Are you over 18 and want to see adult content?
More Annotations

A complete backup of samedayessays.info
Are you over 18 and want to see adult content?

A complete backup of websitebuilderguide.com
Are you over 18 and want to see adult content?

A complete backup of eldoradoranch.com
Are you over 18 and want to see adult content?

A complete backup of goldenstateimages.com
Are you over 18 and want to see adult content?
A complete backup of emrs-strasbourg.com
Are you over 18 and want to see adult content?
Favourite Annotations

Tailored Mens Suits | Montagio Sydney, Brisbane
Are you over 18 and want to see adult content?

Professional Sports Apparel, Fan Gear, MLB Jerseys, T-Shirts & more!
Are you over 18 and want to see adult content?
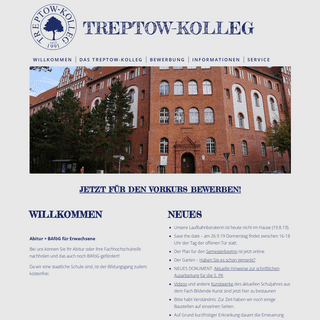
TREPTOW_KOLLEG – ABITUR + BAFÖG FÜR ERWACHSENE
Are you over 18 and want to see adult content?

ОТЕЛЬ MRIYA RESORT & SPA (МРИЯ РЕЗОРТ энд СПА 5*) в Ялте • на берегу моря Крым
Are you over 18 and want to see adult content?

Top Immigration Consultants in Delhi for Canada | Apply for PR Visa
Are you over 18 and want to see adult content?
Text
slide 3 of 2
REVERSINGLABS WINS TRUST AWARD FOR THE BEST THREAT INTELLIGENCE TECHNOLOGY AT SC AWARDS 2021 Read here HOW SOLARWINDS ATTACKERS BREACHED THE SUPPLY CHAIN Read here REVERSINGLABS WINS TRUST AWARD FOR THE BEST THREAT INTELLIGENCE TECHNOLOGY AT SC AWARDS 2021 Read here HOW SOLARWINDS ATTACKERS BREACHED THE SUPPLY CHAIN Read here REVERSINGLABS WINS TRUST AWARD FOR THE BEST THREAT INTELLIGENCE TECHNOLOGY AT SC AWARDS 2021 Read here HOW SOLARWINDS ATTACKERS BREACHED THE SUPPLY CHAIN Read hereSolutions
Manage Digital Risk Software Supply Chain Web & Mobile File UploadsCloud File Shares
Secure
Across SDLC Build & Release Processes Automate SOC Support TriageIncident Response
SIEM/SOAR
Optimize Threat Hunting Malware LabThreat Hunting
Sandbox
EDR
Threat Intelligence PlatformsPlatform & Products
Titanium Platform
Free: Open-Source YARABasic:
Threat Intelligence
Professional: Threat Analysis & Hunting Premium: Elastic Threat Infrastructure Why Choose ReversingLabsPartners
Reseller Partners
Integration PartnersSecurity Partners
Resources
Content Demo VideosLearning with
ReversingLabs
Threat
Intelligence Quiz
Company
Company About Us
Leadership Careers
Events Webinars
Events
RSA 2021
Software Supply
Chain Roadshow
CISO Cyber Talks
Press
Press Releases
In the News
Demo
Search Contact Us SupportLogin
Blog
EXPLAINABLE THREAT INTELLIGENCE ANY FILE. ANY LOCATION. ANY THREAT.slide 3 of 9
Securely Enable Web & Mobile App File Uploads Protect Against New High Risk Business Exposures Accelerate Alert Volume Triage Prioritize Patching with Targeted CVE Correlation Automate Manual Threat Research in 5 milliseconds Cut Incident Response Remediation Cost by 25% Automate Continuous Threat Hunting 24x7 Automate Threat Auditing & Compliance Upskill Junior Analysts with Every Event Securely Enable Web & Mobile App File Uploads Protect Against New High Risk Business ExposuresRequest a Demo
see how we protect
when others miss
Benefits Products & Technology Solutions Customers Insights GAIN EXPLAINABLE INTELLIGENCE INTO MALWARE INFECTED FILES AND OBJECTSWITH...
SPEED & ACTION
to analyze
Speed detection of objects through automated static and dynamic analysis, prioritizing the highest risks with actionable detail, inonly milliseconds.
BREADTH & PRIVACY
files and 4,000 unique formats Accurately detect threats leveraging the largest repository of malware in the industry, while maintaining the privacy you require. TRANSPARENCY & TRUST explain classification Trust in intelligence derived from machine learning classification based entirely on human readable indicators. THEN APPLY THOSE EXPLAINABLE INSIGHTS HEREslide 5 to 6 of 4
INCIDENT RESPONSE
THREAT INTELLIGENCE
INCIDENT RESPONSE
TRIAGE
INCIDENT RESPONSE
THREAT INTELLIGENCE
INCIDENT RESPONSE
TRIAGE
INCIDENT RESPONSE
THREAT INTELLIGENCE
slide 4 of 2
DISCOVER THE TITANIUM PLATFORM THAT AUTOMATES MALWARE INSIGHTS ACROSS THE ENTERPRISE A hybrid cloud platform that processes complex files of any size or type, delivering intelligence that mitigates software supply chain risks, secures the SDLC, automates SOC decision support and enriches the threat hunter malware labFREE:
OPEN-SOURCE YARA
Investigation & HuntingBASIC:
THREAT INTELLIGENCE
TitaniumCloud
PROFESSIONAL:
THREAT ANALYSIS & HUNTINGA1000
PREMIUM:
ELASTIC THREAT INFRASTRUCTURETitaniumScale
Get the Solution Brief I WANT INSIGHTS THAT... PROTECT MY FILE SHARESLearn more
SECURE SOFTWARE RELEASESLearn more
VERIFY SOFTWARE SUPPLY CHAINLearn more
HUNT THREATS CONTINUOUSLYLearn more
PREVENT PHISHING AND ZERO-DAY EMAIL ATTACKSLearn more
EXPAND MY SIEM AND SOAR VISIBILITYLearn more
FUEL MY THREAT INTELLIGENCE PLATFORMLearn more
OPTIMIZE MY SANDBOX PERFORMANCELearn more
READ USER REVIEWS FROM THE TECH COMMUNITYslide 5 to 6 of 3
CISO - Information Security WE USE THE PRODUCT FOR DATA ENRICHMENT OR DOWNLOADING MALICIOUS PROGRAMS THAT WE ARE OTHERWISE UNABLE TO FIND helps to automate SOC operations when it comes to identifying the highest priority threats. We're leveraging the APIs, so the whole process with respect to looking up information and retrieving information about threats is fully...Read More
Information Security Engineer GIVES US A MORE IN-DEPTH ANALYSIS AND BETTER REPORTING ON A LARGER NUMBER OF FILE TYPES We are also using FireEye and Palo Alto. As far as I can tell, the quantity of files that ReversingLabs can process in a day is greater than many of these products. Also, the stability of this product seemsto be much higher.
Read More
Forensic Lead, Global Security VERY GOOD MALWARE AND GOODWARE REPOSITORY AND ENABLES US TO LOOK MORE DEEPLY AT INDICATORS OF COMPROMISE It's absolutely saving us time. We're not even using the full capabilities, but it has reduced our meantime to remediation by about 25 percent....There are about 35 of us using it, including level-ones, level-threes, and forensics.Read More
CISO - Information Security WE USE THE PRODUCT FOR DATA ENRICHMENT OR DOWNLOADING MALICIOUS PROGRAMS THAT WE ARE OTHERWISE UNABLE TO FIND helps to automate SOC operations when it comes to identifying the highest priority threats. We're leveraging the APIs, so the whole process with respect to looking up information and retrieving information about threats is fully...Read More
Information Security Engineer GIVES US A MORE IN-DEPTH ANALYSIS AND BETTER REPORTING ON A LARGER NUMBER OF FILE TYPES We are also using FireEye and Palo Alto. As far as I can tell, the quantity of files that ReversingLabs can process in a day is greater than many of these products. Also, the stability of this product seemsto be much higher.
Read More
Forensic Lead, Global Security VERY GOOD MALWARE AND GOODWARE REPOSITORY AND ENABLES US TO LOOK MORE DEEPLY AT INDICATORS OF COMPROMISE It's absolutely saving us time. We're not even using the full capabilities, but it has reduced our meantime to remediation by about 25 percent....There are about 35 of us using it, including level-ones, level-threes, and forensics.Read More
CISO - Information Security WE USE THE PRODUCT FOR DATA ENRICHMENT OR DOWNLOADING MALICIOUS PROGRAMS THAT WE ARE OTHERWISE UNABLE TO FIND helps to automate SOC operations when it comes to identifying the highest priority threats. We're leveraging the APIs, so the whole process with respect to looking up information and retrieving information about threats is fully...Read More
Information Security Engineer GIVES US A MORE IN-DEPTH ANALYSIS AND BETTER REPORTING ON A LARGER NUMBER OF FILE TYPES We are also using FireEye and Palo Alto. As far as I can tell, the quantity of files that ReversingLabs can process in a day is greater than many of these products. Also, the stability of this product seemsto be much higher.
Read More
Forensic Lead, Global Security VERY GOOD MALWARE AND GOODWARE REPOSITORY AND ENABLES US TO LOOK MORE DEEPLY AT INDICATORS OF COMPROMISE It's absolutely saving us time. We're not even using the full capabilities, but it has reduced our meantime to remediation by about 25 percent....There are about 35 of us using it, including level-ones, level-threes, and forensics.Read More
CISO - Information Security WE USE THE PRODUCT FOR DATA ENRICHMENT OR DOWNLOADING MALICIOUS PROGRAMS THAT WE ARE OTHERWISE UNABLE TO FIND helps to automate SOC operations when it comes to identifying the highest priority threats. We're leveraging the APIs, so the whole process with respect to looking up information and retrieving information about threats is fully...Read More
Information Security Engineer GIVES US A MORE IN-DEPTH ANALYSIS AND BETTER REPORTING ON A LARGER NUMBER OF FILE TYPES We are also using FireEye and Palo Alto. As far as I can tell, the quantity of files that ReversingLabs can process in a day is greater than many of these products. Also, the stability of this product seemsto be much higher.
Read More
slide 9 to 13 of 29
EXPLAINABLE THREAT INTELLIGENCE How Combining Automated Static and Dynamic Analysis with Continuous Machine Learning Delivers the Intelligence Humans Need to Make Better Threat Decisions at SpeedDownload Whitepaper
GET INSIGHTS FROM OUR INDUSTRY PROFESSIONALS SunBurst: the next level of stealthRead More
Advancing the Cybersecurity Industry with the SOREL-20M InitiativeRead More
Rana Android MalwareRead More
MORE SUGGESTED RESOURCES * Videos and Podcasts * ReversingLabs History * ReversingLabs Titanium Platform Overview * What is Explainable Machine Learning? * How to Analyze a Phishing Email * Ebooks and Whitepapers * The Destructive Objects Playbook * Explainable Threat Intelligence * How to Build an Effective Threat Hunting Program * How to Mitigate Software Supply Chain Risk* Webinars
* Lessons Learned from the SolarWinds SunBurst Attack * Top 5 Best Practices to Elevate Your Threat Hunting Program * Understanding Attacks Like Ryuk Before It's Too Late * How to Think Like a Reverse Engineer * Applying YARA to Uncover Hidden Phishing Threats Months After theAttack
Explainable Threat Intelligence. Any file. Any location. Any threat.*
* About Us
* Careers
*
* Contact Us
* Events
*
* In the News
* Press Releases
*
*
*
* YouTube
* RSS
All rights reserved ReversingLabs © 2021 | Privacy Policy| Cookies
✖This website uses cookies to ensure the best website experience. By continuing to use this website you are giving your consent to cookies being used. Detailed information about our use of cookies is here.cookie script
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0