Are you over 18 and want to see adult content?
More Annotations

A complete backup of f45challenge.com
Are you over 18 and want to see adult content?
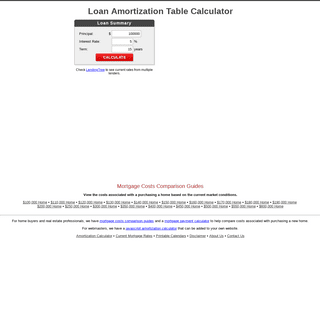
Loan Amortization Table Calculator
Are you over 18 and want to see adult content?

A complete backup of archivesofpathology.org
Are you over 18 and want to see adult content?
Erlebnis Bogensport - Bogenschießen deutschlandweit
Are you over 18 and want to see adult content?
CALCULO INTEGRAL
Are you over 18 and want to see adult content?

Nursery & Kindergarten children school
Are you over 18 and want to see adult content?
Favourite Annotations

Onward State | Penn State Blog by PSU Students | News, Features, and Opinion
Are you over 18 and want to see adult content?

Моётату - идеи для татуировок и значение символов
Are you over 18 and want to see adult content?

Software Battle - Technology magazine
Are you over 18 and want to see adult content?
Encuentros con la Verdad - Libreria Maranatha
Are you over 18 and want to see adult content?

Paragliding Holland: Professionele Paragliding Opleidingen
Are you over 18 and want to see adult content?

Salary Advance Loan|Instant Cash Loan India,Quick Credit|Online Loan
Are you over 18 and want to see adult content?
Virtual Nerd: Real math help for school and home
Are you over 18 and want to see adult content?

Stephen Walther | AngularJS/ASP.NET Web API/TypeScript
Are you over 18 and want to see adult content?
Text
comparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. AVG SECURITY SUIT: PROTECT WHAT MATTERS ON ANY DEVICES AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning prior to opening, search engine link evaluation for phishing, malware, and spyware, and administrative tools to manage the programs for individual users orfor networks.
SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. AVG SECURITY SUIT: PROTECT WHAT MATTERS ON ANY DEVICES AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning prior to opening, search engine link evaluation for phishing, malware, and spyware, and administrative tools to manage the programs for individual users orfor networks.
SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. GENERAL SECURITY TIPS FOR WINDOWS USERS · COMPUTER There are many safety features built into Windows. However, in this day and age, when technology grows rapidly and even school children have basic knowledge of computers, users have to be smart to protect their data and systems.Taking into account that aside from the basic use we now share data, work from locations other than the office, and have portable devices that are easily stolen, we HOW YOU CAN DEVELOP A UNIQUE AND STRONG PASSWORD FOR YOUR Here’s a question for you to ponder: when it comes to your internet security and privacy, do you know how important your email password is? Believe it or not, it’s the last defensive line to your securityand privacy.
HOW TO SAFELY BROWSE THE INTERNET USING BING · SECURITY The internet brought about many incredible social and economic developments. However, the medium is not risk-free. There is nothing like absolute security in the vast web of virtual world when you startbrowsing.
INTRODUCING WINDOWS HELLO: SAY GOODBYE TO USING PASSWORDS In March, Microsoft announced the launch of Windows Hello – a security feature which enables users to access their computers and devices running Windows 10 via the face recognition system, involving iris identification or fingerprint. HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWARE The continuous increase in the number of people who use the internet has given birth to a new brand of criminal, the cyber criminals, and they keep coming up with new and innovative ways to scam and steal from the internet user. As the population has become extremely dependent on the internet, from conducting business to buying groceries, a massive growth in cyber-criminal activities 6 MESSENGERS FOR IOS TO SAFEGUARD YOUR PRIVACY · PRIVACY Are you worried that your messages are being spied on and read by app developers? Are you using any of the following apps to substitute for SMS: WhatsApp, Hangouts, or Line?You might not appreciate them collecting your texts. HOW TO MANAGE YOUR CHILD'S IPAD SECURITY · KIDS & FAMILY Children grow fast and many have their own laptops, which are normally placed with a parental control that will prevent inappropriate content from showing up on a child’s machine. 9 BEST ANTIVIRUS SOFTWARE FOR 2017 TO PROTECT YOUR WINDOWS No one wants to deal with computer viruses and malware.They can slow down your system, change data files and cause your system to misbehave. Chances are you came across this online security article because you want to know the best antivirus software for 2017 available right now. SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. MAKE YOUR ZIP ARCHIVE CONFIDENTIAL HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. MAKE YOUR ZIP ARCHIVE CONFIDENTIAL HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet 12 STEPS TO SECURE YOUR PC AFTER A FRESH WINDOWS When you have to install or reinstall Windows operating system it is a laborious task that takes far too much time, and none of us like to follow through all the steps of the process. HOW YOU CAN DEVELOP A UNIQUE AND STRONG PASSWORD FOR YOUR Malware is software that is intentionally embedded with worms, spyware, adware, viruses, Trojans, and other malicious things. Money is the reason for almost all WHY YOU SHOULD USE A PASSWORD MANAGER · TIPS & TRICKS AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning 5 IMPORTANT TIPS THAT WILL HELP KEEP YOUR DIGITAL Two Egyptian security experts, Ahmed Aboul-Ela and Ibrahim M. El-Sayed, recently identified an intriguing comment authentication bugon YouTube.
HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWARE The continuous increase in the number of people who use the internet has given birth to a new brand of criminal, the cyber criminals, and they keep coming up with new and innovative ways to scam and steal from the internet user. As the population has become extremely dependent on the internet, from conducting business to buying groceries, a massive growth in cyber-criminal activities DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. ARE CLOUD SERVICES REALLY SECURE? REALITY CHECK ON ICLOUD If you are one among those people easily influenced by screaming headlines about hacked accounts and compromised passwords involving the cloud storage, you BYOD (BRING YOUR OWN DEVICE) MODEL REMAINS A BIG QUESTION Even as some businesses are adopting the Bring Your Own Device (BYOD) model in work places, you may also be thinking on whether to join the bandwagon by allowing employees to bring devices like smartphones, tablets and wearables to the office. 9 PRIVACY TIPS FOR POKEMON GO · PRIVACY · SAFETYHOLIC Despite the fact that it’s not available worldwide, just a few days after the launch, Pokemon GO has outnumbered Twitter for active users. The app lured countless numbers of people into exploring the outside while playing on their smartphones, which has led to numerous stories of unusual encounters, some that are heartwarming, and some that arescary.
SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet WHAT IS VPN AND IS IT REALLY NECESSARY FOR PRIVATE What is VPN? A VPN, aka Virtual Private Network, is technology that provides people with a secure connection through a public network.This could be
HOW TO SAFELY BROWSE THE INTERNET USING BING · SECURITY The internet brought about many incredible social and economic developments. However, the medium is not risk-free. There is nothing like absolute security in the vast web of virtual world when you startbrowsing.
HOW YOU CAN DEVELOP A UNIQUE AND STRONG PASSWORD FOR YOUR Here’s a question for you to ponder: when it comes to your internet security and privacy, do you know how important your email password is? Believe it or not, it’s the last defensive line to your securityand privacy.
HOW TO DOWNLOAD FILES FROM THE INTERNET SAFELY · COMPUTER Unless you have been living underneath a rock for the past 10 years, there is a good chance you've downloaded a file from the internet before. There is als WHY YOU SHOULD USE A PASSWORD MANAGER · TIPS & TRICKS AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning BYOD (BRING YOUR OWN DEVICE) MODEL REMAINS A BIG QUESTION Even as some businesses are adopting the Bring Your Own Device (BYOD) model in work places, you may also be thinking on whether to join the bandwagon by allowing employees to bring devices like smartphones, tablets and wearables to the office. DISPOSING OF YOUR OLD PRINTER? MAKE SURE THERE’S NO DATA In an era when data security on smartphones and computers are the prime focus, we often forget other devices which also hold sensitive data. For instance, have you come across any of your friends talking about the need for getting rid of sensitive data from their oldprinters?
HOW TO COMPLETELY WIPE ALL PERSONAL DATA OFF YOUR ANDROID Last year research from security giant Avast discovered that the factory reset option in Android devices do not wipe the personal user data off the phone entirely and can be retrieved by hackers.. The research team experimented with used Android devices and within a short time, they were able to retrieve thousands of photos that belonged to the previous users, hundreds of emails, texts and 6 MESSENGERS FOR IOS TO SAFEGUARD YOUR PRIVACY · PRIVACY Are you worried that your messages are being spied on and read by app developers? Are you using any of the following apps to substitute for SMS: WhatsApp, Hangouts, or Line?You might not appreciate them collecting your texts. SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a MAKE YOUR ZIP ARCHIVE CONFIDENTIAL HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
TOP 30 INTERNET & TECH TERMS FOR DUMMIES With so much information these days and so busy life, it’s only natural not to know lots of things. There’s always more to learn, as every passing second adds to the complexity and vastness of the information available on the internet. TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED The threat of ransomware has been increasing at alarming rates, with even more bad news coming. And it seems that these campaigns have become more simple for hackers to carry out, thanks to Tox Ransomware. WHY YOU SHOULD USE A PASSWORD MANAGER · TIPS & TRICKS AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a MAKE YOUR ZIP ARCHIVE CONFIDENTIAL HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
TOP 30 INTERNET & TECH TERMS FOR DUMMIES With so much information these days and so busy life, it’s only natural not to know lots of things. There’s always more to learn, as every passing second adds to the complexity and vastness of the information available on the internet. TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED The threat of ransomware has been increasing at alarming rates, with even more bad news coming. And it seems that these campaigns have become more simple for hackers to carry out, thanks to Tox Ransomware. WHY YOU SHOULD USE A PASSWORD MANAGER · TIPS & TRICKS AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet 12 STEPS TO SECURE YOUR PC AFTER A FRESH WINDOWS When you have to install or reinstall Windows operating system it is a laborious task that takes far too much time, and none of us like to follow through all the steps of the process. HOW YOU CAN DEVELOP A UNIQUE AND STRONG PASSWORD FOR YOUR Malware is software that is intentionally embedded with worms, spyware, adware, viruses, Trojans, and other malicious things. Money is the reason for almost all WARNING SIGNS YOUR COMPUTER IS INFECTED · COMPUTER A common fear of the average everyday computer user is that they might attract or become infected with malware.The normal operation of a computer is affected by malware in many ways, sometimes it doesn’t reveal its existence at all. HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWARE The continuous increase in the number of people who use the internet has given birth to a new brand of criminal, the cyber criminals, and they keep coming up with new and innovative ways to scam and steal from the internet user. As the population has become extremely dependent on the internet, from conducting business to buying groceries, a massive growth in cyber-criminal activities BYOD (BRING YOUR OWN DEVICE) MODEL REMAINS A BIG QUESTION Even as some businesses are adopting the Bring Your Own Device (BYOD) model in work places, you may also be thinking on whether to join the bandwagon by allowing employees to bring devices like smartphones, tablets and wearables to the office. DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. ARE CLOUD SERVICES REALLY SECURE? REALITY CHECK ON ICLOUD If you are one among those people easily influenced by screaming headlines about hacked accounts and compromised passwords involving the cloud storage, you HOW TO AVOID EMAIL PROBLEMS AND KEEP YOURSELF PROTECTED Email accounts have recently made the news again, thanks to Hillary Clinton’s fateful choice to use her personal email account to conduct official government business. Personal and business should never be mixed and this is sound advice when it comes to setting up your email accounts. DISPOSING OF YOUR OLD PRINTER? MAKE SURE THERE’S NO DATA In an era when data security on smartphones and computers are the prime focus, we often forget other devices which also hold sensitive data. For instance, have you come across any of your friends talking about the need for getting rid of sensitive data from their oldprinters?
SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE Latest computer security news, internet security tips, best antivirus software reviews, best VPN and free VPN reviews, best antivirusescomparisons.
20 SITES TO HIDE YOUR IDENTITY AND SEND EMAILS ANONYMOUSLYAUTHOR:FRANK MURO
There are a variety of sites that you can use in order to send anonymous emails. While there are plenty of free email services, including Yahoo Mail and Gmail, it’s our privacy and our digital right to send email anonymously, should we choose to do so. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE · TIPS It is very easy for you to get comfortable with sharing things within your friend networks online. However, between public Wi-Fi networks and social media, you may not actually know just how much you could be sharing with a total stranger.. On Facebook, Twitter, and Instagram, your location updates could actually be a security concern, especially if you happen to be posting them from a TOX - FREE RANSOMWARE SERVICE · COMPUTER, FEATURED Thanks to Tox Ransomware, non-tech users can now easily threaten others with ransomware. It was developed by an anonymous web hacker so that anyone could set up a virus for free. That’s right! Tox is free for everyone to use. The way hackers make money is by taking a 20% cut from any successful campaigns users carry out. HOW TO MAKE UNBREAKABLE PASSWORD · SECURITY, TIPS & TRICKS It is only natural that we have an unbreakable password to safeguard sensitive information as most of the data are now stored online. In the near future, we will be using not just passwords to keep our personal information. TOP 30 INTERNET & TECH TERMS FOR DUMMIES 3. Broadband connection. Broadband connection is one of the contemporary tech terms that people often encounter online. A broadband connection is a high-speed data transmission wherein single cables carry a huge data amount at once. Cable modems and DSL modems are the most popular forms of internet broadband connections. 5 MOBILE ENCRYPTION TOOLS TO HELP PROTECT YOUR PHONE AND Did you know that most internet traffic is actually being encrypted? Specifically speaking, 70% of it globally. Although right now, encryption levels have dropped lower, at 60%, at least for the mobile internet. Normally, encryption is done at the discretion of thecompany that is
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL DISABLING SYSTEM INTEGRITY PROTECTION ON MAC AND WHY IT’S The Mac OS X 10.11 El Capitan is responsible for protecting system files and processes using the latest feature called System Integrity Protection or SIP, a kernel-level feature limiting what the “root” account is able to do.. This is an excellent security feature and there are few people, including developers and power users, that tamper with it — you should always leave it enabled. SAFE BROWSING: HOW TO SURF THE WEB SECURELY AND PROTECT The internet is full of many great things and can be an excellent source of information. Sadly, just like in the pre-internet world, there are those who misuse it and are out to steal people’s personal information.Safe Browsing is a feature that Internet WHAT IS VPN AND IS IT REALLY NECESSARY FOR PRIVATE What is VPN? A VPN, aka Virtual Private Network, is technology that provides people with a secure connection through a public network.This could be
HOW TO SAFELY BROWSE THE INTERNET USING BING · SECURITY The internet brought about many incredible social and economic developments. However, the medium is not risk-free. There is nothing like absolute security in the vast web of virtual world when you startbrowsing.
HOW YOU CAN DEVELOP A UNIQUE AND STRONG PASSWORD FOR YOUR Here’s a question for you to ponder: when it comes to your internet security and privacy, do you know how important your email password is? Believe it or not, it’s the last defensive line to your securityand privacy.
HOW TO DOWNLOAD FILES FROM THE INTERNET SAFELY · COMPUTER Unless you have been living underneath a rock for the past 10 years, there is a good chance you've downloaded a file from the internet before. There is als WHY YOU SHOULD USE A PASSWORD MANAGER · TIPS & TRICKS AVG is a Dutch software company that specializes in security and protection of individuals’ and companies’ information by providing antivirus, spyware protection, link scanning BYOD (BRING YOUR OWN DEVICE) MODEL REMAINS A BIG QUESTION Even as some businesses are adopting the Bring Your Own Device (BYOD) model in work places, you may also be thinking on whether to join the bandwagon by allowing employees to bring devices like smartphones, tablets and wearables to the office. DISPOSING OF YOUR OLD PRINTER? MAKE SURE THERE’S NO DATA In an era when data security on smartphones and computers are the prime focus, we often forget other devices which also hold sensitive data. For instance, have you come across any of your friends talking about the need for getting rid of sensitive data from their oldprinters?
HOW TO COMPLETELY WIPE ALL PERSONAL DATA OFF YOUR ANDROID Last year research from security giant Avast discovered that the factory reset option in Android devices do not wipe the personal user data off the phone entirely and can be retrieved by hackers.. The research team experimented with used Android devices and within a short time, they were able to retrieve thousands of photos that belonged to the previous users, hundreds of emails, texts and 6 MESSENGERS FOR IOS TO SAFEGUARD YOUR PRIVACY · PRIVACY Are you worried that your messages are being spied on and read by app developers? Are you using any of the following apps to substitute for SMS: WhatsApp, Hangouts, or Line?You might not appreciate them collecting your texts.__
__
* All__
* Featured
* Security__
* Computer
* Data & Storage
* Mobile
* Web & Email
* Privacy__
* Kids & Family Safety* Social Media
* Tips & Tricks
* Spotlight
__
Search
__
Sign in
Welcome! Log into your accountyour username
your password
Forgot your password? Get help Create an accountCreate an account
Welcome! Register for an accountyour email
your username
A password will be e-mailed to you.Password recovery
Recover your passwordyour email
A password will be e-mailed to you.__
* All__
* Featured
* Security__
*
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL – ON EACH OS HOW CAN YOU FIND A SUITABLE ANTIVIRUS SOLUTION WHAT SHOULD YOU DO IF YOUR EMAIL IS COMPROMISED HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWARE GIVE YOUR ANTIVIRUS A REAL LIFE CRASH TESTAll Computer
Data & Storage
Mobile
Web & Email
____
* Privacy__
*
YOU MAY NEED TO GIVE UP YOUR SOCIAL MEDIA PASSWORD TO ENTER THE US MEET VERO, A NO-ADS SOCIAL NETWORK LAUNCHED BY A BILLIONAIRE WHAT PARENTS SHOULD KNOW ABOUT MUSICAL.LY GOOGLE IS JUST ONE STEP BEHIND APPLE: FAMILY SHARING IS LAUNCHED WHAT EVERY PARENT SHOULD KNOW ABOUT FINSTA/SPAM ACCOUNTS All Kids & Family SafetySocial
Media
____
* Tips & Tricks__
*
8 CYBER SECURITY FACTS THAT AFFECT YOUR ONLINE SAFETY 13 TOP SECURITY TIPS FOR WINDOWS IN 2017 15 TIPS TO HELP YOU MAKE A RELIABLE AND STRONG PASSWORD IN 2017 WHY YOU SHOULD USE A PASSWORD MANAGER ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINE____
* Spotlight__
*
9 BEST ANTIVIRUS SOFTWARE FOR 2017 TO PROTECT YOUR WINDOWS 10 PC THE ULTIMATE LIST OF 13 BEST PASSWORD MANAGERS YOU CAN RELY ON IN 2017 CYBERGHOST: RELIABLE VPN THAT WILL PROTECT YOUR PRIVACY AVIRA FREE ANTIVIRUS REVIEW SPEED UP YOUR MAC WITH CLEANMYMAC 3 FROM MACPAW____
__ __
SAFETYHOLIC. INTERNET SECURITY & PRIVACY ONLINE 8 CYBER SECURITY FACTS THAT AFFECT YOUR ONLINE SAFETY Bart Wallis - Mar 27,2017
0
13 TOP SECURITY TIPS FOR WINDOWS IN 2017 Alma Perry - Nov 22, 20160
15 TIPS TO HELP YOU MAKE A RELIABLE AND STRONG PASSWORD IN 2017 Bart Wallis - Oct 31,2016
0
WHY YOU SHOULD USE A PASSWORD MANAGERTerry Strickland -
Aug 18, 2016
0
ONLINE SAFETY TIPS: THINGS NOT TO DO ONLINETerry Strickland -
Aug 10, 2016
0
SECURITY
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL – ON EACH OS Clarence Busby - Sep14, 2017
0
Normally, the Zip files are password protected. However, the conventional Zip encryption system is very weak and might not be suitable if you are... HOW CAN YOU FIND A SUITABLE ANTIVIRUS SOLUTIONAug 30, 2017
WHAT SHOULD YOU DO IF YOUR EMAIL IS COMPROMISEDAug 16, 2017
HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWAREAug 2, 2017
GIVE YOUR ANTIVIRUS A REAL LIFE CRASH TESTJul 26, 2017
PRIVICY
YOU MAY NEED TO GIVE UP YOUR SOCIAL MEDIA PASSWORD TO... Raul Fleury - May 29,2017
0
Thousands of people come to the US every day. If the Trump administration sticks to its policies, some visitors will soon have toreveal...
MEET VERO, A NO-ADS SOCIAL NETWORK LAUNCHED BY A BILLIONAIRE Bart Wallis - May 22,2017
0
The most popular social networks such as Facebook and Twitter are free because they are funded by advertisers. The more time you spendon...
WHAT PARENTS SHOULD KNOW ABOUT MUSICAL.LYMay 15, 2017
GOOGLE IS JUST ONE STEP BEHIND APPLE: FAMILY SHARING IS LAUNCHEDMay 8, 2017
WHAT EVERY PARENT SHOULD KNOW ABOUT FINSTA/SPAM ACCOUNTSMay 1, 2017
NEW INSTAGRAM PRIVACY POLICIES: PARENTS CAN TALK TO THEIR KIDSABOUT...
Apr 24, 2017
____
FEATURED
HOW CAN YOU FIND A SUITABLE ANTIVIRUS SOLUTION Donald Davis - Aug 30,2017
HOW TO TELL IF YOUR COMPUTER IS INFECTED WITH MALWARE Clarence Busby - Aug2, 2017
WHAT EVERY PARENT SHOULD KNOW ABOUT FINSTA/SPAM ACCOUNTS Jose Grabowski - May1, 2017
APPLICATIONS
HOTSPOT SHIELD ELITE: GREAT VPN FOR EVERYONE Ronald Kennell - Jul9, 2015
HOW CAN YOU FIND A SUITABLE ANTIVIRUS SOLUTION Donald Davis - Aug 30,2017
SIMPLE TIPS ON HOW TO UPGRADE YOUR MAC AND SET UP BASIC PROTECTIONFROM...
Bart Wallis - Sep 18,2015
POPULAR FREE VPN HOLA USED AS A GIANT BOTNET SELLING ITS USERS’PERSONAL DATA
Alma Perry - Jun 13, 2015HOT NEWS
IPVANISH VS. HIDEMYASS: WHICH VPN IS BEST FOR YOU? Ronald Kennell - May18, 2015
0
Ipvanish and HideMyAss are top-notch VPN services and are offered at competitive prices. Both offer amazing security and privacy to any online user or small business. Though both are great, you might be inclined to choose one or the other based on your personal needs.____
WINDOWS PHONE
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL – ON EACH OS Clarence Busby - Sep14, 2017
0
Normally, the Zip files are password protected. However, the conventional Zip encryption system is very weak and might not be suitable if you are...EVEN MORE NEWS
MAKE YOUR ZIP ARCHIVE CONFIDENTIAL – ON EACH OSSep 14, 2017
HOW CAN YOU FIND A SUITABLE ANTIVIRUS SOLUTIONAug 30, 2017
WHAT SHOULD YOU DO IF YOUR EMAIL IS COMPROMISEDAug 16, 2017
POPULAR CATEGORY
* Security76
* Computer51
* Privacy45
* Tips & Tricks29
* Web & Email28
* Mobile23
* Spotlight14
* Privacy Policy & Affiliate Disclosure* Contact Us
�
safetyholic.com website wants toShow notification
AllowDeny
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0