Are you over 18 and want to see adult content?
More Annotations
Claire-Marie Le Guay, pianiste | Site officiel
Are you over 18 and want to see adult content?

The Financially Free Life | Helping you with all things personal finance
Are you over 18 and want to see adult content?
A complete backup of sweetcolor.tmall.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://lull.com
Are you over 18 and want to see adult content?
A complete backup of https://businessfast.co.uk
Are you over 18 and want to see adult content?
A complete backup of https://usna.com
Are you over 18 and want to see adult content?
A complete backup of https://quikshiptoner.com
Are you over 18 and want to see adult content?

A complete backup of https://cafegitanenyc.com
Are you over 18 and want to see adult content?
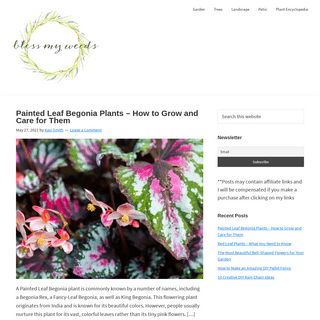
A complete backup of https://blessmyweeds.com
Are you over 18 and want to see adult content?
A complete backup of https://outbreaknewstoday.com
Are you over 18 and want to see adult content?

A complete backup of https://xtrememind.com
Are you over 18 and want to see adult content?
A complete backup of https://sculpture-network.org
Are you over 18 and want to see adult content?

A complete backup of https://vapesoldes.fr
Are you over 18 and want to see adult content?
A complete backup of https://thesimplycraftedlife.com
Are you over 18 and want to see adult content?
Text
Vulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
LA RÉSILIENCE PAR LA COMMUNAUTÉ : PERSPECTIVES POUR …TRANSLATETHIS PAGE
La résilience par la communauté : Perspectives pour 2021. Année de la résilience, 2020 a également été une année pour la communauté. En tant qu’organisation, YesWeHack a démontré une fois de plus sa remarquable agilité. En tant que communauté, YesWeHack a continué à grandir et � HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE" GLOSSAIRE DES TERMES DE LA CYBERSÉCURITÉ A zero-day (also known as 0-day) is a computer-software vulnerability unknown to those who should be interested in its mitigation (including the vendor of the target software). Until the vulnerability is mitigated, malicious hackers can exploit it to adversely affect programs, data, additional computers or a network. YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
LA RÉSILIENCE PAR LA COMMUNAUTÉ : PERSPECTIVES POUR …TRANSLATETHIS PAGE
La résilience par la communauté : Perspectives pour 2021. Année de la résilience, 2020 a également été une année pour la communauté. En tant qu’organisation, YesWeHack a démontré une fois de plus sa remarquable agilité. En tant que communauté, YesWeHack a continué à grandir et � HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE" GLOSSAIRE DES TERMES DE LA CYBERSÉCURITÉ A zero-day (also known as 0-day) is a computer-software vulnerability unknown to those who should be interested in its mitigation (including the vendor of the target software). Until the vulnerability is mitigated, malicious hackers can exploit it to adversely affect programs, data, additional computers or a network.CHOOSE YESWEHACK
Global community of ethical hackers. Maximize breadth of skills and testing capabilities. Compliance with highest security standards. Guarantee your operations security and your data confidentiality. Agile Bug Bounty platform to run your programs. Enable tests scalability and budget control. Personalized support and automationtools.
LAUNCH YOUR BUG BOUNTY WITH YESWEHACK, BUG BOUNTY PLATFORM YesWeHack dashboards provide KPIs to manage your programs efficiently. Since its launch in 2013, YesWeHack have been running hundreds of Bug Bounty & VDP programs of all sizes in the most various contexts. YesWeHack secures organizations of all sizes and industries in more than 25 countries. Our team leverages this unique expertise to guideyou
PWNMACHINEV2: A NEW VERSION OF THE SELF HOSTED PWNING Every bug hunter know how it can be hard to have a ready-to-go environment for Bug Bounty in one click with the perfect setup to have all the rights tools. Last year, we have released a first version of a tool called PwnMachine. This version was functional but not as easily to install and to use as we expected initially. YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
YESWEHACK JOBS
YesWeHack offers jobs related to design-patterns. Security Architect M/F (apprenticeship) Missions principales et responsabilités permanentes FDJ, vous connaissez ? YESWEHACK - OFFRES D'EMPLOI CYBER SÉCURITÉTRANSLATE THIS PAGE YesWeHack est la référence pour trouver un emploi dans la cybersécurité ou s'ouvrir à de nouvelles opportunités de carrière en sécurité informatique. Cherchez un poste ou recrutez et embauchez les meilleurs experts en cybersécurité. A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICY Ethical hackers can make significant contributions to increasing products’ digital security. Still, the situation where a vulnerability is identified by an individual outside the organisation remains uneasy to handle for many organisations. FILE UPLOAD ATTACKS (PART 1) In the first part of the file upload attack series, we will look at an attack surface that one gets when there’s a file upload functionality and we will focus on some ofAPI DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/reports/reports_id_export_format.yml Failed to fetch . Stack trace YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
LA RÉSILIENCE PAR LA COMMUNAUTÉ : PERSPECTIVES POUR …TRANSLATETHIS PAGE
La résilience par la communauté : Perspectives pour 2021. Année de la résilience, 2020 a également été une année pour la communauté. En tant qu’organisation, YesWeHack a démontré une fois de plus sa remarquable agilité. En tant que communauté, YesWeHack a continué à grandir et � HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE" GLOSSAIRE DES TERMES DE LA CYBERSÉCURITÉ A zero-day (also known as 0-day) is a computer-software vulnerability unknown to those who should be interested in its mitigation (including the vendor of the target software). Until the vulnerability is mitigated, malicious hackers can exploit it to adversely affect programs, data, additional computers or a network. YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
LA RÉSILIENCE PAR LA COMMUNAUTÉ : PERSPECTIVES POUR …TRANSLATETHIS PAGE
La résilience par la communauté : Perspectives pour 2021. Année de la résilience, 2020 a également été une année pour la communauté. En tant qu’organisation, YesWeHack a démontré une fois de plus sa remarquable agilité. En tant que communauté, YesWeHack a continué à grandir et � HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE" GLOSSAIRE DES TERMES DE LA CYBERSÉCURITÉ A zero-day (also known as 0-day) is a computer-software vulnerability unknown to those who should be interested in its mitigation (including the vendor of the target software). Until the vulnerability is mitigated, malicious hackers can exploit it to adversely affect programs, data, additional computers or a network.CHOOSE YESWEHACK
Global community of ethical hackers. Maximize breadth of skills and testing capabilities. Compliance with highest security standards. Guarantee your operations security and your data confidentiality. Agile Bug Bounty platform to run your programs. Enable tests scalability and budget control. Personalized support and automationtools.
LAUNCH YOUR BUG BOUNTY WITH YESWEHACK, BUG BOUNTY PLATFORM YesWeHack dashboards provide KPIs to manage your programs efficiently. Since its launch in 2013, YesWeHack have been running hundreds of Bug Bounty & VDP programs of all sizes in the most various contexts. YesWeHack secures organizations of all sizes and industries in more than 25 countries. Our team leverages this unique expertise to guideyou
PWNMACHINEV2: A NEW VERSION OF THE SELF HOSTED PWNING Every bug hunter know how it can be hard to have a ready-to-go environment for Bug Bounty in one click with the perfect setup to have all the rights tools. Last year, we have released a first version of a tool called PwnMachine. This version was functional but not as easily to install and to use as we expected initially. YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. YESWEHACKEDU, UNE NOUVELLE APPROCHE PÉDAGOGIQUETRANSLATE THIS PAGE YesWeHackEDU, une nouvelle approche pédagogique. Le Bug Bounty. Un nouveau standard de cybersécurité. Le Bug Bounty mobilise une communauté de hackers éthiques pour éprouver la sécurité du système d’information. Ces experts sont récompensés selon la gravité de la vulnérabilité découverte et de la qualité de sonanalyse.
YESWEHACK JOBS
YesWeHack offers jobs related to design-patterns. Security Architect M/F (apprenticeship) Missions principales et responsabilités permanentes FDJ, vous connaissez ? YESWEHACK - OFFRES D'EMPLOI CYBER SÉCURITÉTRANSLATE THIS PAGE YesWeHack est la référence pour trouver un emploi dans la cybersécurité ou s'ouvrir à de nouvelles opportunités de carrière en sécurité informatique. Cherchez un poste ou recrutez et embauchez les meilleurs experts en cybersécurité. A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICY Ethical hackers can make significant contributions to increasing products’ digital security. Still, the situation where a vulnerability is identified by an individual outside the organisation remains uneasy to handle for many organisations. FILE UPLOAD ATTACKS (PART 1) In the first part of the file upload attack series, we will look at an attack surface that one gets when there’s a file upload functionality and we will focus on some ofAPI DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/reports/reports_id_export_format.yml Failed to fetch . Stack trace YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE"API DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/business_units_response_templates/business_units_slug_response_templates.ymlFailed
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
A QUICK UPDATE ON OUR RANKING POINT SYSTEM. A quick update on our ranking point system. We have recently been questioned on how our ranking point system works and how report quality is evaluated. Our system has evolved quite a lot since inception, and some new report quality rating features have beenadded.
A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
SOLUTION FOR "A WEIRD XSS CASE"API DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/business_units_response_templates/business_units_slug_response_templates.ymlFailed
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
A QUICK UPDATE ON OUR RANKING POINT SYSTEM. A quick update on our ranking point system. We have recently been questioned on how our ranking point system works and how report quality is evaluated. Our system has evolved quite a lot since inception, and some new report quality rating features have beenadded.
A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICYSEE MORE ONBLOG.YESWEHACK.COM
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Bug Bounty secures applications the agile way with a global community of white hackers through private and public programs. Create an effective vulnerability disclosure strategy for security researchers. LAUNCH YOUR BUG BOUNTY WITH YESWEHACK, BUG BOUNTY PLATFORM YesWeHack dashboards provide KPIs to manage your programs efficiently. Since its launch in 2013, YesWeHack have been running hundreds of Bug Bounty & VDP programs of all sizes in the most various contexts. YesWeHack secures organizations of all sizes and industries in more than 25 countries. Our team leverages this unique expertise to guideyou
BUG BOUNTY PROGRAMS (PRIVATE & PUBLIC) YesWeHack also helps you predefine hunters’ rewards grids. “When we started our first private Bug Bounty program, we relied on YesWeHack to pick up the hunters best suited to our needs.”. 01. 02. Submit your scope to our entire community of hunters and maximize Bug Bounty effectiveness. YOU LOOK FOR A JOB IN CYBERSECURITY? YESWEHACK RECRUIT! A GAME CHANGER IN CYBER SECURITY. YesWeHack harnesses the power of its global community to make security agile, drive digital transformation and build digital trust. ALREADY #1 IN EUROPE. Created in 2013, YesWeHack has become one of the world's leading Bug Bounty platform, with offices in France, Switzerland, Germany and Singapore.YESWEHACK JOBS
YesWeHack offers jobs related to design-patterns. Security Architect M/F (apprenticeship) Missions principales et responsabilités permanentes FDJ, vous connaissez ? VULNERABILITY COORDINATION THROUGH CROWDSOURCED SECURITY Swiss Post launches public Bug Bounty program with YesWeHack. Following a year in private Bug Bounty program, Swiss Post, one of the oldest and most well-known brands in Switzerland, opens its Public Bug Bounty program on YesWehack. HOW WE HELP OUR CLIENTS STEP-BY-STEP IN THEIR BUG BOUNTY The Customer Success team is there to reassure and guide them, to ensure their bug bounty program will succeed and fulfil their goals and expectations. Also, we make sure that our Bug Bounty programs are of high quality to satisfy our hackers too. Of course, our relationship with customers is AUTOREPEATER: ADD AUTOMATION TO YOUR BEAUTIFUL HUNTER LIFE We follow our PimpMyBurp series with a new article about an extension known by many hunters but still (too) rarely used, AutoRepeater. If you use Burp Suite for your hunting session, you probably already know the “match & replace” feature.This one is useful, but with the AutoRepeater add-on, you can extend the possibility of automation to focus more on research and exploits.API DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/business_units_response_templates/business_units_slug_response_templates.ymlFailed
YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
EVENTS - YES WE HACK Events - Yes We Hack SOLUTION FOR "A WEIRD XSS CASE" HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICYSEE MORE ONBLOG.YESWEHACK.COM
API DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/business_units_response_templates/business_units_slug_response_templates.ymlFailed
YESWEHACK - GLOBAL BUG BOUNTY PLATFORM & VDP PLATFORMLAUNCH A PROGRAMINFOSEC JOBSPRESS AREA & CONTACTQ&ALEGAL NOTICESEDU YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’ interests. Leverage our global community of cybersecurity researchers. Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities. Choose the experts. in charge of your. YESWEHACKEDU, A NEW EDUCATIONAL APPROACH A novel. educational approach. Provide a secure, fun and operational framework for cybersecurity training. Enrich the content of cybersecurity curricula through real-life situations. Enhance cybersecurity skills and abilities of students through gamification. Involve students in securing their institution through a CoordinatedVulnerability
YESWEHACK #1 BUG BOUNTY PLATFORM IN EUROPE Olvid - End-to-end encrypted messaging. C. Secure messaging without a central directory of users: Olvid offers the best security, anonymity, and integrity, without collecting any personal data. 3 Scopes. ︎ Bounty. Bounty Range €50 - €2,000. Submit report. Bitsmedia PteLtd.
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
HOW TO EXPLOIT GRAPHQL ENDPOINT: INTROSPECTION, QUERYSEE MORE ONBLOG.YESWEHACK.COM
EVENTS - YES WE HACK Events - Yes We Hack SOLUTION FOR "A WEIRD XSS CASE" HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
A FRAMEWORK FOR SUCCESSFUL VULNERABILITY DISCLOSURE POLICYSEE MORE ONBLOG.YESWEHACK.COM
API DOCUMENTATION
Something went wrong Error downloading https://apps.yeswehack.com/doc/paths/business_units_response_templates/business_units_slug_response_templates.ymlFailed
CHOOSE YESWEHACK
Global community of ethical hackers. Maximize breadth of skills and testing capabilities. Compliance with highest security standards. Guarantee your operations security and your data confidentiality. Agile Bug Bounty platform to run your programs. Enable tests scalability and budget control. Personalized support and automationtools.
BE PART OF ONE OF THE MOST TRUSTED BUG BOUNTY PLATFORMS Check the ranking. 1. 3. What we offer. The best bug bounty programs. Founded in 2013, YesWeHack pioneered Bug Bounty in Europe and established the first research community in Europe, securing organizations of all industries and sizes – from startups to government departments. The most trusted community of white hathackers.
BUG BOUNTY PROGRAMS (PRIVATE & PUBLIC) YesWeHack also helps you predefine hunters’ rewards grids. “When we started our first private Bug Bounty program, we relied on YesWeHack to pick up the hunters best suited to our needs.”. 01. 02. Submit your scope to our entire community of hunters and maximize Bug Bounty effectiveness. WHY BUG BOUNTY? YESWEHACK GLOBAL BUG BOUNTY PLATFORM Secure your exposed scopes the agile way with our global community of ethical hackers. Bug Bounty, the new standard for cybersecurity. Leverage our global community of white hat hackers: forget penetration testing and access a virtually unlimited pool of experts to maximize your testing capabilities. Choose the experts in charge of your YOU ARE A COMPANY? CONTACT OUR YESWEHACK'S TEAM YesWeHack is a Bug Bounty platform with private or public bug bounty programs. Be assisted by our Customer Success Team. +400 programslaunched!
LEGAL NOTICES
Publisher’s company name: YES WE HACK. Legal form: Société par actions simplifiée (simplified joint-stock company) RCS (business registration) number: 814YESWEHACK JOBS
YesWeHack offers jobs. CYBERSECURITY ARCHITECT (H/F) Au sein des projets Systèmes Sols, vous intervenez, en tant que consultant et architecte sécurité, tout VULNERABILITY COORDINATION THROUGH CROWDSOURCED SECURITY Swiss Post launches public Bug Bounty program with YesWeHack. Following a year in private Bug Bounty program, Swiss Post, one of the oldest and most well-known brands in Switzerland, opens its Public Bug Bounty program on YesWehack. HOW TO TEST HORIZONTAL AND VERTICAL PRIVILEGES ESCALATION A few weeks ago, we talked about PwnFox and the Burp Suite extensions Autorize to test IDOR vulnerabilities. In the follow-up of this article, today we’d like to introduce you to the Auth Analyzer plugin. This plugin enables the creation of multiple sessions simultaneously to help you test horizontal and vertical privilegeescalation.
HACKERS MUSEUM PART 5: YO DAWG, WORLD WIDE WEB! In this issue of our HACKERS MUSEUM series, we'll review the creation of the World Wide Web. What you're reading is a web page, and publishing it worldwide would have regarded like pure magic some 30years ago.
* Our programs
* CHANGELOG
* Press
* Career
* YesWeHack EDU
* Other sites
* Follow us:
*
*
*
* fr
* en
* Choose YesWeHack
* Companies
* Hunters
CONTACT
REGISTER
LOGIN
* BUG BOUNTY
* Why Bug Bounty?
* Types of programs
* Launch a program
* Q&A
* VDP
* How VDP works?
* Set up your VDP
*
Public programs
*
News & Events
* HUNTERS
* Public programs
* Join us
* Hacktivity
* Ranking
*
We're hiring!
*
blog
*
Register
Register
* Choose YesWeHack
* Companies
* Hunters
* CONTACT
Try Yeswehack
Become a hunter
*
*
*
fr en
* Our programs
* CHANGELOG
* Press
* Career
* YesWeHack EDU
* Other sites
Companies
* BUG BOUNTY
* Why Bug Bounty?
* Types of programs
* Launch a program
* Q&A
* VDP
* How VDP works?
* Set up your VDP
*
Our public programs
*
News & Events
Hunters
* Public programs
* Join us
* Hacktivity
* Ranking
*
We're hiring!
*
blog
*
GLOBAL BUG BOUNTY
PLATFORM
CROWDSOURCED SECURITY & VULNERABILITY DISCLOSURE FRANCE, SINGAPORE, SWITZERLAND, GERMANYPAY A REWARD
NOT A RANSOM
Global Bug Bounty & VDP Platform UNLEASH THE POWER OF OUR HUNTERS Global Bug Bounty & VDP PlatformHOW IT WORKS
Scroll
1
0
Last hacktivities
0xjal
/
Information Disclosure (CWE-200)new
WHY ELEVATE
YOUR SECURITY
WITH YESWEHACK?
CHOOSE YESWEHACK
Cyber threats are increasing – together with your needs for agility. As a result, traditional approaches and tools no longer meet the challenges of digital transformation. YESWEHACK AND ITS GLOBAL COMMUNITY OF EXPERTS PROVIDE YOU WITH A DISRUPTIVE SOLUTION: BUGBOUNTY.
YesWeHack’s Bug Bounty platform complies with the strictest European standards and regulations to protect its customers and hunters’interests.
LEVERAGE OUR GLOBAL COMMUNITY OF CYBERSECURITY RESEARCHERS Access a virtually unlimited pool of ethical hackers to maximize your testing capabilities.CHOOSE THE EXPERTS
IN CHARGE OF YOUR
CYBERSECURITY
Submit your scopes to be tested to the hunters YOU select - or to ourentire community.
ENTRUST YOUR PROGRAMS TO AN ACTOR RESPECTFUL OF YOUR DATACONFIDENTIALITY
Our Bug Bounty platform complies with the strictest standards and regulations in order to safeguard your interests - as well as ourhunters.
LAUNCH A PROGRAM
YOUR FIRST RESULTS
SINCE YOUR PROGRAM
LAUNCH
Leverage our hunters responsiveness to minimize time to vulnerabilities detection and remediation.START
“Bug Bounty allows us to have permanent feedbacks throughout the year, on various scopes, and to detect bugs very quickly.” Read the full interview Romain Lods, Head of Engineering, Deezer “In a perfect world we should systematically test each update on our website. Bug Bounty makes such continuous verification possible.” Read the full interview Eric Vautier, Group CISO, Groupe ADP “In addition to facilitating report management and rewarding researchers, the YesWeHack Bug Bounty platform unites a community of highly proficient researchers. This last point being the strongest asset for long-term security efficiency.” Sophie Claude, Security Director - Network and IT Division at OrangeFrance
“Hunters find things that no one else could and take the time to enhance/ highlight/ exploit them–-I have access to a wealth ofexpertise.
Read the full interview Edouard Camoin, CISO, Outscale “YesWeHack gives us easy access to experts in various technologies; It’s just impossible to find a team of pentesters with advanced skills in all of these technologies.” Read the full interview Julien Levrard, Security Operations Manager, OVHcloud “Bug Bounty implies an obligation of result (you pay only for what you get), while penetration testing only implies an obligation ofmeans.”
Read the full interview Alain Tiemblo, Security Leader, BlablacarSee all programs
1
6
Latest News
25/05/2021
DOJO CHALLENGE #10 Winners!See more
21/05/2021
How a world-renowned luxury brand implemented a crowdsourced securitystrategy
See more
19/05/2021
PimpMyBurp #4: Burp Suite extensions that should get your attention!See more
Visit our Blog
Next Events
09/06/2021
IT-Security Virtual Conference - ISX QII/21 09/06/2021 - 9:30 am - 3:30 pm08/06/2021
Paris Cyber Week 2021 08/06/2021 - 09/06/2021 - All Day01/06/2021
YesWeHack au Virtual FIC 2021 01/06/2021 - 04/06/2021 - 4:30 pm - 11:30 amMeet YESWEHACK
on those security eventsAll our events
Start Now
LAUNCH A BUG BOUNTY
START HACKING
Choose YESWEHACK
* Companies
* Why Bug Bounty?
* Types of programs
* Launch a Bug Bounty program* How VDP works?
* Set up your VDP
* Hunters
* Join our community* Our programs
* Hacktivity
* Ranking
* OTHER SITES
* Blog
* FireBounty.com
* ZeroDisclo.com
* Infosec Jobs
* Press
* Career
* Contact
* Newsletter
* Glossary
* Follow us:
*
*
* Legal notices
* Privacy Policy
* Cookies policy
�2021 YESWEHACK
Close
OTHER SITES
Close
BLOG
View our latests news, upcoming events and other posts.INFOSEC JOBS
Leading online job board dedicated to cybersecurity. Global aggregator of public Bug Bounty programs. Non-profit platform for Coordinated Vulnerability Disclosure (CVD) toCERTs.
Close
Cookies management panelPrivacy Policy
Preference for all services Allow all Refuse all*
Mandatory cookies
*
This site uses cookies necessary for its proper functioning which cannot be deactivated.Allow Deny
*
APIs
APIs are used to load scripts: geolocation, search engines,translations, ...
*
Advertising network
Ad networks can generate revenue by selling advertising space on thesite.
*
Audience measurement The audience measurement services used to generate useful statistics attendance to improve the site.*
Google Tag Manager This service can install 22 cookies.Allow Deny
*
Comments
Comments managers facilitate the filing of comments and fight againstspam.
*
Other
Services to display web content.*
Gartner PeerInsight This service can install 9 cookies.Allow Deny
*
Site Usage Tracking
User site usage tracking.*
HubSpot This service can install 5 cookies.Allow Deny
*
Social networks
Social networks can improve the usability of the site and help to promote it via the shares.*
Support
Support services allow you to get in touch with the site team andhelp to improve it.
*
Videos
Video sharing services help to add rich media on the site and increase its visibility. * This website does not use any cookie requiring your consent. This website stores cookies on your computer. These cookies are used to improve your website experience and provide more personalized services and offers to you, both on this website and through other media. To find out more about the cookies we and our partners use, see our Cookies Policy - Manage cookiesAccept all
Refuse all
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0