Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://pluspool.org
Are you over 18 and want to see adult content?
A complete backup of https://atomtickets.com
Are you over 18 and want to see adult content?
A complete backup of https://terraeconomicus.com
Are you over 18 and want to see adult content?
A complete backup of https://dodosmusic.net
Are you over 18 and want to see adult content?
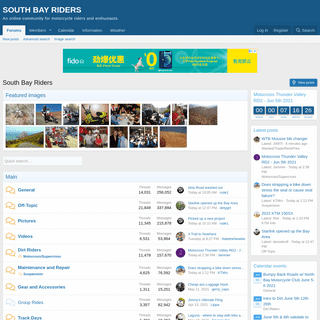
A complete backup of https://southbayriders.com
Are you over 18 and want to see adult content?

A complete backup of https://mydeposits.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://landingcube.com
Are you over 18 and want to see adult content?

A complete backup of https://smaregi.jp
Are you over 18 and want to see adult content?

A complete backup of https://fleetsimplify.com
Are you over 18 and want to see adult content?

A complete backup of https://greenstreet.com
Are you over 18 and want to see adult content?

A complete backup of https://ignitenational.org
Are you over 18 and want to see adult content?

A complete backup of https://inceusa.org
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://liketoknow.it
Are you over 18 and want to see adult content?
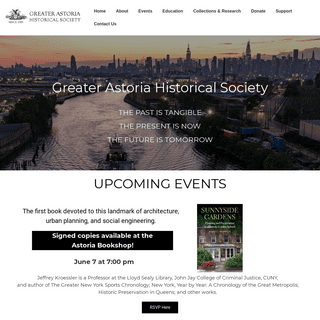
A complete backup of https://astorialic.org
Are you over 18 and want to see adult content?

A complete backup of https://elliottelectric.com
Are you over 18 and want to see adult content?
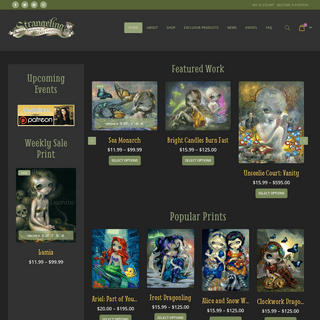
A complete backup of https://strangeling.com
Are you over 18 and want to see adult content?

A complete backup of https://fondazioneluigieinaudi.it
Are you over 18 and want to see adult content?

A complete backup of https://fabickcat.com
Are you over 18 and want to see adult content?
A complete backup of https://adamvstheman.com
Are you over 18 and want to see adult content?
A complete backup of https://worldginday.com
Are you over 18 and want to see adult content?

A complete backup of https://refin.it
Are you over 18 and want to see adult content?

A complete backup of https://gazprom.ru
Are you over 18 and want to see adult content?
A complete backup of https://techgraph.co
Are you over 18 and want to see adult content?

A complete backup of https://marketingtechblog.com
Are you over 18 and want to see adult content?
Text
application
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
A SECURITY OPERATIONS CENTER (SOC) REPORT TEMPLATE FOR THE The Security Operations Center (SOC) is an important element of any organization’s cybersecurity strategy. Staffed by a team of security analysts and incident responders who work together to detect, analyze, respond to, report on, and prevent data breaches. It’s an important role — the SOC is a company’s first line of defense against cybersecurity threats, and also the team responsible THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good SECURITY RATINGS & CYBERSECURITY RISK MANAGEMENTPRODUCTSSOLUTIONSCUSTOMERSPARTNERSRESOURCESCOMPANY See what a hacker sees. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees. 52 OF THE BEST CYBERSECURITY CONFERENCES TO ATTEND IN 2021 For business and security leaders working to drive effective cybersecurity programs, it’s important to keep up with industry best practices and technology. That's why we've put together a list of the 52 best conferences across the globe to attend in 2021. 34 RESOURCES FOR EMPLOYEE CYBERSECURITY TRAINING Small businesses need to train their employees, but they often have limited resources. These nine free security awareness training options in alphabetical order can help fill that gap. 1. Cofense sample lesson. Cofense is a company providing solutions for TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
A SECURITY OPERATIONS CENTER (SOC) REPORT TEMPLATE FOR THE The Security Operations Center (SOC) is an important element of any organization’s cybersecurity strategy. Staffed by a team of security analysts and incident responders who work together to detect, analyze, respond to, report on, and prevent data breaches. It’s an important role — the SOC is a company’s first line of defense against cybersecurity threats, and also the team responsible THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good 7 ESSENTIAL THIRD-PARTY RISK MANAGEMENT (TPRM) TOOLS L 7 Essential Third-Party Risk Management (TPRM) Tools. With 44% of data breaches caused by a third party and only 15% of vendors disclosing that a breach had taken place, it’s no surprise that many organizations are prioritizing investment in their third-party risk management (TPRM) programs. In fact, 74% say their organizationsurgently need
5 WAYS DATA BREACHES AFFECT ORGANIZATIONS L SECURITYSCORECARD 5. Business continuity. If it’s not managed well, a data breach can do lasting damage to your organization. Given the many ways an attack can affect an organization, this isn’t surprising — if you’re not prepared to be attacked, you can lose funds, customer trust,productivity, and
PATCHING CADENCE ISSUE RESOLUTION If a “Vulnerability Found” is patched within 45 (high severity), 60 (medium), and 120 days (low severity) after CVE publish date (Last observed) there will be no “CVE Patching Cadence” findings created and the original “Vulnerability Found” finding will be removed from the scorecard (either based on a remediation request or organically after 45 days after the date of last observation). 57 CYBERSECURITY TERMS YOU SHOULD KNOW IN 2021 Cybersecurity does not need to be so confusing. To help you and your non-technical team members better understand security, check out thislist of
JBS RANSOMWARE ATTACK STARTED IN MARCH SecurityScorecard found that the JBS ransomware attack started in March and is much larger in scope than previously identified. Check out SecurityScorecard's research. TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
OUR INTEGRATIONS
Return Home SecurityScorecard 111 West 33rd Street. FLR 11 New York, NY 10001 United States: (800) 682-1707 International: +1 (646)809-2166
5 DATA BREACH STATISTICS AND TRENDS TO LOOK OUT FOR IN 2020 5 Data Breach Statistics and Trends to Look Out for in 2020. This past year has been quite a year for data breaches. From DoorDash to FEMA, billions of records were breached in 2019, causing millions of dollars in damage. Criminals phished, targeted small businesses and used psychological as well as technological attacks to make money, spy on HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
SEE RISK
No waiting, 100% Free. Get your personalized scorecard today. Get your free scorecard and learn how you stack up across 10 risk categories. Answer a few simple questions and we'll instantly send your score to your business email. WHAT TO KNOW ABOUT SECURITYSCORECARD’S INTEGRATE360 The old saying “it takes a village” applies to many things in life, including securing your organization. Security is a team sport that requires a variety of solutions and providers — such as a firewall, endpoint protection, security information and event management (SIEM), threat intelligence provider, IT service management (ITSM), governance, risk, and compliance solution (GRC), and PROTECT YOUR RETAIL SUPPLY CHAIN AGAINST CYBER SecurityScorecard in partnership with Vodafone will show the importance of continuously monitoring the cybersecurity posture of your own organization and of the third parties we use and trust and demonstrate how you can do that to combat the war against hackers. A SECURITY OPERATIONS CENTER (SOC) REPORT TEMPLATE FOR THE The Security Operations Center (SOC) is an important element of any organization’s cybersecurity strategy. Staffed by a team of security analysts and incident responders who work together to detect, analyze, respond to, report on, and prevent data breaches. It’s an important role — the SOC is a company’s first line of defense against cybersecurity threats, and also the team responsible SECURITY RATINGS & CYBERSECURITY RISK MANAGEMENTPRODUCTSSOLUTIONSCUSTOMERSPARTNERSRESOURCESCOMPANY See what a hacker sees. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees. 34 RESOURCES FOR EMPLOYEE CYBERSECURITY TRAINING Small businesses need to train their employees, but they often have limited resources. These nine free security awareness training options in alphabetical order can help fill that gap. 1. Cofense sample lesson. Cofense is a company providing solutions for 52 OF THE BEST CYBERSECURITY CONFERENCES TO ATTEND IN 2021 For business and security leaders working to drive effective cybersecurity programs, it’s important to keep up with industry best practices and technology. That's why we've put together a list of the 52 best conferences across the globe to attend in 2021. HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
A SECURITY OPERATIONS CENTER (SOC) REPORT TEMPLATE FOR THE The Security Operations Center (SOC) is an important element of any organization’s cybersecurity strategy. Staffed by a team of security analysts and incident responders who work together to detect, analyze, respond to, report on, and prevent data breaches. It’s an important role — the SOC is a company’s first line of defense against cybersecurity threats, and also the team responsible 7 ESSENTIAL THIRD-PARTY RISK MANAGEMENT (TPRM) TOOLS L 7 Essential Third-Party Risk Management (TPRM) Tools. With 44% of data breaches caused by a third party and only 15% of vendors disclosing that a breach had taken place, it’s no surprise that many organizations are prioritizing investment in their third-party risk management (TPRM) programs. In fact, 74% say their organizationsurgently need
THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good PATCHING CADENCE ISSUE RESOLUTION If a “Vulnerability Found” is patched within 45 (high severity), 60 (medium), and 120 days (low severity) after CVE publish date (Last observed) there will be no “CVE Patching Cadence” findings created and the original “Vulnerability Found” finding will be removed from the scorecard (either based on a remediation request or organically after 45 days after the date of last observation). SECURITY RATINGS & CYBERSECURITY RISK MANAGEMENTPRODUCTSSOLUTIONSCUSTOMERSPARTNERSRESOURCESCOMPANY See what a hacker sees. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees. 34 RESOURCES FOR EMPLOYEE CYBERSECURITY TRAINING Small businesses need to train their employees, but they often have limited resources. These nine free security awareness training options in alphabetical order can help fill that gap. 1. Cofense sample lesson. Cofense is a company providing solutions for 52 OF THE BEST CYBERSECURITY CONFERENCES TO ATTEND IN 2021 For business and security leaders working to drive effective cybersecurity programs, it’s important to keep up with industry best practices and technology. That's why we've put together a list of the 52 best conferences across the globe to attend in 2021. HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
A SECURITY OPERATIONS CENTER (SOC) REPORT TEMPLATE FOR THE The Security Operations Center (SOC) is an important element of any organization’s cybersecurity strategy. Staffed by a team of security analysts and incident responders who work together to detect, analyze, respond to, report on, and prevent data breaches. It’s an important role — the SOC is a company’s first line of defense against cybersecurity threats, and also the team responsible 7 ESSENTIAL THIRD-PARTY RISK MANAGEMENT (TPRM) TOOLS L 7 Essential Third-Party Risk Management (TPRM) Tools. With 44% of data breaches caused by a third party and only 15% of vendors disclosing that a breach had taken place, it’s no surprise that many organizations are prioritizing investment in their third-party risk management (TPRM) programs. In fact, 74% say their organizationsurgently need
THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good PATCHING CADENCE ISSUE RESOLUTION If a “Vulnerability Found” is patched within 45 (high severity), 60 (medium), and 120 days (low severity) after CVE publish date (Last observed) there will be no “CVE Patching Cadence” findings created and the original “Vulnerability Found” finding will be removed from the scorecard (either based on a remediation request or organically after 45 days after the date of last observation). SECURITYSCORECARD SPRING 2021 PRODUCT RELEASE SecurityScorecard empowers you to see and understand cybersecurity risk in your organization and across your ecosystem with 360° visibility and seamless workflow integration with your security stack. SPRING 2021 PRODUCT RELEASE: INTEGRATE360° MARKETPLACE NOTES Integrate360° Marketplace . Take your security to the next level with 40+ integrations, additional data, & service providers . Integrate360° is SecurityScorecard’s marketplace of integrations that work with what you have. Discover and deploy integrated solutions to optimize your security workflows, access even more security intelligence, and accelerate risk mitigation. HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
JBS RANSOMWARE ATTACK STARTED IN MARCH SecurityScorecard found that the JBS ransomware attack started in March and is much larger in scope than previously identified. Check out SecurityScorecard's research. SPRING 2021 PRODUCT RELEASE: ATLAS NOTES Evidence Locker. Open exchange of VRM data to automate and accelerate vendor risk security assessments. Evidence Locker is your single source for TPRM documentation, allowing teams to automatically populate vendor and compliance questionnaires with stored data by exchanging this information between Atlas and Ratings.OUR INTEGRATIONS
Return Home SecurityScorecard 111 West 33rd Street. FLR 11 New York, NY 10001 United States: (800) 682-1707 International: +1 (646)809-2166
SECURITYSCORECARD CYBER RISK FACTORS EXPLAINED SecurityScorecard 10 Risk Factors Explained. Increasingly, organizations understand both the financial impact and information security posture value associated with cybersecurity ratings. At SecurityScorecard, we believe that trust begins with transparency. In keeping with this commitment to transparency, SecurityScorecard ensures that our ten KPIS FOR SECURITY OPERATIONS & INCIDENT RESPONSE In today’s constantly changing threat landscape, senior leadership needs to work closely with the security team to create key performance indicators (KPIs) for security operations and incident response to understand your current and future cybersecurity posture. 5 STEPS TO PLANNING YOUR CYBERSECURITY RISK MANAGEMENT No matter how good your security controls are, your business will always have some cyber risk. That can be concerning — the average data breach costs close to $4 million. The good news is that risk can be managed — that’s why it’s so important for every organization to develop a cybersecurity risk management strategy.IN THE NEWS
No waiting, 100% Free. Get your personalized scorecard today. Get your free scorecard and learn how you stack up across 10 risk categories. Answer a few simple questions and we'll instantly send your score to your business email. SECURITY RATINGS & CYBERSECURITY RISK MANAGEMENTPRODUCTSSOLUTIONSCUSTOMERSPARTNERSRESOURCESCOMPANY See what a hacker sees. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees. HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
52 OF THE BEST CYBERSECURITY CONFERENCES TO ATTEND IN 2021 For business and security leaders working to drive effective cybersecurity programs, it’s important to keep up with industry best practices and technology. That's why we've put together a list of the 52 best conferences across the globe to attend in 2021. 34 RESOURCES FOR EMPLOYEE CYBERSECURITY TRAINING Small businesses need to train their employees, but they often have limited resources. These nine free security awareness training options in alphabetical order can help fill that gap. 1. Cofense sample lesson. Cofense is a company providing solutions for TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
BUILDING A CYBERSECURITY BOARD REPORT: A 5-STEP GUIDECYBERSECURITY REPORT 2020CYBERSECURITY BALANCED SCORECARD2019 CYBERSECURITY REPORTCISCO ANNUAL CYBERSECURITY REPORT 2019CISCO CYBERSECURITY REPORT 2019GARTNER CYBERSECURITY REPORT Here are 5 best practices for building a cybersecurity Board report: 1. Follow cybersecurity reporting guidelines. The Securities and Exchange Commission (SEC) provides guidance to companies regarding the responsibility of reporting to shareholders and the Board of directors, and heavily stresses the importance of cyber-relateddisclosures.
INHERENT RISK VS. RESIDUAL RISK: WHAT’S THE DIFFERENCE? Inherent risk is the amount of risk that exists in the absence of controls. In other words, before an organization implements any countermeasures at all, the risk they face is inherent risk. Residual risk is the risk that remains after controls are accounted for. It’s the risk that remains after your organization has taken properprecautions.
THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good PATCHING CADENCE ISSUE RESOLUTION If a “Vulnerability Found” is patched within 45 (high severity), 60 (medium), and 120 days (low severity) after CVE publish date (Last observed) there will be no “CVE Patching Cadence” findings created and the original “Vulnerability Found” finding will be removed from the scorecard (either based on a remediation request or organically after 45 days after the date of last observation). SECURITY RATINGS & CYBERSECURITY RISK MANAGEMENTPRODUCTSSOLUTIONSCUSTOMERSPARTNERSRESOURCESCOMPANY See what a hacker sees. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees. HOW TO PERFORM AN INFORMATION SECURITY GAP ANALYSIS Here are the four steps that are necessary for every information security gap analysis: 1. Select an industry-standard security framework. By selecting an industry-standard security framework, you will have the baseline best practices that you can measure and compare against your own security program. One of the most common frameworksis the
52 OF THE BEST CYBERSECURITY CONFERENCES TO ATTEND IN 2021 For business and security leaders working to drive effective cybersecurity programs, it’s important to keep up with industry best practices and technology. That's why we've put together a list of the 52 best conferences across the globe to attend in 2021. 34 RESOURCES FOR EMPLOYEE CYBERSECURITY TRAINING Small businesses need to train their employees, but they often have limited resources. These nine free security awareness training options in alphabetical order can help fill that gap. 1. Cofense sample lesson. Cofense is a company providing solutions for TOP 20 CYBERSECURITY KPIS TO TRACK IN 2021 Security ratings: Often the easiest way to communicate metrics to non-technical colleagues is through an easy-to-understand score. SecurityScorecard’s security ratings give your company an A-F letter grade on 10 security categories (network security, DNS health, patching cadence, cubit score, endpoint security, IP reputation, webapplication
A VENDOR RISK MANAGEMENT (VRM) QUESTIONNAIRE TEMPLATE A Vendor Risk Management Questionnaire Template. Vendor risk management becomes more important every year. Increasingly, enterprise IT incorporates a complex, interconnected system of cloud-based storage and application resources. Leveraging the cloud’s speed and volume to reduce operational overhead increases compliance risk inequal measure.
BUILDING A CYBERSECURITY BOARD REPORT: A 5-STEP GUIDECYBERSECURITY REPORT 2020CYBERSECURITY BALANCED SCORECARD2019 CYBERSECURITY REPORTCISCO ANNUAL CYBERSECURITY REPORT 2019CISCO CYBERSECURITY REPORT 2019GARTNER CYBERSECURITY REPORT Here are 5 best practices for building a cybersecurity Board report: 1. Follow cybersecurity reporting guidelines. The Securities and Exchange Commission (SEC) provides guidance to companies regarding the responsibility of reporting to shareholders and the Board of directors, and heavily stresses the importance of cyber-relateddisclosures.
INHERENT RISK VS. RESIDUAL RISK: WHAT’S THE DIFFERENCE? Inherent risk is the amount of risk that exists in the absence of controls. In other words, before an organization implements any countermeasures at all, the risk they face is inherent risk. Residual risk is the risk that remains after controls are accounted for. It’s the risk that remains after your organization has taken properprecautions.
THE FEDERAL GOVERNMENT’S PUSH TO CREATE A RESILIENT The Federal Government’s Push to Create a Resilient Industrial Base. Sun Tzu once said, “know thy enemy and know yourself.”. To this advice, cybersecurity professionals would likely add, “know thy friends.”. The recent high-profile cybersecurity incidents involving SolarWinds, Accellion, and Microsoft have made it clear that good PATCHING CADENCE ISSUE RESOLUTION If a “Vulnerability Found” is patched within 45 (high severity), 60 (medium), and 120 days (low severity) after CVE publish date (Last observed) there will be no “CVE Patching Cadence” findings created and the original “Vulnerability Found” finding will be removed from the scorecard (either based on a remediation request or organically after 45 days after the date of last observation). SECURITYSCORECARD SPRING 2021 PRODUCT RELEASE SecurityScorecard empowers you to see and understand cybersecurity risk in your organization and across your ecosystem with 360° visibility and seamless workflow integration with your security stack. ENTERPRISE CYBERSECURITY SOLUTIONS Build a secure ecosystem. Cyber-attacks are increasing in frequency and severity. Data breaches are an inevitable cost of doing business in today’s digital economy, and ecosystem risk management is the smartest approach for minimizing impact. Savvy enterprises leverage the best threat intelligence data available to instantly assess and continuously monitor their own security posture as well SPRING 2021 PRODUCT RELEASE: INTEGRATE360° MARKETPLACE NOTES Integrate360° Marketplace . Take your security to the next level with 40+ integrations, additional data, & service providers . Integrate360° is SecurityScorecard’s marketplace of integrations that work with what you have. Discover and deploy integrated solutions to optimize your security workflows, access even more security intelligence, and accelerate risk mitigation. SPRING 2021 PRODUCT RELEASE: ATLAS NOTES Evidence Locker. Open exchange of VRM data to automate and accelerate vendor risk security assessments. Evidence Locker is your single source for TPRM documentation, allowing teams to automatically populate vendor and compliance questionnaires with stored data by exchanging this information between Atlas and Ratings. SECURITYSCORECARD ANNOUNCES NEXT GEN SECURITY SIGNALS No waiting, 100% Free. Get your personalized scorecard today. Get your free scorecard and learn how you stack up across 10 risk categories. Answer a few simple questions and we'll instantly send your score to your business email. KPIS FOR SECURITY OPERATIONS & INCIDENT RESPONSE In today’s constantly changing threat landscape, senior leadership needs to work closely with the security team to create key performance indicators (KPIs) for security operations and incident response to understand your current and future cybersecurity posture. ZAPIER | SECURITYSCORECARD The attack surface keeps on growing inline with the cybersecurity talent shortage and the number of technologies required to defend businesses from cyberthreats. ZENDESK (COMING SOON) IT Service Management (ITSM) Security and IT teams work in Zendesk to collaborate on issue and ticket resolution. Empower your team to work more productively and efficiently with SecurityScorecard’s app for Zendesk by setting up alerts based on changes withinSecurityScorecard.
MICROSOFT TEAMS (COMING SOON) Workflow Automation. Seamlessly collaborate with your team to mitigate risk based on changes in SecurityScorecard. This SecurityScorecard app for Microsoft Teams app lets you set up notifications in designated channels in Microsoft Teams using our Rule Builder. INTEGRATE360° MARKETPLACE APPS INTO YOUR SECURITY We are always looking to add new integrations and apps to augment your SecurityScorecard experience. You can request new apps right from the platform by selecting the Request new apps button in Integrate360° Marketplace.. This will take you to the SecurityScorecard Customer Ideas Portal, where you can add your request on our form. This website uses cookies to ensure you get the best experience. MoreInfo
OK!
Prioritizing Risk and Business Continuity with Cybereason - 04/21 @ 9am EST. Sign Up Now -->X
SecurityScorecard
Menu
* Free Score
* Request a Demo
* Platform
* Platform Overview
* Security Ratings
* API Connectors
* Atlas
* ThreatMarket
* Solutions
Capabilities
* Overview
* Vendor Risk Management * Executive-Level Reporting* Self Assessment
* Cyber Insurance
* Compliance
* Threat ReconnaissanceIndustries
* Overview
* Financial
* Insurance
* Technology
* Retail
* Healthcare
* Government
* Enterprise
* Customers
* Partners
* Alliance Partners
* Global Partner Program* Resources
* Search and Filter
* Analyst Reports
* Case Studies
* Data Sheets
* Ebooks
* Reports
* Tools
* Trust Portal
* Videos
* Webinars
* White Papers
* Company
* Careers
* Understanding Your Scorecard* Company Overview
* History
* Leadership
* Customer Success
* Press Mentions
* Press Releases
* Events
* Project Escher
* Contact Us
* Login
* Blog
* Contact
* HUB
* Search
1,000,000+ Companies Rated UNDERSTAND AND REDUCE RISK WITH THE WORLD’S MOST EXPANSIVE & SCALABLE CYBERSECURITY RATINGS PLATFORM.Watch the Video
Get Instant Score
SEE WHAT A HACKER SEES. Constantly emerging sophisticated cyber attacks jeopardize your business every minute of every day. SecurityScorecard instantly identifies vulnerabilities, active exploits, and advanced cyber threats to help you rigorously protect your business and strengthen your security posture – from an outside-in perspective, enabling you to see what a hacker sees.Take the Tour
* SECURITY RATINGS
* API CONNECTORS
* ATLAS
* THREATMARKET
Featured Resource
THE FORRESTER NEW WAVE™: 2018 CYBERSECURITY RISK RATING SOLUTIONS Download this new Forrester analyst report to gain bleeding-edge insight into what security risk ratings can do for your organization today, and why SecurityScorecard's offering leads the pack. Get the Analyst Report Now No Waiting, 100% Free GET YOUR PERSONALIZED SCORECARD TODAY Get your free scorecard and learn how you stack up across 10 categories of risk. Answer a few simple questions and instantly receive your score in your business email.Get It Now
BEST-OF-BREED CAPABILITIES DELIVER MEASURABLE RESULTS. Don’t settle for just a cybersecurity score. To counter advanced threats, your business needs telemetry, threat intelligence, and collaboration tools to actively identify vulnerabilities, quickly remediate exploits, and continuously monitor your ecosystem. VENDOR RISK MANAGEMENT Get instant visibility into the security posture of your vendors and business partners. We enable enterprises to take control of risk across their entire ecosystem by continuously monitoring internal systems and vendor environments.Learn More
EXECUTIVE-LEVEL REPORTING _Effectively_ report on your cybersecurity risk to the Board and C-Suite. Have more productive conversations about cyber risk in an increasingly complex regulatory landscape. Create a common language and reporting framework that is easily understandable across yourorganization.
Learn More
SELF ASSESSMENT
Enterprise visibility is often restricted to an inside view of security posture. Our platform enables you to discover, monitor, and report on the cyberhealth of your IT infrastructure from the outside-in - see what a hacker sees.Learn More
CYBER INSURANCE
Insurance providers leverage our platform when underwriting cyber insurance policies for their customers. SecurityScorecard enables enterprises to take control of their risk profile while giving insurers visibility into the cyberhealth of their prospects andpolicyholders.
Learn More
COMPLIANCE
SecurityScorecard enables organizations to easily prove and maintain compliance with leading regulation and standards mandates including PCI, NIST, SOX, GDPR, and many others. Eliminate compliance reporting headaches and minimize the risk of compliance findings and penalties against your business.Learn More
THREAT RECONNAISSANCE We collect and analyze threat signals across the public web, dark web, our global sensor network, and threat intelligence feeds. With the largest and highest quality dataset in the industry, our platform delivers the most accurate security ratings and detailed findingspossible.
Learn More
YOU'RE IN _SMART_ COMPANY View All Customer Stories KEEPING A PULSE ON SECURITYWhat’s New
WHAT ARE SECURITY RATINGS? BLOG • APRIL 14, 2020 In October 2019, Moody’s, the globally recognized business and financial services company, presented “The Financial and Credit Implications of Cyber Risk” at the EnergyTech 2019 Conference. According to the presentation, cyber attacks and the associated risks lead to financial impacts that undermine credit scores, so organizations need to evaluate the operat...Read Blog Post
Event
PRIORITIZING RISK AND BUSINESS CONTINUITY DURING TIMES OF UNCERTAINTY Apr 21 2020 @ 9:00 ESTPress Mentions
TIPS TO IMPROVE NETWORK SECURITY VISIBILITY Posted April 17, 2020Press Mentions
10 HOT CYBERSECURITY COMPANIES TO FOLLOW IN MAY 2020 Posted April 17, 2020Show More
Press Mentions
TIPS TO IMPROVE NETWORK SECURITY VISIBILITY Posted April 17, 2020Press Mentions
10 HOT CYBERSECURITY COMPANIES TO FOLLOW IN MAY 2020 Posted April 17, 2020Press Releases
SECURITYSCORECARD STRENGTHENS COMMITMENT TO HEALTHCARE ORGANIZATIONS; JOINS H-ISAC TO OFFER FREE SELF-MONITORING AND PREFERRED PRICING TOH-ISAC MEMBERS
Posted April 16, 2020Press Mentions
IT SECURITY RISK MANAGEMENT BEST PRACTICES Posted April 14, 2020Press Mentions
‘PEOPLE ARE DESPERATE’: FRAUDSTERS TARGET VULNERABLE TRUCKERS WITHCOVID SCAMS
Posted April 14, 2020Blog
WHAT ARE SECURITY RATINGS? Posted April 14, 2020 Return Home SecurityScorecard 111 West 33rd Street. FLR 11 New York, NY 10001 info@securityscorecard.io United States: (800) 682-1707 International: +1 (646) 809-2166* Platform
* Solutions
* Customers
* Partners
* Resources
* Company
* Login
* Blog
* Contact
� 2020 SecurityScorecard Terms of Use Privacy PolicyPatents Trust
* YouTube
Close
Site Search
Search
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0
