Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.bodyandsoul.com.au/health/health-news/you-can-now-say-goodbye-to-stress-and-anxiety-watching-ikea-worke
Are you over 18 and want to see adult content?

A complete backup of sports.ltn.com.tw/news/breakingnews/3079406
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of thefreeenterpriseinstitute.org
Are you over 18 and want to see adult content?
A complete backup of nikerosherunwomen.co.uk
Are you over 18 and want to see adult content?

A complete backup of intersectionssouthla.org
Are you over 18 and want to see adult content?
A complete backup of clinicalgate.com
Are you over 18 and want to see adult content?

A complete backup of webhostinggeeks.com
Are you over 18 and want to see adult content?
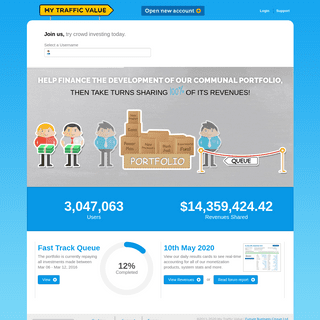
A complete backup of mytrafficvalue.com
Are you over 18 and want to see adult content?
Text
KREBS ON SECURITY
The U.S. Department of Justice said today it has recovered $2.3 million worth of Bitcoin that Colonial Pipeline paid to ransomware extortionists last month. The funds had been sent to DarkSide, aCVE-2021-33742
Microsoft Patches Six Zero-Day Security Holes. June 8, 2021. 0 Comments. Microsoft today released another round of security updatesfor Windows
MICROSOFT PATCHES SIX ZERO-DAY SECURITY HOLES Harry Johnston June 8, 2021. One correction: Adobe’s patch for CVE-2021-28550 (security bulletin APSB21-29, which you link to) was released last month, not today. TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 201 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by FINTECH STARTUP OFFERS $500 FOR PAYROLL PASSWORDS This ad, from workplaceunitedcom, promised up to $500 for people who provided their payroll passwords, plus $25 a month for each month those credentials kept working. HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from hisKREBS ON SECURITY
The U.S. Department of Justice said today it has recovered $2.3 million worth of Bitcoin that Colonial Pipeline paid to ransomware extortionists last month. The funds had been sent to DarkSide, aCVE-2021-33742
Microsoft Patches Six Zero-Day Security Holes. June 8, 2021. 0 Comments. Microsoft today released another round of security updatesfor Windows
MICROSOFT PATCHES SIX ZERO-DAY SECURITY HOLES Harry Johnston June 8, 2021. One correction: Adobe’s patch for CVE-2021-28550 (security bulletin APSB21-29, which you link to) was released last month, not today. TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 201 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by FINTECH STARTUP OFFERS $500 FOR PAYROLL PASSWORDS This ad, from workplaceunitedcom, promised up to $500 for people who provided their payroll passwords, plus $25 a month for each month those credentials kept working. HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from his TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by A BASIC TIMELINE OF THE EXCHANGE MASS-HACK 89 thoughts on “ A Basic Timeline of the Exchange Mass-Hack ” OndraH March 8, 2021. Brian, thanks for the timeline. I can also confirm the scan activity on Feb 26 based on our analysis of CAN WE STOP PRETENDING SMS IS SECURE NOW 58 thoughts on “ Can We Stop Pretending SMS Is Secure Now? Luiggi March 16, 2021. The US is the only country relying completely on SMS.They
KREBS ON SECURITY
The recently-announced credit card breach at P.F. Chang’s Chinese Bistro appears to have gone on for at least nine months: New information indicates that the breach at the nationwide restaurantKREBS ON SECURITY
Digital gift card retailer Gyft has forced a password reset for some of its users.The move comes in response to the theft of usernames and passwords from a subset of Gyft customers. Mountain View RANSOMWARE VICTIMS THAT PAY UP COULD INCUR STEEP FINES Companies victimized by ransomware and firms that facilitate negotiations with ransomware extortionists could face steep fines fromthe U.S.
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking orKREBS ON SECURITY
In-depth security news and investigation. Several MEDantex portal pages left exposed to the Web suggest that the company recently was the victim of WhiteRose, a strain of ransomware that encrypts THREE TOP RUSSIAN CYBERCRIME FORUMS HACKED Over the past few weeks, three of the longest running and most venerated Russian-language online forums serving thousands of experienced cybercriminalsKREBS ON SECURITY
The update comes roughly seven weeks after researcher Craig Heffner discovered and blogged about a feature or bug built into at least eight different models of D-Link routers that could allow anKREBS ON SECURITY
It’s probably worth mentioning that the FSB is the same agency that’s been sanctioned for malicious cyber activity by the U.S. government on multiple occasions over the past five years. TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles of pipe, stranding DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 201 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by FINTECH STARTUP OFFERS $500 FOR PAYROLL PASSWORDS This ad, from workplaceunitedcom, promised up to $500 for people who provided their payroll passwords, plus $25 a month for each month those credentials kept working. AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
THREE TOP RUSSIAN CYBERCRIME FORUMS HACKED Over the past few weeks, three of the longest running and most venerated Russian-language online forums serving thousands of experienced cybercriminals HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from hisKREBS ON SECURITY
It’s probably worth mentioning that the FSB is the same agency that’s been sanctioned for malicious cyber activity by the U.S. government on multiple occasions over the past five years. TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles of pipe, stranding DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 201 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by FINTECH STARTUP OFFERS $500 FOR PAYROLL PASSWORDS This ad, from workplaceunitedcom, promised up to $500 for people who provided their payroll passwords, plus $25 a month for each month those credentials kept working. AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
THREE TOP RUSSIAN CYBERCRIME FORUMS HACKED Over the past few weeks, three of the longest running and most venerated Russian-language online forums serving thousands of experienced cybercriminals HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from hisCVE-2021-31201
1 day ago · Microsoft today released another round of security updates for Windows operating systems and supported software, including fixes for six zero-day TASK FORCE SEEKS TO DISRUPT RANSOMWARE PAYMENTS Task Force Seeks to Disrupt Ransomware Payments. Some of the world’s top tech firms are backing a new industry task force focused on disrupting cybercriminal ransomware gangs by AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking or A BASIC TIMELINE OF THE EXCHANGE MASS-HACK 89 thoughts on “ A Basic Timeline of the Exchange Mass-Hack ” OndraH March 8, 2021. Brian, thanks for the timeline. I can also confirm the scan activity on Feb 26 based on our analysis ofKREBS ON SECURITY
When Karim Rattani isn’t manning the till at the local Subway franchise in his adopted hometown of Cartersville, Ga., he’s usually tinkering with code. The 21-year-old Pakistani native is theKREBS ON SECURITY
In-depth security news and investigation. Jam and jelly maker Smucker’s last week shuttered its online store, notifying visitors that the site was being retooled because of a security breachKREBS ON SECURITY
In February 2017, authorities in the United Kingdom arrested a 29-year-old U.K. man on suspicion of knocking more than 900,000 Germans offline in an attack tied to Mirai, a malware strain thatKREBS ON SECURITY
Digital gift card retailer Gyft has forced a password reset for some of its users.The move comes in response to the theft of usernames and passwords from a subset of Gyft customers. Mountain ViewKREBS ON SECURITY
In-depth security news and investigation. Several MEDantex portal pages left exposed to the Web suggest that the company recently was the victim of WhiteRose, a strain of ransomware that encryptsKREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phony TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 201 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 MICROSOFT PATCH TUESDAY, MAY 2021 EDITION Microsoft Patch Tuesday, May 2021 Edition. May 11, 2021. 35 Comments. Microsoft today released fixes to plug at least 55 security holes inits Windows
AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking orWIPRO DATA BREACH
The criminals responsible for launching phishing campaigns that netted dozens of employees and more than 100 computer systems last month atKREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phony TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking or COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 202 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 MICROSOFT PATCH TUESDAY, MAY 2021 EDITION Microsoft Patch Tuesday, May 2021 Edition. May 11, 2021. 35 Comments. Microsoft today released fixes to plug at least 55 security holes inits Windows
CVE-2021-26411
March 9, 2021. 37 Comments. On the off chance you were looking for more security to-dos from Microsoft todaythe company released software MICROSOFT PATCH TUESDAY JUNE 2021 1 day ago · Microsoft today released another round of security updates for Windows operating systems and supported software, including fixes for six zero-day RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for FINTECH GIANT FISERV USED UNCLAIMED DOMAIN 77 thoughts on “ Fintech Giant Fiserv Used Unclaimed Domain ” Joy Peterson March 17, 2021 “Fiserv February” seems to be an annual event. That is the month Fiserv caused a SOLARWINDS: WHAT HIT US COULD HIT OTHERS 36 thoughts on “ SolarWinds: What Hit Us Could Hit Others ” zainul abideen January 12, 2021. Brand reputation compromise have to be dealtwithin
KREBS ON SECURITY
When Karim Rattani isn’t manning the till at the local Subway franchise in his adopted hometown of Cartersville, Ga., he’s usually tinkering with code. The 21-year-old Pakistani native is the CAN WE STOP PRETENDING SMS IS SECURE NOW 58 thoughts on “ Can We Stop Pretending SMS Is Secure Now? Luiggi March 16, 2021. The US is the only country relying completely on SMS.They
NO, I DID NOT HACK YOUR MS EXCHANGE SERVER Quid March 29, 2021. Of course, bulletproof Open Source Linux is the answer! To quote from the article at hand: “..I checked up on it –and found
KREBS ON SECURITY
In-depth security news and investigation. Several MEDantex portal pages left exposed to the Web suggest that the company recently was the victim of WhiteRose, a strain of ransomware that encryptsKREBS ON SECURITY
In-depth security news and investigation. Jam and jelly maker Smucker’s last week shuttered its online store, notifying visitors that the site was being retooled because of a security breachKREBS ON SECURITY
In-depth security news and investigation. In case any of you loyal readers missed it, KrebsOnSecurity.com and its author were featured in a 60 Minutes interview lastKREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phony TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking or COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 202 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 MICROSOFT PATCH TUESDAY, MAY 2021 EDITION Microsoft Patch Tuesday, May 2021 Edition. May 11, 2021. 35 Comments. Microsoft today released fixes to plug at least 55 security holes inits Windows
CVE-2021-26411
March 9, 2021. 37 Comments. On the off chance you were looking for more security to-dos from Microsoft todaythe company released softwareKREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phony TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a AT LEAST 30,000 U.S. ORGANIZATIONS NEWLY HACKED VIA HOLES At least 30,000 organizations across the United States -- including a significant number of small businesses, towns, cities and localgovernments --
PARKMOBILE BREACH EXPOSES LICENSE PLATE DATA, MOBILE 51 thoughts on “ ParkMobile Breach Exposes License Plate Data, Mobile Numbers of 21M Users ” Lindy April 12, 2021. I don’t use any of these kinds of apps. Nor do I do online banking or COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 202 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to A CLOSER LOOK AT THE DARKSIDE RANSOMWARE GANG Here’s a closer look at the DarkSide cybercrime gang, as seen through their negotiations with a recent U.S. victim that earns $15 billion in annual revenue. Colonial Pipeline has shut down 5,500 MICROSOFT PATCH TUESDAY, MAY 2021 EDITION Microsoft Patch Tuesday, May 2021 Edition. May 11, 2021. 35 Comments. Microsoft today released fixes to plug at least 55 security holes inits Windows
CVE-2021-26411
March 9, 2021. 37 Comments. On the off chance you were looking for more security to-dos from Microsoft todaythe company released software MICROSOFT PATCH TUESDAY JUNE 2021 11 hours ago · Microsoft today released another round of security updates for Windows operating systems and supported software, including fixes for six zero YANDEX – KREBS ON SECURITY 1 day ago · KrebsOnSecurity recently had occasion to contact the Russian Federal Security Service (FSB), the Russian equivalent of the U.S. Federal Bureau of Investigation (FBI). In the process of doingso, I
RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known forTOM ROBINSON
1 day ago · The U.S. Department of Justice said today it has recovered $2.3 million worth of Bitcoin that Colonial Pipeline paid to ransomware extortionists last month. The funds had been sent toDarkSide, a
SOLARWINDS: WHAT HIT US COULD HIT OTHERS 36 thoughts on “ SolarWinds: What Hit Us Could Hit Others ” zainul abideen January 12, 2021. Brand reputation compromise have to be dealtwithin
CAN WE STOP PRETENDING SMS IS SECURE NOW 58 thoughts on “ Can We Stop Pretending SMS Is Secure Now? Luiggi March 16, 2021. The US is the only country relying completely on SMS.They
FINTECH GIANT FISERV USED UNCLAIMED DOMAIN 77 thoughts on “ Fintech Giant Fiserv Used Unclaimed Domain ” Joy Peterson March 17, 2021 “Fiserv February” seems to be an annual event. That is the month Fiserv caused a NO, I DID NOT HACK YOUR MS EXCHANGE SERVER Quid March 29, 2021. Of course, bulletproof Open Source Linux is the answer! To quote from the article at hand: “..I checked up on it –and found
KREBS ON SECURITY
In-depth security news and investigation. Several MEDantex portal pages left exposed to the Web suggest that the company recently was the victim of WhiteRose, a strain of ransomware that encryptsKREBS ON SECURITY
The recently-announced credit card breach at P.F. Chang’s Chinese Bistro appears to have gone on for at least nine months: New information indicates that the breach at the nationwide restaurantKREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phonyABOUT THE AUTHOR
About the Author. Brian Krebs worked as a reporter for The Washington Post from 1995 to 2009, authoring more than 1,300 blog posts for the Security Fix blog, as well as hundreds of stories for TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for BLUELEAKS – KREBS ON SECURITY The collection, dubbed “ BlueLeaks ” and made searchable online, stems from a security breach at a Texas web design and hosting companythat maintains a
WIPRO DATA BREACH
The criminals responsible for launching phishing campaigns that netted dozens of employees and more than 100 computer systems last month at HOW THE PWNEDLIST GOT PWNED How the Pwnedlist Got Pwned. May 2, 2016. 49 Comments. Last week, I learned about a vulnerability that exposed all 866 million account credentials harvested by pwnedlist.com, a HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from his BUYERS BEWARE OF TAMPERED GIFT CARDS Prepaid gift cards make popular presents and no-brainer stocking stuffers, but before you purchase one be on the lookout for signs that someone may have tampered with it.KREBS ON SECURITY
In-depth security news and investigation. Like an ever-expanding venn diagram, a review of the extensions commented on by each new fake reviewer found led to the discovery of even more phonyABOUT THE AUTHOR
About the Author. Brian Krebs worked as a reporter for The Washington Post from 1995 to 2009, authoring more than 1,300 blog posts for the Security Fix blog, as well as hundreds of stories for TRY THIS ONE WEIRD TRICK RUSSIAN HACKERS HATE The Twitter thread came up in a discussion on the ransomware attack against Colonial Pipeline, which earlier this month shut down 5,500 miles of fuel pipe for nearly a COLONIAL PIPELINE RANSOMWARE ATTACK May 11, 2021. 122 Comments. The FBI confirmed this week that a relatively new ransomware group known as DarkSide is responsible for an attack that caused Colonial Pipeline to shut down 5,550 miles RANSOMWARE – KREBS ON SECURITY October 28, 2020. 80 Comments. On Monday, Oct. 27, KrebsOnSecurity began following up on a tip from a reliable source that an aggressive Russian cybercriminal gang known for BLUELEAKS – KREBS ON SECURITY The collection, dubbed “ BlueLeaks ” and made searchable online, stems from a security breach at a Texas web design and hosting companythat maintains a
WIPRO DATA BREACH
The criminals responsible for launching phishing campaigns that netted dozens of employees and more than 100 computer systems last month at HOW THE PWNEDLIST GOT PWNED How the Pwnedlist Got Pwned. May 2, 2016. 49 Comments. Last week, I learned about a vulnerability that exposed all 866 million account credentials harvested by pwnedlist.com, a HOW TO FIGHT MOBILE NUMBER PORT-OUT SCAMS 60 thoughts on “ How to Fight Mobile Number Port-out Scams ” Number 1 February 28, 2018. Sir Elton John has reportedly received two ceramic urns from his BUYERS BEWARE OF TAMPERED GIFT CARDS Prepaid gift cards make popular presents and no-brainer stocking stuffers, but before you purchase one be on the lookout for signs that someone may have tampered with it. CRYPTOPRO – KREBS ON SECURITY 17 hours ago · KrebsOnSecurity recently had occasion to contact the Russian Federal Security Service (FSB), the Russian equivalent of the U.S. Federal Bureau of Investigation (FBI). In the process of doingso, I
DARKSIDE RANSOMWARE GANG QUITS AFTER SERVERS, BITCOIN 202 thoughts on “ DarkSide Ransomware Gang Quits After Servers, Bitcoin Stash Seized ” BitcoinMoney May 16, 2021. Well I see what it was* It was organised Mission to MICROSOFT BUYS CORP.COM SO BAD GUYS CAN’T Microsoft Buys Corp.com So Bad Guys Can’t. In February, KrebsOnSecurity told the story of a private citizen auctioning off the dangerous domain corp.com for the starting price of $1.7 millionTOM ROBINSON
9 hours ago · The U.S. Department of Justice said today it has recovered $2.3 million worth of Bitcoin that Colonial Pipeline paid to ransomware extortionistsKREBS ON SECURITY
The New York Times this week published a fascinating story about a young programmer in Ukraine who’d turned himself in to the local police.The Times says the man did so after one of his softwareKREBS ON SECURITY
A recent phishing campaign targeting customers of several major U.S. banks was powered by text messages directing recipients to call hacked phone lines at Holiday Inn locations in the south. Such BROWSER EXTENSIONS: ARE THEY WORTH THE RISK? Popular file-sharing site Mega.nz is warning users that cybercriminals hacked its browser extension for Google Chrome so that any usernamesand
KREBS ON SECURITY
An industrial maintenance and construction firm in Tennessee that was hit by a $327,000 cyberheist is suing its financial institution to recover the stolen funds, charging the bank with negligenceKREBS ON SECURITY
Microsoft on Tuesday released software updates to fix at least 62 security vulnerabilities in Windows, Office and other software. Two of those flaws were detailed publicly before yesterday’sKREBS ON SECURITY
A bug in the software that powers a broad array of Webcams, IP surveillance cameras and baby monitors made by Chinese camera giant Foscam allows anyone with access to the device’s InternetAdvertisement
Subscribe to RSS
Follow me on Twitter Join me on FacebookKREBS ON SECURITY
IN-DEPTH SECURITY NEWS AND INVESTIGATION* About the Author
* Advertising/Speaking -------------------------Breadcrumbs /
Ne'er-Do-Well News
— 11
comments
10
Mar 20
FBI ARRESTS ALLEGED OWNER OF DEER.IO, A TOP BROKER OF STOLEN ACCOUNTS FBI officials last week arrested a Russian computer security researcher on suspicion of operating DEER.IO, a vast marketplace for buying and selling stolen account credentials for thousands of popular online services and stores. KIRILL V. FIRSOV was arrested Mar. 7 after arriving at New York’s John F. Kennedy Airport, according to court documents unsealed Monday. Prosecutors with the U.S. DISTRICT COURT FOR THE SOUTHERN DISTRICT OF CALIFORNIA allege Firsov was the administrator of deer.io, an online platform that hosted more than 24,000 shops for selling stolen and/or hacked usernames and passwords for a variety of top onlinedestinations.
An example seller’s panel at deer.io. Click image to enlarge. The indictment against Firsov says deer.io was responsible for $17 million worth of stolen credential sales since its inception in 2013. “The FBI’s review of approximately 250 DEER.IO storefronts reveals thousands of compromised accounts posted for sale via this platform and its customers’ storefronts, including videogame accounts (gamer accounts) and PII files containing user names, passwords, U.S. Social Security Numbers, dates of birth, and victim addresses,” theindictment states.
In addition to facilitating the sale of hacked accounts at video streaming services like NETFLIX and HULU and social media platforms like FACEBOOK, TWITTER and VKONTAKTE (the Russian equivalent of Facebook), deer.io also is a favored marketplace for people involved in selling phony social media accounts. For example, one early adopter of deer.io was a now-defunct shop called “Dedushka” (“grandpa” in transliterated Russian), a service offering aged, fake Vkontakte accounts that was quite popular among crooks involved in various online dating scams. The indictment doesn’t specify how prosecutors pegged Firsov as the mastermind behind deer.io, but there are certainly plenty of clues that suggest such a connection. _Continue reading →_ Other — 11 comments07
Mar 20
U.S. GOVT. MAKES IT HARDER TO GET .GOV DOMAINS The federal agency in charge of issuing .gov domain names is enacting new requirements for validating the identity of people requesting them. The additional measures come less than four months after KrebsOnSecurity published research suggesting it was relatively easy for just about anyone to get their very own .gov domain. In November’s piece It’s Way Too Easy to Get a .gov Domain Name,
an anonymous source detailed how he obtained one by impersonating an official at a small town in Rhode Island that didn’t already haveits own .gov.
“I had to ‘an official authorization form,’ which basically just lists your admin, tech guy, and billing guy,” the source said. “Also, it needs to be printed on ‘official letterhead,’ which of course can be easily forged just by Googling a document from said municipality. Then you either mail or fax it in. After that, they send account creation links to all the contacts.” While what my source did was technically wire fraud (obtaining something of value via the Internet through false pretenses), cybercriminals bent on using fake .gov domains to hoodwink Americans likely would not be deterred by such concerns. “I never said it was legal, just that it was easy,” the source told KrebsOnSecurity. “I assumed there would be at least ID verification. The deepest research I needed to do was Yellow Pagesrecords.”
Now, Uncle Sam says in a few days all new .gov domain applications will include an additional authorization step. “Effective on March 10, 2020, the DotGov Program will begin requiring notarized signatures on all authorization letters when submitting a request for a new .gov domain,” reads a notice published March 5 by the U.S. GENERAL SERVICES ADMINISTRATION, which oversees the .gov space. “This is a necessary security enhancement to prevent mail and wire fraud through signature forgery in obtaining a .gov domain,” the statement continues. “This step will help maintain the integrity of .gov and ensure that .gov domains continue to be issued only to official U.S. government organizations.” _Continue reading →_Breadcrumbs —
69 comments
03
Mar 20
THE CASE FOR LIMITING YOUR BROWSER EXTENSIONS Last week, KrebsOnSecurity reported to health insurance provider BLUE SHIELD OF CALIFORNIA that its Web site was flagged by multiple security products as serving malicious content. Blue Shield quickly removed the unauthorized code. An investigation determined it was injected by a browser extension installed on the computer of a Blue Shield employee who’d edited the Web site in the past month. The incident is a reminder that browser extensions — however useful or fun they may seem when you install them — typically have a great deal of power and can effectively read and/or write all data in your browsing sessions. And as we’ll see, it’s not uncommon for extension makers to sell or lease their user base to shady advertising firms, or in some cases abandon them to outright cybercriminals. The health insurance site was compromised after an employee at the company edited content on the site while using a Web browser equipped with a once-benign but now-compromised extension which quietly injected code into the page. The extension in question was Page Ruler,
a Chrome addition with some 400,000 downloads. Page Ruler lets users measure the inch/pixel width of images and other objects on a Web page. But the extension was sold by the original developera few years back,
and for some reason it’s still available from the Google Chrome store despite multiple recent reports from people blaming it for spreading malicious code. How did a browser extension lead to a malicious link being added to the health insurance company Web site? This compromised extension tries to determine if the person using it is typing content into specific Web forms, such as a blog post editing system like WORDPRESSor JOOMLA.
In that case, the extension silently adds a request for a javascript link to the end of whatever the user types and saves on the page. When that altered HTML content is saved and published to the Web, the hidden javascript code causes a visitor’s browser to display ads under certain conditions. Who exactly gets paid when those ads are shown or clicked is not clear, but there are a few clues about who’s facilitating this. The malicious link that set off antivirus alarm bells when people tried to visit Blue Shield California downloaded javascript content from a domain called LINKOJAGERORG. The file it attempted to download — 212B3D4039AB5319EC.JS — appears to be named after an affiliate identification number designating a specific account that should get credited for serving advertisements. A simple Internet search shows this same javascript code is present on hundreds of other Web sites,
no doubt inadvertently published by site owners who happened to be editing their sites with this Page Ruler extension installed. If we download a copy of that javascript file and view it in a text editor, we can see the following message toward the end of the file: > ’s development is supported by > advertisements that are added to some of the websites you visit. > During the development of this extension, I’ve put in thousands of > hours adding features, fixing bugs and making things better, not > mentioning the support of all the users who ask for help.>
> Ads support most of the internet we all use and love; without them, > the internet we have today would simply not exist. Similarly, > without revenue, this extension (and the upcoming new ones) would > not be possible.>
> You can disable these ads now or later in the settings page. You can > also minimize the ads appearance by clicking on partial support > button. Both of these options are available by clicking \’x\’ > button in the corner of each ad. In both cases, your choice will > remain in effect unless you reinstall or reset the extension. This appears to be boilerplate text used by one or more affiliate programs that pay developers to add a few lines of code to their extensions. The opt-out feature referenced in the text above doesn’t actually work because it points to a domain that no longer resolves — THISADSFORUS. But that domain is still useful for getting a better idea of what we’re dealing with here. Registration records maintained by DomainToolssay it was
originally registered to someone using the email address FRANKOMEDISON1020@GMAIL.COM. A reverse WHOIS search on that unusual name turns up several other interesting domains, includingICONTENTUS.
icontentus is currently not resolving either, but a cached version of it at Archive.org shows it once belonged to an advertising network called METREXT, which marketed itself as an analytics platform that let extension makers track users in real time. An archived copy of the content once served at icontentus promises “plag’n’play” capability. “Three lines into your product and it’s in live,” iContent enthused. “High revenue per user.” Another domain tied to Frank Medison is CDNPPSUS, which currently redirects to the domain “MONETIZUSCOM.” Like its competitors, Monetizus’ site is full of grammar and spelling errors: “Use Monetizus Solutions to bring an extra value to your toolbars, addons and extensions, without loosing an audience,” the company says in a banner at the top of its site. Be sure not to “loose” out on sketchy moneymaking activities! Contacted by KrebsOnSecurity, Page Ruler’s original developer PETER NEWNHAM confirmed he sold his extension to MonetizUs in 2017. “They didn’t say what they were going to do with it but I assumed they were going to try to monetize it somehow, probably with the scripts their website mentions,” Newnham said. _Continue reading→_
Breadcrumbs —
20 comments
02
Mar 20
FRENCH FIRMS ROCKED BY KASBAH HACKER? A large number of French critical infrastructure firms were hacked as part of an extended malware campaign that appears to have been orchestrated by at least one attacker based in Morocco, KrebsOnSecurity has learned. An individual thought to be involved has earned accolades from the likes of APPLE, DELL, and MICROSOFT for helping to find and fix security vulnerabilities in their products. In 2018, security intelligence firm HYAS discovered a malware network communicating with systems inside of a French national power company. The malware was identified as a version of the remote access trojan (RAT) known as njRAT , which has been used against millions of targets globally with a focus on victims in the Middle East. Further investigation revealed the electricity provider was just one of many French critical infrastructure firms that had systems beaconing home to the malware network’s control center. Other victims included one of France’s largest hospital systems; a French automobile manufacturer; a major French bank; companies that work with or manage networks for French postal and transportation systems; a domestic firm that operates a number of airports in France; a state-owned railway company; and multiple nuclear researchfacilities.
HYAS said it quickly notified the French national computer emergency team and the FBI about its findings, which pointed to a dynamic domainname system (DNS)
provider on which the purveyors of this attack campaign relied for their various malware servers. When it didn’t hear from French authorities after almost a week, HYAS asked the dynamic DNS provider to “sinkhole” the malware
network’s control servers. Sinkholing is a practice by which researchers assume control over a malware network’s domains, redirecting any traffic flowing to those systems to a server the researchers control. While sinkholing doesn’t clean up infected systems, it can prevent the attackers from continuing to harvest data from infected PCs or sending them new commands and malware updates. HYAS found that despite its notifications to the French authorities, some of the apparently infected systems were still attempting to contact the sinkholed control networks up until late 2019. “Due to our remote visibility it is impossible for us to determine if the malware infections have been contained within the organizations,” HYAS wrote in a report summarizing their findings. “It is possible that an infected computer is beaconing, but is unable to egress to the command and control due to outbound firewallrestrictions.”
About the only French critical infrastructure vertical not touched by the Kasbah hackers was the water management sector. HYAS said given the entities compromised — and that only a handful of known compromises occurred outside of France — there’s a strong possibility this was the result of an orchestrated phishing campaign targeting French infrastructure firms. It also concluded the domains associated with this campaign were very likely controlled by a group of adversaries based in Morocco. “What caught our attention was the nature of the victims and the fact that there were no other observed compromises outside of France,” said Sasha Angus, vice president of intelligence for HYAS. “With the exception of water management, when looking at the organizations involved, each fell within one of the verticals in France’s critical infrastructure strategic plan. While we couldn’t rule out financial crime as the actor’s potential motive, it didn’t appear that the actor leveraged any normal financial crimetools.”
‘FATAL’ ERROR
HYAS said the dynamic DNS provider shared information showing that one of the email addresses used to register a key DNS server for the malware network was tied to a domain for a legitimate business basedin Morocco.
According to historic records maintained by Domaintools.com, that email
address — ING.EQUIPEPRO@GMAIL.COM — was used in 2016 to register the Web site TALAININE.COM, a now-defunct business that offered recreational vehicle-based camping excursions just outside of a city in southern Morocco called Guelmim.
Archived copies of talainine.com indicate the business was managed by two individuals, including someone named YASSINE ALGANGAF. A Google search for that name reveals a similarly named individual has been credited by a number of major software companies — including Apple, Dell
and Microsoft
—
with reporting security vulnerabilities in their products. A search on this name at Facebook turned up a page for another now-defunct businesscalled YAMOSOFT.COM
that lists Algangaf as an owner. A cached copy of Yamosoft.com atarchive.org
says it was a Moroccan computer security service that specialized in security audits, computer hacking investigations, penetration testing and source code review. _Continue reading →_The Coming Storm
— 29 comments
28
Feb 20
FCC PROPOSES TO FINE WIRELESS CARRIERS $200M FOR SELLING CUSTOMERLOCATION DATA
The U.S. FEDERAL COMMUNICATIONS COMMISSION (FCC) today proposed fines of more than $200 million against the nation’s four largest wireless carriers for selling access to their customers’ location information without taking adequate precautions to prevent unauthorized access to that data. While the fines would be among the largest the FCC has ever levied, critics say the penalties don’t go far enough to deter wireless carriers from continuing to sell customer location data. The FCC proposed fining T-MOBILE $91 million; AT&T faces more than $57 million in fines; VERIZON is looking at more than $48 million in penalties; and the FCC said SPRINT should pay more than $12 million.An FCC statement
(PDF) said
“the size of the proposed fines for the four wireless carriers differs based on the length of time each carrier apparently continued to sell access to its customer location information without reasonable safeguards and the number of entities to which each carrier continued to sell such access.” The fines are only “proposed” at this point because the carriers still have an opportunity to respond to the commission and contest the figures. _The Wall Street Journal_ first reported earlier this week that the FCC was considering the fines. The commission said it took action in response to a May 2018 story broken by _The New York Times_, which exposed how a company called SECURUS TECHNOLOGIES had been selling location data on customers of virtually any major mobile provider to law enforcement officials. That same month, KrebsOnSecurity broke the news that LOCATIONSMART — a data aggregation firm working with the major wireless carriers — had a free, unsecured demo of its service online that anyone could abuse to find the near-exact location of virtually any mobile phone in North America. _Continue reading →_Latest Warnings
/ Time to
Patch — 22 comments26
Feb 20
ZYXEL 0DAY AFFECTS ITS FIREWALL PRODUCTS, TOO On Monday, networking hardware maker ZYXEL released security updates to plug a critical security hole in its network attached storage (NAS) devices that is being actively exploited by crooks who specialize in deploying ransomware. Today, Zyxel acknowledged the same flaw is present in many of its firewall products. This week’s story on the Zyxel patch was prompted by the discovery that exploit code for attacking the flaw was being sold in the cybercrime underground for $20,000. Alex Holden , the security expert who first spotted the code for sale, said at the time the vulnerability was so “stupid” and easy to exploit that he wouldn’t be surprised to find other Zyxel products were similarly affected. Now it appears Holden’s hunch was dead-on. “We’ve now completed the investigation of all Zyxel products and found that firewall products running specific firmware versions are also vulnerable,” Zyxel wrote in an email to KrebsOnSecurity. “Hotfixes have been released immediately, and the standard firmware patches will be released in March.” The updated security advisory from Zyxel states the exploit works against its UTM, ATP, and VPN firewalls running firmware version _ZLD V4.35 Patch 0_ through _ZLD V4.35 Patch 2_, and that those with firmware versions before _ZLD V4.35 Patch_ 0 are not affected. Zyxel’s new advisory suggests that some affected firewall product won’t be getting hotfixes or patches for this flaw, noting that the affected products listed in the advisory are only those which are “within their warranty support period.” Indeed, while the exploit also works against more than a dozen of Zyxel’s NAS product lines, the company only released updates for NAS products that were newer than 2016. Its advice for those still using those unsupported NAS devices? “Do not leave the product directly exposed to the internet. If possible, connect it to a security router or firewall for additional protection.” Hopefully, your vulnerable, unsupported Zyxel NAS isn’t being protected by a vulnerable, unsupported Zyxel firewall product. > My advice? If you can’t patch it, pitch it. CERT’s advisory on the flaw rate this vulnerability at a “10” — its most severe. My advice? If you can’t patch it, pitch it. The zero-day sales thread first flagged by Holden also hinted at the presence of post-authentication exploits in many Zyxel products, but the company did not address those claims in its securityadvisories.
Recent activity suggests that attackers known for deploying ransomware have been actively working to test the zero-day for use against targets. Holden said the exploit is now being used by a group of bad guys who are seeking to fold the exploit into Emotet , a powerful malware tool typically disseminated via spam that is frequently used to seed a target with malcode which holds the victim’s files for ransom. “To me, a 0day exploit in Zyxel is not as scary as who bought it,” he said. “The Emotet guys have been historically targeting PCs, laptops and servers, but their venture now into IoT devices is verydisturbing.”
Latest Warnings
/ The Coming
Storm / Time to
Patch — 27 comments24
Feb 20
ZYXEL FIXES 0DAY IN NETWORK STORAGE DEVICES PATCH COMES AMID ACTIVE EXPLOITATION BY RANSOMWARE GANGS Networking hardware vendor ZYXEL today released an update to fix a critical flaw in many of its network attached storage (NAS) devices that can be used to remotely commandeer them. The patch comes 12 days after KrebsOnSecurity alerted the company that precise instructions for exploiting the vulnerability were being sold for $20,000 in the cybercrime underground. Based in Taiwan, Zyxel Communications Corp. (a.k.a “ZyXEL”) is a maker of networking devices, including Wi-Fi routers, NAS products and hardware firewalls. The company has roughly 1,500 employees and boasts some 100 million devices deployed worldwide. While in many respects the class of vulnerability addressed in this story is depressingly common among Internet of Things (IoT) devices, the flaw is notable because it has attracted the interest of groups specializing in deploying ransomwareat scale.
KrebsOnSecurity first learned about the flaw on Feb. 12 from ALEX HOLDEN, founder of Milwaukee-based security firm Hold Security . Holden had obtained a copy of the exploit code, which allows an attacker to remotely compromise more than a dozen types of Zyxel NAS products remotely without any helpfrom users.
A snippet from the documentation provided by 500mhz for the Zyxel0day.
Holden said the seller of the exploit code — a ne’er-do-well who goes by the nickname “500MHZ” –is known for being reliable and thorough in his sales of 0day exploits (a.k.a. “zero-days,” these are vulnerabilities in hardware or software products that vendors first learn about when exploit code and/or active exploitation showsup online).
For example, this and previous zero-days for sale by 500mhz came with exhaustive documentation detailing virtually everything about the flaw, including any preconditions needed to exploit it, step-by-step configuration instructions, tips on how to remove traces of exploitation, and example search links that could be used to readily locate thousands of vulnerable devices.
500mhz’s profile on one cybercrime forum states that he is constantly buying, selling and trading various 0day vulnerabilities. “In some cases, it is possible to exchange your 0day with my existing 0day, or sell mine,” his Russian-language profile reads. The profile page of 500mhz, translated from Russian to English viaGoogle Chrome.
PARTIAL PATCH
KrebsOnSecurity first contacted Zyxel on Feb. 12, sharing a copy of the exploit code and description of the vulnerability. When four days elapsed without any response from the vendor to notifications sent via multiple methods, this author shared the same information with vulnerability analysts at the U.S. Department of Homeland Security (DHS) and with the CERT Coordination Center(CERT/CC ), a
partnership between DHS and CARNEGIE MELLON UNIVERSITY. Less than 24 hours after contacting DHS and CERT/CC, KrebsOnSecurity heard back from Zyxel, which thanked KrebsOnSecurity for the alert without acknowledging its failure to respond until they were sent the same information by others. “Thanks for flagging,” Zyxel’s team wrote on Feb. 17. “We’ve just received an alert of the same vulnerabilities from US-CERT over the weekend, and we’re now in the process of investigating. Still, we heartily appreciate you bringing it to our attention.” Earlier today, Zyxel sent a message saying it had published a securityadvisory and patch
for the zero-day exploit in some of its affected products. The vulnerable devices include NAS542, NAS540, NAS520, NAS326, NSA325 v2, NSA325, NSA320S, NSA320, NSA310S, NSA310, NSA221, NSA220+, NSA220, and NSA210. The flaw is designated as CVE-2020-9054.
However, many of these devices are no longer supported by Zyxel and will not be patched. Zyxel’s advice for those users is simply “do not leave the product directly exposed to the internet.” “If possible, connect it to a security router or firewall for additional protection,” the advisory reads. Holden said given the simplicity of the exploit — which allows an attacker to seize remote control over an affected device by injecting just two characters to the username field of the login panel for Zyxel NAS devices — it’s likely other Zyxel products may have relatedvulnerabilities.
“Considering how stupid this exploit is, I’m guessing this is not the only one of its class in their products,” he said. CERT’s advisory on the flaw rates it at a “10” — its most severe. The advisory includes additional mitigation instructions, including a proof-of-concept exploit that has the ability to power down affected Zyxel devices. _Continue reading →_ A Little Sunshine /Data Breaches
— 73 comments
19
Feb 20
HACKERS WERE INSIDE CITRIX FOR FIVE MONTHS Networking software giant CITRIX SYSTEMS says malicious hackers were inside its networks for five months between 2018 and 2019, making off with personal and financial data on company employees, contractors, interns, job candidates and their dependents. The disclosure comes almost a year after Citrix acknowledged that digital intruders had broken in by probing its employee accounts for weak passwords. Citrix provides software used by hundreds of thousands of clients worldwide, including most of the Fortune 100 companies. It is perhaps best known for selling virtual private networking (VPN) software that lets users remotely access networks and computers over an encryptedconnection.
In March 2019, the FEDERAL BUREAU OF INVESTIGATION (FBI) alerted Citrix they had reason to believe cybercriminals had gained access to the company’s internal network. The FBI told Citrix the hackers likely got in using a technique called “password spraying,” a
relatively crude but remarkably effective attack that attempts to access a large number of employee accounts (usernames/email addresses) using just a handful of common passwords.In a statement
released at the time, Citrix said it appeared hackers “may have accessed and downloaded business documents,” and that it was still working to identify what precisely was accessed or stolen. But in a letter sent to affected individuals dated Feb. 10, 2020, Citrix disclosed additional details about the incident. According to the letter, the attackers “had intermittent access” to Citrix’s internal network between Oct. 13, 2018 and Mar. 8, 2019, and that there was no evidence that the cybercrooks still remain in the company’s systems. Citrix said the information taken by the intruders may have included Social Security Numbers or other tax identification numbers, driver’s license numbers, passport numbers, financial account numbers, payment card numbers, and/or limited health claims information, such as health insurance participant identification number and/or claims information relating to date of service andprovider name.
It is unclear how many people received this letter, but the communication suggests Citrix is contacting a broad range of individuals who work or worked for the company at some point, as well as those who applied for jobs or internships there and people who may have received health or other benefits from the company by virtue of having a family member employed by the company. _Continue reading →_ A Little Sunshine /The Coming Storm
— 56 comments
18
Feb 20
ENCODING STOLEN CREDIT CARD DATA ON BARCODES Crooks are constantly dreaming up new ways to use and conceal stolen credit card data. According to the U.S. SECRET SERVICE, the latest scheme involves stolen card information embedded in barcodes affixed to phony money network rewards cards. The scammers then pay for merchandise by instructing a cashier to scan the barcode and enter the expiration date and card security code. This phony reloadable rewards card conceals stolen credit card data written to a barcode. The barcode and other card data printed on the card have been obfuscated. Image: U.S. Secret Service. Earlier this month, the Secret Service documented a recent fraud incident in Texas involving a counterfeit club membership card containing a barcode, and a card expiration date and CVV printed belowthe barcode.
“Located underneath the barcode are instructions to the cashier on the steps necessary to complete the transaction,” reads an alert the Secret Service sent to law enforcement agencies. “They instruct the cashier to select card payment, scan the barcode, then enter the expiration date and CVV. In this instance, the barcode was encoded with a VISA credit card number.” _Continue reading →_ A Little Sunshine /The Coming Storm /
Web Fraud 2.0
— 52 comments
17
Feb 20
PAY UP, OR WE’LL MAKE GOOGLE BAN YOUR ADS A new email-based extortion scheme apparently is making the rounds, targeting Web site owners serving banner ads through Google’s ADSENSE program. In this scam, the fraudsters demand bitcoin in exchange for a promise not to flood the publisher’s ads with so much bot and junk traffic that Google’s automated anti-fraud systems suspend the user’s AdSense account for suspicious traffic. A redacted extortion email targeting users of Google’s AdSenseprogram.
Earlier this month, KrebsOnSecurity heard from a reader who maintains several sites that receive a fair amount of traffic. The message this reader shared began by quoting from an automated email Google’s systems might send if they detect your site is seeking to benefit from automated clicks. The message continues: > “Very soon the warning notice from above will appear at the > dashboard of your AdSense account undoubtedly! This will happen due > to the fact that we’re about to flood your site with huge amount > of direct bot generated web traffic with 100% bounce ratio and > thousands of IP’s in rotation — a nightmare for every AdSense > publisher. More also we’ll adjust our sophisticated bots to open, > in endless cycle with different time duration, every AdSense banner > which runs on your site.” The message goes on to warn that while the targeted site’s ad revenue will be briefly increased, “AdSense traffic assessment algorithms will detect very fast such a web traffic pattern asfraudulent.”
> “Next an ad serving limit will be placed on your publisher account > and all the revenue will be refunded to advertisers. This means that > the main source of profit for your site will be temporarily > suspended. It will take some time, usually a month, for the AdSense > to lift your ad ban, but if this happens we will have all the > resources needed to flood your site again with bad quality web > traffic which will lead to second AdSense ban that could be> permanent!”
The message demands $5,000 worth of bitcoin to forestall the attack. In this scam, the extortionists are likely betting that some publishers may see paying up as a cheaper alternative to having their main source of advertising revenue evaporate. The reader who shared this email said while he considered the message likely to be a baseless threat, a review of his recent AdSense traffic statistics showed that detections in his “AdSense invalid traffic report” from the past month had increased substantially. _Continuereading →_
← Older Entries
Advertisement
*
*
MAILING LIST
Subscribe here
*
*
RECENT POSTS
* FBI Arrests Alleged Owner of Deer.io, a Top Broker of StolenAccounts
* U.S. Govt. Makes it Harder to Get .Gov Domains * The Case for Limiting Your Browser Extensions * French Firms Rocked by Kasbah Hacker? * FCC Proposes to Fine Wireless Carriers $200M for Selling CustomerLocation Data
*
*
ALL ABOUT SKIMMERS
Click image for my skimmer series.*
*
SPAM NATION
A New York Times Bestseller!*
*
THE VALUE OF A HACKED PC Badguy uses for your PC*
TOOLS FOR A SAFER PC Tools for a Safer PC*
THE PHARMA WARS
Spammers Duke it Out*
BADGUY USES FOR YOUR EMAIL Your email account may be worth far more than you imagine.*
EBANKING BEST PRACTICES eBanking Best Practices for Businesses*
MOST POPULAR POSTS
* Sextortion Scam Uses Recipient's Hacked Passwords(1076)
* Online Cheating Site AshleyMadison Hacked(798)
* Sources: Target Investigating Data Breach(620)
* Cards Stolen in Target Breach Flood Underground Markets(445)
* Reports: Liberty Reserve Founder Arrested, Site Shuttered(416)
* Was the Ashley Madison Database Leaked?(376)
* True Goodbye: 'Using TrueCrypt Is Not Secure'(363)
* Who Hacked Ashley Madison?(361)
* Following the Money, ePassporte Edition(353)
* U.S. Government Seizes LibertyReserve.com(315)
*
CATEGORY: WEB FRAUD 2.0 Innovations from the Underground*
ID Protection Services Examined*
IS ANTIVIRUS DEAD?
The reasons for its decline*
THE GROWING TAX FRAUD MENACE File 'em Before the Bad Guys Can*
INSIDE A CARDING SHOP A crash course in carding.*
BEWARE SOCIAL SECURITY FRAUD Sign up, or Be Signed Up!*
HOW WAS YOUR CARD STOLEN? Finding out is not so easy.*
KREBS’S 3 RULES… ...For Online Safety. ------------------------- � 2020 Krebs on Security. Powered by WordPress. Privacy Policy
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0