Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.xhamster.desi
Are you over 18 and want to see adult content?

A complete backup of amateuralbum.net
Are you over 18 and want to see adult content?

A complete backup of thefappening.pro
Are you over 18 and want to see adult content?

A complete backup of www.nerdpervert.com
Are you over 18 and want to see adult content?

A complete backup of www.nakenprat.com
Are you over 18 and want to see adult content?

A complete backup of www.www.zenra.net
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://chinaq.tv/th/
Are you over 18 and want to see adult content?

A complete backup of https://sgphkgmls247.blogspot.com/
Are you over 18 and want to see adult content?
A complete backup of https://www.accessify.com/k/kuttymovies.in
Are you over 18 and want to see adult content?
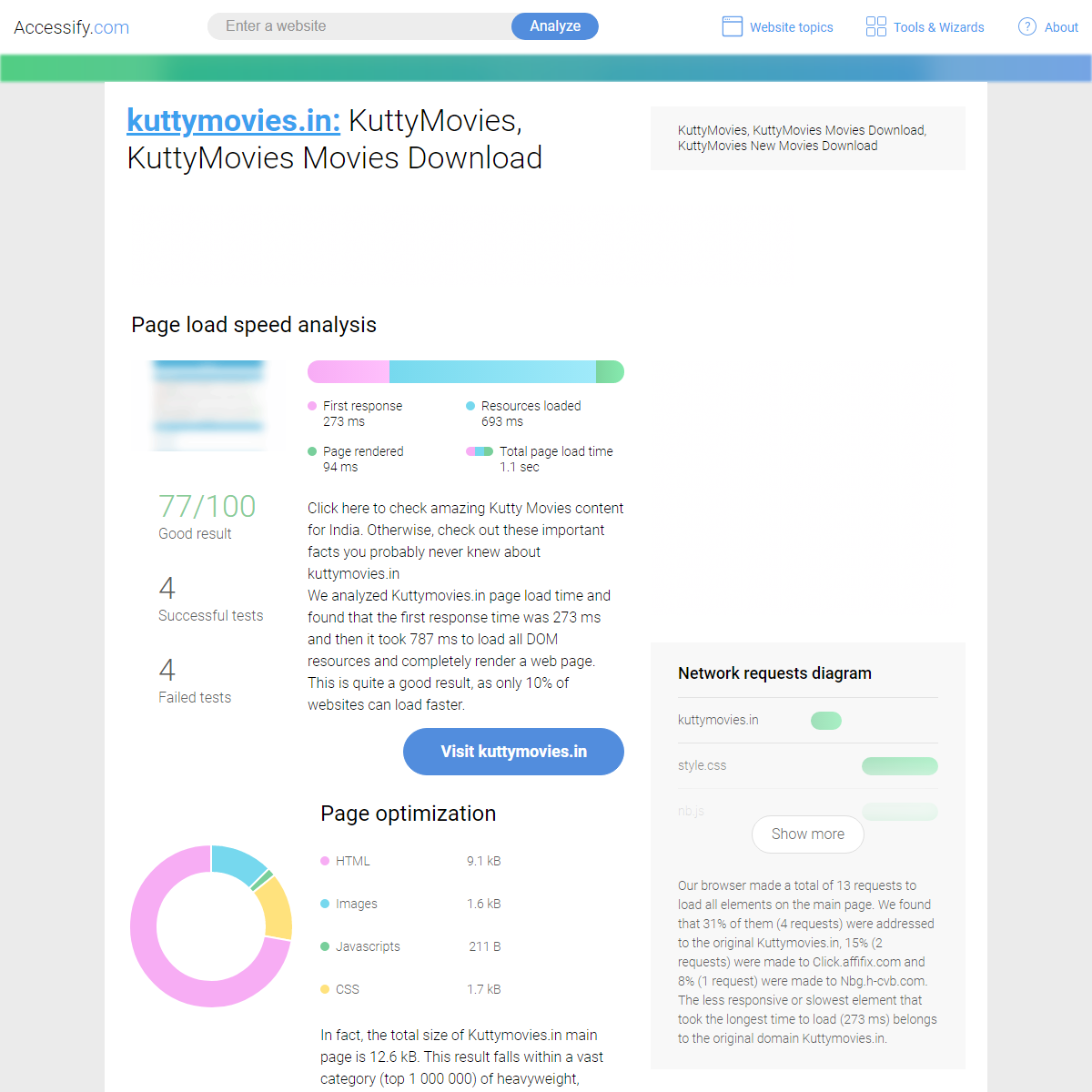
A complete backup of https://kontactr.com/website/site/extremotvplay.com
Are you over 18 and want to see adult content?
A complete backup of https://fotougynokseg.lap.hu/
Are you over 18 and want to see adult content?

A complete backup of https://chinaq.tv/aurora/
Are you over 18 and want to see adult content?

A complete backup of https://agriwell.mahaonline.gov.in/
Are you over 18 and want to see adult content?

A complete backup of https://balkanje.com/tag/sardine/
Are you over 18 and want to see adult content?

A complete backup of https://nacionalbox.com/
Are you over 18 and want to see adult content?

A complete backup of https://taketones.com/
Are you over 18 and want to see adult content?
Text
SEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Indian Statistical Institute, Kolkata. AY 2017-2018 S1 -- Computing for Data Sciences-- PGDBA, Year 1 AY 2016-2017 S2 -- Foundations of Data Science -- MTech CS, Year 1--
SEN GUPTA | SOURAV
Panel Moderator, Women in Asia Blockchain Event, Science Park (2018) SCSE Faculty Representative, SCS Gala, IT Leader Awards (2019) Member, Working Group, Introduction to Blockchain Technology, RBI and IDRBT (2017) Co-organizer -- Workshops and training programs in Free and Open Source Software. LINEAR ALGEBRA EXPLAINED IN FOUR PAGES 2 Instead of writing ~y= T A(~x) for the linear transformation T A applied to the vector ~x, we simply write ~y= A~x. Applying the linear transformation T A to the vector ~xcorresponds to the product of the matrix Aand the column vector ~x. We say T Ais represented by the matrix A. You can think of linear transformations as “vector functions” and describeBSTAT | NUMANA2016
Resources for Scribes It is preferred that the scribes are typeset in LaTeX -- but it is NOT mandatory at all. In case you are not comfortable with LaTeX, or do not want to spend the time to learn it, no worry -- submit the scribes as neatly hand-written documents. KNOW THY COMPLEXITIES! Know Thy Complexities! www.bigocheatsheet.com Big-O Complexity Chart Excelent Good Fair Bad Horrible O(1), O(log n) O(n) O(n log n) O(n^2)O(n!) O(2^n)
THE FUNDAMENTAL THEOREM OF LINEAR ALGEBRA GILBERT STRANG The dimensions obey the most important laws of linear algebra: dim R( A) = dim R( AT) and dim R( A) + dim N( A) = n. When the row space has dimension r, the nullspace has dimension n -r. Elimination identifies r pivot variables and n -r free variables.Those variables MORE ON SVD AND GRAM-SCHMIDT ORTHOGONALIZATION 6.2 Approximation by low rank matrices Expanding A= U VT we get, A= Xl i=1 ˙ iu~ iv~ i T where l= minfm;ngand u~ i and v~ i are the i-th column of Uand V respectively.The sum goes to l because the other terms will be zeroed out by .This shows that the matrix A(say of rank CDS SCRIBING: LECTURE 10 Algorithm An algorithm is a sequence of computational steps performed on a data input to generate a required result or solve a problem. It is an abstraction of program to be executed on a physical ROSSMANN SALES PREDICTION 14. Competition open since year Interval 1900-2015 15. Promo2 (Long Term Promotion) Nominal 0,1 16. Promo2 since week Interval 1-50 17. Promo2 since year Interval 2009-2015 SEN GUPTA | SOURAVSOURAV SEN GUPTATEACHINGRESEARCHACTIVITIESRANDOMCDS2017 I am a Teacher and Researcher, positioned precariously at the confluence of Computer Science, Mathematics and Engineering. While my research area and interest revolves around the "science of security" (primarily focused on cryptology), I love to teachSEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Indian Statistical Institute, Kolkata. AY 2017-2018 S1 -- Computing for Data Sciences-- PGDBA, Year 1 AY 2016-2017 S2 -- Foundations of Data Science -- MTech CS, Year 1--
SEN GUPTA | SOURAV
Panel Moderator, Women in Asia Blockchain Event, Science Park (2018) SCSE Faculty Representative, SCS Gala, IT Leader Awards (2019) Member, Working Group, Introduction to Blockchain Technology, RBI and IDRBT (2017) Co-organizer -- Workshops and training programs in Free and Open Source Software. LINEAR ALGEBRA EXPLAINED IN FOUR PAGES 2 Instead of writing ~y= T A(~x) for the linear transformation T A applied to the vector ~x, we simply write ~y= A~x. Applying the linear transformation T A to the vector ~xcorresponds to the product of the matrix Aand the column vector ~x. We say T Ais represented by the matrix A. You can think of linear transformations as “vector functions” and describeBSTAT | NUMANA2016
Resources for Scribes It is preferred that the scribes are typeset in LaTeX -- but it is NOT mandatory at all. In case you are not comfortable with LaTeX, or do not want to spend the time to learn it, no worry -- submit the scribes as neatly hand-written documents. KNOW THY COMPLEXITIES! Know Thy Complexities! www.bigocheatsheet.com Big-O Complexity Chart Excelent Good Fair Bad Horrible O(1), O(log n) O(n) O(n log n) O(n^2)O(n!) O(2^n)
THE FUNDAMENTAL THEOREM OF LINEAR ALGEBRA GILBERT STRANG The dimensions obey the most important laws of linear algebra: dim R( A) = dim R( AT) and dim R( A) + dim N( A) = n. When the row space has dimension r, the nullspace has dimension n -r. Elimination identifies r pivot variables and n -r free variables.Those variables MORE ON SVD AND GRAM-SCHMIDT ORTHOGONALIZATION 6.2 Approximation by low rank matrices Expanding A= U VT we get, A= Xl i=1 ˙ iu~ iv~ i T where l= minfm;ngand u~ i and v~ i are the i-th column of Uand V respectively.The sum goes to l because the other terms will be zeroed out by .This shows that the matrix A(say of rank CDS SCRIBING: LECTURE 10 Algorithm An algorithm is a sequence of computational steps performed on a data input to generate a required result or solve a problem. It is an abstraction of program to be executed on a physical ROSSMANN SALES PREDICTION 14. Competition open since year Interval 1900-2015 15. Promo2 (Long Term Promotion) Nominal 0,1 16. Promo2 since week Interval 1-50 17. Promo2 since year Interval 2009-2015SEN GUPTA | SOURAV
Panel Moderator, Women in Asia Blockchain Event, Science Park (2018) SCSE Faculty Representative, SCS Gala, IT Leader Awards (2019) Member, Working Group, Introduction to Blockchain Technology, RBI and IDRBT (2017) Co-organizer -- Workshops and training programs in Free and Open Source Software.SEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Journal Papers. Security is an Architectural Design Constraint Prasanna Ravi, Zakaria Najm, Shivam Bhasin, Mustafa Khairallah, Sourav SEN GUPTA | SOURAVTRANSLATE THIS PAGE Random Facts. I spent most of my childhood and initial school days at two small/medium towns of West Bengal, India -- Raghunathganj (don't remember much) and Siliguri (can't recognize now). I loved my one-year stint as a PhD Candidate at the University of Washington, Seattle, where I was fortunate to work with two intriguing personalities -- Neal Koblitz and William Stein.SEN GUPTA | SOURAV
Course Information. In today's era of Information, 'Data' is the new driving force, provided we know how to extract relevant 'Intelligence'. This course will start with the core principles of Data Science, and will equip the students with the basic tools and techniques of data handling, exploratory data analysis, data visualization, data-based inference, and data-focused communication.BSTAT | NUMANA2016
Resources for Scribes It is preferred that the scribes are typeset in LaTeX -- but it is NOT mandatory at all. In case you are not comfortable with LaTeX, or do not want to spend the time to learn it, no worry -- submit the scribes as neatly hand-written documents. MEASUREMENTS, ANALYSES, AND INSIGHTS ON THE ENTIRE WWW ’20, April 20–24, 2020, Taipei, Taiwan Lee and Khan, et al. global state of the blockchain. This motivates us to study a public permissionless blockchain network as a complex system. A BLOCKCHAIN FRAMEWORK FOR INSURANCE PROCESSES A Blockchain Framework for Insurance Processes Mayank Raikwar∗, Subhra Mazumdar †, Sushmita Ruj , Sourav Sen Gupta†, Anupam Chattopadhyay ∗, and Kwok-Yan Lam ∗School of Computer Science and Engineering, Nanyang Technological University, Singapore 639798 Email: {mraikwar,anupam,kwokyan.lam}@ntu.edu.sg †Indian Statistical Institute, 203 Barrackpore Trunk AN INTRODUCTION TO ROC ANALYSIS An introduction to ROC analysis Tom Fawcett Institute for the Study of Learning and Expertise, 2164 Staunton Court, Palo Alto, CA 94306, USA Available online 19 December 2005 A TUTORIAL ON PRINCIPAL COMPONENT ANALYSIS A Tutorial on Principal Component Analysis Jonathon Shlens Google Research Mountain View, CA 94043 (Dated: April 7, 2014; Version 3.02) Principal component analysis (PCA) is a mainstay of modern data analysis - a black box that is widely used EXTREME GRADIENT BOOSTING (XGBOOST) On the basis, the prediction model ( ̂) can be written as the aggregation of all the prediction score for eac h tree for a sample (x).Particularly for i-th sample, where K is the number of trees, f is the function in the functional space 𝓕 and ℱ is the all possible set of tr ees having prediction score in each leaf, slightly different from decision tree which only contains decisio SEN GUPTA | SOURAVSOURAV SEN GUPTATEACHINGRESEARCHACTIVITIESRANDOMCDS2017 I am a Teacher and Researcher, positioned precariously at the confluence of Computer Science, Mathematics and Engineering. While my research area and interest revolves around the "science of security" (primarily focused on cryptology), I love to teachSEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Journal Papers. Security is an Architectural Design Constraint Prasanna Ravi, Zakaria Najm, Shivam Bhasin, Mustafa Khairallah, SouravSEN GUPTA | SOURAV
While I love teaching laboratory-based courses in Programming, my passion lies in teaching Discrete Mathematics, Number Theory, Algebra and Linear Algebra to Computer Science students. I have taught more than a dozen different courses at various levels of Computer Science and Mathematics. Since 2014, I have designed most of the courses thatI
SEN GUPTA | SOURAV
Panel Moderator, Women in Asia Blockchain Event, Science Park (2018) SCSE Faculty Representative, SCS Gala, IT Leader Awards (2019) Member, Working Group, Introduction to Blockchain Technology, RBI and IDRBT (2017) Co-organizer -- Workshops and training programs in Free and Open Source Software.SEN GUPTA | SOURAV
Course Information. In today's era of Information, 'Data' is the new driving force, provided we know how to extract relevant 'Intelligence'. This course will start with the core principles of Data Science, and will equip the students with the basic tools and techniques of data handling, exploratory data analysis, data visualization, data-based inference, and data-focused communication. LINEAR ALGEBRA EXPLAINED IN FOUR PAGES 2 Instead of writing ~y= T A(~x) for the linear transformation T A applied to the vector ~x, we simply write ~y= A~x. Applying the linear transformation T A to the vector ~xcorresponds to the product of the matrix Aand the column vector ~x. We say T Ais represented by the matrix A. You can think of linear transformations as “vector functions” and describe CDS SCRIBING: LECTURE 10 Algorithm An algorithm is a sequence of computational steps performed on a data input to generate a required result or solve a problem. It is an abstraction of program to be executed on a physical MORE ON SVD AND GRAM-SCHMIDT ORTHOGONALIZATION 6.2 Approximation by low rank matrices Expanding A= U VT we get, A= Xl i=1 ˙ iu~ iv~ i T where l= minfm;ngand u~ i and v~ i are the i-th column of Uand V respectively.The sum goes to l because the other terms will be zeroed out by .This shows that the matrix A(say of rank PUBLISHING UPPER HALF OF RSA DECRYPTION EXPONENT 28 S. Maitra, S. Sarkar, and S. Sen Gupta Input: Small encryption key e, Bitsize of primes lp,lq,andd0 with ld0 = lN Output: RSA parameters p,q,N,d 1 Pick a prime p at random with bit-size lp such that gcd(p− 1,e)=1; Pick a random number dpad of length 1 2 2 ld0 or less; Set d˜ 3 0 ← d0 +dpad; 4 Pick a random number k of length le with gcd(k,e)=1; Set x ← e− (k(p − 1))−1 mod e5; ROSSMANN SALES PREDICTION 14. Competition open since year Interval 1900-2015 15. Promo2 (Long Term Promotion) Nominal 0,1 16. Promo2 since week Interval 1-50 17. Promo2 since year Interval 2009-2015 SEN GUPTA | SOURAVSOURAV SEN GUPTATEACHINGRESEARCHACTIVITIESRANDOMCDS2017 I am a Teacher and Researcher, positioned precariously at the confluence of Computer Science, Mathematics and Engineering. While my research area and interest revolves around the "science of security" (primarily focused on cryptology), I love to teachSEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Journal Papers. Security is an Architectural Design Constraint Prasanna Ravi, Zakaria Najm, Shivam Bhasin, Mustafa Khairallah, SouravSEN GUPTA | SOURAV
While I love teaching laboratory-based courses in Programming, my passion lies in teaching Discrete Mathematics, Number Theory, Algebra and Linear Algebra to Computer Science students. I have taught more than a dozen different courses at various levels of Computer Science and Mathematics. Since 2014, I have designed most of the courses thatI
SEN GUPTA | SOURAV
Panel Moderator, Women in Asia Blockchain Event, Science Park (2018) SCSE Faculty Representative, SCS Gala, IT Leader Awards (2019) Member, Working Group, Introduction to Blockchain Technology, RBI and IDRBT (2017) Co-organizer -- Workshops and training programs in Free and Open Source Software.SEN GUPTA | SOURAV
Course Information. In today's era of Information, 'Data' is the new driving force, provided we know how to extract relevant 'Intelligence'. This course will start with the core principles of Data Science, and will equip the students with the basic tools and techniques of data handling, exploratory data analysis, data visualization, data-based inference, and data-focused communication. LINEAR ALGEBRA EXPLAINED IN FOUR PAGES 2 Instead of writing ~y= T A(~x) for the linear transformation T A applied to the vector ~x, we simply write ~y= A~x. Applying the linear transformation T A to the vector ~xcorresponds to the product of the matrix Aand the column vector ~x. We say T Ais represented by the matrix A. You can think of linear transformations as “vector functions” and describe CDS SCRIBING: LECTURE 10 Algorithm An algorithm is a sequence of computational steps performed on a data input to generate a required result or solve a problem. It is an abstraction of program to be executed on a physical MORE ON SVD AND GRAM-SCHMIDT ORTHOGONALIZATION 6.2 Approximation by low rank matrices Expanding A= U VT we get, A= Xl i=1 ˙ iu~ iv~ i T where l= minfm;ngand u~ i and v~ i are the i-th column of Uand V respectively.The sum goes to l because the other terms will be zeroed out by .This shows that the matrix A(say of rank PUBLISHING UPPER HALF OF RSA DECRYPTION EXPONENT 28 S. Maitra, S. Sarkar, and S. Sen Gupta Input: Small encryption key e, Bitsize of primes lp,lq,andd0 with ld0 = lN Output: RSA parameters p,q,N,d 1 Pick a prime p at random with bit-size lp such that gcd(p− 1,e)=1; Pick a random number dpad of length 1 2 2 ld0 or less; Set d˜ 3 0 ← d0 +dpad; 4 Pick a random number k of length le with gcd(k,e)=1; Set x ← e− (k(p − 1))−1 mod e5; ROSSMANN SALES PREDICTION 14. Competition open since year Interval 1900-2015 15. Promo2 (Long Term Promotion) Nominal 0,1 16. Promo2 since week Interval 1-50 17. Promo2 since year Interval 2009-2015SEN GUPTA | SOURAV
Course Information. In today's era of Information, 'Data' is the new driving force, provided we know how to extract relevant 'Intelligence'. This course will start with the core principles of Data Science, and will equip the students with the basic tools and techniques of data handling, exploratory data analysis, data visualization, data-based inference, and data-focused communication.SEN GUPTA | SOURAV
Official website of Sourav Sen Gupta. Cx4153 : Blockchain Technology. Technical Elective offered at the Third/Fourth Year level (in the First Semester of the Academic Year) for students in the undergraduate program at the School of Computer Science and Engineering, NTU.A1 | INT2PRO2014
Official website of Sourav Sen Gupta. Tests tests The tests constitute 80% of the total marks. There will be two tests over the duration of the course, and both the scores will be counted towards the computation of the final grade. A BLOCKCHAIN FRAMEWORK FOR INSURANCE PROCESSES A Blockchain Framework for Insurance Processes Mayank Raikwar∗, Subhra Mazumdar †, Sushmita Ruj , Sourav Sen Gupta†, Anupam Chattopadhyay ∗, and Kwok-Yan Lam ∗School of Computer Science and Engineering, Nanyang Technological University, Singapore 639798 Email: {mraikwar,anupam,kwokyan.lam}@ntu.edu.sg †Indian Statistical Institute, 203 Barrackpore Trunk ATTACK ON BROADCAST RC4 REVISITED Attack on Broadcast RC4 Revisited Subhamoy Maitra 1, Goutam Paul2, and Sourav Sen Gupta 1 Applied Statistics Unit, Indian Statistical Institute, Kolkata 700 108, India {subho,souravsg r}@isical.ac.in2 Department of Computer Science and Engineering, Jadavpur University, Kolkata 700 032, India goutam.paul@ieee.org Abstract.PGDBA | CDS2015
Timeline. 10 Oct 2015: Choice for the topic of the Project should be finalized.; 14 Nov 2015: Project Presentation (30 mins) and Question-Answer Session (10 mins).; 03 Dec 2015: Project Presentation (30 mins) and Question-Answer Session (10 mins).; 05 Dec 2015: Submission of the final Project Report due.; Project Ideas The groups may choose any of the following ideas for the course project, or LINEAR REGRESSION AND THE BIAS VARIANCE TRADEOFF MoHvaon • One of the most widely used techniques • Fundamental to many larger models – Generalized Linear Models – Collaboravefiltering
‘WHAT’S COOKING?’ ‘WHAT’S COOKING?’ A SNEAK PEEK INTO CLASSIFIERSAND WEB SCRAPING CDS 2015, Group 4 Bodhisattwa Prasad Majumder (11) Dattatreya Biswas (13) Keshav Sehgal (20) IN-HOSPITAL ICU MORTALITY PREDICTION MODEL In-hospital Intensive Care Unit Mortality Prediction Model COMPUTING FOR DATA SCIENCES GROUP 6: MANASWI VELIGATLA (24), NEETI POKHARNA (27), ROBIN SINGH (36), SAURABH RAWAL (42) REINFORCEMENT LEARNING FOR OPTIMIZED TRADE EXECUTION Reinforcement Learning for Optimized Trade Execution Yuriy Nevmyvaka yuriy.nevmyvaka@lehman.com Lehman Brothers, 745 Seventh Av., New York,NY 10019, USA
Sourav Sen Gupta
* Home
* About
* Research
* Teaching
* Publications
* Synergy
* School of CSE
* NTU Singapore
CURRENT POSITION
Lecturer (since 2018) | Profile @ SCSE NTU School of Computer Science and Engineering Nanyang Technological University, SingaporePREVIOUS POSITION
Visiting Lecturer and Lecturer (2014 to 2017) R C Bose Centre for Cryptology and Security Indian Statistical Institute, KolkataREACH ME AT
sg.sourav@ntu.edu.sg (Official @ NTU) sg.sourav@gmail.com (personal email) N4-02b-66 | Level 2, Block N4, SCSE, NTUABOUT ME ABOUT
I am a Researcher and Teacher, positioned precariously at the confluence of Computer Science, Mathematics and Engineering. While my research interest revolves around the "science of security" (primarily focused on cryptology), I love to teach the "art of analytics" (broadly dealing with data science).ACADEMIC POSITIONS
* Since 2018 : Lecturer -- School of Computer Science and Engineering, NTU Singapore * May-Dec 2017 : Visiting Lecturer -- R C Bose Centre, Indian Statistical Institute * 2014-2017 : Lecturer-cum-PDF -- R C Bose Centre, Indian Statistical Institute * 2011-2014 : Researcher -- Centre of Excellence in Cryptology, Indian Statistical Institute * 2010-2011 : Research-Fellow -- Applied Statistics Unit, Indian Statistical Institute * 2009-2010 : Researcher -- Applied Statistics Unit, Indian Statistical Institute * 2008–2009 : Teaching Assistant -- Dept. of Mathematics, Univ. ofWashington, Seattle
* Summer 2008 : Sessional Instructor -- Dept. of Pure Mathematics,Univ. of Waterloo
* 2006-2008 : Teaching Assistant -- Dept. of Pure Mathematics, Univ.of Waterloo
ACADEMIC BACKGROUND
* 2014 : PhD in Computer Science (Cryptology) -- Indian StatisticalInstitute
* 2008 : M.Math. in Pure Mathematics -- University of Waterloo * 2006 : B.E.Tel.E. in Electronics and Telecommunication Engg. --Jadavpur University
I will be glad to share a copy of my CV, with further professional details, if you are interested.RESEARCH RESEARCH
Owing to my interdisciplinary academic background, my research interests follow two apparently diverse tracks of Cryptology -- mathematical security analysis of cryptographic primitives towards discovering their security vulnerabilities, and efficient engineering of cryptographic designs for high performance. Currently, I am interested in applications of Machine Learning in various domains of Security, and the state-of-the-art developments in the emerging area of Bitcoin and Blockchain technologies. In addition to my primary research interests, I am also inclined towards topics in Number Theory that have close ties with cryptographic applications. Distribution of primes, primality testing algorithms, the factorization problem, lattice based analysis of cryptographic constructions, and topics in elliptic curve cryptography pique my interest. Time and again, I also like to explore elegant theoretical and computational problems in elementary Number Theory, Statistics and Data Science.TEACHING TEACHING
NTU SINGAPORE
Since January 2018, I have taught the following courses at Nanyang Technological University. * Fall 2018 -- Introduction to Computational Thinking (CE/CZ1003) --Example Classes
* Fall 2018 -- Computer Security / Systems Security (CE/CZ4062) --Part-Time Students
* Spring 2018 -- Data Science for Business (CE/CZ4073) -- Elective,Course Coordinator
* Spring 2018 -- Cryptography and Network Security (CE/CZ4024) --Part-Time Students
* Spring 2018 -- Operating Systems (CE/CZ2005) -- Laboratories andTutorial Sessions
ISI KOLKATA
Since Fall 2014, I have taught the following courses at Indian Statistical Institute, Kolkata. Please feel free to browse through the course websites to know more about the course format and contents. * Fall 2017 -- Computing for Data Sciences --PGDBA, First Year
* Spring 2017 -- Machine Learning -- MSc Data Science and MSc CS, RKM Vivekananda University * Spring 2017 -- Foundations of Data Science -- M.Tech. CS, First Year -- Informal Reading Course * Fall 2016 -- Computing for Data Sciences --PGDBA, First Year
* Fall 2016 -- Programming and Data Structures Laboratory -- M.Tech. CS, First Year * Spring 2016 -- Numerical Analysis --B.Stat., First Year
* Fall 2015 -- Computing for Data Sciences --PGDBA, First Year
* Fall 2015 -- Programming and Data Structures Laboratory -- M.Tech. CS, First Year * Fall 2015 -- Foundations of Data Science -- M.Tech. CS, Second Year -- Informal Reading Course * Spring 2015 -- Numerical Analysis -- B.Stat., First Year -- Jointly with Prof. Subhamoy Maitra * Fall 2014 -- Introduction to Programming -- M.Tech. CS, First Year PUBLICATIONS PUBLICATIONS The following is a select list of my publications. Please feel free tocheck my DBLP page
as well.
I will be glad to share a copy of my CV, with a complete list of publications, if you are interested.REFEREED JOURNAL
* Proving TLS-attack related open biases of RC4 DES. CODES CRYPTOGRAPHY 77(1): 231-253 (2015) -- S. Sarkar, S. Sen Gupta, G. Paul, S. Maitra * (Non-)Random Sequences from (Non-)Random Permutations -- Analysis of RC4 stream cipher JOURNAL OF CRYPTOLOGY 27(1): 67-108 (2014) -- S. Sen Gupta, S. Maitra, G. Paul, S. Sarkar * High Performance Hardware Implementation for RC4 Stream Cipher IEEE TRANS. COMPUTERS 62(4): 730-743 (2013) -- S. Sen Gupta, A. Chattopadhyay, K. Sinha, S. Maitra, B. P. Sinha * Designing Integrated Accelerator for Stream Ciphers with Structural Similarities CRYPTOGRAPHY AND COMMUNICATIONS 5(1): 19-47 (2013) -- S. Sen Gupta, A. Chattopadhyay, A. Khalid * Counting Heron triangles with constraints INTEGERS 13: #A3 (2013) -- P. Stanica, S. Sarkar, S. Sen Gupta, S. Maitra, N. KarREFEREED CONFERENCE
* Dependence in IV-related bytes of RC4 key enhances vulnerabilitiesin WPA
FSE 2014 -- S. Sen Gupta, S. Maitra, W. Meier, G. Paul and S. Sarkar * Attack on Broadcast RC4 Revisited FSE 2011 -- S. Maitra, G. Paul and S. Sen Gupta * Proof of Empirical RC4 Biases and New Key Correlations SAC 2011 -- S. Sen Gupta, S. Maitra, G.Paul and S. Sarkar
* HiPAcc-LTE: An Integrated High Performance Accelerator for 3GPPLTE Stream Ciphers
INDOCRYPT 2011 -- S. Sen Gupta, A. Chattopadhyay and A. Khalid * One Byte per Clock: A Novel RC4 Hardware INDOCRYPT 2010 -- S. Sen Gupta, K. Sinha, S. Maitra and B. P. Sinha * Partial Key Exposure Attack on RSA - Improvements for LimitedLattice Dimensions
INDOCRYPT 2010 -- S. Sarkar, S. SenGupta and S. Maitra
* Factoring RSA Modulus using Prime Reconstruction from Random KnownBits
AFRICACRYPT 2010 -- S. Maitra, S. Sarkar and S. Sen GuptaTHESIS
* Analysis and Implementation of RC4 Stream Cipher PHD THESIS (2013) -- Advisor: Prof. Subhamoy Maitra, ISI Kolkata * Artin's Conjecture - Unconditional Approach and Elliptic Analogue MMATH THESIS (2008) -- Advisor: Dr. Yu-Ru Liu and Dr. Wentang Kuo, Univ. of WaterlooSYNERGY SYNERGY
* Member of Program Committee for SPACE 2018, Indocrypt 2016, Indocrypt 2015, Indocrypt 2014. * Reviewer/Sub-reviewer for Journal of Cryptology, IEEE Transactions on Computers, IEEE Transactions on VLSI, Microprocessors and Microsystems, Cryptography and Communications, Crypto, Eurocrypt, Asiacrypt, FSE, ACNS, SAC, Indocrypt, Africacrypt, ProvSec, etc. * Member of Organizing Committee for SPACE 2018, VLSI Design 2016, Indocrypt 2016, Indocrypt 2013, Indocrypt 2012. * Organized several workshops and training programs in Cryptology and allied disciplines, hosted by Centre of Excellence in Cryptology, Indian Statistical Institute, Kolkata. * Organized several summer internships and training programs in Cryptology and allied disciplines, hosted by R C Bose Centre for Cryptology and Security, Indian Statistical Institute, Kolkata. * Organized several Mathematics workshops and training programs for school students, primarily targeted towards Mathematics Olympiad. Affiliated with the RMO Committee of West Bengal. * Co-organizer of various workshops and training programs in Free and Open Source Software.MEMBER OF
* IACR
* CRSI
* AMS
YOU MAY LIKE
* IACR ePrint Archive * Open positions in Cryptology (IACR) * PhD Comics (if you can handlethe truth)
PERSONAL
I have had a bounty of hobbies and leisurely activities over the course of time -- sketching, magic, shayaari, recitation, karate, and many more. At present, I am interested in cooking, photography, design, and listening to music. I am also an avid reader, and I love listening to technical and non-technical lectures from various sources (TED talksare my favorite).
� Sourav Sen Gupta
Any feedback, comment and criticism about this website is most welcome. Just drop me an email.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0