Are you over 18 and want to see adult content?
More Annotations
A complete backup of westonbrands.com
Are you over 18 and want to see adult content?
A complete backup of proxdynamics.com
Are you over 18 and want to see adult content?
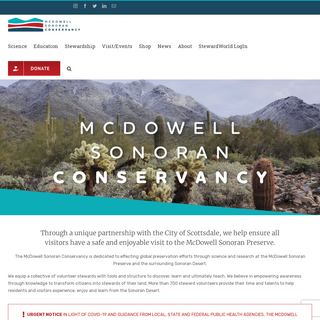
A complete backup of mcdowellsonoran.org
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of woolandthegang.com
Are you over 18 and want to see adult content?

A complete backup of alberthammond.com
Are you over 18 and want to see adult content?

A complete backup of fromthetrenchesworldreport.com
Are you over 18 and want to see adult content?

A complete backup of libertybasic.com
Are you over 18 and want to see adult content?
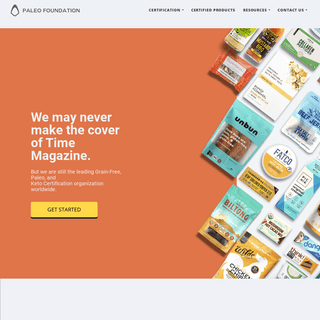
A complete backup of paleofoundation.com
Are you over 18 and want to see adult content?
Text
NETWORK REPORTING
Network Reporting. Every day, Shadowserver sends custom remediation reports to more than 6000 vetted subscribers, including over 131 national governments in 173 countries and many Fortune 500 companies. These reports are detailed, targeted, relevant and free. To become better informed about the state of your networks and their security OPEN PORTMAPPER REPORT The analogous shell command to mimic our portmapper scan is: rpcinfo -T udp -p And the analogous shell command that mimics our probe of the mountd program is: showmount -e For simplicity, the programs in the output of the portmapper scan are kept numeric, but below is a mapping of common program numbers to names: Program Number. ACCESSIBLE SMB REPORT This report identifies hosts that have an SMB instance running on port 445/TCP that are accessible on the Internet. This service should not be exposed to the Internet. For more details behind the scan methodology and a daily update of global SMB scan statistics please ACCESSIBLE VNC REPORT This report identifies hosts that have a VNC instance running on port 5900/TCP that are accessible on the Internet. If improperly configured, VNC may allow remote access to a desktop in an unintended manner. For more details behind the scan methodology and a daily update of global VNC scan statistics please visit our dedicated VNCscan page.
OPEN LDAP TCP REPORT This report identifies hosts that have an LDAP instance running on port 389/TCP that are accessible on the Internet. These hosts are often Active Directory servers. The data disclosed by the server could reveal large amounts of information about the network that the serverresides on.
NTP MONITOR REPORT
This report identifies NTP servers that have the potential to be used in amplification attacks by criminals that wish to perform denial of service attacks. The NTP monitor command is a Mode 7 query for MON_GETLIST_1. To manually test if a system is vulnerable to this, you can use the command: ntpdc -n -c monlist For more details behindthe
HAFNIUM EXCHANGE VICTIM SPECIAL REPORT This Special Report contains information on potential victims of HAFNIUM Microsoft Exchange Server breaches. You can read more on the background of HAFNIUM and this report in a blog post here. Shadowserver Special Reports are unlike all of our other standard free daily network reports. They do not cover a specific time period.Instead, we
HAS THE SUN SET ON THE NECURS BOTNET? ACCESSIBLE XDMCP SERVICE REPORT This report identifies hosts that have the X Display Manager service running and accessible on the Internet. Our probe tests to see if the X Display Manager is accessible by sending a “Query” packet to the XDMCP port (177/UDP) and listening for the responses. The responses received are typically either of the “Willing” type, which means THE SHADOWSERVER FOUNDATIONNEWS & INSIGHTSSTATISTICSBECOME A SPONSORCONTACT USSUBSCRIBE TO REPORTSMEDIA COVERAGE The Shadowserver Foundation. The Shadowserver Foundation is a nonprofit security organization working altruistically behind the scenes to make the Internet more secure for everyone. Our Story URGENT APPEAL FOR FINANCIAL SUPPORT.NETWORK REPORTING
Network Reporting. Every day, Shadowserver sends custom remediation reports to more than 6000 vetted subscribers, including over 131 national governments in 173 countries and many Fortune 500 companies. These reports are detailed, targeted, relevant and free. To become better informed about the state of your networks and their security OPEN PORTMAPPER REPORT The analogous shell command to mimic our portmapper scan is: rpcinfo -T udp -p And the analogous shell command that mimics our probe of the mountd program is: showmount -e For simplicity, the programs in the output of the portmapper scan are kept numeric, but below is a mapping of common program numbers to names: Program Number. ACCESSIBLE SMB REPORT This report identifies hosts that have an SMB instance running on port 445/TCP that are accessible on the Internet. This service should not be exposed to the Internet. For more details behind the scan methodology and a daily update of global SMB scan statistics please ACCESSIBLE VNC REPORT This report identifies hosts that have a VNC instance running on port 5900/TCP that are accessible on the Internet. If improperly configured, VNC may allow remote access to a desktop in an unintended manner. For more details behind the scan methodology and a daily update of global VNC scan statistics please visit our dedicated VNCscan page.
OPEN LDAP TCP REPORT This report identifies hosts that have an LDAP instance running on port 389/TCP that are accessible on the Internet. These hosts are often Active Directory servers. The data disclosed by the server could reveal large amounts of information about the network that the serverresides on.
NTP MONITOR REPORT
This report identifies NTP servers that have the potential to be used in amplification attacks by criminals that wish to perform denial of service attacks. The NTP monitor command is a Mode 7 query for MON_GETLIST_1. To manually test if a system is vulnerable to this, you can use the command: ntpdc -n -c monlist For more details behindthe
HAFNIUM EXCHANGE VICTIM SPECIAL REPORT This Special Report contains information on potential victims of HAFNIUM Microsoft Exchange Server breaches. You can read more on the background of HAFNIUM and this report in a blog post here. Shadowserver Special Reports are unlike all of our other standard free daily network reports. They do not cover a specific time period.Instead, we
HAS THE SUN SET ON THE NECURS BOTNET? ACCESSIBLE XDMCP SERVICE REPORT This report identifies hosts that have the X Display Manager service running and accessible on the Internet. Our probe tests to see if the X Display Manager is accessible by sending a “Query” packet to the XDMCP port (177/UDP) and listening for the responses. The responses received are typically either of the “Willing” type, which means CHANGES IN SINKHOLE AND HONEYPOT REPORT TYPES AND FORMATS Changes in Sinkhole and Honeypot Report Types and Formats. April 1, 2021. Over the years, Shadowserver’s report list has grown considerably from when we originally started. Our daily reports now number over 80 distinct types and they include data from a large amount of sources, including sinkholes, sandboxes, scans, honeypotsand several others.
ACCESSIBLE ADB REPORT The IP address of the device in question. protocol. Protocol that the ADB response came on (always TCP) port. Port that the ADB response came from (5555/TCP) hostname. Reverse DNS name of the device in question. tag. This will always be adb.OPEN SNMP REPORT
Open SNMP Report. This report identifies hosts with SNMPv2 publicly accessible, that are responding to the community “public”, and that have the potential to be used in amplification attacks by criminals who wish to perform denial of service attacks. The OID being probed for is 1.3.6.1.2.1.1.1.0 (sysDescr) and if the host responds tothat
ACCESSIBLE VNC REPORT This report identifies hosts that have a VNC instance running on port 5900/TCP that are accessible on the Internet. If improperly configured, VNC may allow remote access to a desktop in an unintended manner. For more details behind the scan methodology and a daily update of global VNC scan statistics please visit our dedicated VNCscan page.
LEGACY: COMPROMISED HOST REPORT This report provides an extensive combination of information about a Compromised Host. Many times, there are three IPs listed in the report, because we will have the Command and Control that is controlling the systems, the Attacking IP address, and finally the Compromised IP address. Some of the botnets will have the individualbots report back
HAS THE SUN SET ON THE NECURS BOTNET? Private sector partners Microsoft and Bitsight announced their disruption of the Necurs botnet on March 10th 2020. Shadowserver supported the operation, through the use of our Registrar of Last Resort (RoLR) for helping to deal with the millions of potential DGA C2 domains involved, and by making available our victim remediationreporting channels.
VULNERABLE ISAKMP REPORT This report identifies hosts that have a vulnerable IKE service accessible on the Internet. For more information, please see the Cisco Security Advisory. For more details behind the scan methodology and a daily update of global ISAKMP scan statistics please visit our dedicated Vulnerable ISAKMP scan page. For more information on ourscanning
BRUTE FORCE ATTACK REPORT Brute Force Attack Report. This report identifies hosts that have been observed performing brute force attacks, using SISSDEN’s network of honeypots. One of these honeypot type sensors is dedicated to detecting SSH and telnet attacks against network devices. These attacks typically involve brute-forcing credentials to obtain access.BLOCK LIST REPORT
This report is the aggregation of a variety of different Block/Deny list providers, for end-users’ reference. The purpose in sharing this information is to alert end-users that specific IP addresses of theirs have been flagged by providers as possibly malicious, and different services might LEGACY: BOTNET URL REPORT These URLs could up updates for a botnet, a link to something that the criminals thought was interesting, or even vacation pictures of the criminals. Because it is difficult to know what value anyone may have for any specific URL, no whitelisting occurs to filter any of the information. This means that the result of the report will includeSearch
* News & Insights
* Statistics
* Become a Sponsor
* Contact Us
* Subscribe to Reports* Who We Are
* What We Do
* Who We Serve
* Who We Are
* What We Do
* Who We Serve
* Subscribe to Reports The Shadowserver Foundation is a nonprofit security organization working altruistically behind the scenes to make the Internet more secure for everyone. Our Story URGENT APPEAL FORFINANCIAL SUPPORT
WHAT WE DO
We collect vast amounts of threat data, send tens of thousands of free daily remediation reports, and cultivate strong reciprocal relationships with NETWORK PROVIDERS, NATIONAL GOVERNMENTS and LAW ENFORCEMENT. We bring malicious activities and abusable vulnerabilities out of the shadows, expedite their remediation and help to better secure the Internet. Find Out More4-5 million
IP addresses sinkholed per day, across 400 DIFFERENT MALWARE FAMILYVARIANTS
71
different data sets generated through FULL DAILY INTERNET-WIDE IPV4SCANNING
4 billion
IPv4 addresses scanned on 45 ports each per day. 139 MILLION hostsrespond
WHO WE SERVE
NATIONAL CSIRTS
We give CSIRTs the vantage point to understand the big picture of what’s happening on the networks they’re responsible for.National CSIRTs
INDUSTRY SECTORS
We work with business and tech firms, financial institutions and academia, to improve network security, enhance product capability, and advance threat research.Industry Sectors
LAW ENFORCEMENT
We partner with law enforcement to help protect victims, take down global cybercrime infrastructures and prevent attacks before theyoccur.
Law Enforcement
NEWS & INSIGHTS
*
NEW DATA CENTER REQUIREMENTS - CAN YOU HELP HOST SHADOWSERVER?April 22, 2020
Shadowserver urgently needs to move our current data center by August 2020. We are blogging our data center requirements for hosting and colocation providers, or other companies who might be able to help provide a new home for our public benefit services for the global Internet. Please reach out and get in touch if you can help.Read More
�
*
DATA CENTER MIGRATION DEADLINE EXTENDED DUE TO COVID-19April 9, 2020
The original deadline for Shadowserver to move our data center has been extended from May 26th to August 31st 2020, due to the worsening COVID-19 pandemic and Silicon Valley 'Shelter in Place' lockdowns. This extension provides us with some much needed additional time to continue raising funding for our 2020 operations, such as the recently received donation from cryptocurrency exchange BitMEX.Read More
�
*
PROGRESS IN 2020 FUNDING CHALLENGE - THANKS TO FANTASTIC GLOBAL SUPPORTERS, BUT MORE HELP STILL NEEDED!April 2, 2020
Our first status update on the critical initial milestone in Shadowserver's urgent 2020 funding challenge. Great progress from our awesome community, with particular thanks to philanthropist Craig Newmark, but more help still needed to fully secure our data center operations in 2020. Join with us to continue protecting victims of cybercrime and help protect the Internet.Read More
�
More News & InsightsTOOLS & RESOURCES
Get reports about your network »Common
questions » Statistics on malware, DDoS attacks, more »Press kit »
Media coverage »
Follow us on Twitter » Shadowserver @Shadowserver Apr 20 We have a free whitelist lookup service to test an executable file against a list of known software apps. Over 16.8… https://t.co/3EqP7GqpIf HELP US MAKE THE INTERNET MORE SECURE The Shadowserver Foundation is an altruistic, public benefit, nonprofit organization funded by sponsorships, grants, and charitabledonations.
Become a Sponsor
* Home
* Who We Are
* What We Do
* Who We Serve
* News & Insights
* Statistics
* Common Questions
* Become a Sponsor
* Contact Us
� 2020 The Shadowserver FoundationPrivacy & Terms
Shadowserver Wiki » Shadowserver uses cookies to gather analytics. This allows us to measure how the site is used and improve the experience for our users. For more information about cookies and how Shadowserver uses them, see our privacy policy . We need your consent to use cookies in this way on your device.Accept Decline
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0