Are you over 18 and want to see adult content?
More Annotations

A complete backup of monteurzimmer-oyten.de
Are you over 18 and want to see adult content?
A complete backup of quickphotoedit.com
Are you over 18 and want to see adult content?

A complete backup of artsoulradio.com
Are you over 18 and want to see adult content?
A complete backup of caririgardenshopping.com.br
Are you over 18 and want to see adult content?
A complete backup of directorymaster.com.ar
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://feel-music.ru
Are you over 18 and want to see adult content?

A complete backup of https://michaelkenna.com
Are you over 18 and want to see adult content?
A complete backup of https://avoalre.net
Are you over 18 and want to see adult content?
A complete backup of https://biohackerslab.com
Are you over 18 and want to see adult content?
A complete backup of https://nwcu.com
Are you over 18 and want to see adult content?

A complete backup of https://italiantours.tours
Are you over 18 and want to see adult content?
A complete backup of https://nyla.org
Are you over 18 and want to see adult content?

A complete backup of https://cnwebe.com
Are you over 18 and want to see adult content?
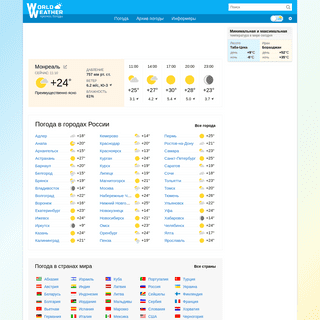
A complete backup of https://world-weather.ru
Are you over 18 and want to see adult content?

A complete backup of https://opportunitylouisiana.com
Are you over 18 and want to see adult content?
A complete backup of https://naaee.org
Are you over 18 and want to see adult content?
A complete backup of https://internationaleonline.org
Are you over 18 and want to see adult content?
Text
INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured toEFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to SPAM BLOCKER: HOW TO BLOCK SPAM Spam Blocker: How to Block Spam. A spam blocker can be an effective manner in which to cope with unwanted email. This anti spam software is different from spam filter programs in that it functions by blocking the majority of all incoming spam. HOW VIRUSES CAN DAMAGE YOUR COMPUTER THE IMPORTANCE OF DATA SECURITY Why Data Security is of Paramount Importance. Data security is critical for most businesses and even home computer users. Client information, payment information, personal files, bank account details - all of this information can be hard to replace and potentially dangerous if it falls into the wrong hands. COMPUTER WORM MALWARE: HOW IT WORKS Once the malcode has infected the PC, the worm will use a tool that is designed to discover other computers that are connected to the network. From there it scans the other computers on the network to locate vulnerabilities and then uses the penetration tool to access those computers. This is known as a payload and is malware that iscapable of
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured toEFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to SPAM BLOCKER: HOW TO BLOCK SPAM Spam Blocker: How to Block Spam. A spam blocker can be an effective manner in which to cope with unwanted email. This anti spam software is different from spam filter programs in that it functions by blocking the majority of all incoming spam. HOW VIRUSES CAN DAMAGE YOUR COMPUTER THE IMPORTANCE OF DATA SECURITY Why Data Security is of Paramount Importance. Data security is critical for most businesses and even home computer users. Client information, payment information, personal files, bank account details - all of this information can be hard to replace and potentially dangerous if it falls into the wrong hands. COMPUTER WORM MALWARE: HOW IT WORKS Once the malcode has infected the PC, the worm will use a tool that is designed to discover other computers that are connected to the network. From there it scans the other computers on the network to locate vulnerabilities and then uses the penetration tool to access those computers. This is known as a payload and is malware that iscapable of
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
SPAM BLOCKER: HOW TO BLOCK SPAM Spam Blocker: How to Block Spam. A spam blocker can be an effective manner in which to cope with unwanted email. This anti spam software is different from spam filter programs in that it functions by blocking the majority of all incoming spam.FEDERAL LAWS
The Federal Trade Commission (FTC) is responsible for regulating and enforcing the law. CAN-SPAM Act of 2003 is an acronym which stands for: Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003. Many anti-spammers have taken a stance against this law claiming that it is a failed attempt at really regulatingspam within
COMPANION VIRUS
The most common method is employed by the companion virus, also known as the spawning virus or the cluster virus. Instead of modifying the existing files in your system like most viruses, it creates new ones and sends them off to spread the malicious code. The companion virus works by seeking all files with extensions ending in EXE. SCAMS: 1-900 NUMBERS Another popular 1-900 scam involves snail mail and email messages. Upon receiving a letter, you are notified of winning a prize and instructed to call a 1-900 number to retrieve it. Usually, these prizes are worth no more than a few dollars. If this is the case, you've certainly been swindled. COMPUTER WORM MALWARE: HOW IT WORKS Once the malcode has infected the PC, the worm will use a tool that is designed to discover other computers that are connected to the network. From there it scans the other computers on the network to locate vulnerabilities and then uses the penetration tool to access those computers. This is known as a payload and is malware that iscapable of
WHY YOU SHOULD PROTECT YOUR PASSWORDS Make sure the passwords are unique for each account and login. It takes a few minutes every couple of months to protect a life's worth of data. Furthermore, you can protect your passwords by frequently changing them. This is a solid precautionary measure just in case someone happens to find them or the hackers become more advanced. WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
THE RISKS OF CHAIN LETTERS Quite simply, a commercial chain letter is designed to extort money from you. It may make you believe that by giving some of your money away you will get more back in return, however this is not the real purpose of the chain letter. Whether other people are able to make money is of little interest to the person who started the scam. MANAGEMENT SERVER SECURITY RISKS Management Server Security Risks. A management server is a platform used within organizations to deliver centralized management services that include the employment of a comprehensive security policy, chain of command security management, monitoring of real-time applications, logging activity, auditing of programs, and compliance reporting. JAMAICAN SWITCH FRAUD One of the most daring types of fraud attempted today is known as the Jamaican Switch. Here's an example of how it works: A woman approaches you in distress. Due to a thick foreign accent, you have a hard time making out her pleas but finally realize that she's looking to rent a hotel room for the night. Since the woman speaks bad English andBLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems.EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death toINSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference. HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. TEST RESTORE AND ITS IMPORTANCE IN A NETWORK BACKUP SYSTEM Test Restore and Its Importance in a Network Backup System. Test restore is a process that is performed on a frequent basis to ensure the network backup system is working at the optimum level. There are a variety of issues that can cause a backup system to malfunction which includes failed backup software, incomplete data backup failure, or an WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
BLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems.EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death toINSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference. HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. TEST RESTORE AND ITS IMPORTANCE IN A NETWORK BACKUP SYSTEM Test Restore and Its Importance in a Network Backup System. Test restore is a process that is performed on a frequent basis to ensure the network backup system is working at the optimum level. There are a variety of issues that can cause a backup system to malfunction which includes failed backup software, incomplete data backup failure, or an WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
BLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems. LITERARY SCAMS: WRITERS WATCH OUT! Literary Scams: Writers Watch Out! Credit card scams, lottery scams, internet scams, investment scams, domain name registration scams, and adding to this quite endless list of scams are even literary scams.It seems that scammers spare no one.FEDERAL LAWS
The Federal Trade Commission (FTC) is responsible for regulating and enforcing the law. CAN-SPAM Act of 2003 is an acronym which stands for: Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003. Many anti-spammers have taken a stance against this law claiming that it is a failed attempt at really regulatingspam within
PROTECTING YOUR DATA ON THE INTERNET A firewall will help to keep computer crackers out of your system by monitoring network traffic. For the average home user, this network is the internet. Acting as your personal security guard, a firewall looks out for outside intrusion and will alert you of anyone attempting to access your computer. Some also monitor and block outbound traffic THE TRUTH BEHIND NIGERIAN SCAMS The Facts. Emerged in the early 1980s under consecutive governments of Nigeria. Constitutes the 3rd to the 5th largest industry in Nigeria. May be also referred to as an advanced fee fraud, 419 fraud, The Nigerian Connection, and 419 – a section of the criminal code of Nigeria. Authorities often don’t recover the cash raked in fromvictims.
WHAT IS THE BEST WAY TO REMOVE SPYWARE? This is done by using the uninstall function of your computer. For Windows users, you can remove specific applications by going to your control panel (in "Settings") and selecting the "Add/Remove Programs" function. Once there, you will see a list of programs. Click on the program you believe to be spyware and select "Remove".COMPANION VIRUS
The most common method is employed by the companion virus, also known as the spawning virus or the cluster virus. Instead of modifying the existing files in your system like most viruses, it creates new ones and sends them off to spread the malicious code. The companion virus works by seeking all files with extensions ending in EXE. REASONS TO SECURE YOUR WEB BROWSER These are only a few reasons why you should secure your Web browser. The process of configuring your browser security features is rather simple to accomplish and well worth the investment of a few minutes of your time. Due to the explosion of the Internet, attacking the vulnerabilities in Web browsers has become one of the most popularways for
HOW TO PREVENT UNAUTHORIZED COPYING OF CONFIDENTIAL WEB How to Prevent Unauthorized Copying of Confidential Web Content. Organizations that provide websites with confidential information often face the issues of protecting the information and the html source codes that accompany it from being copied by an unauthorizeduser.
WHAT IS A PACKET SNIFFER AND HOW DOES IT WORK? A packet sniffer is a device that is used by network administrators to monitor the data that is being transmitted over a network. Packet sniffers are used for network management and network security and they can also be used by unauthorized users to steal information from a network. Hackers often use packet sniffers because they are veryEFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.BLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured toFEDERAL LAWS
The Federal Trade Commission (FTC) is responsible for regulating and enforcing the law. CAN-SPAM Act of 2003 is an acronym which stands for: Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003. Many anti-spammers have taken a stance against this law claiming that it is a failed attempt at really regulatingspam within
LITERARY SCAMS: WRITERS WATCH OUT! Literary Scams: Writers Watch Out! Credit card scams, lottery scams, internet scams, investment scams, domain name registration scams, and adding to this quite endless list of scams are even literary scams. It seems that scammers spare no one. Not even writers. YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.BLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured toFEDERAL LAWS
The Federal Trade Commission (FTC) is responsible for regulating and enforcing the law. CAN-SPAM Act of 2003 is an acronym which stands for: Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003. Many anti-spammers have taken a stance against this law claiming that it is a failed attempt at really regulatingspam within
LITERARY SCAMS: WRITERS WATCH OUT! Literary Scams: Writers Watch Out! Credit card scams, lottery scams, internet scams, investment scams, domain name registration scams, and adding to this quite endless list of scams are even literary scams. It seems that scammers spare no one. Not even writers. YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
BLOCKING SPAM
How to Block Spam Effectively. If you use the internet then you're going to have to get used to spam. Although using email to communicate is really useful and convenient there are a number of problems. LITERARY SCAMS: WRITERS WATCH OUT! Literary Scams: Writers Watch Out! Credit card scams, lottery scams, internet scams, investment scams, domain name registration scams, and adding to this quite endless list of scams are even literary scams.It seems that scammers spare no one.FEDERAL LAWS
The Federal Trade Commission (FTC) is responsible for regulating and enforcing the law. CAN-SPAM Act of 2003 is an acronym which stands for: Controlling the Assault of Non-Solicited Pornography and Marketing Act of 2003. Many anti-spammers have taken a stance against this law claiming that it is a failed attempt at really regulatingspam within
PROTECTING YOUR DATA ON THE INTERNET A firewall will help to keep computer crackers out of your system by monitoring network traffic. For the average home user, this network is the internet. Acting as your personal security guard, a firewall looks out for outside intrusion and will alert you of anyone attempting to access your computer. Some also monitor and block outbound traffic THE TRUTH BEHIND NIGERIAN SCAMS The Facts. Emerged in the early 1980s under consecutive governments of Nigeria. Constitutes the 3rd to the 5th largest industry in Nigeria. May be also referred to as an advanced fee fraud, 419 fraud, The Nigerian Connection, and 419 – a section of the criminal code of Nigeria. Authorities often don’t recover the cash raked in fromvictims.
WHAT IS THE BEST WAY TO REMOVE SPYWARE? This is done by using the uninstall function of your computer. For Windows users, you can remove specific applications by going to your control panel (in "Settings") and selecting the "Add/Remove Programs" function. Once there, you will see a list of programs. Click on the program you believe to be spyware and select "Remove".COMPANION VIRUS
The most common method is employed by the companion virus, also known as the spawning virus or the cluster virus. Instead of modifying the existing files in your system like most viruses, it creates new ones and sends them off to spread the malicious code. The companion virus works by seeking all files with extensions ending in EXE. REASONS TO SECURE YOUR WEB BROWSER These are only a few reasons why you should secure your Web browser. The process of configuring your browser security features is rather simple to accomplish and well worth the investment of a few minutes of your time. Due to the explosion of the Internet, attacking the vulnerabilities in Web browsers has become one of the most popularways for
HOW TO PREVENT UNAUTHORIZED COPYING OF CONFIDENTIAL WEB How to Prevent Unauthorized Copying of Confidential Web Content. Organizations that provide websites with confidential information often face the issues of protecting the information and the html source codes that accompany it from being copied by an unauthorizeduser.
WHAT IS A PACKET SNIFFER AND HOW DOES IT WORK? A packet sniffer is a device that is used by network administrators to monitor the data that is being transmitted over a network. Packet sniffers are used for network management and network security and they can also be used by unauthorized users to steal information from a network. Hackers often use packet sniffers because they are verySPAM – ANTIVIRUS
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help ourreaders
EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to THE DANGERS OF POPUPS YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to 5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
TYPES OF ADWARE: GATORSPAM – ANTIVIRUS
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help ourreaders
EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to THE DANGERS OF POPUPS YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to 5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
TYPES OF ADWARE: GATORSPAM – ANTIVIRUS
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help ourreaders
HOW TO AVOID ADWARE
Below we have provided a few tips to help you avoid adware and several other security threats: Put up a firewall: Firewall products have become recommended in the world of computer security and often come included as features of anti-virus software. This component will help to prevent third-party intrusion and report any attempts made to enterDIRECTORY VIRUSES
A directory virus will modify the paths that indicate location, manipulating them to execute and infect clean files, spreading itself throughout the system. In most cases you can successfully run the file you request while simultaneously launching the infectious program with no knowledge of the activity. After the virus has run it's course, theINSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to TYPES OF ADWARE: GATOR Description of Gator. Gator is promoted as a low-risk, harmless adware program compatible with Windows 98, ME, 2000, 2003 and Windows server platforms. What isn't advertised is the fact that Gator replicates itself similar to a virus. It has also been known to secretly download updates and install other types of adware and spyware that monitors THE TRUTH BEHIND NIGERIAN SCAMS The Facts. Emerged in the early 1980s under consecutive governments of Nigeria. Constitutes the 3rd to the 5th largest industry in Nigeria. May be also referred to as an advanced fee fraud, 419 fraud, The Nigerian Connection, and 419 – a section of the criminal code of Nigeria. Authorities often don’t recover the cash raked in fromvictims.
HOW TO IDENTIFY TROJAN MALWARE How to Identify a Trojan. The first sign that a Trojan has entered your PC is that your PC will act really strange and start doing some very uncommon things. Screen Change: The screen color will change along with the screen resolution or the screen will turn upside down for seemingly no reason. Antivirus Disabled: A Trojan can disable your JAMAICAN SWITCH FRAUD One of the most daring types of fraud attempted today is known as the Jamaican Switch. Here's an example of how it works: A woman approaches you in distress. Due to a thick foreign accent, you have a hard time making out her pleas but finally realize that she's looking to rent a hotel room for the night. Since the woman speaks bad English and SET-UP BLUETOOTH ON YOUR DEVICES AND COMPUTERS When you insert your Bluetooth USB key, you can install the Bluetooth hardware that comes with the operating system. After installation, a Bluetooth icon will appear in the system icon tray. Click on the icon to open the Bluetooth network. When you download programs - particularly freeware, or peer-to-peer sharing programs. WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
SPAM – ANTIVIRUS
SpamLaws.com is dedicated to providing accurate and up-to-date information on issues affecting Internet security and scams.EFFECTS OF FRAUD
•automobile insurance • homeowners' insurance • medical insurance • the welfare system • government contracts • used cars • prize drawings • social engineering Lasting Impact of Fraud. It is often stated that many of these crimes such as insurance and welfare fraud have no direct victims. HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference. YELLOW PAGES BILLING SCAM No company is too big - they all can be used to pull off scams! Scams are abundant on the web. One particular scheme that is growing at a rapid rate involves the nationally renown business directory, Yellow Book, formerly known as Yellow Pages. THE DANGERS OF POPUPS 5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too.If you're seriously thinking about setting up your own network, you should be informed about all of the advantages anddisadvantages too.
WHAT IS LINUX AND HOW DOES IT WORK? Fraud causes hundreds of millions of dollars in damage each year and affects just as many people. Credit card fraud is the most common type of fraud to occur each year and cost its victims up to $500 million dollars in damages each year.INSERTION ATTACKS
Types of Wireless Network Attacks: Insertion. Computer technology has rapidly evolved over the past decade or so. Much of this can be attributed to the internet as many computers now have a need to be networked together to establish an online connection. TYPES OF ADWARE: GATORSPAM – ANTIVIRUS
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help ourreaders
EFFECTS OF FRAUD
Fraud has a negative effect on everyone. Here are few consequences we all endure: • economic decline due to losses suffered by publicly used services such as transportation, police and fire departments. • indirect economic losses endured by prominent corporations due to losses suffered by their clients. • physical injury or death to THE DANGERS OF POPUPS YELLOW PAGES BILLING SCAM Aware of the scam in process, the manager continues to refuse while the caller carries on with legal threats. Realizing that things are going nowhere, the manager ends the conversation and plays the call as if it never even happened. Months pass with no letters, faxes, phone calls or further problems from the Yellow Pages representative. HOW TO POSITION A WIRELESS ACCESS POINT OR ROUTER How to Position a Wireless Access Point or Router. When you're setting up your wireless home network, one of the most important things to consider is where to put your router or access point.To maximize the signal strength of your access point or router, and thus the performance of your WiFi home network, you want to keep three factors to a minimum: distance, obstructions, and interference.INSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to 5 WAYS HACKERS CAN ACCESS YOUR DATA Data Security: 5 Ways Hackers Can Access Your Data. With the increasing number of people that are shopping, performing confidential tasks, and doing their banking online, there is a lot of sensitive information that is being stored on computers and in organizationnetworks.
HOME AND OFFICE NETWORKS: NETWORKING DISADVANTAGES Disadvantages of A Home or Office Network. While there are many advantages to installing a home or office network, there can be disadvantages too. If you're seriously thinking about setting up your own network, you should be informed about all of the advantages and disadvantages too. Expensive to Install: For one, networks can bepricey to set up.
WHAT IS LINUX AND HOW DOES IT WORK? Linux is an operating system that runs on the Linux kernel which was created by Linus Torvalds back in the early 1990s in Finland. The kernel was made available for free and allowed other programmers to add to the kernel as a free contribution. After hundreds of programmers started developing the kernel, the Linux system rapidlygrew.
TYPES OF ADWARE: GATORSPAM – ANTIVIRUS
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help ourreaders
HOW TO AVOID ADWARE
Below we have provided a few tips to help you avoid adware and several other security threats: Put up a firewall: Firewall products have become recommended in the world of computer security and often come included as features of anti-virus software. This component will help to prevent third-party intrusion and report any attempts made to enterDIRECTORY VIRUSES
A directory virus will modify the paths that indicate location, manipulating them to execute and infect clean files, spreading itself throughout the system. In most cases you can successfully run the file you request while simultaneously launching the infectious program with no knowledge of the activity. After the virus has run it's course, theINSERTION ATTACKS
One of the most commonly employed wireless exploits is the insertion attack. This practice involves bypassing security mechanisms and inserting unauthorized devices on a wireless network. The device used is usually a laptop or PDA in which the intruder tries to connect it to the base station. Although a base station should be configured to TYPES OF ADWARE: GATOR Description of Gator. Gator is promoted as a low-risk, harmless adware program compatible with Windows 98, ME, 2000, 2003 and Windows server platforms. What isn't advertised is the fact that Gator replicates itself similar to a virus. It has also been known to secretly download updates and install other types of adware and spyware that monitors THE TRUTH BEHIND NIGERIAN SCAMS The Facts. Emerged in the early 1980s under consecutive governments of Nigeria. Constitutes the 3rd to the 5th largest industry in Nigeria. May be also referred to as an advanced fee fraud, 419 fraud, The Nigerian Connection, and 419 – a section of the criminal code of Nigeria. Authorities often don’t recover the cash raked in fromvictims.
HOW TO IDENTIFY TROJAN MALWARE How to Identify a Trojan. The first sign that a Trojan has entered your PC is that your PC will act really strange and start doing some very uncommon things. Screen Change: The screen color will change along with the screen resolution or the screen will turn upside down for seemingly no reason. Antivirus Disabled: A Trojan can disable your JAMAICAN SWITCH FRAUD One of the most daring types of fraud attempted today is known as the Jamaican Switch. Here's an example of how it works: A woman approaches you in distress. Due to a thick foreign accent, you have a hard time making out her pleas but finally realize that she's looking to rent a hotel room for the night. Since the woman speaks bad English and SET-UP BLUETOOTH ON YOUR DEVICES AND COMPUTERS When you insert your Bluetooth USB key, you can install the Bluetooth hardware that comes with the operating system. After installation, a Bluetooth icon will appear in the system icon tray. Click on the icon to open the Bluetooth network. When you download programs - particularly freeware, or peer-to-peer sharing programs. WHITE BOX TESTING AND WHY IT IS IMPORTANT TO NETWORK SECURITY White Box Testing. White box testing is a recent method of assessing applications and WiFi security on a network. This type of testing is also known as penetration testing which is a process of assessing and evaluating a network to ensure that the proper measures are being taken to secure the network against threats and attacks with maliciousintent.
Menu
* Identity Theft
* Scams
* Spam
* Fraud
* Antivirus
* Spyware
* Adware
* Backup
* Computer Virus & Worms* Wireless Security
* Networking
* Software Reviews
* Phishing
* Malware 101
* Parental Control
* Network Security
* Operating Systems
* Data Encryption
* Browsers
* Email Client Software * Password ProtectionSpam Laws
* United States
* European Union
* Other Countries
* Cases
* Articles
Report Spam
SPAMLAWS - HOW TO STOP SCAMS AND FRAUD SpamLaws.com is dedicated to providing accurate and up-to-date information on issues affecting Internet security. Our team of writers, programmers, researchers and Internet experts are committed to ensuring our work is of the highest quality possible. We are devoted to supplying our readers with the best Internet protection information and are constantly striving to learn more about and report on the latest and most up-to-date Internet security issues, software,and protection.
We also investigate common Internet based scams and fraud issues to help our readers protect themselves from the most current Internet threats. We stay on top of all the newest and most advanced security protection software to help you choose the best way to protect your computer and online identity. In addition, we endeavor to help our readers deal with issues of Internet viruses, identity theft, malware, and spam in order to provide you with the quickest way defuse potentially harmful situations for you and your computer. We hope SpamLaws.com helps you with all of your Internet securityneeds!
YOUR ONLINE SECURITY RESOURCE Viruses, spam, spyware - the list seems endless. Indeed, as technology becomes more sophisticated and accessible, so too do methods of corrupting them. And unfortunately, at some point or another, we will all fall victim to one or more of these potentially dangerous computerthreats.
So what can you do protect your personal information? You can start bygetting informed.
SPAM LAWS
Spam emails are a huge annoyance to Internet-goers. But with some 80% of all emails reported as unsolicited, the numbers don't appear to be decreasing. This has many people wondering just what is being done to protect their privacy. Learn what anti spam laws are in place whereyou live.
Learn More
SPYWARE
Have you noticed your computer is performing at less than optimal capacity? More likely than not, spyware is to blame. Find out about the latest and most effective spyware removal programs, as well as tips on how to prevent this unwanted material from taking over yourcomputer.
Learn More
IDENTITY THEFT
Identity theft is on the rise, affecting some 10 million Americans annually. And with the Internet making access to personal information more readily available, cause for concern is growing ever greater. So just what can you do to protect yourself from becoming the next victim? Read on for tips and advice.Learn More
Report Spam
Spyware has many ways of getting onto your computer, such as: When you download programs - particularly freeware, or peer-to-peersharing programs.
More covertly, spyware can install itself just by you visiting certain sites, by prompting you to download an application to see the siteproperly.
ActiveX controls. These pesky spyware makers will prompt you to install themselves while using your Internet browser Contact Us |About us | Privacy Policy | Spam Laws Site Maps | Terms of Use and Disclaimer | Resources � 2020 Spamlaws.com All rights reserved.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0