NULL PRINT ERROR WITH WINDOWS UPDATE AND HOW TO RESOLVE I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this HOW TO: SYNC BROWSER SESSIONS BETWEEN MULTIPLE COMPUTERS Stable channel: This channel has gotten the full testing and blessing of the Chrome test team, and is the best bet to avoid crashes and other issues. It’s updated roughly every two-three weeks for minor releases, and every 6 weeks for major releases. Beta channel: If you are interested in seeing what’s next, with minimal risk, Beta channel is the place to be. AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005 I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased).PAULSPOERRY.COM
May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. HOW TO: SYNC BROWSER SESSIONS BETWEEN MULTIPLE COMPUTERS Stable channel: This channel has gotten the full testing and blessing of the Chrome test team, and is the best bet to avoid crashes and other issues. It’s updated roughly every two-three weeks for minor releases, and every 6 weeks for major releases. Beta channel: If you are interested in seeing what’s next, with minimal risk, Beta channel is the place to be. AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to PROGRAMMER PERSONALITY TEST Check out the programmer’s personality test.It is based of the Myers-Briggs Personality Test and has been changed to relate to your programming personality type. This is not a joke test and is really only relevant to programmers, however anyone is welcome to take the test.� There are 12 questions with 2 answers for each question and you must choose one answer from each and every THE BEST WAY TO CONTROL MULTIPLE COMPUTERS WITH A SINGLE What’s the best way to control multiple computers with a single keyboard and mouse? InputDirector. Using multiples computers in a single space has always been a pain. All those keyboards, displays, and mice not only take up a considerable amount of space but movingfrom one to
LITTLE GIRL TO STREET PREACHER: PIE HOLE SHOULD BE QUIET! +Bearman Cartoons except that he's the one with a bullhorn not asking if people even want to be spoken to, he's just over a bullhorn yelling at people about how they're going to hell unless they subscribe to hisdogmatic views.
BATTERYBAR PRO: EVEN BATTER TASKBAR BATTERY MANAGEMENT I originally review BatteryBar back in Feb 2009 in the article “BatteryBar – Ultimate taskbar battery management“. Essentially, BatteryBar adds a slick looking battery life meter to the Windows taskbar. It comes with detailed battery life information and some gorgeous eye candy in a mouse over dialog. My original review covered the standard “FREE” version of BatteryBar and outlined AUTOMATICALLY BACKUP MY DOCUMENTS FOLDER TO GOOGLE DRIVE Google Drive can be sync’d automatically with your My Documents. On Microsoft Windows systems My Documents (or just Documents on Vista/7/8) is the name of a special folder on the computer’s hard drive that the system commonly uses to store a user’s documents, music, pictures, downloads, and other files. FRALEY V. FACEBOOK IS ACTUALLY A LEGIT LAWSUIT The gist of Fraley v.Facebook is that Facebook was using Facebook users’ names and likenesses in advertisements called “Sponsored Stories”. The Fraley v. Facebook, Inc. a website www.fraleyfacebooksettlement.com describes sponsored stories as: Sponsored Stories are a form of advertising that typically contain posts which appear on facebook.com about or from a Facebook user SCALING REMOTE DESKTOP TO SPECIFIC RESOLUTION (AKA STILL There’s no denying that Remote Desktop is one of the greatest features of Windows. It’s incredibly handy and it’s speed and performance beats VNC and many other remote control solutions in speed and picture quality.PAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. FRALEY V. FACEBOOK IS ACTUALLY A LEGIT LAWSUIT The crazy this is that Fraley v. Facebook is actually a legitimate filed in California against Facebook alleging misappropriation of Facebook users’ names and likenesses in advertisements called “Sponsored Stories”. The case resulted in the parties reaching a settlement. Fraley v. Facebook is a real class action suit. FUCK THAT: A GUIDED MEDITATION 0:00. 0:00 / 2:30. Live. •. Are you stressed out? Storyteller Jason Headley provides us with a great way to relax and chill out from the everyday B.S. with a guided meditation session like no other. Best with headphones on and eyes closed. Ommmmmmmmmmmmmmmmmmmm. Check thisout
HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to AUTOMATICALLY BACKUP MY DOCUMENTS FOLDER TO GOOGLE DRIVE Google Drive can be sync’d automatically with your My Documents. On Microsoft Windows systems My Documents (or just Documents on Vista/7/8) is the name of a special folder on the computer’s hard drive that the system commonly uses to store a user’s documents, music, pictures, downloads, and other files. LITTLE GIRL TO STREET PREACHER: PIE HOLE SHOULD BE QUIET! +Bearman Cartoons except that he's the one with a bullhorn not asking if people even want to be spoken to, he's just over a bullhorn yelling at people about how they're going to hell unless they subscribe to hisdogmatic views.
DOWNLOAD TWEETS FROM TWITTER: HOW TO Download Tweets: Save As. This is the most simple method to download Tweets. From your Twitter page, or the page of anyone else, simple tell your browser to ‘Save As’ and download the page. In Chrome the easiest way to do this is to right click on the page and click ‘Save As’. A dialog box will appear and you can name the download,and
AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005EXTENDED ERROR HAS OCCURRED MAPPINGAN AUTHENTICATION ERROR HAS OCCURRED WINDO…AN ERROR HAS OCCURRED CRAIGSLISTAN ERROR HAS OCCURRED PLAYSTATIONAN INTERNAL ERROR HAS OCCURREDAN UNKNOWN ERROR HAS OCCURRED The old skool way is to open a command prompt and type the following: rundll32.exe keymgr.dll,KRShowKeyMgr. When you do you’ll see the Stored User Names and Passwords. Just edit or remove the problematic share. The new skool way (and this THE APPLICATION LOGSPROVIDER (PROCESS COM.SEC.ANDROIDANDROID APP LOGANDROID FILE PROVIDERANDROID LOG INFOANDROID PROVIDERS DOWNLOADSANDROID SYSTEM LOGCALENDAR PROVIDER ANDROID /The application LogsProvider (process com.sec.android.provider.logsprovider) has stopped unexpectedly.PAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. FRALEY V. FACEBOOK IS ACTUALLY A LEGIT LAWSUIT The crazy this is that Fraley v. Facebook is actually a legitimate filed in California against Facebook alleging misappropriation of Facebook users’ names and likenesses in advertisements called “Sponsored Stories”. The case resulted in the parties reaching a settlement. Fraley v. Facebook is a real class action suit. FUCK THAT: A GUIDED MEDITATION 0:00. 0:00 / 2:30. Live. •. Are you stressed out? Storyteller Jason Headley provides us with a great way to relax and chill out from the everyday B.S. with a guided meditation session like no other. Best with headphones on and eyes closed. Ommmmmmmmmmmmmmmmmmmm. Check thisout
HOW TO CHECK IF A SQL SERVER RULE IS BOUND TO A COLUMN A SQL Server RULE specifies the acceptable values that can be inserted into a database column. Let’s see how to find out if a RULE is bound to a column in SQL Server and how to remove them. A RULE is very much like a check constraint; except that they only work in T-SQL and Microsoft has deprecated them. A SQL Server RULE is intended to check information as new rows are inserted or AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to AUTOMATICALLY BACKUP MY DOCUMENTS FOLDER TO GOOGLE DRIVE Google Drive can be sync’d automatically with your My Documents. On Microsoft Windows systems My Documents (or just Documents on Vista/7/8) is the name of a special folder on the computer’s hard drive that the system commonly uses to store a user’s documents, music, pictures, downloads, and other files. LITTLE GIRL TO STREET PREACHER: PIE HOLE SHOULD BE QUIET! +Bearman Cartoons except that he's the one with a bullhorn not asking if people even want to be spoken to, he's just over a bullhorn yelling at people about how they're going to hell unless they subscribe to hisdogmatic views.
DOWNLOAD TWEETS FROM TWITTER: HOW TO Download Tweets: Save As. This is the most simple method to download Tweets. From your Twitter page, or the page of anyone else, simple tell your browser to ‘Save As’ and download the page. In Chrome the easiest way to do this is to right click on the page and click ‘Save As’. A dialog box will appear and you can name the download,and
AN EXTENDED ERROR HAS OCCURRED OR ERROR CODE 0X80004005EXTENDED ERROR HAS OCCURRED MAPPINGAN AUTHENTICATION ERROR HAS OCCURRED WINDO…AN ERROR HAS OCCURRED CRAIGSLISTAN ERROR HAS OCCURRED PLAYSTATIONAN INTERNAL ERROR HAS OCCURREDAN UNKNOWN ERROR HAS OCCURRED The old skool way is to open a command prompt and type the following: rundll32.exe keymgr.dll,KRShowKeyMgr. When you do you’ll see the Stored User Names and Passwords. Just edit or remove the problematic share. The new skool way (and this THE APPLICATION LOGSPROVIDER (PROCESS COM.SEC.ANDROIDANDROID APP LOGANDROID FILE PROVIDERANDROID LOG INFOANDROID PROVIDERS DOWNLOADSANDROID SYSTEM LOGCALENDAR PROVIDER ANDROID /The application LogsProvider (process com.sec.android.provider.logsprovider) has stopped unexpectedly.PAULSPOERRY.COM
May 22, 2020 by Paul Spoerry. May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. CATEGORIES - PAULSPOERRY.COM PaulSpoerry.com Social Media, Technology, and geeky stuff for yourbrain.
CONTACT - PAULSPOERRY.COM If you have a professional inquiry, comments or critiques over content on the site, or anything else feel free to get in touch with me through my consulting siteTHE PLUS EDITOR
Google Chrome users can use Post Editor for Google+, an extension that adds formatting controls directly into the post box.But what if you use another browser, or if you want to know how to format via your mobile phone? The Plus Editor is a simple, yet powerful text editorfor Google+.
AUTOMATICALLY LOG OFF INACTIVE WINDOWS 7 USERS Automatically Log Off Inactive Windows 7 Users after a specified period of time; learn two different methods to automatically log off an inactive user on Windows 7.. In my house we have a media server/Minecraft machine that my son uses. It runs Plex, our shared iTunes library, etc. In addition to that it’s the main machine my kid uses to surf the net or, more importantly to him lately, to BIBLEVIZ – AN INTERACTIVE CHART OF BIBLICAL CONTRADICTIONS BibleViz – An Interactive Chart of Biblical Contradictions. There are 63,779 cross references in the Bible (if a verse in the New Testament referred back to a verse in the Old Testament). Some would call that complex but given the number of contradictions others would call it a book in desperate need of an editor even a shitty one. Many HOW TO GET AN INVITE TO WHAT.CD What.cd is an exclusive, invite-only music BitTorrent tracker and community. If you’re trying to get an invite to What.cd you have two options: score an invite from an existing user or go through an interview process via IRC and get invited by a What.cd staff member.Here we’ll focus on the latter of the two methods. If you had an invite you wouldn’t be reading this LITTLE GIRL TO STREET PREACHER: PIE HOLE SHOULD BE QUIET! In the very least she should have been taught 1) Respect your elders, and 2) Respect other peoples beliefs. I have friends who are atheist, gay, muslim, witnesses, and so on. HOW TO: SYNC BROWSER SESSIONS BETWEEN MULTIPLE COMPUTERS Stable channel: This channel has gotten the full testing and blessing of the Chrome test team, and is the best bet to avoid crashes and other issues. It’s updated roughly every two-three weeks for minor releases, and every 6 weeks for major releases. Beta channel: If you are interested in seeing what’s next, with minimal risk, Beta channel is the place to be. I ORDERED A CHICKEN AND AN EGG FROM AMAZON. I’LL LET YOU KNOW I’m a groovy cat who’s into technology, Eastern Thought, and house music. I’m a proud and dedicated father to the coolest little guy on the planet (seriously, I'm NOT biased). I’m fascinated by ninjas, the Internet, and anybody who can balance objects on their nose for long periods of time.PAULSPOERRY.COM
SOCIAL MEDIA, TECHNOLOGY, AND GEEKY STUFF FOR YOUR BRAIN.LET’S CONNECT!
*
*
*
*
*
*
* Home
* About
* Privacy Policy
* Categories
* Google+ Posts
* Site news
* Tech
* Android
* Apple
* Chrome
* Gadgets
* Hacking
* Linux
* OSX
* Privacy
* Web Life
* Bittorrent
* FireFox
* GMail
* Google+
* WordPress
* Windows
* Windows 7
* Google+: Getting Started Guides* Games
* Meditation
* Politics
* Science
* That’s freakin hilarious* Code
* FreeImageZoom
* Post Editor for Google+™* The Plus Editor
* Contact
HAPPY BITCOIN BITCOIN PIZZA DAY! May 22, 2020 by Paul Spoerry May 22, 2010 marks the 10th anniversary of the first Bitcoin transaction, in which a Florida man paid for two pizzas with the Bitcoin. The day has become part of folklore, not because of the transaction, but more the price: Laszlo Hanyecz paid 10,000 Bitcoins for two Papa John’s pizzas. In a recent interview, he said pizzas were delicious and that he does not regret anything. 10,000 $BTC is now worth around $92 _Million_USD.
Organized on bitcointalk forum, the Florida man reached out for help. “I’ll pay 10,000 bitcoins for a couple of pizzas.. like maybe 2 large ones so I have some left over for the next day,” Hanyeczwrote.
“I like having left over pizza to nibble on later. You can make the pizza yourself and bring it to my house or order it for me from a delivery place, but what I’m aiming for is getting food delivered in exchange for bitcoins where I don’t have to order or prepare it myself, kind of like ordering a ‘breakfast platter’ at a hotel or something, they just bring you something to eat and you’re happy!” A British man took up Hanyecz’s offer and bought the two pizzas for him in exchange for the 10,000 Bitcoins. Even then the recipient of the Bitcoins got himself a bargain, paying $25 for the pizzas, while 10,000 Bitcoins were worth around $41 at the time. Despite the astronomical rise in the price of Bitcoin it seems Hanyecz is not phased about his deal. “It wasn’t like Bitcoins had any value back then, so the idea of trading them for a pizza was incredibly cool,” Hanyecz told the NY Times. Filed Under: Cryptocurrency, Tech
ANDROID GAMES TO KEEP YOU BUSY DURING SOCIAL DISTANCING April 10, 2020 by Paul Spoerry No specific order… though these are typically pay games or ones that do NOT require In App Purchases (IAP) to play.* Hades Star
(my current and long running obsession) * Bridge Constructor Portal* Mini Metro
* Monument Valley 2
(1 is great too)
* Island Delta
* Agent A
* Human Resource Machine* Counterspy
* The Room Three
(everything in this series is great though) * Battlevoid Harbinger * First Strike Final Hour* Despotism 3k
* Bad North: Jotunn Edition* Hitman Sniper
(this does have some IAP but I don’t think they are required… they would just speed you up to get additional rifles. I think… it’s been ages and I still don’t uninstall it because I played the every living shit out of this game) Filed Under: Android, Games
, Tech
APPLE’S PRIVACY MYTH NEEDS TO END January 23, 2020 by Paul Spoerry It’s pretty clear that most people have very little understanding of privacy, falling victim to mainstream media’s depiction of it and the world in general—the very power system(s) they’re trying to combat. The belief in Apple as privacy-oriented is one such illusion. So before starting I highly suggest people educate themselves on media and propaganda (I’ll happily provide book recommendations) to develop a more critical framework. A good introduction is thisdocumentary .
A rough summary is that mainstream media are huge corporations whose profit-making comes not from readers/viewers or paid subscribers, but advertisers. This means there’s two important institutional constraints on media ideology: that of their owners and of their buyers. Both inherently determine their values and the kind of content they make. Corporate media are businesses selling products (us, consumers) to other businesses. What kind of ideology and picture of the world do you think you’re getting from that?. The rest of this post is written under the assumption that this sub is informed enough to view Apple as nothing more than “the lesser of evils”. A perspective I will argue is still misguided. 1. USER IDENTIFICATION: Outside the ones shared by all competing products in the industry, there are additional ways to identify you in specifically Appleproducts.
* iOS subliminally and constantly collects sensitive data and links it to hardware identifiers almost guaranteed to link to a realidentity.
* iOS forces users to activate devices which sets up a remote UUID-linked (also collecting registration IP) database for a given device with Apple’s services. * iOS and iOS-based coprocessors force the regular sending of incredibly sensitive metadata to Apple for the mere ability to use the device for questionable and unknown reasons. 2.1. PRIVACY POLICY IN PRACTICE IN REGARDS TO THE AUTHORITIES: Apple is subject to the FISA Amendments Act of 2009,
and PRISM is an example of that law in practice, which Apple is part of (amongst others). As public disclosure of cooperation with authorities have been allowed in in limited degrees in recent years, we’ve seen examples like Apple admitting to complying with 90% of government requests of accessing thousands of user files
every year
. FBI
OPENLY PRAISED THEM FOR PROVIDING “AMPLE ASSISTANCE”. It therefore came as no surprise when a recent leak revealed that the company purposefully kept their phones less secure to makeaccess
easier for the authorities.
Despite all this, Apple is still most associated with the FBI encryption dispute in 2015, which has been a huge PR success for them. The latter case, which was
completely fraudulent,
is still widely circulated and frequently brought up as demonstration of Apple’s integrity. In reality it was a demonstration, like the general theme of much else in this post, of successful media propaganda. Apple (or even FBI) aren’t able to fool professional and well-educated journalists of NYT, WP, etc. They also rely on the media’s conformity through misrepresentation of the available facts, as well as accessible and well-known critique. Apple have outlined how they give virtually everything relevanton
iCloud to the authorities.
As the CEO of ElcomSot, a security company that revealed iCloud was uploading data to Apple servers without users knowing, said: “The takeaway really is don’t ever used iCloud”.Apple
having the encryption keys to iCloud as well as other parts of your iPhone completely invalidates the point of E2EE, and might explainwhy/how NSA MINES
DATA
DIRECTLY FROM THEIR SERVERS.
The company’s respect for privacy is no better outside the US. We know that they oblige and assist authoritarian governmentslike
China in installing firewalls to block citizens’ access to encrypted tools, like social media apps. They’re actively undermining people’s security and privacy from violent regimes for the sake ofprofit.
2.2. PRIVACY POLICY IN PRACTICE IN REGARDS TO THE PRIVATE INDUSTRY.Apple sell
certificates
to third-party developers that allow them
to
track users within
their
own
app
s
—THIRD-PARTY
DEVELOPERS ARE ALLOWED TO COLLECT DATA ON IOS. Facebook’s privacy scandal (interestingly, Apple themselves were one of the main partners buying data from Facebook)
involved iOS users as well due to the mentioned tracking. Apple reacted to the scandal with another publicity stunt by superficially punishing Facebook. A real response, like removing Facebook from the App Store or removing their ability to track you, did not happen. The company attacks Google and Facebook’s intrusion on users’ privacy, yet are enabling them and other businesses in doing so on their products. They even use Google as Safari’s default searchprovider—making
12
billion USD in 2019 alone from this deal. If they really cared about privacy they would deny the ability of privacy-invasive apps to collect any user date. They don’t because these apps’ importance in keeping their products’ platform popular and therefore profitable. 3. THE LACK OF OPEN SOURCE CODE. Open source code, specifically those that have been audited, is for obvious reasons much safer than closed source ones. Even government agencies take it into account in choosing secure software for their members. It is all the more important when the company in question surrenders data to state authorities, allows third-party developers to collect data, have weak security measures(sometimes
on purpose) and have been discovered of numerous suspicious activities. No to mention the fact that Apple’s verification mechanism in designed in such a way that they have the ability to “silently send targeted malicious updates to devices matching specific unique ID criteria”. IOS
IS A TEXTBOOK EXAMPLE OF WHY CLOSED SOURCE IS BAD. Imagine if Huawei, on top of providing third-party developers the ability to track its users, admitted to giving the Chinese government access to user data (but only after it was caught doing so) and were continuously caught in suspicious activities (many involving Chinese authorities)—all on a completely closed source software platform. Would you take their claims of “security” and “privacy”seriously?
Many users (predominately Americans) already have a hard time trusting Huawei, despite 0 evidence of illegal data collectionof
users
or
claimed
connections with the CCP.Users
have bought into US government claims and mainstream media propaganda. At the same time they buy and congratulate Apple for their privacy-oriented approach. A PERFECT EXAMPLE OF A SYSTEM OFINDOCTRINATION.
4. ALTERNATIVES.
Here are some _reasonable_ steps with descending order in how effective they are, that provide you with Android-based alternatives superior to iOS in privacy and security: 1: Disable Google tracking and services in settings (the little that they make available to you) and use F-Droid instead of Play Store. Notwithstanding the lack of privacy in many ways, it’s a goodstarting point.
-At this point your privacy from private companies is a bit betterthan on iOS.
1.5: Some OEMs, like Huawei, simplify and help users uninstall Google apps and services. Huawei’s current products (like Mate Pro 30) also come without all that, due to the current trade war. The phones still come with Huawei bloat and their ad-based data mining, but it’s nowhere as bad as Google and easier to evade. -At this point your privacy from private companies is better than oniOS.
2: Root your device (an easy task) and uninstall all Google apps and services, as well as anything else, completely. -At this point your privacy from both government and private companies is better than on iOS. 3: Install Custom ROMs that allow the same as 2, have even more open software for examination and also include enhanced privacy features in the system (or you can get these as third-party apps). Some, like LineageOS, also provide UI, performance and update cycles superior to almost all the main Android OSes (One UI, MIUI, EMUI, LG UI, etc.) -At this point your privacy from both government and private companies is significantly better than on iOS. 4: GrapheneOS. It provides an exceptional level of privacy and security that has been praised bySnowden
himself.
It runs a stock Android setup with the same pros as LOS above, making it very well from a non-privacy perspective as well. If you want a user-friendly and highly privacy-related platform without having to do a lot of tinkering and manual management, this is the ROM for you. -At this point your privacy from both government and private companies is tremendously better than on iOS. 5. SUMMARY: IPHONES ARE NOT THE BEST ALTERNATIVE FOR DATA PRIVACY. iPhones give no additional security and privacy from the government over Android phones. They only do in limited conditions that are inconsequential to this sub. The minute you want to improve your privacy and security beyond what you get out of the box, iOS is terrible. IT IS NOT THE “LESSER OF EVILS”— A MYTH THAT NEEDS TODIE.
Additionally, positioning themselves as a beacon of privacy make them even more dangerous, as they become a honeypot for people in severe need of privacy. This has profound consequences in authoritarian societies for journalists, demonstrators and other dissidents. COINTELPRO has shown how ugly it can get in free societies as well. If Apple’s software and ecosystem is more important to you than increased security on even some of the best UX alternatives on Android (LOS, GrapheneOS, etc), then at least admit to this hard truth and move on. Spreading misinformation undermines the privacy of others, and doing that to serve your confirmation bias is disingenuous and honestly deplorable. Note: None of this is to say that Google Android is necessarily a secure alternatives in general, only in RELATIVE TERMS – but at least it’s Open Source. Having said that, the hardware it runs on is not and some features they are building in only work on their devices. So if you have a Pixel and want all the features you are locked, essentially, into Close Source hardware due to chips like PVC,Titan, Soli, etc. Pixels with GOS make very little sense due to them being overpriced and having fairly mediocre flagship hardware. Their most fundamental strengths lie in software smoothness and image processing. Both of which are are lost when installing GOS. It’s important to understand that while not ending government intrusion (though severely limiting it and its data mining), the available methods on Android, which include continuous development of new and better measures, tremendously improve on privacy from the private industry. All that is is simply impossible on iOS as a system; its security and privacy out of the box is also all you get. You have zero flexibility on the system and are completely locked in. This is really bad with their track record (covered in OP). All its important hardware being in-house and exclusive to them is even more troubling. A good way to approach hardware security is to see what members of non-allied countries use. To give an example, Germany’ aerospace industry got rid of Cisco routers after discovering backdoors installed in their hardware.The
issue in that case was industrial espionage, which The Five Eyes’ Project ECHELON, as a European Union reporton
the matter states, is “A GLOBAL SYSTEM FOR THE INTERCEPTION OF PRIVATE AND COMMERCIAL COMMUNICATIONS”. As for general surveillance, when Angela Merkel found out that her and other politicians’ Nokia 6260 Slides were tapped by USintelligence
,
she switched to a Blackberry fitted with an encryption chip by Secusmart. The latter company is a popular option for many governmentagencies.
Another thing to consider in a scenario where you need to choose between hardware backdoors of two rivalling countries, is to always go for the rival/enemy. It’s safer for a Chinese citizen to use phones with US-based hardware backdoors, and equally so for a US citizen to use phones with Chinese hardware backdoors. The reason being that the most immediate and relevant threats to you is your own government. They are the ones with sovereignty and monopoly of power over you and they are the ones who care. IF SURVEILLANCE IS THE ONLY CHOICE, IT’S ALWAYS BETTER TO CHOOSE A NON-ALLIED COUNTRY. Of course, the above hardware backdoor example is theoretical. In reality, governments often use dedicated security chips in phones unavailable to regular consumers. Furthermore, companies from non-allied countries cooperate with surveillance laws of local governments. Those relate to software and not hardware though (and this is why Android’s open source nature is extremely important). Much of this is a repost from /r/Privacy. Filed Under: Android, Apple
, Business
, Politics
, Privacy
, Tech
STUDY CONFIRMS CLIMATE MODELS ARE GETTING FUTURE WARMING PROJECTIONSRIGHT
January 11, 2020 by Paul Spoerry For decades, people have legitimately wondered how well climate models perform in predicting future climate conditions. Based on solid physics and the best understanding of the Earth system available, they skillfully reproduce observed data. Nevertheless, they have a wide response to increasing carbon dioxide levels, and many uncertainties remain in the details. The hallmark of good science, however, is the ability to make testable predictions, and climate models have been making predictions since the 1970s. How reliable have they been? Now a new evaluation of global climate models used to project Earth’s future global average surface temperatures over the past half-century answers that question: MOST OF THE MODELS HAVE BEENQUITE ACCURATE.
Models
that were used in the IPCC 4th Assessment Report can be evaluated by comparing their approximately 20-year predictions with what actually happened. In this figure, the multi-model ensemble and the average of all the models are plotted alongside the NASA Goddard Institute for Space Studies (GISS) Surface Temperature Index (GISTEMP) . Climate drivers were known for the ‘hindcast’ period (before 2000) and fore We hit 2012 and everything goes bananas. The coming decades might bepretty rough.
Filed Under: Science GOOGLE EXPOSES 14 LONG-HIDDEN EXPLOITS IN IOS August 30, 2019 by Paul SpoerryLeave a Comment
According to one blog post, the 14 vulnerabilities were a part of five unique iPhone exploit chains that covered almost every version of Apple’s mobile operating system from iOS 10 to the latest version of iOS 12, indicating that the hackers were working hard to exploit thesecurity flaws.
Half of the iPhone vulnerabilities were discovered in Apple’s Safari browser, five in the kernel, and hackers also used two separate sandbox escapes to access data outside the permissions of an app or aprocess.
The attack had such deep access to iPhone systems that hackers could even read or eavesdrop the messages of victims on encrypted communications services like WhatsApp, iMessage, and ProtonMail. “There was no target discrimination,” Ian Beer, a Google hacker and member of the company’s Project Zero team, wrote in a blog. “Simply visiting the hacked site was enough for the exploit server to attack your device, and if it was successful, install a monitoringimplant.”
There’s also a chance that the attackers have acquired access tokens from the Apple victims, which they could use to log into social media and communications accounts. You can read the in-depth posts on Google’s Project Zero blog. Filed Under: Apple ,Hacking , Tech
Next Page »
Copyright © 2021 · Epik on Genesis Framework · WordPress� Log in
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0