Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://www.pinterest.fr/pin/838725130601166366/
Are you over 18 and want to see adult content?
A complete backup of https://sixsixone.com/
Are you over 18 and want to see adult content?

A complete backup of https://dramasq.com/hanzawa/
Are you over 18 and want to see adult content?
A complete backup of https://kuttymovies.netlify.app/
Are you over 18 and want to see adult content?

A complete backup of https://www.pedalpub.com/calgary-ab/
Are you over 18 and want to see adult content?

A complete backup of https://kalyanstarline.com/
Are you over 18 and want to see adult content?
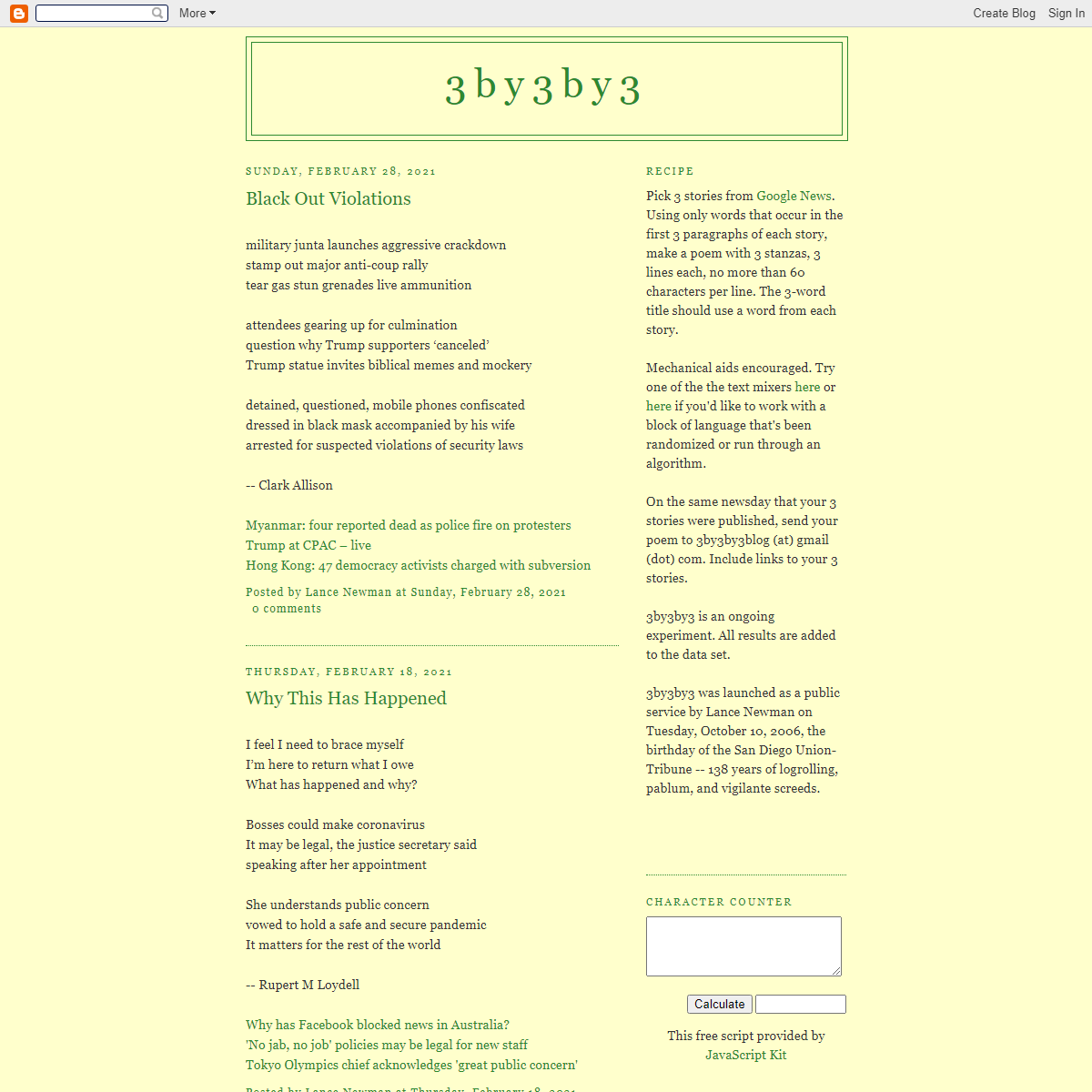
A complete backup of https://3by3by3.blogspot.com/
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of camping-sonnenberg.com
Are you over 18 and want to see adult content?

A complete backup of worshipmusician.com
Are you over 18 and want to see adult content?

A complete backup of repairsponsel.com
Are you over 18 and want to see adult content?
Text
Safeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH The following is the expected output: Then we can leverage the “Invoke-DNSUpdate” command within the PowerMad tool using the “powershell-import” and “powerpick” commands. powerpick Invoke-DNSUpdate -DNSType A -DNSName cloudfiles -DNSData 192.168.109.13. The expected output is shown below. THREAT HUNTING: HOW TO DETECT PSEXEC AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
HOW TO MITIGATE MIMIKATZ WDIGEST CLEARTEXT CREDENTIAL Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit. In the console tree under Computer Configuration or User Configuration, expand the Preferences folder, and then expand the Windows Settings folder. Right-click the Registry node, point to New, and select Registry Item. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH The following is the expected output: Then we can leverage the “Invoke-DNSUpdate” command within the PowerMad tool using the “powershell-import” and “powerpick” commands. powerpick Invoke-DNSUpdate -DNSType A -DNSName cloudfiles -DNSData 192.168.109.13. The expected output is shown below. THREAT HUNTING: HOW TO DETECT PSEXEC AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
HOW TO MITIGATE MIMIKATZ WDIGEST CLEARTEXT CREDENTIAL Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit. In the console tree under Computer Configuration or User Configuration, expand the Preferences folder, and then expand the Windows Settings folder. Right-click the Registry node, point to New, and select Registry Item. HOW TO REDIRECT TRAFFIC FROM AN INCOMING TCP PORT USING Overview. In a previous article titled “Active Directory Computer Account SMB Relaying Attack,” we discussed how an attacker could leverage computers assigned administrative rights to other computers to escalate privileges or move laterally using the printer spooler service.Colloquially we often refer to this as a “Computer AdminTo Computer” vulnerability. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOP AWS IAM Assume Role Vulnerabilities Found in Many Top Vendors. by Kesten Broughton on June 12, 2020. . In this first blog in our series on cross-account-trust we will present the results from 90 vendors showing that 37% had not implemented the ExternalId correctly to protect against confused-deputy attacks. A further 15% of vendors GOOGLE CLOUD IAM: DESIGNS FOR SELF-SERVICE PRIVILEGE Google Cloud IAM: Designs for Self-Service Privilege Escalation. by Andy Gu and Jesse Somerville on May 4, 2021. In a perfect world, all organizations would incorporate security into their cloud environments from the start. Unfortunately, common development practices tend to postpone the implementation of security controls in the product EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. RUNNING A .NET ASSEMBLY IN MEMORY WITH METERPRETER What you’ll need: Visual Studio Code installed on a Windows box (VMs work well) .NET 3.5 and/or .NET 4.0 features installed in Visual Studio. Some C# code to run, Seatbelt. Feel free to use your own code. A Meterpreter session on a target Windows box with the corresponding .NET runtime installed. 15 – 20 minutes. HOW TO PREVENT, DETECT AND REMEDIATE PROXYLOGON In our testing the script has been relatively low impact to the server and should not affect the operation capacity of the server. In our testing the Test-Proxy Logong Script found the majority of the ways we executed the exploit chain, and while it is not fool proof it is still one of the better mechanisms to detect any evidence of proxylogonactivity.
NIST CYBERSECURITY FRAMEWORK VS. NIST SPECIAL PUBLICATION NIST 800-53 is a regulatory document, encompassing the processes and controls needed for a government-affiliated entity to comply with the FIPS 200 certification. In contrast, the Framework is voluntary for organizations and therefore allows more flexibility in its implementation. The Framework builds on and does not replace securitystandards
PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH The following is the expected output: Then we can leverage the “Invoke-DNSUpdate” command within the PowerMad tool using the “powershell-import” and “powerpick” commands. powerpick Invoke-DNSUpdate -DNSType A -DNSName cloudfiles -DNSData 192.168.109.13. The expected output is shown below. THREAT HUNTING: HOW TO DETECT PSEXEC AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
HOW TO MITIGATE MIMIKATZ WDIGEST CLEARTEXT CREDENTIAL Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit. In the console tree under Computer Configuration or User Configuration, expand the Preferences folder, and then expand the Windows Settings folder. Right-click the Registry node, point to New, and select Registry Item. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH The following is the expected output: Then we can leverage the “Invoke-DNSUpdate” command within the PowerMad tool using the “powershell-import” and “powerpick” commands. powerpick Invoke-DNSUpdate -DNSType A -DNSName cloudfiles -DNSData 192.168.109.13. The expected output is shown below. THREAT HUNTING: HOW TO DETECT PSEXEC AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
HOW TO MITIGATE MIMIKATZ WDIGEST CLEARTEXT CREDENTIAL Right-click the Group Policy object (GPO) that should contain the new preference item, and then click Edit. In the console tree under Computer Configuration or User Configuration, expand the Preferences folder, and then expand the Windows Settings folder. Right-click the Registry node, point to New, and select Registry Item. HOW TO REDIRECT TRAFFIC FROM AN INCOMING TCP PORT USING Overview. In a previous article titled “Active Directory Computer Account SMB Relaying Attack,” we discussed how an attacker could leverage computers assigned administrative rights to other computers to escalate privileges or move laterally using the printer spooler service.Colloquially we often refer to this as a “Computer AdminTo Computer” vulnerability. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOP AWS IAM Assume Role Vulnerabilities Found in Many Top Vendors. by Kesten Broughton on June 12, 2020. . In this first blog in our series on cross-account-trust we will present the results from 90 vendors showing that 37% had not implemented the ExternalId correctly to protect against confused-deputy attacks. A further 15% of vendors GOOGLE CLOUD IAM: DESIGNS FOR SELF-SERVICE PRIVILEGE Google Cloud IAM: Designs for Self-Service Privilege Escalation. by Andy Gu and Jesse Somerville on May 4, 2021. In a perfect world, all organizations would incorporate security into their cloud environments from the start. Unfortunately, common development practices tend to postpone the implementation of security controls in the product EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. RUNNING A .NET ASSEMBLY IN MEMORY WITH METERPRETER What you’ll need: Visual Studio Code installed on a Windows box (VMs work well) .NET 3.5 and/or .NET 4.0 features installed in Visual Studio. Some C# code to run, Seatbelt. Feel free to use your own code. A Meterpreter session on a target Windows box with the corresponding .NET runtime installed. 15 – 20 minutes. HOW TO PREVENT, DETECT AND REMEDIATE PROXYLOGON In our testing the script has been relatively low impact to the server and should not affect the operation capacity of the server. In our testing the Test-Proxy Logong Script found the majority of the ways we executed the exploit chain, and while it is not fool proof it is still one of the better mechanisms to detect any evidence of proxylogonactivity.
NIST CYBERSECURITY FRAMEWORK VS. NIST SPECIAL PUBLICATION NIST 800-53 is a regulatory document, encompassing the processes and controls needed for a government-affiliated entity to comply with the FIPS 200 certification. In contrast, the Framework is voluntary for organizations and therefore allows more flexibility in its implementation. The Framework builds on and does not replace securitystandards
PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
WHY PRAETORIAN BENCHMARKS TO MITRE ATT&CK™ AND WHY YOUSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS THREAT HUNTING: HOW TO DETECT PSEXEC ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
CLOUD DATA EXFILTRATION VIA GCP STORAGE BUCKETS AND HOW TO The Solution. Use VPC Service Controls to restrict access to specific GCP resources VPC Service Controls allow users to define a security perimeter around Google Cloud Platform resources such as Cloud Storage buckets, Bigtable instances, and BigQuery datasets to constrain data within a VPC and help mitigate data exfiltration risks. HASHJACKING: ANYONE CAN STEAL YOUR WINDOWS PASSWORDSEE MORE ONPRAETORIAN.COM
CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
WHY PRAETORIAN BENCHMARKS TO MITRE ATT&CK™ AND WHY YOUSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPS THREAT HUNTING: HOW TO DETECT PSEXEC ATTACKING AND DEFENDING OAUTH 2.0 (PART 1 OF 2SEE MORE ONPRAETORIAN.COM
PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
CLOUD DATA EXFILTRATION VIA GCP STORAGE BUCKETS AND HOW TO The Solution. Use VPC Service Controls to restrict access to specific GCP resources VPC Service Controls allow users to define a security perimeter around Google Cloud Platform resources such as Cloud Storage buckets, Bigtable instances, and BigQuery datasets to constrain data within a VPC and help mitigate data exfiltration risks. HASHJACKING: ANYONE CAN STEAL YOUR WINDOWS PASSWORDSEE MORE ONPRAETORIAN.COM
HOW TO REDIRECT TRAFFIC FROM AN INCOMING TCP PORT USING Overview. In a previous article titled “Active Directory Computer Account SMB Relaying Attack,” we discussed how an attacker could leverage computers assigned administrative rights to other computers to escalate privileges or move laterally using the printer spooler service.Colloquially we often refer to this as a “Computer AdminTo Computer” vulnerability. CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20” CIS Controls Version 8 Overview: Bye-Bye “Top 20”. by Trevor Steen on May 20, 2021. The Center for Internet Security (CIS) has just released Version 8 of their popular security controls. With this version, the “Top 20” moniker has been lost and the list of controls reduced to 18. The Version 8 is a major update to theSafeguards, builds
CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH The following is the expected output: Then we can leverage the “Invoke-DNSUpdate” command within the PowerMad tool using the “powershell-import” and “powerpick” commands. powerpick Invoke-DNSUpdate -DNSType A -DNSName cloudfiles -DNSData 192.168.109.13. The expected output is shown below. A NEW TOOL FOR PASSWORD SPRAYING EMULATION A New Tool for Password Spraying Emulation. Password spraying is an attack method in which malicious actors attempt to gain access by “spraying” a large number of user accounts with a small number of commonly used passwords such as “Password123” or “September2020”. While password spraying is not a particularly newor complicated
HASHJACKING: ANYONE CAN STEAL YOUR WINDOWS PASSWORD Physical Access. The Physical attack vector for this issue is very straightforward, but still significant. If you have access to a Windows machine that you would like to know the password to: just type in the address to your malicious SMB share in the browser, and then attempt to crack the hash. If the logged in user has administratorrights
OBTAINING LAPS PASSWORDS THROUGH LDAP RELAYING ATTACKS Conclusion. The application of LDAP relaying and other L2 poisoning attacks provides a unique set of capabilities to red team operators. The difficulty in leveraging these techniques in practice often arises due to the difficulty of leveraging these tools through a reverse shell or “beacon” implant on a Windows machine. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. NIST CYBERSECURITY FRAMEWORK VS. NIST SPECIAL PUBLICATION NIST 800-53 is a regulatory document, encompassing the processes and controls needed for a government-affiliated entity to comply with the FIPS 200 certification. In contrast, the Framework is voluntary for organizations and therefore allows more flexibility in its implementation. The Framework builds on and does not replace securitystandards
PATH.COMBINE SECURITY ISSUES IN ASP.NET APPLICATIONS Path traversal vulnerabilities are a common class of web application vulnerability, where an attacker aims to access files outside of the intended directory by using “../” patterns to traverse directories or by using absolute paths. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPSNATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
BUILDING THE HASHCAT API IN RUBY TO CRACK EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPSNATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
BUILDING THE HASHCAT API IN RUBY TO CRACK EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. HOW TO REDIRECT TRAFFIC FROM AN INCOMING TCP PORT USING Overview. In a previous article titled “Active Directory Computer Account SMB Relaying Attack,” we discussed how an attacker could leverage computers assigned administrative rights to other computers to escalate privileges or move laterally using the printer spooler service.Colloquially we often refer to this as a “Computer AdminTo Computer” vulnerability. ABOUT US | PRAETORIAN Praetorian is a cybersecurity solutions company whose mission is to make the digital world safer and more secure. Through expertise and engineering, Praetorian helps today's leading organizations solve complex cybersecurity problems across critical enterprise assets and product portfolios. From the Cloud to IoT, we are bringing togetherthe
CASE STUDIES ARCHIVE Net Promoter Score (NPS) is a survey system used to gauge client satisfaction and happiness. The Net Promoter Score is calculated off of client responses to a single question: How likely are you to recommend our company to a colleague? The scoring for this answer is based on a 0 to 10 scale. NPS can be as low as −100 (everyone is adetractor
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. THREAT HUNTING: HOW TO DETECT PSEXEC This post is the first in a threat hunting series profiling detection points for common cyber threat actor attack techniques. The series is geared toward network defenders wanting to understand, identify, and protect against these attacks. PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
NIST CYBERSECURITY FRAMEWORK VS. NIST SPECIAL PUBLICATION NIST 800-53 is a regulatory document, encompassing the processes and controls needed for a government-affiliated entity to comply with the FIPS 200 certification. In contrast, the Framework is voluntary for organizations and therefore allows more flexibility in its implementation. The Framework builds on and does not replace securitystandards
PATH.COMBINE SECURITY ISSUES IN ASP.NET APPLICATIONS Path traversal vulnerabilities are a common class of web application vulnerability, where an attacker aims to access files outside of the intended directory by using “../” patterns to traverse directories or by using absolute paths. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPSNATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
BUILDING THE HASHCAT API IN RUBY TO CRACK EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. PRAETORIAN | YOUR SECURITY EXPERTSSUCCESS STORIESSECURITY BLOGWHITEPAPERSABOUT USEXECUTIVE TEAMNEWS + PRESS security experts. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape. with Chariot. Strategic application security orchestration and automation platform. CAREERS | PRAETORIAN 4. CEO Call. 1. Discovery Call. The typical call lasts 30 minutes and is an opportunity for us to get to know more about you. We typically spend about 15 minutes asking you questions to learn more about your passion and interests, then we turn the call over to you for questions you have about Praetorian. REPRODUCING THE MICROSOFT EXCHANGE PROXYLOGON EXPLOITSEE MORE ONPRAETORIAN.COM
AWS IAM ASSUME ROLE VULNERABILITIES FOUND IN MANY TOPSEE MORE ONPRAETORIAN.COM
NIST CYBERSECURITY FRAMEWORK VIGNETTES: BACKUPSNATHAN SPORTSMAN
Nationally recognized as a leader in the cybersecurity field, Nathan is a frequent public speaker, is a contributing author to the world’s best-selling computer security book, Hacking Exposed, is a U.S. patent holder, and has served as an adjunct professor at the University of Texas at Austin (nationally ranked #5 for ComputerScience and
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
BUILDING THE HASHCAT API IN RUBY TO CRACK EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. HOW TO REDIRECT TRAFFIC FROM AN INCOMING TCP PORT USING Overview. In a previous article titled “Active Directory Computer Account SMB Relaying Attack,” we discussed how an attacker could leverage computers assigned administrative rights to other computers to escalate privileges or move laterally using the printer spooler service.Colloquially we often refer to this as a “Computer AdminTo Computer” vulnerability. ABOUT US | PRAETORIAN Praetorian is a cybersecurity solutions company whose mission is to make the digital world safer and more secure. Through expertise and engineering, Praetorian helps today's leading organizations solve complex cybersecurity problems across critical enterprise assets and product portfolios. From the Cloud to IoT, we are bringing togetherthe
CASE STUDIES ARCHIVE Net Promoter Score (NPS) is a survey system used to gauge client satisfaction and happiness. The Net Promoter Score is calculated off of client responses to a single question: How likely are you to recommend our company to a colleague? The scoring for this answer is based on a 0 to 10 scale. NPS can be as low as −100 (everyone is adetractor
GETTING STARTED WITH DAMN VULNERABLE ROUTER FIRMWARE (DVRF Getting Started with Damn Vulnerable Router Firmware (DVRF) v0.1. The goal of the DVRF project is to simulate a real-world environment to help people learn about other CPU architectures outside of the x86_64 space. The project will also help people get into discovering new things about hardware. As of now this DVRF firmware is tailored forthe
EFFECTIVELY MEASURING RISK ASSOCIATED WITH VULNERABILITIES Effectively measuring the risk associated with identified vulnerabilities is one of the challenges associated with providing remediation plan recommendations to our clients. To address this challenge, our team employs a tailored risk rating framework as part of our comprehensive and methodical approach to assessing the security of web applications. ICMP C2 STANDARD NON-APPLICATION LAYER PROTOCOL (ATT&CK ICMP C2 Standard Non-Application Layer Protocol (ATT&CK T1095) Testing network defense tools is one important service that our team offers. We do this by mapping out detection capabilities based on the MITRE ATT&CK™ framework. Praetorian looks at the techniques and measures the organization has implemented to detect certain activities. THREAT HUNTING: HOW TO DETECT PSEXEC This post is the first in a threat hunting series profiling detection points for common cyber threat actor attack techniques. The series is geared toward network defenders wanting to understand, identify, and protect against these attacks. PHP-CGI REMOTE COMMAND EXECUTION VULNERABILITY During a recent penetration test, our team found a few web servers that were vulnerable to a PHP-CGI query string parameter vulnerability ( CVE-2012-1823 ). This vulnerability allows an attacker to execute commands without authentication, under the privileges of the web server. The target environment had very strong egress controls inplace.
NIST CYBERSECURITY FRAMEWORK VS. NIST SPECIAL PUBLICATION NIST 800-53 is a regulatory document, encompassing the processes and controls needed for a government-affiliated entity to comply with the FIPS 200 certification. In contrast, the Framework is voluntary for organizations and therefore allows more flexibility in its implementation. The Framework builds on and does not replace securitystandards
PATH.COMBINE SECURITY ISSUES IN ASP.NET APPLICATIONS Path traversal vulnerabilities are a common class of web application vulnerability, where an attacker aims to access files outside of the intended directory by using “../” patterns to traverse directories or by using absolute paths. Skip To Content Toggle Menu Back* Services
Services
*
WHAT WE DO
Through expertise and engineering, Praetorian helps today’s leading organizations solve complex cybersecurity problems across critical enterprise assets and product portfolios.Learn More
*
ENTERPRISE INFRASTRUCTURESECURITY SERVICES
From NIST CSF to penetration testing, our corporate security engineers help to ensure that your data, networks, and other critical infrastructure is secure.Learn More
*
PRODUCT & APPLICATIONSECURITY SERVICES
From cloud apps to IoT, our product security teams are an extension of your development teams so you can focus on your next wave ofinnovation.
Learn More
* Labs
* Products
Products
*
INTRODUCING CHARIOT BY PRAETORIAN Chariot brings all application security program activities into a single view, giving visibility into the breadth of coverage and opportunities to improve across the entire CI/CD lifecycle.Platform Overview
* Resources
Resources
*
THE PRAETORIAN BLOG
Keep up-to-date on cybersecurity industry trends and the latest tools & techniques from the world’s foremost cybersecurity experts.Visit the Blog
*
WHITEPAPERS
Our whitepapers blend data and thought leadership across a range of security matters, to help you understand an issue, solve a problem, ormake a decision.
Read the Whitepapers*
CHALLENGES
Share our passion for solving puzzles through our CTF and other cyberchallenges.
Explore Challenges
* Who We Are
Who We Are
*
WHO WE ARE
We are on a mission is to make the world a safer and more secure place. Our solutions enable clients to find, fix, stop, and ultimately solve cybersecurity problems across their entire enterprise andproduct portfolios.
Learn More
*
CAREERS
We are hiring! Join the brightest minds in cybersecurity, who share a passion for working hard on behalf of our clients, solving the hardest problems, and making a big impact.Work At Praetorian
Open Listings
*
* Who We Are
Meet our leadership team.* News & Press
Read our latest company news.* Get in Touch
* Contact
YOUR SECURITY EXPERTS. As a collective of highly technical engineers and developers offering deep security expertise, Praetorian solves the toughest challenges faced by today’s leading organizations across an ever-evolving digital threat landscape.More Below
PLATFORM SECURE YOUR FUTUREWITH CHARIOT.
Strategic application security orchestration and automation platform. Explore the Platform * Integrate all security tools across the CI/CD lifecycleinto one view.
* Track vulnerabilities to closure quicklyand easily.
* Leverage the power of machine learning aided identification and remediation. * Tap into the security experts at Praetorian whenhelp is needed.
WHAT WE DO SOLVING YOUR SECURITY PROBLEMS. Through expertise and engineering, Praetorian helps today’s leading organizations solve complex cybersecurity problems across critical enterprise assets and product portfolios.Learn More
*
Application Security Zoom Read Success Story*
21st Century Fox Read Success Story WE ARE OBSESSED WITH YOUR SATISFACTION, BUT DON'T JUST TAKE OUR WORDFOR IT...
2U, INC.
Strengthening enterprise incident response processes and procedures The security team of 2U, Inc., a global leader in education technology, speaks about the ways they worked with Praetorian to exercise, assess,... Explore the Case Story THE LATEST POSTS FROM OURSECURITY EXPERTS.
View All
* Network in Tools & Techniques HOW TO EXPLOIT ACTIVE DIRECTORY ACL ATTACK PATHS THROUGH LDAP RELAYINGATTACKS
May 20, 2021
* Enterprise IT in Security Insights CIS CONTROLS VERSION 8 OVERVIEW: BYE-BYE “TOP 20”May 20, 2021
* Cloud in Tools & Techniques GOOGLE CLOUD IAM: DESIGNS FOR SELF-SERVICE PRIVILEGE ESCALATIONMay 04, 2021
READY TO DISCUSS YOUR NEXT SECURITY INITIATIVE?Contact Us
* Github
* Youtube
* Services
* Corporate Security * Product & Application Security * Critical Infrastructure Security* IoT Security
* Mobile Security
* Network Security
* Penetration Testing* Cloud Security
* Grouping
* Platform
* Chariot
* Industry Security Solutions * Security for the Automotive Industry * Security for the Financial Services Sector * Healthcare Security * Security for the Energy Sector * Manufacturing Security* Company
* Praetorian Labs
* Overview
* Who We Are
* News & Press
* Careers
* Contact
* Resources
* The Praetorian Blog* Whitepapers
* Challenges
� 2021 All Rights Reserved.* Privacy Policy
* Responsible Disclosure Policy WE DON'T SUPPORT INTERNET EXPLORER Please use Chrome, Safari, Firefox, or Edge to view this site.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0