Are you over 18 and want to see adult content?
More Annotations
Salt & Honey Catering & Events | San Francisco Bay Area Catering & Events
Are you over 18 and want to see adult content?
Запчасти для бытовой техники | Интернет-магазин Sambt.ru
Are you over 18 and want to see adult content?

پیشگام نگار | فروشگاه اینترنتی محصولات آرایشی بهداشتی - فروشگاه آرایشی بهداشتی پیشگام نگار
Are you over 18 and want to see adult content?
Home page of History.org : The Colonial Williamsburg Foundation's official History and Citizenship site
Are you over 18 and want to see adult content?

Water Sports Equipment Online | Boatworld UK
Are you over 18 and want to see adult content?
Favourite Annotations
فروشگاه اینترنتی کاردستی | ماگ ، پیکسل ، قاب موبایل ، کیف و دفترهای فانتزی
Are you over 18 and want to see adult content?
MYLÉ VAPOR Shop | Vape E-Cig, Flavor Pods, Starter Kits
Are you over 18 and want to see adult content?
CHARONA II | The changing role of NARICs
Are you over 18 and want to see adult content?

Ranking Lekarzy - oceń swojego lekarza, poznaj opinie innych
Are you over 18 and want to see adult content?
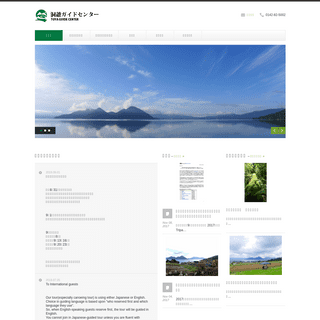
洞爺ガイドセンター カヌーツアーや中島ネイチャーツアーで洞爺湖の自然をご案内します。-HOME- www.toya-guide.com
Are you over 18 and want to see adult content?

A complete backup of planetgates.myshopify.com
Are you over 18 and want to see adult content?
Text
) now
ADVANTAGES OF SALES FUNNEL Before you know the advantages of what sales funnel are, you must have a clear idea of what it is. The idea of sales funnel is not very complex but rather simple when we boil down the definition. It could be understood simply as a visual representation of the journey of the customer. The journey implies the processes HOW TO USE THE TRACEROUTE COMMAND IN FAST WAY How to Use the Traceroute Command in Fast Way?. Traceroute is a command which can show you the path a packet of information takes from your computer to one you specify.It will list all the routers it passes through until it reaches its destination, or fails to and isdiscarded.
FIND OUT WHICH USB DEVICES HAVE BEEN USED ON YOUR PC You can easily find out the traces of used USB drive with USBDeview tool by Nirosoft. USBDeview is a small utility that lists all USB devices that currently connected to your computer, as well as all USB devices that you previously used. For each USB device, extended information is displayed: Device name/description, device type, serialnumber
HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilities DOWNLOAD CRACKS, KEYGENS, VIEW SERIAL NUMBERS FOR ANY Today i am going show you number of sites those are providing cracks and Serial numbers. 1. www.keygenguru.com /. keygenguru.com is the best way to find cracks, serial numbers, keygens. 2. www.serials.be. Serials.BE is a new international sharing project. Serials.BE is not commercial project and doesn`t give any profit to anybody. HOW TO COPY FASTER IN WINDOWS How to copy faster in windows :- Copying files to one drive to other drive or flash drive is one of most used work on Windows. However with windows 7 & 8, Microsoft improve the copying speed. But still if you are not happy with copy, then try out this tips. it STOP UNWANTED EMAIL WITH SPAMBLOCKER IN WATCHGUARD Stop Unwanted Email with SpamBlocker in WatchGuard :- Unwanted email, also known as spam, fills the average Inbox at an amazing rate. A large volume of spam decreases the bandwidth available to other applications, degrades employee productivity, and wastes network resources. The WatchGuard® spamBlocker™ service uses SEARCH MULTIPLE TORRENT ENGINES AT ONCE Search Multiple Torrent Engines At Once :- Torrent is one of the most popular method of file sharing over internet.However it,s very hectic to search each torrent sites for your favorite software or movies. Today i am going to show you How you can search multiple torrent engine at once with free available tools and HOW TO FILL A PART OF AN IMAGE IN PHOTOSHOP How to Fill a Part of an Image in Photoshop :-Most of the time when we are taking the picture, it,s some part are not complete. Like in my previous article Creating Warped Text In Photoshop when i write the article my canvas size is not going fit for write. so i decided to write How to Fill a Part of an Image in Photoshop . Open your Picture in Photoshop and make one duplicate layer of copy HOW TO CRACK A WPA2-PSK PASSWORD WITH WINDOWS First you need to be capture the Wpa2, four-way handsake with CommView. Open commView and click on the Start option. then click on the capture option to start the capture. now it will show you all available AP, Now click on the Tools > Select the Node Reassoication option ( if Node Rassociation is not working , then use WiFi Alfa card) now
ADVANTAGES OF SALES FUNNEL Before you know the advantages of what sales funnel are, you must have a clear idea of what it is. The idea of sales funnel is not very complex but rather simple when we boil down the definition. It could be understood simply as a visual representation of the journey of the customer. The journey implies the processes HOW TO USE THE TRACEROUTE COMMAND IN FAST WAY How to Use the Traceroute Command in Fast Way?. Traceroute is a command which can show you the path a packet of information takes from your computer to one you specify.It will list all the routers it passes through until it reaches its destination, or fails to and isdiscarded.
FIND OUT WHICH USB DEVICES HAVE BEEN USED ON YOUR PC You can easily find out the traces of used USB drive with USBDeview tool by Nirosoft. USBDeview is a small utility that lists all USB devices that currently connected to your computer, as well as all USB devices that you previously used. For each USB device, extended information is displayed: Device name/description, device type, serialnumber
HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilities 10 TIPS FOR BUYING PRODUCTS ONLINE This is perhaps the most important when you are shopping online. Always trust what your instincts say. If you have even the slightest doubt, it is better to be safe than sorry. If the offer is too good to be true, such as a price that is unbelievably low, this is an obvious sign that you need to be cautious. SEARCH MULTIPLE TORRENT ENGINES AT ONCE Search Multiple Torrent Engines At Once :- Torrent is one of the most popular method of file sharing over internet.However it,s very hectic to search each torrent sites for your favorite software or movies. Today i am going to show you How you can search multiple torrent engine at once with free available tools and HOW TO INSTALL CHECKPOINT GAIA ON VMWARE How to install checkpoint gaia on vmware :- In Greek mythology Gaia was the mother goddess who presided over the earth. Check Point GAiA is the unified cutting-edge secure operating system for all Check Point Appliances, open servers and virtualized gateways. GAiA combines the best features from IPSO and HOW TO USE THE TRACEROUTE COMMAND IN FAST WAY How to Use the Traceroute Command in Fast Way?. Traceroute is a command which can show you the path a packet of information takes from your computer to one you specify.It will list all the routers it passes through until it reaches its destination, or fails to and isdiscarded.
HOW TO CREATE A DATABASE IN FILEMAKER PRO How to create a Database in Filemaker Pro :- If you are looking for database for Contact Management, Asset management, Document inventory, Expense report , Employee database , school attendance etc.. and you don’t have knowledge about database program then file maker pro program will be the best solution for it. HOW TO INSTALL WINDOWS PROGRAMS IN LINUX MINT How to install windows programs in Linux Mint :- Ubuntu and Linux Mint are two of the most popular desktop Linux distributions at the moment. Linux Mint is based on Ubuntu. In these days, Mint seems to offer more configurability than Ubuntu out-of-the-box. Whereas Ubuntu’s Unity only includes a few options in the HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilities HOW TO DETECT KEYLOGGER ON YOUR PC How to detect keylogger on your PC :-Keylogger is a program that is used by Hackers to gain access to your keystrokes. In other words Hacker is able to see what you are typing on the keyboard, even your Username and passwords and your important information from your HOW TO RESET DAMAGED OR CORRUPTED TCP/IP CONNECTION How to reset damaged or corrupted TCP/IP connection :- TCP / IP can sometimes become damaged or corrupted. One of the components of the Internet connection on your computer is a built-in set of instructions called TCP/IP. TCP/IP can sometimes become damaged or corrupted. If you cannot connect to the Internet and you HOW TO VIEW SYN-FLOOD ATTACK USING THE COMMAND PROMPT How to View SYN-Flood attack using the Command Prompt ? SYN Flood Attack :- An arriving SYN sends the “connection” into SYN-RCVD state It can stay in this state for quite a while, awaiting the acknowledgment of the SYN+ACK packet, and tying up memory For this reason, the number of connections for a given port in DOWNLOAD CRACKS, KEYGENS, VIEW SERIAL NUMBERS FOR ANY Today i am going show you number of sites those are providing cracks and Serial numbers. 1. www.keygenguru.com /. keygenguru.com is the best way to find cracks, serial numbers, keygens. 2. www.serials.be. Serials.BE is a new international sharing project. Serials.BE is not commercial project and doesn`t give any profit to anybody. HOW TO COPY FASTER IN WINDOWS How to copy faster in windows :- Copying files to one drive to other drive or flash drive is one of most used work on Windows. However with windows 7 & 8, Microsoft improve the copying speed. But still if you are not happy with copy, then try out this tips. it STOP UNWANTED EMAIL WITH SPAMBLOCKER IN WATCHGUARD Stop Unwanted Email with SpamBlocker in WatchGuard :- Unwanted email, also known as spam, fills the average Inbox at an amazing rate. A large volume of spam decreases the bandwidth available to other applications, degrades employee productivity, and wastes network resources. The WatchGuard® spamBlocker™ service uses HOW TO CRACK A WPA2-PSK PASSWORD WITH WINDOWS First you need to be capture the Wpa2, four-way handsake with CommView. Open commView and click on the Start option. then click on the capture option to start the capture. now it will show you all available AP, Now click on the Tools > Select the Node Reassoication option ( if Node Rassociation is not working , then use WiFi Alfa card) now
SEARCH MULTIPLE TORRENT ENGINES AT ONCE Search Multiple Torrent Engines At Once :- Torrent is one of the most popular method of file sharing over internet.However it,s very hectic to search each torrent sites for your favorite software or movies. Today i am going to show you How you can search multiple torrent engine at once with free available tools and HOW TO FILL A PART OF AN IMAGE IN PHOTOSHOP How to Fill a Part of an Image in Photoshop :-Most of the time when we are taking the picture, it,s some part are not complete. Like in my previous article Creating Warped Text In Photoshop when i write the article my canvas size is not going fit for write. so i decided to write How to Fill a Part of an Image in Photoshop . Open your Picture in Photoshop and make one duplicate layer of copy HOW TO CREATE A DATABASE IN FILEMAKER PRO How to create a Database in Filemaker Pro :- If you are looking for database for Contact Management, Asset management, Document inventory, Expense report , Employee database , school attendance etc.. and you don’t have knowledge about database program then file maker pro program will be the best solution for it. ADVANTAGES OF SALES FUNNEL Before you know the advantages of what sales funnel are, you must have a clear idea of what it is. The idea of sales funnel is not very complex but rather simple when we boil down the definition. It could be understood simply as a visual representation of the journey of the customer. The journey implies the processes HOW TO INSTALL CHECKPOINT GAIA ON VMWARE How to install checkpoint gaia on vmware :- In Greek mythology Gaia was the mother goddess who presided over the earth. Check Point GAiA is the unified cutting-edge secure operating system for all Check Point Appliances, open servers and virtualized gateways. GAiA combines the best features from IPSO and HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilities DOWNLOAD CRACKS, KEYGENS, VIEW SERIAL NUMBERS FOR ANY Today i am going show you number of sites those are providing cracks and Serial numbers. 1. www.keygenguru.com /. keygenguru.com is the best way to find cracks, serial numbers, keygens. 2. www.serials.be. Serials.BE is a new international sharing project. Serials.BE is not commercial project and doesn`t give any profit to anybody. HOW TO COPY FASTER IN WINDOWS How to copy faster in windows :- Copying files to one drive to other drive or flash drive is one of most used work on Windows. However with windows 7 & 8, Microsoft improve the copying speed. But still if you are not happy with copy, then try out this tips. it STOP UNWANTED EMAIL WITH SPAMBLOCKER IN WATCHGUARD Stop Unwanted Email with SpamBlocker in WatchGuard :- Unwanted email, also known as spam, fills the average Inbox at an amazing rate. A large volume of spam decreases the bandwidth available to other applications, degrades employee productivity, and wastes network resources. The WatchGuard® spamBlocker™ service uses HOW TO CRACK A WPA2-PSK PASSWORD WITH WINDOWS First you need to be capture the Wpa2, four-way handsake with CommView. Open commView and click on the Start option. then click on the capture option to start the capture. now it will show you all available AP, Now click on the Tools > Select the Node Reassoication option ( if Node Rassociation is not working , then use WiFi Alfa card) now
SEARCH MULTIPLE TORRENT ENGINES AT ONCE Search Multiple Torrent Engines At Once :- Torrent is one of the most popular method of file sharing over internet.However it,s very hectic to search each torrent sites for your favorite software or movies. Today i am going to show you How you can search multiple torrent engine at once with free available tools and HOW TO FILL A PART OF AN IMAGE IN PHOTOSHOP How to Fill a Part of an Image in Photoshop :-Most of the time when we are taking the picture, it,s some part are not complete. Like in my previous article Creating Warped Text In Photoshop when i write the article my canvas size is not going fit for write. so i decided to write How to Fill a Part of an Image in Photoshop . Open your Picture in Photoshop and make one duplicate layer of copy HOW TO CREATE A DATABASE IN FILEMAKER PRO How to create a Database in Filemaker Pro :- If you are looking for database for Contact Management, Asset management, Document inventory, Expense report , Employee database , school attendance etc.. and you don’t have knowledge about database program then file maker pro program will be the best solution for it. ADVANTAGES OF SALES FUNNEL Before you know the advantages of what sales funnel are, you must have a clear idea of what it is. The idea of sales funnel is not very complex but rather simple when we boil down the definition. It could be understood simply as a visual representation of the journey of the customer. The journey implies the processes HOW TO INSTALL CHECKPOINT GAIA ON VMWARE How to install checkpoint gaia on vmware :- In Greek mythology Gaia was the mother goddess who presided over the earth. Check Point GAiA is the unified cutting-edge secure operating system for all Check Point Appliances, open servers and virtualized gateways. GAiA combines the best features from IPSO and HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilitiesRUMY IT TIPS
How to Crack a Wpa2-Psk Password with Windows. Syed Balal Rumy - 5 August, 2013 34. It,s very common question on the internet to How tohack a
HACK WIRELESS ROUTER ADMIN PASSWORD WITH BACKTRACK OR KALI Hack Wireless Router Admin Password With Backtrack or Kali Linux Router administrator password is always important for it,s administration. However most the of the time when people forget their router administrator password they prefer to reset the router settings to default.but it,s not always good to reset your router to defaultsettings.
HOW TO INSTALL CHECKPOINT GAIA ON VMWARE How to install checkpoint gaia on vmware :- In Greek mythology Gaia was the mother goddess who presided over the earth. Check Point GAiA is the unified cutting-edge secure operating system for all Check Point Appliances, open servers and virtualized gateways. GAiA combines the best features from IPSO and WHAT IS A WEB APPLICATION FIREWALL What is a Web Application Firewall ? A Web application firewall protects Web servers from malicious traffic and blocks attempts to compromise the system. It prevents targeted attacks that include cross-site scripting, SQL injection, forceful browsing, cookiepoisoning and
HOW TO PERFORM A DOS ATTACK ON A WEBSITE (LOIC TOOL How to Perform a DOS attack on a Website (LOIC Tool)? DOS stand for Denial of Services is an attempt to make a machine or network resources unavailable for legitimate users.. What is LOIC Tool ? A LOIC (Low Orbit Ion Cannon) is one of the most powerful DOS attacking tools freely available.If you follow news related to hacking and security issues, you doubtless have been hearing about this tool HOW TO FIX USER IS OVER QUOTA ERROR IN OUTLOOK 1. In Microsoft Outlook :-. Navigate to File > Info > Account settings. Now click on the User account > More Settings > now under advanced > In the Delivery section “ Unchecked the Leave the message on the server or select 1 days “. It will take approx HOW TO ALLOW ICMP TRAFFIC THROUGH PFSENSE FIREWALL How to Allow ICMP traffic through pfsense firewall:-. pfSense is a free, open source customized distribution of FreeBSD tailored for use as a firewall and router. In addition to being a powerful, flexible firewalling and routing platform, it includes a long list of related features and a package system allowing further expandability without adding bloat and potential security vulnerabilities REASONS AS TO WHY THE CRYPTOCURRENCY IS REGARDED AS When you take a look at the blockchain technology, there are a lot of pros and cons that are associated with it. Along with the advantages, there are a lot of disadvantages as well, which people notice when it comes to Bitcoin technology, and some of them continuously focus on the downside of this particular trading. STOP CHROME HOGGING YOUR PC MEMORY Stop Chrome hogging your PC memory :- Everything you do in your browser uses up some of your PC's memory. Tabs,apps and add-ons all use memory, and if you have a lot of them open and running, your PC will slow down. Today i am going to show you Stop Chrome hogging your PC memory . 1. To identify the sites and FIND OUT WHICH USB DEVICES HAVE BEEN USED ON YOUR PC You can easily find out the traces of used USB drive with USBDeview tool by Nirosoft. USBDeview is a small utility that lists all USB devices that currently connected to your computer, as well as all USB devices that you previously used. For each USB device, extended information is displayed: Device name/description, device type, serialnumber
__
__ __
__ __
__
* Home
* Cisco
* BackTrack
* Windows
* Internet
* WordPress
* PhotoShop
__
Sign in
__
Welcome!Log into your accountyour username
your password
Forgot your password?__
Password recovery
Recover your passwordyour email
__
Search
__
Sign in
Welcome! Log into your accountyour username
your password
Forgot your password? Get helpPassword recovery
Recover your passwordyour email
A password will be e-mailed to you.RUMY IT TIPS
__
* Home
* Cisco
* BackTrack
* Windows
* Internet
* WordPress
* PhotoShop
__ __
TIPS ON SHOWING POTENTIAL EMPLOYERS THAT YOU ARE A TRUSTWORTHYEMPLOYEE
Syed Balal Rumy - 28 September,2020 0
Internet
Getting a job is not only about having the... HOW TO MAKE YOUR HOME QUIETER Syed Balal Rumy - 22 September,2020 0
Internet
We all want peace and quiet every once in... 3 REPERCUSSIONS OF THE INTERNET AND HOW TO DEAL WITH THEM Syed Balal Rumy - 18 September,2020 0
Internet
For the most part, the rise of the Internet... HOW TO GET THE MOST OUT OF MICROSOFT 365 Syed Balal Rumy - 14 September,2020 0
Internet
Like all large-scale, mass-market programs, Microsoft 365 is known... TOP 12 SOFTWARE TESTING ERRORS BEGINNERS MAKE & HOW TO AVOID... Syed Balal Rumy - 29 August,2020 0
Internet
Software testing is one of the most critical processes... WHY IS PRICE AUTOMATION A KEY FACTOR FOR SUCCESS IN AMAZON? Syed Balal Rumy - 29 August,2020 0
Internet
A common factor that online shoppers look for in...POPULAR POSTS
Internet
HOW TO CRACK A WPA2-PSK PASSWORD WITH WINDOWS Syed Balal Rumy - 5 August,2013 34
It,s very common question on the internet to How to hack a Facebook account password and how to hack a WiFi password. Even if... HIDE YOUR REAL IP LOCATION AND BROWSE ANONYMOUSLY31 May, 2013
MANAGE YOUR ANDROID PHONE FROM YOUR COMPUTER1 June, 2013
ENCRYPT YOUR WEB BROWSING WITH HTTPS EVERYWHERE28 May, 2013
SPEED UP YOUR INTERNET BROWSING WITH FASTEST AVAILABLE PUBLIC DNS4 June, 2013
SEND NOTES THAT WILL SELF-DESTRUCT AFTER BEING READ5 June, 2013
MATCH COLORS BETWEEN IMAGES IN PHOTOSHOP28 June, 2013
HOW TO TRACK ANY MAC ADDRESS GEOGRAPHICAL LOCATION15 June, 2013
SCAN YOUR LOCAL CONNECTED NETWORK WITH BACKTRACK26 May, 2013
AWESOME ARTICLES
HOW HACKERS GAIN ACCESS TO YOUR COMPUTER23 July, 2013
PROS OF INDOOR FOUNTAIN TECH IN THE HOME15 November, 2018
BENEFITS OF SAME DAY REPAIRS13 December, 2018
WHY BUY KRATOM FROM BUY KRATOM BULK THE USA?19 July, 2020
HOW TO DRIVE ORGANIC TRAFFIC TO YOUR E-COMMERCE STORE IN 202024 February, 2020
5 ECO-FRIENDLY MARKETING STRATEGIES THAT WORK23 January, 2019
HOW TO CREATE WORDLIST WITH CRUNCH IN KALI LINUX12 July, 2013
BEST FREE TOOLS TO SPEED-UP YOUR PC6 June, 2013
HOW TO ENABLE VIDEO STREAMING IN UTORRENT17 September, 2013
* Contact Us
� All Contents are Copyright to Rumy IT TipsDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0