Are you over 18 and want to see adult content?
More Annotations
Business, Legal, Tax, Investment, Accounting News | India Briefing
Are you over 18 and want to see adult content?

The Spideygirl Blog
Are you over 18 and want to see adult content?
Reiseberichte - Sehenswürdigkeiten - Reiseführer › Kanada Rundreisen
Are you over 18 and want to see adult content?
Textilscreens.de- reißfester Sonnenschutz mit Durchblick -Fabrikspreise
Are you over 18 and want to see adult content?

Báo tin tức Thông tấn Xã Việt Nam, Tin tức thời sự | baotintuc.vn
Are you over 18 and want to see adult content?

Camisetas, regatas e sacolas personalizadas, bonés | Target Bonés
Are you over 18 and want to see adult content?
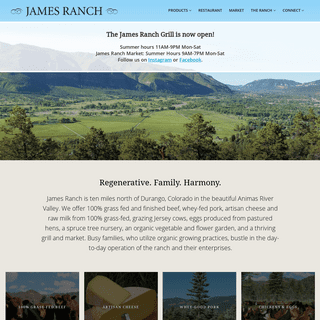
James Ranch | Sustainable Beef, Cheese, Pork, Raw Milk, Fresh Eggs, and Produce in Durango, CO
Are you over 18 and want to see adult content?

CICinema - Chronicle of Iranian Cinema, Iranian Movies and Celebrities
Are you over 18 and want to see adult content?

Terrace View Apartments for rent in Toms River, NJ $250 Rewards
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of pharmacyonline-canadian.xyz
Are you over 18 and want to see adult content?
A complete backup of americanjournalofsurgery.com
Are you over 18 and want to see adult content?

A complete backup of soundlabsgroup.com.au
Are you over 18 and want to see adult content?
A complete backup of pandorajoyasde.es
Are you over 18 and want to see adult content?
Text
ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices. VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC FOR GDPR COMPLIANCE Improve your GDPR compliance with a solution that provides clientless endpoint management, visibility and control, addresses GDPR requirements and has the ability toENDPOINT MANAGEMENT
Endpoint security management is the practice of managing network security, often on an enterprise level, through a combination of policy and security-based technology. Network security is generally handled through software suites alone (antivirus, spyware / malware protection etc.) rather than through a more advanced, combinedapproach.
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
PROMISEC – ACTIONABLE ENDPOINT INTELLIGENCE Inspect. Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices. VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC FOR GDPR COMPLIANCE Improve your GDPR compliance with a solution that provides clientless endpoint management, visibility and control, addresses GDPR requirements and has the ability toENDPOINT MANAGEMENT
Endpoint security management is the practice of managing network security, often on an enterprise level, through a combination of policy and security-based technology. Network security is generally handled through software suites alone (antivirus, spyware / malware protection etc.) rather than through a more advanced, combinedapproach.
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
ENDPOINT MANAGER
Endpoint manager. PEM leverages patented technology to quickly inspect your entire enterprise to identify, analyze, and remediate security gaps. The solution is engineered to run at scale on any network, covering use cases from compliance through cyber. Why do you need PEM, when there are so many security solutions?ANNOUNCEMENTS
Promisec Team | 13 Apr, 2021. Promisec Announces New and Revamped Version of Its Endpoint Manager + ENDPOINT SECURITY MANAGEMENT SOFTWARE & SOLUTIONS Endpoint Security - Promisec’s unique agentless Endpoint Security Management software gives you 100% visibility & enables you to manage multiple endpoints within 6-10 sec. PROMISEC CAN HELP YOU PREVENT WANNACRY RANSOMWARE The ransom asked against the decryption key starts with $300 Bitcoin which increases after every few hours. Promisec can help you prevent. WannaCry ransomware! Light touch on premise installation plus optional cloud scanning capabilities. Rapid search and detect functionality across 1000s of endpoints. Quick patch deployment and verification.INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data. CLOUD BASED ENDPOINT PROTECTION Cloud Endpoint Protection. Cloud endpoint security products are still new with relatively low levels of adoption. That being said; advanced cloud-based endpoint management is a service which provides a myriadof benefits.
ENDPOINT SOFTWARE FOR BANKING REGULATORS Why Promisec. Why You Need Promisec; How We Help; The Promisec ROI; Customer Success; Solutions. On-Premise. Promisec Endpoint Manager Platform The Promisec Endpoint Manager (PEM) Platform delivers true Endpoint Detection and Response (EDR) through agentless inspection, threat detection, alerting, reporting and automated remediation delivering huge value for both security and IT WWW.PROMISEC.COMTRANSLATE THIS PAGEwww.promisec.com
PEM VERSION 5.20 RELEASE NOTES www. Promisec – Member of the MER Group 5 Hatzoref St., Holon 5885633, Israel T+972-3-5572555 F+972-3-5580282 promisec.com | info@ .com ©2018 Promisec – Private & ConfidentialPROMISEC.COM
promisec.com
PROMISEC – ACTIONABLE ENDPOINT INTELLIGENCE Inspect. Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices. VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC FOR GDPR COMPLIANCE Improve your GDPR compliance with a solution that provides clientless endpoint management, visibility and control, addresses GDPR requirements and has the ability toENDPOINT MANAGEMENT
Endpoint security management is the practice of managing network security, often on an enterprise level, through a combination of policy and security-based technology. Network security is generally handled through software suites alone (antivirus, spyware / malware protection etc.) rather than through a more advanced, combinedapproach.
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
PROMISEC – ACTIONABLE ENDPOINT INTELLIGENCE Inspect. Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices. VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC FOR GDPR COMPLIANCE Improve your GDPR compliance with a solution that provides clientless endpoint management, visibility and control, addresses GDPR requirements and has the ability toENDPOINT MANAGEMENT
Endpoint security management is the practice of managing network security, often on an enterprise level, through a combination of policy and security-based technology. Network security is generally handled through software suites alone (antivirus, spyware / malware protection etc.) rather than through a more advanced, combinedapproach.
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
ENDPOINT MANAGER
Endpoint manager. PEM leverages patented technology to quickly inspect your entire enterprise to identify, analyze, and remediate security gaps. The solution is engineered to run at scale on any network, covering use cases from compliance through cyber. Why do you need PEM, when there are so many security solutions?ANNOUNCEMENTS
Promisec Team | 13 Apr, 2021. Promisec Announces New and Revamped Version of Its Endpoint Manager + ENDPOINT SECURITY MANAGEMENT SOFTWARE & SOLUTIONS Endpoint Security - Promisec’s unique agentless Endpoint Security Management software gives you 100% visibility & enables you to manage multiple endpoints within 6-10 sec. PROMISEC CAN HELP YOU PREVENT WANNACRY RANSOMWARE The ransom asked against the decryption key starts with $300 Bitcoin which increases after every few hours. Promisec can help you prevent. WannaCry ransomware! Light touch on premise installation plus optional cloud scanning capabilities. Rapid search and detect functionality across 1000s of endpoints. Quick patch deployment and verification. ENDPOINT SOFTWARE FOR BANKING REGULATORS Why Promisec. Why You Need Promisec; How We Help; The Promisec ROI; Customer Success; Solutions. On-Premise. Promisec Endpoint Manager Platform The Promisec Endpoint Manager (PEM) Platform delivers true Endpoint Detection and Response (EDR) through agentless inspection, threat detection, alerting, reporting and automated remediation delivering huge value for both security and IT CLOUD BASED ENDPOINT PROTECTION Cloud Endpoint Protection. Cloud endpoint security products are still new with relatively low levels of adoption. That being said; advanced cloud-based endpoint management is a service which provides a myriadof benefits.
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data. WWW.PROMISEC.COMTRANSLATE THIS PAGEwww.promisec.com
PEM VERSION 5.20 RELEASE NOTES www. Promisec – Member of the MER Group 5 Hatzoref St., Holon 5885633, Israel T+972-3-5572555 F+972-3-5580282 promisec.com | info@ .com ©2018 Promisec – Private & ConfidentialPROMISEC.COM
promisec.com
PROMISEC – ACTIONABLE ENDPOINT INTELLIGENCE Inspect. Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices.ENDPOINT MANAGER
Endpoint manager. PEM leverages patented technology to quickly inspect your entire enterprise to identify, analyze, and remediate security gaps. The solution is engineered to run at scale on any network, covering use cases from compliance through cyber. Why do you need PEM, when there are so many security solutions? VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC CAN HELP YOU PREVENT WANNACRY RANSOMWARE The ransom asked against the decryption key starts with $300 Bitcoin which increases after every few hours. Promisec can help you prevent. WannaCry ransomware! Light touch on premise installation plus optional cloud scanning capabilities. Rapid search and detect functionality across 1000s of endpoints. Quick patch deployment and verification.INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
PROMISEC – ACTIONABLE ENDPOINT INTELLIGENCE Inspect. Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.ABOUT – PROMISEC
Promisec is a CYDERO company since November 2019 and includes an elite team of cyber experts from 8200 alumni. The company operates from its headquarters in Israel and collaborates with local partners in the USA, EMEA and APAC. Promisec is the developer of Endpoint Manager, an agentless solution that delivers complete visibility and remediation IT INVENTORY MANAGEMENT SOFTWARE Enhance efficiency with agent-less inventory management software systems. Are you looking to streamline your processes while at the same time want to reduce the costs of IT inventory management? COMPLIANCE MANAGEMENT SOLUTIONS Promisec can ensure compliance of your endpoints thru continuous monitoring of your environments adherence to a golden image or standard configuration. This golden image can be quickly defined by pointing to a real system or created custom by you. Promisec can leverage known standards such as NIST and CIS policy definitions andsupports PCI-DSS
APPLICATION VISIBILITY AND CONTROL Promisec Application Visibility and Controls retrieve detailed software information of all your endpoints. Commonly defined application visibility and control policies do not allow employees to download or execute unwanted applications and use corporate digital assets for personal use or allow transfer of data to external devices.ENDPOINT MANAGER
Endpoint manager. PEM leverages patented technology to quickly inspect your entire enterprise to identify, analyze, and remediate security gaps. The solution is engineered to run at scale on any network, covering use cases from compliance through cyber. Why do you need PEM, when there are so many security solutions? VULNERABILITY SCANNING AND DETECTION Vulnerability Scanning Tools. Vulnerability scanning tools can help you automate security auditing and can play a crucial part in your IT security strategy. Finding vulnerabilities goes beyond simply scanning for services that are exposed to the network. Successful vulnerability scanning also involves deep inspection of endpoints to ensure that PROMISEC CAN HELP YOU PREVENT WANNACRY RANSOMWARE The ransom asked against the decryption key starts with $300 Bitcoin which increases after every few hours. Promisec can help you prevent. WannaCry ransomware! Light touch on premise installation plus optional cloud scanning capabilities. Rapid search and detect functionality across 1000s of endpoints. Quick patch deployment and verification.INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.WWW.PROMISEC.COM
www.promisec.com
WWW.PROMISEC.COM
www.promisec.com
INCIDENT RESPONSE
Cyber Incident Response Starts Before Hackers Have a Chance to Spread. From advanced persistent threats (APTs), to sophisticated phishing attacks and attempts to breach the perimeter of the network, attackers are constantly looking for ways to get your users and systems to run their malware in order to gain unfettered access to your data.ENDPOINT MANAGEMENT
Endpoint security management is the practice of managing network security, often on an enterprise level, through a combination of policy and security-based technology. Network security is generally handled through software suites alone (antivirus, spyware / malware protection etc.) rather than through a more advanced, combinedapproach.
CONTACT US – PROMISEC Address. 7a HaShalom Rd, Tel Aviv-Yafo, 6789208, Israel. Support SOFTWARE LICENSE MANAGEMENT Software License Management. According to the Business Software Alliance (BSA), 43% of software installed on personal computers around the world – including servers, workstations, laptops and tablets at organizations of all sizes – is not properly licensed.ANNOUNCEMENTS
Promisec Team | 13 Apr, 2021. Promisec Announces New and Revamped Version of Its Endpoint Manager + APPLICATION WHITELISTING SOFTWARE Application whitelisting software. Organizations generally have a standard operating environment, or SOE. This ensures consistent performance and reliability by maintaining the same basic software, operating system, and applications across the user base. PROMISEC.COMTRANSLATE THIS PAGEpromisec.com
OEM PARTNERS
Why Promisec. Why You Need Promisec; How We Help; The Promisec ROI; Customer Success; Solutions. On-Premise. Promisec Endpoint Manager Platform The Promisec Endpoint Manager (PEM) Platform delivers true Endpoint Detection and Response (EDR) through agentless inspection, threat detection, alerting, reporting and automated remediation delivering huge value for both security and IT operations. PROMISEC INTEGRITY CLOUD Promisec Integrity leverages the flexibility and scalability of the cloud to offer advanced cyber protection that is affordable and easy to deploy and use in small-to-medium enterprise environments. PROMISEC ENDPOINT MANAGER Designed to meet the complex security needs of large global enterprises, Promisec Endpoint Manager provides visibility and remediation capabilities across the entire endpoint environment.* Overview
* Solution Brief
* System Requirements* Free Trial
* Request a Live DemoGET IN TOUCH
Promisec LLC
One Boston Place
Suite 2600
Boston MA 02108
Sales: sales@promisec.com Support: support@promisec.com __More Contact Options Feel free to start a live chat with us from the bottom of your screens____
* Why Promisec
* Why You Need Promisec* How We Help
* The Promisec ROI
* Customer Success
* Solutions
* __ On-Premise__
* Promisec Endpoint Manager PlatformThe Promisec Endpoint Manager (PEM) Platform delivers true Endpoint Detection and Response (EDR) through agentless inspection, threat detection, alerting, reporting and automated remediation delivering huge value for both security andIT operations.
* Overview
* Capabilities
* Benefits
* __ System Requirements * __ Free Demo Request* __ Use Cases__
* Endpoint Management * Application Visibility and Control* Incident Response
* Vulnerability Scanning and Detection * IT Inventory Management * Compliance Management Solutions* GDPR Compliance
* PCI DSS Compliance Software * ISO 27001 Compliance* HIPAA Compliance
* Software License Management * Cloud based Endpoint Protection * Application Whitelisting Software * Prevent WannaCrypt Ransomware* __ Industries__
* __ Retail
* __ Health Care
* __ Financial
* __ Service
* __ Legal
* __ Government
* __ Telecommunication * Technology Integrations* ITSM Tools
* SIEM Tools
* Downloads
* Solution Briefs__
* __ Promisec Endpoint Manager * Integrated Platforms * __ BlueCoat and Promisec solution brief * __ PEM Plus Portnox and Arcsight* Whitepapers__
* __ SCCM Use Cases and Solutions * __ SANS Product Review * __ SANS Critical Controls * __ Avoid Panama Papers Leak * __ Avoid Locky Ransomware * __ Use Cyber Intelligence – Intelligently * __ Enforcing Security Compliance * __ Cyber Best Practices * __ Cyber Configurations* __ ArcSight
* __ Why Security Programs Continue to Miss the Mark* Case Studies__
* __ Elisra Electronic Systems Ltd. * __ University Health Sciences Center* __ Amdocs
* __ State Education Association* __ New York Bank
* __ Bouygues Telecom* __ Fossil Group
* Videos__
* All Videos
* Webcasts
* __ Youtube
* Company
* Featured In
* About__
* Contact Sales or Support* Where to Buy
* Partners__
* Find a Partner
* __ Premier Partner Program * __ Value-Added Resellers* __ Distributor
* __ MSSP
* __ Technology Partners* __ OEM Partners
* __ Technology Integrations* __ ITSM
* __ NAC
* __ SIEM
* Blog__
* All Posts
* News
* #press-coverage
* #endpoint-security* #cyber-attacks
* #infographic
* Careers
* Contact Us
__
__ __
__ Schedule Demo
Compliance, Inventory management and Threat Detection Without Agents__Watch Video
ENDPOINT SECURITY MANAGEMENT SOFTWARE AND SOLUTIONS _devices and the critical content on them_ _results for security and compliance_ _issues, to achieve desired endpoint state_PROMISEC SOLUTIONS
ON PREMISE
PROMISEC ENDPOINT MANAGER Designed to meet the complex security needs of large global enterprises, Promisec Endpoint Security Software provides visibility and remediation capabilities across the entire endpoint environment.__ Learn More
__ Solution Brief
ESTABLISH A SECURE ENDPOINT FOUNDATION LET’S TALK NUMBERS150+
Active Customers
13+
Years Active
1200000+
Endpoints Managed
6+
Patents
OUR CUSTOMERS LOVE US!SUCCESS STORIES
_“It is very important for us to be able to know that our endpoints are secure across the entire enterprise, Promisec allows us to monitor and remediate policy non-compliance across the enterprise. We are pleased with Promisec’s clientless approach which is flexible, non-disruptive and quick to implement. Not having to install software on each and every PC is a major selling point.”_ Nancy Lundergan, Manager of Security and Process Skadden Arps _“We have found the key benefits of Promisec Endpoint Security Software to be many. In particular, we have significantly increased visibility into all of our endpoints and we now have the ability to take immediate action when issues are found so that we are confident that our endpoints are in compliance”_ Dennis Thomas, Manager Systems Engineering IS Operations Fossil Group _“With Promisec Endpoint Manager we can control our global security policies, while enabling our regional system and security administrators to view the very same reports. This provides us with visibility and a full understanding of the risks, their severity, and the tools needed to minimize them.”_ Amdocs IT Professional Amdocs _“It is very important for us to be able to know that our endpoints are secure across the entire enterprise, Promisec allows us to monitor and remediate policy non-compliance across the enterprise. We are pleased with Promisec’s clientless approach which is flexible, non-disruptive and quick to implement. Not having to install software on each and every PC is a major selling point.”_ Nancy Lundergan, Manager of Security and Process Skadden Arps _“We have found the key benefits of Promisec Endpoint Security Software to be many. In particular, we have significantly increased visibility into all of our endpoints and we now have the ability to take immediate action when issues are found so that we are confident that our endpoints are in compliance”_ Dennis Thomas, Manager Systems Engineering IS Operations Fossil Group_
_
_
_
CLIENTELE
FEATURED IN
_
_
_
_
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0