Are you over 18 and want to see adult content?
5
More Annotations
2
A complete backup of kenh14.vn/xau-chuoi-nhanh-loat-phot-qua-lai-cua-thay-tro-chau-dang-khoa-vai-tieng-qua-orange-boc-cong-ty-kh
kenh14.vn/xau-chuoi-nhanh-loat-phot-qua-lai-cua-thay-tro-chau-dang-khoa-vai-tieng-qua-orange-boc-cong-ty-khong-du-trinh-do-tieng-anh-lyly-to-chau-dang-khoa-dung-ten-ca-khuc-do-minh-sang-tac-2020030216113809.chn
Are you over 18 and want to see adult content?
4
Favourite Annotations

A complete backup of totositekorea.com
totositekorea.com
Are you over 18 and want to see adult content?
2

A complete backup of galeriebuchholz.de
galeriebuchholz.de
Are you over 18 and want to see adult content?
1
Text
ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security. * Instagram
* Instagram
* Instagram
\AppData\Local\Programs\Python\Python37\), so if you want to use some custom modules you have to use the (complex) default structure, or you can use your own. Using your own directories for custom modules requires adding the path(s) to the environment variable PYTHONPATH.
my.startup ProgramArguments
launchctl setenv PYTHONPATH ~/Python_Scripts/_my_modules RunAtLoad
The string ‘~/Python_Scripts_/_my_modules/’ points to my custom module directory. Edit this to reflect your own directory structure. If you need multiple directories you can add these by seperating them by using a colon (:) e.g.
my.startup ProgramArguments
launchctl setenv PYTHONPATH ~/Python_Scripts/_my_modules:~/Desktop/my_scripts RunAtLoad
To makes these changes active you can either REBOOT, LOG-OUT/LOG-in or execute the following command: launchctl load ~/Library/LaunchAgents/my.startup.plist _ * _snmp routing-instant-access access-list _ Having done that, AND adding a _context_ parameter to the actual query will give the correct results. Posted on June 27, 2018 by Willem and filed under Junos , Security , Tips'n Tricks and tagged snmpv3 srx virtual router
LEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IRREDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsSWITCHED2MAC
March 7th, 2009. My first introduction to Apple was in my early years. A brother of a friend of mine had an Apple PC at home for work. In those days we played a lot of “Dark Castle” on that Apple PC (no idea what the type was/is). I do remember that it was kinda weird that the PC had this weird 3.5″ floppy disk, since my Commodore 64 has those cool Double Sided Double Density 5.25 CARL ZEISS AND LEICA 50MM LENS COMPARISSON Carl Zeiss and Leica 50mm Lens Comparisson. When I got the Leica M9, the Leica Summilux 50mm was nowhere to found. So, at the time, I 'settled' for the Carl Zeiss (CZ) C Sonnar 1.5/50mm ZM lens instead, and entered the world of the Leica waiting-list. A couple of weeks back I got the call that the latest version of the Summilux wasavailable
REDELIJKHEID
Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
DIY PORN ON THE IPHONE Most of the regular iPhone / iPod Touch users already know that there's no sign of porn or erotica to be found in the Apple App Store. Reason for this is (according ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security.LEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IRREDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsSWITCHED2MAC
March 7th, 2009. My first introduction to Apple was in my early years. A brother of a friend of mine had an Apple PC at home for work. In those days we played a lot of “Dark Castle” on that Apple PC (no idea what the type was/is). I do remember that it was kinda weird that the PC had this weird 3.5″ floppy disk, since my Commodore 64 has those cool Double Sided Double Density 5.25 CARL ZEISS AND LEICA 50MM LENS COMPARISSON Carl Zeiss and Leica 50mm Lens Comparisson. When I got the Leica M9, the Leica Summilux 50mm was nowhere to found. So, at the time, I 'settled' for the Carl Zeiss (CZ) C Sonnar 1.5/50mm ZM lens instead, and entered the world of the Leica waiting-list. A couple of weeks back I got the call that the latest version of the Summilux wasavailable
REDELIJKHEID
Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
DIY PORN ON THE IPHONE Most of the regular iPhone / iPod Touch users already know that there's no sign of porn or erotica to be found in the Apple App Store. Reason for this is (according ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms LEICA M — LEICA DIARY — REDELIJKHEID Ever since the introduction of the Leica M10, I got this itch.One I didn't get when Leica introduced every other type 2xx version of the M-camera. But the new M10 doesn't come cheap, and what's a 6/7 year old M9 worth nowadays? LEICA RELEASED THE LEICA M10 I got the Leica M9 a couple of years ago, and in the meantime they released several Leica M Type 24x and 26x versions with, and without video etc. I still like the M9, eventhough it lacks video, high ISO, etc.. I like it because it digital photography without any overhead. No fancy auto-focus, 4k vi GOODBYE MY OLD FRIEND Ever since the introduction of the Leica M10 , I got this itch. One I didn't get when Leica introduced every other type 2xx version of the M-camera. But the new M10 doesn't come cheap, and what's a 6/7 year old M9 worth nowadays? An upgrade is only an option if LEICA MINI M IS A SLOW LEICA X VARIO CAMERA The cat is out of the bag. Full specs are available now, and it is disappoining. Very disappointing (for the price). The Mini M is actually a Leica X with a fixed zoom lens . And not just any zoomlens. No, a slow zoomlens. No (hidden) M-Mount to play with. I really wonderwho (in their
THE LEICA M, AND WILL I GET ONE? Leica M Leica announced the new Leica M rangefinder camera earlier this week. It wasn't named the M10, but just M. The new rangefinder will have: 24Mpix CMOS sensor Better ISO performance Live-view with focus peaking Movie-mode (max. 1080p@25fps) Better dynamic rangeBigger and bett
GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
DIY PORN ON THE IPHONE Most of the regular iPhone / iPod Touch users already know that there's no sign of porn or erotica to be found in the Apple App Store. Reason for this is (accordingMISCELLANEOUS
This gallery is the general photobucket'. Browse through it if you like. Use the Dynamic galleries to browse a certain topic (e.g. Leica Shots -> Photos taken with my Leica). ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security.REDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
LEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IR WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security.REDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
LEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IR WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms LEICA M — LEICA DIARY — REDELIJKHEID Ever since the introduction of the Leica M10, I got this itch.One I didn't get when Leica introduced every other type 2xx version of the M-camera. But the new M10 doesn't come cheap, and what's a 6/7 year old M9 worth nowadays? IMPORTING DEVICES IN MICROSOFT ACTIVE DIRECTORY The Microsoft Active Directory is a place where you can find different kind of objects; Users Computers Servers Printers (Security) Groups etc. One thing you don't find are generic devices . And with devices I mean devices according to the LDAP definition ( ObjectClass: device ). LEICA MINI M IS A SLOW LEICA X VARIO CAMERA The cat is out of the bag. Full specs are available now, and it is disappoining. Very disappointing (for the price). The Mini M is actually a Leica X with a fixed zoom lens . And not just any zoomlens. No, a slow zoomlens. No (hidden) M-Mount to play with. I really wonderwho (in their
LEICA SUMMILUX-M 50MM SHARPNESS Last week, I headed out for an early morning walk. Playing a bit with my new Leica Summilux-M 50mm Asph, I was amazed by the sharpness of this lens at f/1.4. The following image was taken at the minimum focussing distance (~0.7m); Frozen Heath @ 50mm f/1.4 Viewing aSWITCHED2MAC
The SWITCHED2MAC.COM domain is for sale. Use the contact page for inquiries. My first introduction to Apple was in my early years. A brother of a friend of mine had an Apple PC at home for work. In those days we played a lot of “ Dark Castle ” on that Apple PC (no idea what the type was/is). I do remember that it was kinda weird that thePC
APPLE IOS PERSONAL HOTSPOT ANNOYANCES Apple iOS Personal Hotspot Annoyances. This week, I ran into an annoying feature regarding the Apple iOS Personal Hotspot function of my iPhone 5s. I had to do some software testing with various WiFi clients. This worked fine, up to the moment that new devices ran into connectivity problems. The new devices could connect, but got amessage that
UPLOAD CA CERTIFICATE FOR SYMBIAN BASED PHONES V2.0 Import CA Certificate On Symbian Based Phones v2.0. This web page enables users with a Symbian-based smartphone (like the Nokia E50, E60, E61, E61i, E62, E65, E70, E71, E90 and the N-Series) to import CA certificates in a very easy manner.MISCELLANEOUS
This gallery is the general photobucket'. Browse through it if you like. Use the Dynamic galleries to browse a certain topic (e.g. Leica Shots -> Photos taken with my Leica). WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :)REDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE The problems mentioned before can be solved with the open-source program called Calibre . The e-book management program is available for most operating systems (Windows Apple OS X, Linux), and is extremely powerful. The interface isn't as slick as most commercial programs (in general), but that is one of the open-source features(also in
USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. ENABLE JUNIPER SRX FIREWALL LOGGING Juniper started to migrate their firewalls from Netscreen to the Junos environment 'a couple of' months back. The advantage is that there's a universal OS for routers, switches and firewalls. Just like Cisco IOS. The disadvantage is that the Junos OS is being adapted for the firewalls. So the founda BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :)REDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE The problems mentioned before can be solved with the open-source program called Calibre . The e-book management program is available for most operating systems (Windows Apple OS X, Linux), and is extremely powerful. The interface isn't as slick as most commercial programs (in general), but that is one of the open-source features(also in
USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. ENABLE JUNIPER SRX FIREWALL LOGGING Juniper started to migrate their firewalls from Netscreen to the Junos environment 'a couple of' months back. The advantage is that there's a universal OS for routers, switches and firewalls. Just like Cisco IOS. The disadvantage is that the Junos OS is being adapted for the firewalls. So the founda BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security.LEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IR WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms IMPORTING DEVICES IN MICROSOFT ACTIVE DIRECTORY The Microsoft Active Directory is a place where you can find different kind of objects; Users Computers Servers Printers (Security) Groups etc. One thing you don't find are generic devices . And with devices I mean devices according to the LDAP definition ( ObjectClass: device ). ENABLE JUNIPER SRX FIREWALL LOGGING Juniper started to migrate their firewalls from Netscreen to the Junos environment 'a couple of' months back. The advantage is that there's a universal OS for routers, switches and firewalls. Just like Cisco IOS. The disadvantage is that the Junos OS is being adapted for the firewalls. So the founda JUNOS DUAL ISP BACKUP ROUTE CONFIGURATION Junos Dual ISP Backup Route Configuration. The last couple of years, we've had two ISP's on premise. One ( XS4ALL) for basic Internet Access via VDSL, and one our (VoIP) phone provided by Ziggo. The Ziggo phone services includes free (and ultra lite) Internet access through the use of their cable modem. It's ultra-lite, since it's only256kbps.
GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, youSWITCHED2MAC
The SWITCHED2MAC.COM domain is for sale. Use the contact page for inquiries. My first introduction to Apple was in my early years. A brother of a friend of mine had an Apple PC at home for work. In those days we played a lot of “ Dark Castle ” on that Apple PC (no idea what the type was/is). I do remember that it was kinda weird that thePC
CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsREDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ IMPORTING DEVICES IN MICROSOFT ACTIVE DIRECTORY The Microsoft Active Directory is a place where you can find different kind of objects; Users Computers Servers Printers (Security) Groups etc. One thing you don't find are generic devices . And with devices I mean devices according to the LDAP definition ( ObjectClass: device ). KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE The problems mentioned before can be solved with the open-source program called Calibre . The e-book management program is available for most operating systems (Windows Apple OS X, Linux), and is extremely powerful. The interface isn't as slick as most commercial programs (in general), but that is one of the open-source features(also in
USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. CONFIGURE SSL CERTIFICATE FOR JUNIPER J-WEB INTERFACE The contents of this text file is added to the SRX firewall. Select in the J-Web GUI Configure -> System Properties -> Management Access, and press the Edit button.. Select the Certificate tab, and press Add. Enter a logical name for the certificate (preferably the FQDN of the certificate), and past the entire contents of the exported PEM file in the Certificate content text-area, and press OK. CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsREDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ IMPORTING DEVICES IN MICROSOFT ACTIVE DIRECTORY The Microsoft Active Directory is a place where you can find different kind of objects; Users Computers Servers Printers (Security) Groups etc. One thing you don't find are generic devices . And with devices I mean devices according to the LDAP definition ( ObjectClass: device ). KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE The problems mentioned before can be solved with the open-source program called Calibre . The e-book management program is available for most operating systems (Windows Apple OS X, Linux), and is extremely powerful. The interface isn't as slick as most commercial programs (in general), but that is one of the open-source features(also in
USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. CONFIGURE SSL CERTIFICATE FOR JUNIPER J-WEB INTERFACE The contents of this text file is added to the SRX firewall. Select in the J-Web GUI Configure -> System Properties -> Management Access, and press the Edit button.. Select the Certificate tab, and press Add. Enter a logical name for the certificate (preferably the FQDN of the certificate), and past the entire contents of the exported PEM file in the Certificate content text-area, and press OK. CISCO ISE: CHANGE OF AUTHORIZATION (COA) NOT WORKING Dynamic Authorization Failed : 11213 No responds received from Network Access Device. After some searching, we found out that the support for Change of Authorization (CoA - RFC 3576) was disabled on the Cisco Wireless LAN Controllers (a what you would call a WTF moment). View fullsize. In this screenshot, the support for RFC 3576 is enabled. It ABOUT ME — REDELIJKHEID Hi, my name is Willem Redelijkheid (William Reasonableness in English, or Guillaume Raisonnable in French). In my professional life, I’m a Technical Consultant with the largest telecommunication provider in the Netherlands, and working on corporate network security. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsLEICA DIARY
Leica M10 with Zeiss Distagon 4/18 ZM and Infrared. Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. While browsing my filter set I found found my IR WORKFLOW — REDELIJKHEID Workflow. The following epos is an overview of the workflow I (try to) follow when getting photos from the camera to the web or print. I hope it helps others to understand why my photos suck :) CONFIGURE SSL CERTIFICATE FOR JUNIPER J-WEB INTERFACE The contents of this text file is added to the SRX firewall. Select in the J-Web GUI Configure -> System Properties -> Management Access, and press the Edit button.. Select the Certificate tab, and press Add. Enter a logical name for the certificate (preferably the FQDN of the certificate), and past the entire contents of the exported PEM file in the Certificate content text-area, and press OK. PHOTOS.REDELIJKHEID.COM Powered by SmugMug. After Curfew . Curfew ended at 04:30, and we wereout around 04:40
JUNOS DUAL ISP BACKUP ROUTE CONFIGURATION Junos Dual ISP Backup Route Configuration. The last couple of years, we've had two ISP's on premise. One ( XS4ALL) for basic Internet Access via VDSL, and one our (VoIP) phone provided by Ziggo. The Ziggo phone services includes free (and ultra lite) Internet access through the use of their cable modem. It's ultra-lite, since it's only256kbps.
ENABLE JUNIPER SRX FIREWALL LOGGING Juniper started to migrate their firewalls from Netscreen to the Junos environment 'a couple of' months back. The advantage is that there's a universal OS for routers, switches and firewalls. Just like Cisco IOS. The disadvantage is that the Junos OS is being adapted for the firewalls. So the founda GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. To solve this I needed to injectthe route
BLOG - EVERYTHING WITHIN REASON - REDELIJKHEID Leica M7 à la Carte This post is for everyone who wishes me the best. In this case, the best à la carte (film-based) Leica M camera. Our German friends @ Leica created a website called 'Leica à la Carte' where you can order a fully customizable Leica M7 or MP. They have a nice wizard where you can specify every option for the M camera, but in stead of hitting a submit button at the end, you XIAOMI XIAOFANG WIRELESS CAMERA CUSTOM FIRMWARE HACKXIAOMI CAMERA HACKXIAOMI XIAOFANG 1SXIAOMI XIAOFANG SETUPXIAOMI CAMERA HOMEXIAOMI FIRMWARE DOWNLOADXIAOMI FIRMWARE MOD Xiaomi Xiaofang Wireless Camera Custom Firmware Hack. A colleague of mine demonstrated a Wyze webcam a couple of weeks before. A nifty little FullHD wireless IP camera that has a decent (iOS/Android) app and cloud connectivity to store the data. I liked everything about it, except the cloud-storage part. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's termsREDELIJKHEID
It’s a file generated from the information in the oui.txt file. Solution: In the netaddr directory where the oui.txt and oui.idx is located is a ieee.py script. Run that script, and it creates a new idx file based on the oui.txt file in that directory (as shown in thefollowing example).
DOCKER IMAGES NOT STARTING For some reason IPv6 (the hint is tcp6) is screwing things up. The problem is that I disabled IPv6 from the start on this host. Mainly because of some concerns in regards of routing and internet accessibility (I have a formal IPv6 subnet at home). CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CONFIGURE NGINX AS A SECURE REVERSE PROXY NGINX (pronounced as engine-x) is a versatile (reverse) proxy service for Linux which can be used for many purposes. This post gives a relative small and easy example that I use at home for accessing insecure web services in my home. These are: Domoticz Free and USEFULL JUNIPER SRX COMMANDS root@srx100> show security flow session summary. Clear sessions through the firewall. root@srx100> clear security flow session all. Switch to other node in a cluster via CLI (over the HA-link): root@srx100> request routing-engine login node 1. For High End devices, the command will be from shell: % rlogin -Jk -T node1. KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE The problems mentioned before can be solved with the open-source program called Calibre . The e-book management program is available for most operating systems (Windows Apple OS X, Linux), and is extremely powerful. The interface isn't as slick as most commercial programs (in general), but that is one of the open-source features(also in
FLASHING THE SONOFF TH16 WIRELESS SWITCH The Sonoff TH16 is an inexpensive piece of hardware that can be controlled over WiFi. Apart from the switch (that's capable of handling electrical currents up to 16A) there's an interface for temperature and humidity. The actual temp/humid sensor is sold separately (in most cases). FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX The normal firewall policy logging will show traffic ALLOWED to these blocked ip addresses. Even if it's blocked by the firewall filter. If you need/want logging for this, you need to add the syslog statement. The syslog source is the Control plane. So make sure you collect the syslog messages from the Control pane. XIAOMI XIAOFANG WIRELESS CAMERA CUSTOM FIRMWARE HACKXIAOMI CAMERA HACKXIAOMI XIAOFANG 1SXIAOMI XIAOFANG SETUPXIAOMI CAMERA HOMEXIAOMI FIRMWARE DOWNLOADXIAOMI FIRMWARE MOD A colleague of mine demonstrated a Wyze webcam a couple of weeks before. A nifty little FullHD wireless IP camera that has a decent (iOS/Android) app and cloud connectivity to store the data. I liked everything about it, except the cloud-storage part. I don’t like it when I don’t know where my priREDELIJKHEID
The thing that took the most amount of time to figure out was the PUID/PGID part of the config. This basically are the user id and group id which are used to run the container and also when creating directories and files on the physical filesystem of the host.LEICA DIARY
Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. DOCKER IMAGES NOT STARTING For some reason IPv6 (the hint is tcp6) is screwing things up. The problem is that I disabled IPv6 from the start on this host. Mainly because of some concerns in regards of routing and internet accessibility (I have a formal IPv6 subnet at home). CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CONFIGURE NGINX AS A SECURE REVERSE PROXY NGINX (pronounced as engine-x) is a versatile (reverse) proxy service for Linux which can be used for many purposes. This post gives a relative small and easy example that I use at home for accessing insecure web services in my home. These are: Domoticz Free and KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE Since the bookcase in our living room is is reaching its maximum capacity, we're moving from traditional books to e-books. My wife already has the Sony PRS-T2 e-reader , and this week, I bought the Kobo Glo for myself. The reason for choosing the Kobo Glo is that it has an illuminated screen FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX Now that the foundation is in place, it's quite easy to add additional prefix-lists for different purposes. The easiest way of adding a lot of IP addresses is to use the CLI Editor in the WebGUI of the firewall, just add the IP addresses in CIDR format (don't forget the trailing semicolon).. The following configuration contains the set commands for my configuration. USEFULL JUNIPER SRX COMMANDS This post contains several useful Junos SRX commands for the CLI. Mainly for myself, because I don't use those command regularly. This post will be updated over time Here it goes: View session information: root@srx100> show security flow session summary Clear sessions throug FLASHING THE SONOFF TH16 WIRELESS SWITCH The Sonoff TH16 is an inexpensive piece of hardware that can be controlled over WiFi. Apart from the switch (that's capable of handling electrical currents up to 16A) there's an interface for temperature and humidity. The actual temp/humid sensor is sold separately (in most cases).LEICA DIARY
Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms KEEPASS PASSWORD GENERATOR With the increasing password complexity demands in both online and offline services, you basically can’t live without a password manager. Personally I use 1Password , but at work Keepass is recommended. Main reason is that it remains local (no passwords inREDELIJKHEID
The thing that took the most amount of time to figure out was the PUID/PGID part of the config. This basically are the user id and group id which are used to run the container and also when creating directories and files on the physical filesystem of the host. CISCO ISE MAC ADDRESSS DATABASE CLEAN UP Imagine having 15.000+ MAC addresses in a Cisco ISE database. All these MAC addresses are used to gain access to wireless networks protected with WPA2-PSK and MAC-filtering. But how to make sure that they are all (still) valid? Remove MAC Addresses After Change In ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ JUNIPER SRX APPLY-GROUPS A while back I wrote a blog post about enabling global logging on security rules . This week I applied the same technique to enable ping on all zones for testing / troubleshooting purposes. Instead of adding ping as a host-inbound-traffic system-service to all zones, andif you have a
GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. MICROSOFT CRYPTOGRAPHIC STORE AND PASSWORDS We've been experimenting with with the use of user certificates for VPN access to the lab. Issuing, and using them isn't the problem. The problem is that there's no way of enforcing a password on the use of the private key. You can use private key protection on the certificate template, but that sti WHERE CAN I FIND THE ITUNESHELPER APP? The iTunesHelper application is used to automatically detect iPod's/iPad's and iPhones, when you connect these to your Mac. The application launches iTunes, and (if configured) synchronizes stuff. Very handy, but it can be quite annoying. E.g. I have an iMac (main 'PC' around the house), and a Ma XIAOMI XIAOFANG WIRELESS CAMERA CUSTOM FIRMWARE HACKXIAOMI CAMERA HACKXIAOMI XIAOFANG 1SXIAOMI XIAOFANG SETUPXIAOMI CAMERA HOMEXIAOMI FIRMWARE DOWNLOADXIAOMI FIRMWARE MOD A colleague of mine demonstrated a Wyze webcam a couple of weeks before. A nifty little FullHD wireless IP camera that has a decent (iOS/Android) app and cloud connectivity to store the data. I liked everything about it, except the cloud-storage part. I don’t like it when I don’t know where my priREDELIJKHEID
The thing that took the most amount of time to figure out was the PUID/PGID part of the config. This basically are the user id and group id which are used to run the container and also when creating directories and files on the physical filesystem of the host.LEICA DIARY
Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. DOCKER IMAGES NOT STARTING For some reason IPv6 (the hint is tcp6) is screwing things up. The problem is that I disabled IPv6 from the start on this host. Mainly because of some concerns in regards of routing and internet accessibility (I have a formal IPv6 subnet at home). CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CONFIGURE NGINX AS A SECURE REVERSE PROXY NGINX (pronounced as engine-x) is a versatile (reverse) proxy service for Linux which can be used for many purposes. This post gives a relative small and easy example that I use at home for accessing insecure web services in my home. These are: Domoticz Free and KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE Since the bookcase in our living room is is reaching its maximum capacity, we're moving from traditional books to e-books. My wife already has the Sony PRS-T2 e-reader , and this week, I bought the Kobo Glo for myself. The reason for choosing the Kobo Glo is that it has an illuminated screen FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX Now that the foundation is in place, it's quite easy to add additional prefix-lists for different purposes. The easiest way of adding a lot of IP addresses is to use the CLI Editor in the WebGUI of the firewall, just add the IP addresses in CIDR format (don't forget the trailing semicolon).. The following configuration contains the set commands for my configuration. USEFULL JUNIPER SRX COMMANDS This post contains several useful Junos SRX commands for the CLI. Mainly for myself, because I don't use those command regularly. This post will be updated over time Here it goes: View session information: root@srx100> show security flow session summary Clear sessions throug FLASHING THE SONOFF TH16 WIRELESS SWITCH The Sonoff TH16 is an inexpensive piece of hardware that can be controlled over WiFi. Apart from the switch (that's capable of handling electrical currents up to 16A) there's an interface for temperature and humidity. The actual temp/humid sensor is sold separately (in most cases). XIAOMI XIAOFANG WIRELESS CAMERA CUSTOM FIRMWARE HACKXIAOMI CAMERA HACKXIAOMI XIAOFANG 1SXIAOMI XIAOFANG SETUPXIAOMI CAMERA HOMEXIAOMI FIRMWARE DOWNLOADXIAOMI FIRMWARE MOD A colleague of mine demonstrated a Wyze webcam a couple of weeks before. A nifty little FullHD wireless IP camera that has a decent (iOS/Android) app and cloud connectivity to store the data. I liked everything about it, except the cloud-storage part. I don’t like it when I don’t know where my priREDELIJKHEID
The thing that took the most amount of time to figure out was the PUID/PGID part of the config. This basically are the user id and group id which are used to run the container and also when creating directories and files on the physical filesystem of the host.LEICA DIARY
Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. DOCKER IMAGES NOT STARTING For some reason IPv6 (the hint is tcp6) is screwing things up. The problem is that I disabled IPv6 from the start on this host. Mainly because of some concerns in regards of routing and internet accessibility (I have a formal IPv6 subnet at home). CONFIGURING SYSLOG-NG ON UBUNTU Syslog-ng is a replacement for the default syslog daemons you get with most Linux distributions. The advantage of syslog-ng is that the configuration is easier to understand, and it gives the sys-admin numerous advantages. Especially in complex environments. Let's say wehave a
CONFIGURE NGINX AS A SECURE REVERSE PROXY NGINX (pronounced as engine-x) is a versatile (reverse) proxy service for Linux which can be used for many purposes. This post gives a relative small and easy example that I use at home for accessing insecure web services in my home. These are: Domoticz Free and KOBO GLO EBOOK LIBRARY MANAGEMENT WITH CALIBRE Since the bookcase in our living room is is reaching its maximum capacity, we're moving from traditional books to e-books. My wife already has the Sony PRS-T2 e-reader , and this week, I bought the Kobo Glo for myself. The reason for choosing the Kobo Glo is that it has an illuminated screen FILTER / BLOCK IP ADDRESSES ON A JUNIPER SRX Now that the foundation is in place, it's quite easy to add additional prefix-lists for different purposes. The easiest way of adding a lot of IP addresses is to use the CLI Editor in the WebGUI of the firewall, just add the IP addresses in CIDR format (don't forget the trailing semicolon).. The following configuration contains the set commands for my configuration. USEFULL JUNIPER SRX COMMANDS This post contains several useful Junos SRX commands for the CLI. Mainly for myself, because I don't use those command regularly. This post will be updated over time Here it goes: View session information: root@srx100> show security flow session summary Clear sessions throug FLASHING THE SONOFF TH16 WIRELESS SWITCH The Sonoff TH16 is an inexpensive piece of hardware that can be controlled over WiFi. Apart from the switch (that's capable of handling electrical currents up to 16A) there's an interface for temperature and humidity. The actual temp/humid sensor is sold separately (in most cases).LEICA DIARY
Yesterday, I picked up a second-hand Zeiss Distagon 4/18mm ZM for some landscape and general wide-angle photos. Since the Zeiss 18mm has a 58mm filter size, and my Lee filter kit contained a 58mm adapter, I wanted to see if that would work. CONTACT — REDELIJKHEID NOTE: requests or suggestions about website, or search-engine optimization / exposure (and that sort of useless crap) will be send to /dev/null (or in layman's terms KEEPASS PASSWORD GENERATOR With the increasing password complexity demands in both online and offline services, you basically can’t live without a password manager. Personally I use 1Password , but at work Keepass is recommended. Main reason is that it remains local (no passwords inREDELIJKHEID
The thing that took the most amount of time to figure out was the PUID/PGID part of the config. This basically are the user id and group id which are used to run the container and also when creating directories and files on the physical filesystem of the host. CISCO ISE MAC ADDRESSS DATABASE CLEAN UP Imagine having 15.000+ MAC addresses in a Cisco ISE database. All these MAC addresses are used to gain access to wireless networks protected with WPA2-PSK and MAC-filtering. But how to make sure that they are all (still) valid? Remove MAC Addresses After Change In ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\\ JUNIPER SRX APPLY-GROUPS A while back I wrote a blog post about enabling global logging on security rules . This week I applied the same technique to enable ping on all zones for testing / troubleshooting purposes. Instead of adding ping as a host-inbound-traffic system-service to all zones, andif you have a
GUILLAUME RAISONNABLE Juniper SRX, Routing Instances, and Syslog Challenges. In the previous post I described the issue I had with routing instances and DHCP-relay, and how I fixed it. It turns out that DHCP-relay wasn’t my only problem. Turns out that syslog also stopped at the time I implemented the routing instances. MICROSOFT CRYPTOGRAPHIC STORE AND PASSWORDS We've been experimenting with with the use of user certificates for VPN access to the lab. Issuing, and using them isn't the problem. The problem is that there's no way of enforcing a password on the use of the private key. You can use private key protection on the certificate template, but that sti WHERE CAN I FIND THE ITUNESHELPER APP? The iTunesHelper application is used to automatically detect iPod's/iPad's and iPhones, when you connect these to your Mac. The application launches iTunes, and (if configured) synchronizes stuff. Very handy, but it can be quite annoying. E.g. I have an iMac (main 'PC' around the house), and a Ma* Blogs
* Blog
* Leica Diary
* Tumblr
* Photography
* History
* Workflow
* My Photos
* About
* About Me
* Switched2Mac
* Contact
* Search
* Blogs
* Blog
* Leica Diary
* Tumblr
* Photography
* History
* Workflow
* My Photos
* About
* About Me
* Switched2Mac
* Contact
* Search
REDELIJKHEID
HOME OF GUILLAUME RAISONNABLE* Blog
* Leica Diary
* Tumblr
* All
* Annoying
* Apple
* Browsers
* Copyrights
* Domotica
* DRM
* Fun
* Gadgets
* Gaming
* Gear
* General
* Hardware
* Holiday
* Internet
* iPhone
* Junos
* Leica M9
* Linux
* Microsoft
* Movies
* Music
* News
* No Way!!!
* Operating Systems
* Personal
* Photography
* Privacy
* Programming
* Raspberry Pi
* Review
* Security
* Software
* Switched2Mac
* Symbian
* Tips'n Tricks
* TV
* Video
* Website
* WordPress
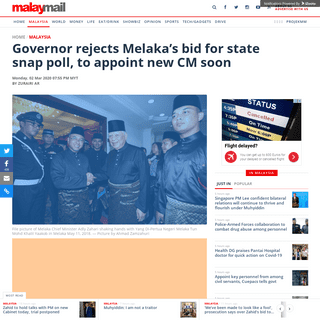
XIAOMI XIAOFANG WIRELESS CAMERA CUSTOM FIRMWARE HACK A colleague of mine demonstrated a Wyze webcam a couple of weeks before. A nifty little FullHD wireless IP camera that has a decent (iOS/Android) app and cloud connectivity to store the data. I liked everything about it, except the cloud-storage part. I don’t like it when I don’t know where my private data resides. So I started a to search to see if these devices could be altered to benefit my needs, and guess what, they can be altered. There’s a github projectwhere they
fabricated a firmware hack and with custom software the camera can be used for much more. So now I had to get my hands on the most inexpensive version of the camera. Since there are different brands that ship basically the same hardware with a different firmware, there’s more than enough choice.Read more …
Posted on November 19, 2019 by Willem and filed under Gadgets , Hardware , Security , Review , Tips'n Tricks and tagged Xiaomi firmware hack Xiaofang IP camera.
1 Likes
Share
Comment
ADD CUSTOM PYTHON3 MODULES PATH (WINDOWS / MACOS) After installing Python on Windows or MacOS, the installer makes sure that everything works fine. All paths are available/accessible for Python. Adding modules through pip also works just fine. The problem is that the paths used are hard to remember (e.g. Windows: c:\Users\WINDOWS
After installing Python, the installer add the PYTHONPATH environment variable to Windows. All you need to do is add your custom path tothis variable.
The environment variables can be found through: THIS PC -> PROPERTIES -> ADVANCED SETTINGS -> ENVIRONMENT VARIABLESIn screenshots:
MACOS
On my MacOS devices I had to add the path(s) to 2 different files because (regular) GUI based programs (like Pycharm and Python IDLE) use different environment variables than the terminal / consoleinterpreter.
GUI-BASED PROGRAMS
Create a startup plist file (e.g. ~/Library/LaunchAgents/my.startup.plist) and add the following XMLcontent:
Label
sh
-c
Label
sh
-c
TERMINAL / CONSOLE
For the terminal / console based Python interpreter you need to add some lines to the ~/.bash_profile file. PYTHONPATH="~/Python_Scripts/_my_modules:$"export PYTHONPATH
Multiple directories can (again) be added by using the colon seperator(:):
PYTHONPATH="~/Python_Scripts/_my_modules:~/Desktop/my_scripts:$"export PYTHONPATH
To activate this, just quit the open terminal/console windows (CMD-q)and open it again.
Posted on November 7, 2019 by Willem and filed under Programming, Tips'n Tricks
and tagged Python3 PYTHONPATH MacOSWindows .
1 Likes
Share
Comment
CISCO ISE MAC ADDRESSS DATABASE CLEAN UP Imagine having 15.000+ MAC addresses in a Cisco ISE database. All these MAC addresses are used to gain access to wireless networks protected with WPA2-PSK and MAC-filtering. But how to make sure that they are all (still) valid? REMOVE MAC ADDRESSES AFTER CHANGE IN AUTHENTICATION Finally, the time has come to implement 802.1x on the wireless network for a substantial amount of these devices. These devices are consist mainly of Windows machines or Thin Clients. Both of those are managed through either the Microsoft Active Directory or a Thin Client Management Suite. So, applying setting related to 802.1x are pretty straight forward to distribute. There are however some Windows / Thin client devices that will remain on the MAC-filtering wifi networks fornumerous reasons.
After a few tests the migration of the new 802.1x devices has started, but is leaving us with a MAC Address database filled with addresses that can be removed, since they are no longer used…. But how to do that? Cisco ISE has a lot of features, and is capable of generating rich reports about almost everything. However it has no way of reporting on dot1x devices that might still remain in the MAC address database as well. That is where I had to become creative. First I explored the Cisco ISE Monitoring API, but that only gives active connections. There’s no way of exploring past (successful) authentications/authorizations. I needed a way to get current and past successful dot1x authentications and compare the MAC addresses associated with those entries to the MAC address database, and remove those from that database. Eventually, I found two paths to accomplish this; First through the reporting module. There you can export all RADIUS authentications to CSV. Filtering these results in Excel, or through Python scripting, you are able to extract the MAC Addresses that successfully authenticated with dot1x. Feed these MAC addresses to a script and remove them through the Cisco ISE ERS API. Or if you’ve got nothing else to do; do it by hand. The other path is by following the syslog output and parsing that feed. The downside to this is that you have to have syslog file access or add an additional syslog server to Cisco ISE that you may access (e.g. your scripting machine). The syslog version makes a a bit more tricky, since the (syslog)log lines are very long and you have to combine the correct lines to get the full message. Parsing CSV is much easier, so I followed that path first. DORMANT/OBSOLETE MAC ADDRESSES Another issue with static MAC addresses (and even local accounts) is that they tend to remain indefinitely in the MAC database. Lang after devices have been decommissioned, the MAC address remains. Which leaves a security hole to be exploited. By using the generated ‘RADIUS Authentications’ reports over a longer time (e.g. 90 days) you can do a cross reference with MAC addresses in the database and recent successful authentications ofthat MAC address.
There are some caveats though;*
you need a session-timeout on the network (either statically defined on the network device) or by RADIUS return attribute, so that devices have to re-authenticate periodically. Otherwise you might not see a valid device in the logging and removed it by mistake.*
RADIUS Reporting goes only 30 days back, so you have to combine several (scheduled) reports to achieve a longer time span. There used to be a custom time frame option, but seems to have disappeared inversion 2.6
Posted on October 17, 2019 by Willem and filed under Programming, Security , Tips'n
Tricks and tagged Cisco ISE Identity Services Engine Python Scripting MAC Addressesdot1x 802.1x .
1 Likes
Share
Comment
INCREASE UBUNTU VM DISK SPACE I ran into a very familiar problem (for me anyway) on an Ubuntu 18 virtual machine today. It started with, what I thought was, a Cisco ISE issue. Cisco ISE reports that I wanted to write to a repository ended up as empty files (0 bytes). Initial thought was that I ran into an Cisco ISE bug related to repositories, but it turned out that my Ubuntu server had run out of disk space; Err:2 http://archive.ubuntu.com/ubuntu bionic-updates InRelease Error writing to output file - write (28: No space left on device) A quick DF -H revealed that my Ubuntu server had only 4GB (out of the 100GB I assigned in VMWare). willem@ubuntu:~$ df -h Filesystem Size Used Avail Use% Mounted on udev 967M 0 967M 0% /dev tmpfs 200M 1.1M 199M 1% /run /dev/mapper/ubuntu--vg-ubuntu--lv 3.9G 3.9G 0M 100% / tmpfs 997M 0 997M 0% /dev/shm tmpfs 5.0M 0 5.0M 0% /run/lock tmpfs 997M 0 997M 0% /sys/fs/cgroup /dev/loop0 90M 90M 0 100% /snap/core/7713 /dev/loop1 90M 90M 0 100% /snap/core/7917 /dev/sda2 976M 222M 688M 25% /boot tmpfs 200M 0 200M 0% /run/user/1000 So, now I had to add the unassigned 96GB to the Ubuntu filesystem. Thankfully, askubuntu to the rescue.
root@ubuntu:~# lvm
lvm> lvextend -l +100%FREE /dev/mapper/ubuntu--vg-ubuntu--lv Size of logical volume ubuntu-vg/ubuntu-lv changed from 4.00 GiB (1024 extents) to <99.00 GiB (25343 extents). Logical volume ubuntu-vg/ubuntu-lv successfully resized.lvm> exit
Exiting.
root@ubuntu:~# resize2fs /dev/mapper/ubuntu--vg-ubuntu--lv resize2fs 1.44.1 (24-Mar-2018) Filesystem at /dev/mapper/ubuntu--vg-ubuntu--lv is mounted on /; on-line resizing required old_desc_blocks = 1, new_desc_blocks = 13 The filesystem on /dev/mapper/ubuntu--vg-ubuntu--lv is now 25951232 (4k) blocks long. root@ubuntu:~# df -h Filesystem Size Used Avail Use% Mounted on udev 967M 0 967M 0% /dev tmpfs 200M 1.1M 199M 1% /run /dev/mapper/ubuntu--vg-ubuntu--lv 98G 3.4G 91G 4% / tmpfs 997M 0 997M 0% /dev/shm tmpfs 5.0M 0 5.0M 0% /run/lock tmpfs 997M 0 997M 0% /sys/fs/cgroup /dev/loop0 90M 90M 0 100% /snap/core/7713 /dev/loop1 90M 90M 0 100% /snap/core/7917 /dev/sda2 976M 222M 688M 25% /boot tmpfs 200M 0 200M 0% /run/user/1000root@ubuntu:~#
Posted on October 16, 2019 by Willem and filed under Linux , Tips'n Tricks and tagged ubuntu disk space lvm.
1 Likes
Share
Comment
CISCO ISE V2.6 AND GOOGLE CHROMEOS While playing around with the new Cisco Identity Service Engine (ISE) v2.6 (patch2) I stumbled upon a security feature while testing Wireless 802.1x access with an Acer Chromebook (ChromeOS v75.0.3770.144). When connecting to the 802.1x enabled SSID the connection failed, while other devices (Windows 10, Apple iOS and MacOS) connected just fine. The problem is the client EAP handshake and usually this relates to untrusted server certificates. This happens to me a lot since I use different RADIUS services for my testing SSID’s. So after clearing the SSID settings (forget) on the Chromebook it should work, but it didn’t. The logging showed that the EAP handshake failed because the client didn’t offer a suitable cipher to the ISE server. Turns out that Cisco ISE v2.6 has SHA1 disabled by default, and you need to enable it in: ADMINISTRATION -> SYSTEM -> SETTINGS -> SECURITY SETTINGS With the setting ‘_Allow SHA1 Ciphers_’, and ‘_Allow only TLS_RSA_WITH_AES_128_CBC_SHA_’ the Chromebook was able to connect to the 802.1x enabled SSID using old/depricated ciphers. Now I wonder why the Chromebook still uses SHA1 based ciphers for secure communications, since Google Chrome started to abandon SHA1 as one of the first browsers…. Even installing the ‘_Powerwash for added security_’ feature in ChromeOS didn’t enable or add stronger ciphers on the Chromebook. Posted on July 31, 2019 by Willem and filed under Tips'n Tricks , Security and tagged Cisco ISE Chromebook ChromeOS SHA1 cipher v2.6 802.1x Identity Services Engine.
2 Likes
Share
Comment
UPDATE PYTHON NETADDR OUI DATABASE For a small project I needed to validate ~1500 MAC addresses on validity and their vendor Organizational Unique Identifier id (OUI). So a bit of Python scripting was in order. I used a regular expression for basic MAC address validation, and the _netaddr_ module to check the OUI of the MAC Address. A simple example of the code is shown below #!/usr/bin/env python3 import netaddr as naimport re
_mac = '88-E9-FE-1F-65-7D' if re.match('{2}(?){2}(\\1{2}){4}$', _mac.lower()): print(f'{_mac} - {na.EUI(_mac).oui.registration().org}') Checking this MAC address online gives anormal result.
Python (or specifically netaddr) not so much, so there some work to be done. The error clearly shows that the OUI for that MAC address is not registered (in netaddr’s local database). The problem is that the OUI ‘database’ from _netaddr_ is (extremely) out-dated, so recently assigned OUI’s are not available, and result in Python script errors. Unfortunatelly, the _netaddr_ documentation doesn’t give any hint on how to update this database. Some searching on the local filesystem showed that there is a _oui.txt_ file within the directory structure of _netaddr_ (which in my case can be seen in the error shown above). The latest oui.txt (~0.5MB larger than the _netaddr_ version) can be downloaded @ IEEE (the organization were hardware vendors can request new OUI’s). The file location is: http://standards-oui.ieee.org/oui.txt. I downloaded the file and replaced the original _netaddr_ version. Running the code again gave no solution, since I got the same error. So back to the drawing board. In the same directory as the _oui.txt_ is a file called _oui.idx_. This file contains the decimal value of the OUI, and an offset. It turns out that the netaddr codeused this idx file to quickly skip to the actual vendor information in the oui.txt file. And since my idx file was based on the old oui.txt the vendor could still not be found. The idx file cannot be found on the internet. It’s not something IEEE provides. It’s a file generated from the information in the_oui.txt_ file.
Solution: In the _netaddr_ directory where the _oui.txt_ and _oui.idx_ is located is a _ieee.py_ script. Run that script, and it creates a new idx file based on the _oui.txt_ file in that directory (as shown in the following example). myhost:eui myname$ pwd /Library/Frameworks/Python.framework/Versions/3.7/lib/python3.7/site-packages/netaddr/eui myhost:eui myname$ ls -latotal 12856
drwxr-xr-x 9 myname admin 288 Jan 26 13:37 . drwxr-xr-x 11 myname admin 352 Jan 26 13:37 .. -rw-r--r-- 1 myname admin 24990 Jan 26 13:37 __init__.py drwxr-xr-x 4 myname admin 128 Jan 26 13:37 __pycache__ -rw-r--r-- 1 myname admin 95467 Jan 26 13:37 iab.idx -rw-r--r-- 1 myname admin 2453271 Jan 26 13:37 iab.txt -rw-r--r-- 1 myname admin 9500 Jan 26 13:37 ieee.py -rw-r--r-- 1 myname admin 419098 Jan 26 13:37 oui.idx -rw-r--r-- 1 myname admin 3566144 Jan 26 13:37 oui.txt myhost:eui myname$ curl http://standards-oui.ieee.org/oui.txt --output oui.txt % Total % Received % Xferd Average Speed Time Time Time Current Dload Upload Total Spent Left Speed 100 4039k 100 4039k 0 0 370k 0 0:00:10 0:00:10 --:--:-- 437k myhost:eui myname$ python3 ieee.py myhost:eui myname$ ls -latotal 14336
drwxr-xr-x 9 myname admin 288 Jan 26 13:37 . drwxr-xr-x 11 myname admin 352 Jan 26 13:37 .. -rw-r--r-- 1 myname admin 24990 Jan 26 13:37 __init__.py drwxr-xr-x 4 myname admin 128 Jan 26 13:37 __pycache__ -rw-r--r-- 1 myname admin 95467 May 10 12:14 iab.idx -rw-r--r-- 1 myname admin 2453271 Jan 26 13:37 iab.txt -rw-r--r-- 1 myname admin 9500 Jan 26 13:37 ieee.py -rw-r--r-- 1 myname admin 485973 May 10 12:14 oui.idx -rw-r--r-- 1 myname admin 4136058 May 10 12:14 oui.txtmyhost:eui myname$
After that the output of my script was the following: /usr/local/bin/python3.7 /Volumes/Python_Scripts/test.py 88-E9-FE-1F-65-7D - Apple, Inc. Process finished with exit code 0 Posted on May 10, 2019 by Willem and filed under Programming , Annoying and tagged netaddr python3OUI MAC Address .
3 Likes
Share
1 Comment
INSTALL CISCO IDENTITY SERVICES ENGINE V2.4 FROM USB The Cisco Identity Service Engine (ISE) is a NAC solution used for accessing the network. The version (while writing this post) is v2.4. For a new implementation of Cisco ISE I had to re-image 2 SNS-3595 appliances with the latest software. This can be done in various ways;*
Write the ISE iso to USB and boot / install from the USB flash-drive*
Use the JAVA/HTML5 KVM option through the CICM interface*
Hookup a USB DVD player with a dual-layer DVD containing the appropriate ISO file The preferred option is the USB flash-drive, since it’s the fastest, but only if you are able to boot from USB….. After trying several USB flash drives with the tool recommended in the Cisco manual I gave up. No way that the Boot menu saw the USB flash drive. So after wasting several hours doing that I opted for the KVM install method.Read more …
Posted on February 4, 2019 by Willem and filed under Tips'n Tricks , Software , Annoying and tagged Cisco ISE Identity Services Engine Rufus Fedora LiveUSB CreatorUEFI SNS-3595 .
2 Likes
Share
2 Comments
MY RADIO 2 TOP 2000 LIST FOR 2018 The following spotify playlist was submitted to the Top 2000 of NPORadio 2 :
Posted on December 6, 2018 by Willemand tagged Top2000
radio2 .
1 Likes
Share
Comment
WAKING UP INSIDE A CAMERA OBSCURA This weekend I woke up inside an actual camera obscura . Our (hotel) bedroom had Velux roof window which was minimally opened. The tiny openings on the lower side of the window projected the neighboring scenery on our (white) bedroom walls. Camera Obscura Scene (stitch of multiple photos)" data-lightbox-theme="dark" id="yui_3_17_2_1_1574299641108_186"> Camera Obscura Scene (stitch of multiple photos) The smaller the hole, the sharper the projected image is. You can even see the beer crates in front of the neighboring house. Rotated photo showing the beer crates" id="yui_3_17_2_1_1574299641108_212"> Rotated photo showing the beer crates All photos were taken handheld from the bed at ISO30.000 (or higher), so there is wee bit of noise. The photos also show the bed, door-handle and a radiator in the room. Posted on July 9, 2018 by Willem and filed under Personal , Photography and tagged Camera Obscura.
2 Likes
Share
Comment
JUNIPER SRX, VIRTUAL ROUTERS, AND SNMPV3 In this continuing story about Junos and virtual routers an episodeabout SNMPv3.
A simple SNMPv3 config for Junos would be the following: set snmp v3 usm local-engine user authpriv authentication-md5 authentication-password My_Password_01 set snmp v3 usm local-engine user authpriv privacy-aes128 privacy-password My_Password_02 set snmp v3 vacm security-to-group security-model usm security-name v3test group v3test set snmp v3 vacm security-to-group security-model usm security-name authpriv group v3test set snmp v3 vacm access group v3test default-context-prefix security-model any security-level authentication read-view v3testview set snmp v3 vacm access group v3test default-context-prefix security-model any security-level authentication write-view v3testview set snmp v3 vacm access group v3test default-context-prefix security-model any security-level authentication notify-view v3testview set snmp v3 vacm access group v3test default-context-prefix security-model any security-level privacy read-view v3testview set snmp v3 vacm access group v3test default-context-prefix security-model any security-level privacy write-view v3testview set snmp v3 vacm access group v3test default-context-prefix security-model any security-level privacy notify-view v3testview set snmp v3 snmp-community v3test security-name v3test set snmp view v3testview oid system include set snmp view v3testview oid .1 include Authenticating with the correct credentials (U: authpriv, P: My_Password_01) will give results in a single (default) virtualrouter.
Using this config in a multiple VR environment will result in Authentication and/or authorization errors. Reason being the not using the root/single VR configuration. Adding some details to the config, AND altering the actual SNMPv3 query will solve that. set snmp v3 usm local-engine user authpriv authentication-md5 authentication-password My_Password_01 set snmp v3 usm local-engine user authpriv privacy-aes128 privacy-password My_Password_02 set snmp v3 vacm security-to-group security-model usm security-name authpriv group v3test set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level authentication read-view v3testview set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level authentication write-view v3testview set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level authentication notify-view v3testview set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level privacy read-view v3testview set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level privacy write-view v3testview set snmp v3 vacm access group v3test context-prefix DEFAULT security-model any security-level privacy notify-view v3testview set snmp v3 snmp-community v3test security-name v3test set snmp view v3testview oid system include set snmp view v3testview oid .1 include set snmp routing-instance-access access-list DEFAULT The main differences are: * _context-prefix.
1 Likes
Share
Comment
Source
Blog
Newer / Older
REDELIJKHEID.COM - Copyright 1999-2015All Rights Reserved
POWERED BY SQUARESPACEDetails
3
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0