Are you over 18 and want to see adult content?
More Annotations

Universal Radio shortwave, amateur, scanner and CB radio since 1942
Are you over 18 and want to see adult content?
Rede de Administradores
Are you over 18 and want to see adult content?
Crafting a Green World • The home for green crafts and tutorials!
Are you over 18 and want to see adult content?
Danmarks Billigste Sokker | FRA KUN 4.99,- | CoolSokker.dk
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of barrettssmokehouse.com
Are you over 18 and want to see adult content?

A complete backup of thefinelinemag.com
Are you over 18 and want to see adult content?

A complete backup of gardenhealth.com
Are you over 18 and want to see adult content?
A complete backup of coasttocoastimports.com
Are you over 18 and want to see adult content?

A complete backup of edmarfs.blogspot.com
Are you over 18 and want to see adult content?
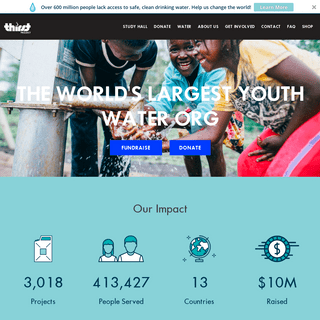
A complete backup of thirstproject.org
Are you over 18 and want to see adult content?
A complete backup of livejaverianaedu-my.sharepoint.com
Are you over 18 and want to see adult content?
Text
a
KEYLENGTH - COMPARE ALL METHODS Keylength - Compare all Methods. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - BSI CRYPTOGRAPHIC KEY LENGTH REPORT (2020) Keylength - BSI Cryptographic Key Length Report (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM NSA COMMERCIAL Keylength - Cryptographic Key Length from NSA Commercial National Security Algorithm (2016) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - LENSTRA CRYPTOGRAPHIC KEY LENGTH EQUATIONS (2004) Keylength - Lenstra Cryptographic Key Length Equations (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM RFC3766 / RFC Keylength - Cryptographic Key Length from RFC3766 / RFC 3766 / BCP86 / BCP 86 (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - ANSSI CRYPTOGRAPHIC KEY LENGTH REPORT (2014) Keylength - ANSSI Cryptographic Key Length Report (2014) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - ECRYPT-CSA REPORT ON KEY SIZES (2018) The goal of ECRYPT-CSA (Coordination & Support Action) is to strengthen European excellence in the area of cryptology. This report on cryptographic algorithms, schemes, keysizes and protocols is a direct descendent of the reports produced by the ECRYPT I and II projects (2004-2012), and the ENISA reports (2013-2014). It provides rather conservative guiding principles, based on current state-of KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH RECOMMENDATIONLENSTRA AND VERHEUL EQUATIONS (2000)LENSTRA UPDATED EQUATIONS (2004) Keylength - Cryptographic Key Length Recommendation. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - NIST REPORT ON CRYPTOGRAPHIC KEY LENGTH AND Keylength - NIST Report on Cryptographic Key Length and Cryptoperiod (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to KEYLENGTH - LENSTRA AND VERHEUL CRYPTOGRAPHIC KEY LENGTH The lengths provided here are designed to resist mathematic attacks; they do not take algorithmic attacks, hardware flaws, etc. into account. In 1999, Prof. Arjen K. Lenstra and Prof. Eric R. Verheul described mathematical formulas providing key length recommendations for most cryptographic systems . This is the first publication witha
KEYLENGTH - COMPARE ALL METHODS Keylength - Compare all Methods. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - BSI CRYPTOGRAPHIC KEY LENGTH REPORT (2020) Keylength - BSI Cryptographic Key Length Report (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM NSA COMMERCIAL Keylength - Cryptographic Key Length from NSA Commercial National Security Algorithm (2016) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - LENSTRA CRYPTOGRAPHIC KEY LENGTH EQUATIONS (2004) Keylength - Lenstra Cryptographic Key Length Equations (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM RFC3766 / RFC Keylength - Cryptographic Key Length from RFC3766 / RFC 3766 / BCP86 / BCP 86 (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - ANSSI CRYPTOGRAPHIC KEY LENGTH REPORT (2014) Keylength - ANSSI Cryptographic Key Length Report (2014) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - ECRYPT-CSA REPORT ON KEY SIZES (2018) The goal of ECRYPT-CSA (Coordination & Support Action) is to strengthen European excellence in the area of cryptology. This report on cryptographic algorithms, schemes, keysizes and protocols is a direct descendent of the reports produced by the ECRYPT I and II projects (2004-2012), and the ENISA reports (2013-2014). It provides rather conservative guiding principles, based on current state-of KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH RECOMMENDATION In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - RECOMMANDATION SUR LA LONGUEUR DES …TRANSLATE THIS PAGE Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer la taille minimale sécuritaire des clefs cryptographiques. KEYLENGTH - COMPARER LES MÉTHODESTRANSLATE THIS PAGE Ce site internet vous permet d’évaluer une longueur de clef appropriée garantissant un niveau de sécurité minimal en implémentant les formules mathématiques et en résumant les informations disponibles dans toutes ces publications. Vous pouvez également comparer ces méthodes facilement. Les longueurs fournies ici sont conçues pour KEYLENGTH - ÉQUATIONS DE LENSTRA ET VERHEUL SUR LA …TRANSLATE THISPAGE
En 1999, Pr. Arjen K. Lenstra and Pr. Eric R. Verheul ont décrit des formules mathématiques permettant d’estimer la taille minimale sécuritaire des clefs cryptographiques .Il s’agit de la première publication ayant une approche mathématique basée sur des paramètres concrets. KEYLENGTH - TAILLE DES CLEFS CRYPTOGRAPHIQUES …TRANSLATE THIS PAGE Calculez facilement la longueur des clefs cryptographiques provenant du RFC 3766, Determining Strengths for Public Keys Used for Exchanging Symmetric Keys, H. Orman and P. Hoffman. KEYLENGTH - RAPPORT DU NIST SUR LA TAILLE DES CLEFSTRANSLATE THIS PAGE Keylength - Rapport du NIST sur la taille des clefs cryptographiques et leurs cryptopériodes (2020) Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniquesmathématiques
KEYLENGTH - RAPPORT DU BSI SUR LA TAILLE DES CLEFSTRANSLATE THIS PAGE Keylength - Rapport du BSI sur la taille des clefs cryptographiques (2020) Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer lataille
KEYLENGTH - ÉQUATIONS DE LENSTRA SUR LA TAILLE DES …TRANSLATE THISPAGE
En 2004, Pr. Arjen K. Lenstra a décrit des formules mathématiques permettant d’estimer la taille minimale sécuritaire des clefs cryptographiques . Il s’agit d’une mise à jour par rapport � la première version . Cette méthode est plus facile à manipuler,car elle réduit
KEYLENGTH - TAILLE DES CLEFS CRYPTOGRAPHIQUES …TRANSLATE THIS PAGE Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer la taille minimale sécuritaire des clefs cryptographiques. KEYLENGTH - RAPPORT DE L'ANSSI SUR LA TAILLE DES CLEFSTRANSLATE THISPAGE
Keylength - Rapport de l'ANSSI sur la taille des clefs cryptographiques (2014) Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer la taille KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH RECOMMENDATIONLENSTRA AND VERHEUL EQUATIONS (2000)LENSTRA UPDATED EQUATIONS (2004) Keylength - Cryptographic Key Length Recommendation. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - NIST REPORT ON CRYPTOGRAPHIC KEY LENGTH AND Keylength - NIST Report on Cryptographic Key Length and Cryptoperiod (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to KEYLENGTH - LENSTRA AND VERHEUL CRYPTOGRAPHIC KEY LENGTH The lengths provided here are designed to resist mathematic attacks; they do not take algorithmic attacks, hardware flaws, etc. into account. In 1999, Prof. Arjen K. Lenstra and Prof. Eric R. Verheul described mathematical formulas providing key length recommendations for most cryptographic systems . This is the first publication witha
KEYLENGTH - COMPARE ALL METHODS Keylength - Compare all Methods. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - BSI CRYPTOGRAPHIC KEY LENGTH REPORT (2020) Keylength - BSI Cryptographic Key Length Report (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM NSA COMMERCIAL Keylength - Cryptographic Key Length from NSA Commercial National Security Algorithm (2016) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - LENSTRA CRYPTOGRAPHIC KEY LENGTH EQUATIONS (2004) Keylength - Lenstra Cryptographic Key Length Equations (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM RFC3766 / RFC Keylength - Cryptographic Key Length from RFC3766 / RFC 3766 / BCP86 / BCP 86 (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - ANSSI CRYPTOGRAPHIC KEY LENGTH REPORT (2014) Keylength - ANSSI Cryptographic Key Length Report (2014) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - ECRYPT-CSA REPORT ON KEY SIZES (2018) The goal of ECRYPT-CSA (Coordination & Support Action) is to strengthen European excellence in the area of cryptology. This report on cryptographic algorithms, schemes, keysizes and protocols is a direct descendent of the reports produced by the ECRYPT I and II projects (2004-2012), and the ENISA reports (2013-2014). It provides rather conservative guiding principles, based on current state-of KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH RECOMMENDATIONLENSTRA AND VERHEUL EQUATIONS (2000)LENSTRA UPDATED EQUATIONS (2004) Keylength - Cryptographic Key Length Recommendation. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - NIST REPORT ON CRYPTOGRAPHIC KEY LENGTH AND Keylength - NIST Report on Cryptographic Key Length and Cryptoperiod (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to KEYLENGTH - LENSTRA AND VERHEUL CRYPTOGRAPHIC KEY LENGTH The lengths provided here are designed to resist mathematic attacks; they do not take algorithmic attacks, hardware flaws, etc. into account. In 1999, Prof. Arjen K. Lenstra and Prof. Eric R. Verheul described mathematical formulas providing key length recommendations for most cryptographic systems . This is the first publication witha
KEYLENGTH - COMPARE ALL METHODS Keylength - Compare all Methods. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - BSI CRYPTOGRAPHIC KEY LENGTH REPORT (2020) Keylength - BSI Cryptographic Key Length Report (2020) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM NSA COMMERCIAL Keylength - Cryptographic Key Length from NSA Commercial National Security Algorithm (2016) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - LENSTRA CRYPTOGRAPHIC KEY LENGTH EQUATIONS (2004) Keylength - Lenstra Cryptographic Key Length Equations (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM RFC3766 / RFC Keylength - Cryptographic Key Length from RFC3766 / RFC 3766 / BCP86 / BCP 86 (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - ANSSI CRYPTOGRAPHIC KEY LENGTH REPORT (2014) Keylength - ANSSI Cryptographic Key Length Report (2014) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - ECRYPT-CSA REPORT ON KEY SIZES (2018) The goal of ECRYPT-CSA (Coordination & Support Action) is to strengthen European excellence in the area of cryptology. This report on cryptographic algorithms, schemes, keysizes and protocols is a direct descendent of the reports produced by the ECRYPT I and II projects (2004-2012), and the ENISA reports (2013-2014). It provides rather conservative guiding principles, based on current state-of KEYLENGTH - LENSTRA AND VERHEUL CRYPTOGRAPHIC KEY LENGTH The lengths provided here are designed to resist mathematic attacks; they do not take algorithmic attacks, hardware flaws, etc. into account. In 1999, Prof. Arjen K. Lenstra and Prof. Eric R. Verheul described mathematical formulas providing key length recommendations for most cryptographic systems . This is the first publication witha
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH RECOMMENDATION In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - LENSTRA CRYPTOGRAPHIC KEY LENGTH EQUATIONS (2004) Keylength - Lenstra Cryptographic Key Length Equations (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimumkey
KEYLENGTH - CRYPTOGRAPHIC KEY LENGTH FROM RFC3766 / RFC Keylength - Cryptographic Key Length from RFC3766 / RFC 3766 / BCP86 / BCP 86 (2004) In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. KEYLENGTH - ÉQUATIONS DE LENSTRA ET VERHEUL SUR LA …TRANSLATE THISPAGE
En 1999, Pr. Arjen K. Lenstra and Pr. Eric R. Verheul ont décrit des formules mathématiques permettant d’estimer la taille minimale sécuritaire des clefs cryptographiques .Il s’agit de la première publication ayant une approche mathématique basée sur des paramètres concrets. KEYLENGTH - COMPARER LES MÉTHODESTRANSLATE THIS PAGE Ce site internet vous permet d’évaluer une longueur de clef appropriée garantissant un niveau de sécurité minimal en implémentant les formules mathématiques et en résumant les informations disponibles dans toutes ces publications. Vous pouvez également comparer ces méthodes facilement. Les longueurs fournies ici sont conçues pour KEYLENGTH - TAILLE DES CLEFS CRYPTOGRAPHIQUES …TRANSLATE THIS PAGE Calculez facilement la longueur des clefs cryptographiques provenant du RFC 3766, Determining Strengths for Public Keys Used for Exchanging Symmetric Keys, H. Orman and P. Hoffman. KEYLENGTH - RAPPORT DU BSI SUR LA TAILLE DES CLEFSTRANSLATE THIS PAGE Keylength - Rapport du BSI sur la taille des clefs cryptographiques (2020) Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer lataille
KEYLENGTH - ÉQUATIONS DE LENSTRA SUR LA TAILLE DES …TRANSLATE THISPAGE
En 2004, Pr. Arjen K. Lenstra a décrit des formules mathématiques permettant d’estimer la taille minimale sécuritaire des clefs cryptographiques . Il s’agit d’une mise à jour par rapport � la première version . Cette méthode est plus facile à manipuler,car elle réduit
KEYLENGTH - TAILLE DES CLEFS CRYPTOGRAPHIQUES …TRANSLATE THIS PAGE Dans la plupart des fonctions cryptographiques, la longueur des clefs est un paramètre sécuritaire important. Un certain nombre de publications académiques et gouvernementales fournissent des recommandations et des techniques mathématiques pour estimer la taille minimale sécuritaire des clefs cryptographiques. In most cryptographic functions, the key length is an important security parameter. Both academic and private organizations provide recommendations and mathematical formulas to approximate the minimum key size requirement for security. Despite the availability of these publications, choosing an appropriate key size to protect your system from attacks remains a headache as you need to read and understand allthese papers.
This web site implements mathematical formulas and summarizes reports from well-known organizations allowing you to quickly evaluate the minimum security requirements for your system. You can also easily compare all these techniques and find the appropriate key length for your desired level of protection. The lengths provided here are designed to resist mathematic attacks; they do not take algorithmic attacks, hardware flaws, etc. into account. PLEASE ENABLE JAVASCRIPT TO FULLY UTILIZE THIS WEBSITE (PRIVACYPOLICY)
Choose a Method
Lenstra and Verheul Equations (2000) Lenstra and Verheul Equations (2000) Lenstra Updated Equations (2004) Lenstra Updated Equations (2004) ECRYPT-CSA Recommendations (2018) ECRYPT-CSA Recommendations (2018) NIST Recommendations (2019) NIST Recommendations (2019) ANSSI Recommendations (2014) ANSSI Recommendations (2014) NSA CNSA Suite (2016) NSA CNSASuite (2016)
Network Working Group RFC3766 (2004) Network Working Group RFC3766 (2004) BSI Recommendations (2020) BSI Recommendations (2020)Compare all Methods
Compare all Methods
� 2020
BlueKrypt - v 32.2 - April 8, 2020Author: Damien Giry
Approved by Prof. Jean-Jacques Quisquater Contact: keylength@bluekrypt.com _You need Javascript enabled to viewthis email address_
I would like to thank Prof. Arjen K. Lenstra for his kind authorization and comments. Surveys of laws and regulations on cryptology: Crypto Law Survey / Digital Signature Law Survey.
Privacy Policy | Disclaimer / Copyright | Release NotesDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0