Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://thestayathomechef.com
Are you over 18 and want to see adult content?

A complete backup of https://lermanet.com
Are you over 18 and want to see adult content?

A complete backup of https://bizfunding.co.za
Are you over 18 and want to see adult content?
A complete backup of https://wifinowevents.com
Are you over 18 and want to see adult content?
A complete backup of https://matthiasott.com
Are you over 18 and want to see adult content?
A complete backup of https://michaelkorswatches.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://bayern-park.de
Are you over 18 and want to see adult content?
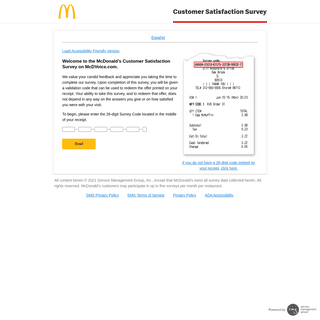
A complete backup of https://mcdvoice.com
Are you over 18 and want to see adult content?
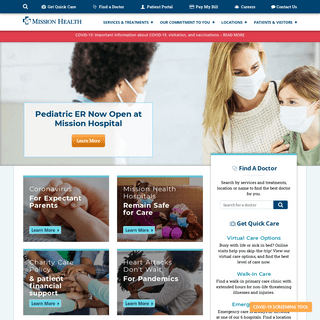
A complete backup of https://mission-health.org
Are you over 18 and want to see adult content?
A complete backup of https://toldot.ru
Are you over 18 and want to see adult content?
A complete backup of https://vectura.su
Are you over 18 and want to see adult content?
A complete backup of https://psicoterapeutas.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://dalkinovaspc.com
Are you over 18 and want to see adult content?

A complete backup of https://labtestsonline.org
Are you over 18 and want to see adult content?

A complete backup of https://crystalhotels.com.tr
Are you over 18 and want to see adult content?

A complete backup of https://swivigal.tk
Are you over 18 and want to see adult content?

A complete backup of https://searchenginewatch.com
Are you over 18 and want to see adult content?
A complete backup of https://mkssoftware.com
Are you over 18 and want to see adult content?
A complete backup of https://visitrussia.org.uk
Are you over 18 and want to see adult content?

A complete backup of https://rasandclin.tk
Are you over 18 and want to see adult content?

A complete backup of https://hoki-museum.jp
Are you over 18 and want to see adult content?

A complete backup of https://fossilrim.org
Are you over 18 and want to see adult content?
Text
SCOTTHELME.CO.UK
SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so PUMPING UP YOUR INTERNET SPEEDS WITH THE UNIFI SECURITY Go to the Devices section of your controller, select the USG to open the information pane, select Ports and then Configure Interfaces. Once you save those settings, the second port is ready to be used. You then need to go to Settings (bottom left), Internet and then WAN Networks. HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
INTRODUCING ANOTHER FREE CA AS AN ALTERNATIVE TO LET'S ENCRYPT Let's Encrypt is an amazing organisation doing an amazing thing by providing certificates at scale, for free. The problem though was that they were the only such organisation for a long time, but I'm glad to say that the ecosystem is changing. It's always a good idea to haveanother
REPORT URI PENETRATION TEST A penetration test, colloquially known as a pen test, pentest or ethical hacking, is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system. In short, a 'pen test' is where you pay a group of highly skilled security experts to try to hack into your application to see if they can break it THE M140I PROJECT POST The series. As I post more parts of this series I will update the links so you can easily browse through them. Part 1 was a great starting point with mostly visual mods but now it's time to step it up a gear (see what I did there?) and continue the journey of customisingmy BMW M140i.
SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back LET'S ENCRYPT WITH DNS ROUND-ROBIN The plan was simple: create server, add IP address to DNS. DNS round-robin allows you to have 2 (or more) IP addresses for the same domain and they are returned in a different order so that clients will use different ones. The idea is to end up with fairly basic load balancing and ~50% of the traffic on each server. This solves my loadissue.
WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. ENABLING CERTIFICATE REVOCATION CHECKS IN GOOGLE CHROME It's really easy to enable standard revocation checking in Google Chrome. Navigate to the Chrome settings window, chrome://settings/, click on "Show advanced settings" and then scroll down to the "HTTPS/SSL" section. Once there, you need to tick the "Check for server certificate revocationOCSP MUST-STAPLE
To setup OCSP Must-Staple all you need to do is add the following line. Don't worry too much about the details here, but if you do want to know then 1.3.6.1.5.5.7.1 is the object identifier for SMI Security for PKIX Certificate Extension and 24 is the id assigned to RFC 7633. SAFARI DOESN'T LIKE CSP I've recently hit a few bumps with Safari whilst implementing an improved CSP on report-uri.io. This blog post is to outline the issues I've had so that others might be able to avoid them! Versions and info I'm using Safari 8.0.8 (10600.8.9) on OS X SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so MY UBIQUITI HOME NETWORK The UniFi Security Gateway (USG) is the router and firewall that will sit at the edge of your network between your LAN and the WAN. It has one Ethernet port for the WAN, one for the LAN and on the latest firmware upgrade, the VOIP port can be provisioned as a second LAN connection, the remaining port is the Console port. HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate. SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so MY UBIQUITI HOME NETWORK The UniFi Security Gateway (USG) is the router and firewall that will sit at the edge of your network between your LAN and the WAN. It has one Ethernet port for the WAN, one for the LAN and on the latest firmware upgrade, the VOIP port can be provisioned as a second LAN connection, the remaining port is the Console port. HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate.SCOTT HELME
Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training onWHAT THE FLOC?!
FLoC aims to remove the need for invasive tracking to serve relevant ads to users by categorising users based on their browsing history on the client device itself. The client would then provide a FLoC ID to the server upon request and the site would know what your interests are. I might have a FLoC ID of 721954 generated which means I'm MY UBIQUITI HOME NETWORK The UniFi Security Gateway (USG) is the router and firewall that will sit at the edge of your network between your LAN and the WAN. It has one Ethernet port for the WAN, one for the LAN and on the latest firmware upgrade, the VOIP port can be provisioned as a second LAN connection, the remaining port is the Console port. SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate. TESTING OUT ECDSA CERTIFICATES Generating the ECDSA key. If you want to generate an ECDSA key to get a certificate from Let's Encrypt then you can use the following commands. Remove the -aes128 from the end of the command if you don't want to set a password on the key. openssl ecparam -genkey -name secp256r1 | openssl ec -out ecdsa.key -aes128. ENABLING CERTIFICATE REVOCATION CHECKS IN GOOGLE CHROME It's really easy to enable standard revocation checking in Google Chrome. Navigate to the Chrome settings window, chrome://settings/, click on "Show advanced settings" and then scroll down to the "HTTPS/SSL" section. Once there, you need to tick the "Check for server certificate revocation THE BEST TLS TRAINING IN THE WORLD They're a dedicated technology venue and their facilities are fantastic. They even have a bar at the venue so we can kick back with a beer after the course if you want to hang around, I've even been known to get a round in! Dates: 7th Feb - The Best TLS Training in the World (Sold Out) 8th Feb -OCSP MUST-STAPLE
To setup OCSP Must-Staple all you need to do is add the following line. Don't worry too much about the details here, but if you do want to know then 1.3.6.1.5.5.7.1 is the object identifier for SMI Security for PKIX Certificate Extension and 24 is the id assigned to RFC 7633. SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
PUMPING UP YOUR INTERNET SPEEDS WITH THE UNIFI SECURITY Go to the Devices section of your controller, select the USG to open the information pane, select Ports and then Configure Interfaces. Once you save those settings, the second port is ready to be used. You then need to go to Settings (bottom left), Internet and then WAN Networks. MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
THE BEST TLS TRAINING IN THE WORLD They're a dedicated technology venue and their facilities are fantastic. They even have a bar at the venue so we can kick back with a beer after the course if you want to hang around, I've even been known to get a round in! Dates: 7th Feb - The Best TLS Training in the World (Sold Out) 8th Feb - STABILISING FAILOVER DETECTION ON THE UNIFI SECURITY GATEWAY Changing the failover criteria. It's easy to change these settings directly on the USG via SSH using the configure command. Scott@UnifiSecurityGateway:~$ configure. Once you've run that command you can now edit the configuration and set/change options as needed. Scott@UnifiSecurityGateway# set load-balance group wan_failoverinterface pppoe0
SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
PUMPING UP YOUR INTERNET SPEEDS WITH THE UNIFI SECURITY Go to the Devices section of your controller, select the USG to open the information pane, select Ports and then Configure Interfaces. Once you save those settings, the second port is ready to be used. You then need to go to Settings (bottom left), Internet and then WAN Networks. MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
THE BEST TLS TRAINING IN THE WORLD They're a dedicated technology venue and their facilities are fantastic. They even have a bar at the venue so we can kick back with a beer after the course if you want to hang around, I've even been known to get a round in! Dates: 7th Feb - The Best TLS Training in the World (Sold Out) 8th Feb - STABILISING FAILOVER DETECTION ON THE UNIFI SECURITY GATEWAY Changing the failover criteria. It's easy to change these settings directly on the USG via SSH using the configure command. Scott@UnifiSecurityGateway:~$ configure. Once you've run that command you can now edit the configuration and set/change options as needed. Scott@UnifiSecurityGateway# set load-balance group wan_failoverinterface pppoe0
SCOTT HELME (PAGE 2) I was looking forward to something happening this month in the world of PKI that has had to be postponed for the 3rd time. Let's Encrypt were going to be. ← Newer Posts Page 2 of 35 Older Posts →. Upcoming Events. Practical TLS and PKI (USA/EU TZ Remote) 6th - 9th July. Cheat Sheets. CSP Cheat Sheet. HSTS Cheat Sheet.WHAT THE FLOC?!
FLoC aims to remove the need for invasive tracking to serve relevant ads to users by categorising users based on their browsing history on the client device itself. The client would then provide a FLoC ID to the server upon request and the site would know what your interests are. I might have a FLoC ID of 721954 generated which means I'm THE M140I PROJECT POST The series. As I post more parts of this series I will update the links so you can easily browse through them. Part 1 was a great starting point with mostly visual mods but now it's time to step it up a gear (see what I did there?) and continue the journey of customisingmy BMW M140i.
CROSS-SIGNING AND ALTERNATE TRUST PATHS; HOW THEY WORK The CA has two steps to complete to sign the certificate. The first step is the CA taking the Pre-Certificate and running it through a hash function, currently SHA256, to obtain the digest. The second step is the CA then taking that digest and encrypting it with their privatekey.
TESTING OUT ECDSA CERTIFICATES Generating the ECDSA key. If you want to generate an ECDSA key to get a certificate from Let's Encrypt then you can use the following commands. Remove the -aes128 from the end of the command if you don't want to set a password on the key. openssl ecparam -genkey -name secp256r1 | openssl ec -out ecdsa.key -aes128. SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate. ENABLING CERTIFICATE REVOCATION CHECKS IN GOOGLE CHROME It's really easy to enable standard revocation checking in Google Chrome. Navigate to the Chrome settings window, chrome://settings/, click on "Show advanced settings" and then scroll down to the "HTTPS/SSL" section. Once there, you need to tick the "Check for server certificate revocation GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. SAFARI DOESN'T LIKE CSP I've recently hit a few bumps with Safari whilst implementing an improved CSP on report-uri.io. This blog post is to outline the issues I've had so that others might be able to avoid them! Versions and info I'm using Safari 8.0.8 (10600.8.9) on OS X SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. HARDENING YOUR HTTP RESPONSE HEADERS TESTING OUT ECDSA CERTIFICATES HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. HARDENING YOUR HTTP RESPONSE HEADERS TESTING OUT ECDSA CERTIFICATES HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
WHY CLOSING PORT 80 IS BAD FOR SECURITY And about usability, closing port 80 is only a problem for users typing manually the url in an old browser. (And, in my opinion, when port 80 is closed browsers should try https, as Firefox tries "www." when the bare domain doesn't answer.) Furthermore, security is about limiting the surface attacks. Closing port 80 goes to the rightdirection.
HARDENING YOUR HTTP RESPONSE HEADERS Following the recent announcement of my new service, https://securityheaders.io, I thought I'd cover some more of the security based HTTP response headers out there and look at how to harden your existing HTTP response headers. Introduction. HTTP Response headers are name-value pairs of strings sent back from a server with the content you requested. TESTING OUT ECDSA CERTIFICATES Generating the ECDSA key. If you want to generate an ECDSA key to get a certificate from Let's Encrypt then you can use the following commands. Remove the -aes128 from the end of the command if you don't want to set a password on the key. openssl ecparam -genkey -name secp256r1 | openssl ec -out ecdsa.key -aes128. SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. LET'S ENCRYPT WITH DNS ROUND-ROBIN The plan was simple: create server, add IP address to DNS. DNS round-robin allows you to have 2 (or more) IP addresses for the same domain and they are returned in a different order so that clients will use different ones. The idea is to end up with fairly basic load balancing and ~50% of the traffic on each server. This solves my loadissue.
MY UBIQUITI HOME NETWORK The UniFi Security Gateway (USG) is the router and firewall that will sit at the edge of your network between your LAN and the WAN. It has one Ethernet port for the WAN, one for the LAN and on the latest firmware upgrade, the VOIP port can be provisioned as a second LAN connection, the remaining port is the Console port. SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM The first step is to go to Settings, search for Local Network and click Create New Local Network. Click Create Advanced Network and then fill out a Name, make sure the Network Purpose is set to Guest, give it a VLAN ID of 2 or higher if that's already taken and click Done. If you created a guest Wifi network in the previous step you can go back ENABLING CERTIFICATE REVOCATION CHECKS IN GOOGLE CHROME It's really easy to enable standard revocation checking in Google Chrome. Navigate to the Chrome settings window, chrome://settings/, click on "Show advanced settings" and then scroll down to the "HTTPS/SSL" section. Once there, you need to tick the "Check for server certificate revocation DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate. CROSS-SITE REQUEST FORGERY IS DEAD! When operating in Strict mode the browser will not send the cookie on any cross-origin request, at all, so CSRF is completely dead in the water. The only problem you might come across is that it also won't send the cookie on top-level navigations (changing the URL in the address bar) either. SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
HARDENING YOUR HTTP RESPONSE HEADERS GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. TESTING OUT ECDSA CERTIFICATES WHY CLOSING PORT 80 IS BAD FOR SECURITY With the giant push to HTTPS taking place on the web, I often hear the idea of closing port 80 to improve security further. Here's why youshouldn't.
SCOTT HELMESPEAKINGTRAININGMEDIACONTACTSPONSORCLOUDFLARE WORKERS Hi, I'm Scott Helme, a Security Researcher, Entrepreneur and International Speaker. I'm the creator of Report URI and Security Headers and I deliver world renowned training on MY UBIQUITI HOME NETWORK My Ubiquiti Home Network - V1. It was Dec 2016 when I wrote about My Ubiquiti Home Network, which I'm now going to brand as V1, and what drove me to replace my existing setup with Ubiquiti hardware.It was quite a bit of money to shell out on network kit for my house but I was pissed off with the equipment provided my ISP, bought my own and then got fed up of trying to make stuff work COEP COOP CORP CORS CORB Yep, you heard it right, we have a few new security features and even some new Security Headers in town! Whilst technically only COOP, COEP, CORP and CORB are new, CORS is very related despite having been around for a while and is still very much worth talking about, so A NEW SECURITY HEADER: REFERRER POLICY Regular readers will know how fond I am of the existing security headers so it's great to hear that we're getting another! Referrer Policy will allow a site to control the value of the referer header in links away from their pages. HACKING AZURE TABLE STORAGE TO DO LIKE QUERIESSEE MORE ONSCOTTHELME.CO.UK
MY TLS CONUNDRUM AND WHY I DECIDED TO LEAVE CLOUDFLARESEE MORE ONSCOTTHELME.CO.UK
HARDENING YOUR HTTP RESPONSE HEADERS GETTING AN A+ ON THE QUALYS SSL TEST My previous article has gained a lot of attention as a reference point on how to score the highest A+ rating on the Qualys SSL Test. In doing so, site admins are ensuring that the TLS configuration on their server offers up to date and robust security to their users. Focused around my own NginX install on Ubuntu, my previous article didn't cater for Windows Server admins. TESTING OUT ECDSA CERTIFICATES WHY CLOSING PORT 80 IS BAD FOR SECURITY With the giant push to HTTPS taking place on the web, I often hear the idea of closing port 80 to improve security further. Here's why youshouldn't.
HARDENING YOUR HTTP RESPONSE HEADERS Following the recent announcement of my new service, https://securityheaders.io, I thought I'd cover some more of the security based HTTP response headers out there and look at how to harden your existing HTTP response headers. Introduction. HTTP Response headers are name-value pairs of strings sent back from a server with the content you requested. SETTING UP HTTPS ON THE UDM PRO HTTPS on the UniFi Cloud Key. In my 'V1' home network, My Ubiquiti Home Network, I had the UniFi Security Gateway and a few other goodies like the UniFi Cloud Key.You can read full details of my previous home setup in the link, but, of course, I did a blog post on how to setup HTTPS on the web UI, Setting up HTTPS on the UniFi Cloud Key. It wasn't the most straightforward thing to, but it's TESTING OUT ECDSA CERTIFICATES Let's Encrypt recently started signing certificates that use ECDSA keys so I figured I'd grab one and give it a try. ECDSA offers considerable increases in both security and performance compared to RSA and boy can you see it! ECDSA I'm not going to do a deep dive onECDSA
SECURING YOUR HOME NETWORK IN PREPARATION FOR WORKING FROM I'm fortunate to have spent the last few years either working from home or travelling the World doing training, consultancy and public speaking. With the recent Coronavirus epidemic having quite literally wiped my travel schedule clean, I find myself doing a UPGRADING MY PC WITH A TPM What is a TPM? A TPM, a Trusted Platform Module, a little hardware device that's usually embedded into most modern PCs on the motherboard. The TPM is designed to be a tamper-resistant store for cryptographic keys and in the context of this article, I will be talking about using it in conjunction with BitLocker drive encryption. MY UBIQUITI HOME NETWORK Ubiquiti. I'd heard of Ubiquiti before but only in enterprise scenarios. Whilst walking around offices I had recognised their access points dotted around on walls and hadn't really thought much more of LET'S ENCRYPT WITH DNS ROUND-ROBIN I was having a period of really high load on securityheaders.io earlier and whilst I looked into it and sorted out the root cause I wanted to throw some more cloud behind the site to bolster it. That introduced an interesting problem that I wanted to solve quickly. DNS Round-Robin. I wanted to spin up another server to split the load off the current, single instance that securityheaders.io ENABLING CERTIFICATE REVOCATION CHECKS IN GOOGLE CHROME Following on from the announcement of Heartbleed, it's fair to assume that there will be a huge amount of certificate revocations both in progress and in the days and weeks to come. With an increased number of revocations, there's the potential that OCSP/CRL responses maystart to take a
DEMONSTRATING THAT REVOCATION CHECKING IS POINTLESS! Revocation checking: a brief history. I have a super detailed blog post all about the 2 main mechanism for revocation checking that people are often familiar with. We have Certificate Revocation Lists (CRL) and the Online Certificate Status Protocol (OCSP) which let a client check if a certificate has been revoked and the client should no longer trust that otherwise valid certificate. CROSS-SITE REQUEST FORGERY IS DEAD! After toiling with Cross-Site Request Forgery on the web for, well forever really, we finally have a proper solution. No technical burden on the site owner, no difficult implementation, it's trivially simple to deploy, it's Same-Site Cookies.* Home
* Speaking
* Training
* Media
* Contact
* Sponsor
* __
* __
* __
* __
Subscribe
SCOTT HELME
HI, I'M SCOTT HELME, A SECURITY RESEARCHER, ENTREPRENEUR AND INTERNATIONAL SPEAKER. I'M THE CREATOR OF REPORT URI AND SECURITY HEADERS AND I DELIVER WORLD RENOWNED TRAINING ON HACKING ANDENCRYPTION.
SPONSORED BY: Want to sponsor my site? Click here for more info!Free Post
Let's Encrypt
INTRODUCING ANOTHER FREE CA AS AN ALTERNATIVE TO LET'S ENCRYPT Let's Encrypt is an amazing organisation doing an amazing thing by providing certificates at scale, for free. The problem though was that they were the only such organisation for a*
Scott Helme
Scott Helme 20 Nov 2020 • 3 min readFree Post
HSTS
WANT TO ENCRYPT ALL THE THINGS? FIREFOX HAS YOU COVERED WITHHTTPS-ONLY MODE!
We are currently powering towards an encrypted Web and in recent years we've made tremendous progress on that journey. In the latest version of Firefox, a browser that's been at*
Scott Helme
Scott Helme 17 Nov 2020 • 3 min readFree Post
certificate revocation DÉJÀ VU - MACOS HITS OCSP HURDLES Regular readers will have seen me talk about OCSP many times before and some of those times are going back quite a number of years. That'swhy it came as
*
Scott Helme
Scott Helme 16 Nov 2020 • 7 min readFree Post
BMW M140i Project
THE M140I PROJECT POST - PART 11 This is going to be a big one and I'm super excited! In this post I'm only going to be talking about one thing but it's pretty significantin a
*
Scott Helme
Scott Helme 13 Nov 2020 • 10 min readFree Post
Let's Encrypt
LET'S ENCRYPT ISSUES NEW ROOT AND INTERMEDIATE CERTIFICATES Let's Encrypt have just issued a bunch of new certificates including a new Root and several Intermediates. These will bring some significant advantages so let's dive in and take a*
Scott Helme
Scott Helme 30 Oct 2020 • 8 min readFree Post
BMW M140i Project
THE M140I PROJECT POST - PART 10 Part 10?! When I started writing this series I did not expect to hit Part 10 and the good news for those appreciating these blog posts is that there's probably*
Scott Helme
Scott Helme 30 Sep 2020 • 11 min readFree Post
Let's Encrypt
LET'S ENCRYPT POSTPONE THE ISRG ROOT TRANSITION I was looking forward to something happening this month in the world of PKI that has had to be postponed for the 3rd time. Let's Encryptwere going to be
*
Scott Helme
Scott Helme 24 Sep 2020 • 4 min readFree Post
Security Headers
GOODBYE FEATURE POLICY AND HELLO PERMISSIONS POLICY! I talked about Feature Policy almost 2 years ago and it has seen great adoption since then. As things have progressed a name change has been proposed and accepted so*
Scott Helme
Scott Helme 7 Sep 2020 • 2 min readFree Post
BMW M140i Project
THE M140I PROJECT POST - PART 9 After another short break from writing about the car project it's time to hit it again with Part 9 and quite a few items that you don't needto be
*
Scott Helme
Scott Helme 31 Aug 2020 • 11 min readFree Post
Certificate Authorities FINDING ALTERNATE TRUST PATHS THE EASY WAY; INTRODUCING CHAIN BUILDER I ended up talking a lot about certificates recently and covered quite a few topics in a good amount of detail. To demonstrate something I've touched on a few times*
Scott Helme
Scott Helme 6 Jul 2020 • 8 min read Page 1 of 33 Older Posts →UPCOMING EVENTS
The Best TLS Training in the World (EMEA TZ Remote)23rd - 26th Nov
The Best TLS Training in the World (US/Can TZ Remote)7th - 10th Dec
CHEAT SHEETS
CSP Cheat Sheet
HSTS Cheat Sheet
HTTPS Cheat Sheet
Performance Cheat SheetPROJECTS
Report URI
Security Headers
Why No HTTPS?
Crawler.Ninja
HTTP Forever
FOLLOW
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
License CC BY-SA 4.0to scotthelme.co.uk
__ __
__
__
Thanks for supporting me and my work! Great, you're subscribed! Perhaps you'd also consider supporting mywork?
Welcome back! You've successfully signed in. Wow! Thanks for the support! Success! Your billing info is updated. Billing info update failed.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0


