Are you over 18 and want to see adult content?
More Annotations
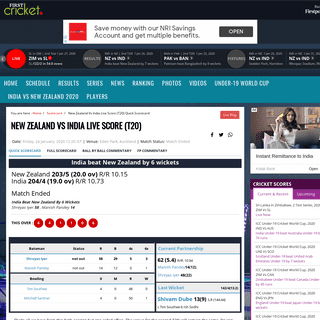
A complete backup of www.hindustantimes.com/cricket/india-vs-new-zealand-team-india-ride-on-kl-rahul-and-shreyas-iyer-brilliance
Are you over 18 and want to see adult content?

A complete backup of fox61.com/2020/01/28/police-say-fotis-dulos-is-in-critical-condition-attorney-says-he-will-be-treated-in-hy
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://kayak.co.in
Are you over 18 and want to see adult content?
A complete backup of https://officefurnituredisposal.com
Are you over 18 and want to see adult content?

A complete backup of https://step.com
Are you over 18 and want to see adult content?
A complete backup of https://promotur.org
Are you over 18 and want to see adult content?

A complete backup of https://edenbeachresorts.com
Are you over 18 and want to see adult content?

A complete backup of https://watfordcolosseum.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://liraland.ua
Are you over 18 and want to see adult content?
A complete backup of https://favchef.com
Are you over 18 and want to see adult content?
A complete backup of https://mohawk.la
Are you over 18 and want to see adult content?
A complete backup of https://select-type.com
Are you over 18 and want to see adult content?

A complete backup of https://biuro-synergia.pl
Are you over 18 and want to see adult content?

A complete backup of https://dataprotectionworldforum.com
Are you over 18 and want to see adult content?
Text
network.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. MBR FILTER - A SIMPLE DISK FILTER THAT BLOCKS WRITE ACCESS MBR Filter. MBR Filter is a simple disk filter designed by Cisco Talos to block write access to the Master Boot Record (MBR). The MBR is used to store information related to how the storage device is partitioned, as well as details regarding the filesystem configuration on thedevice.
BEERS WITH TALOS PODCASTS || CISCO TALOS INTELLIGENCE Joe Marshall from the Talos Outreach group joins to share his insights on the space and how donuts are the ultimate career track switching tool. Oh- and Matt’s cat discovers jerky. Full show notes on the Talos blog. Hosted By: Mitch Neff @MitchNeff. Special Guest: Joe Marshall @ImmortanJo3. Featuring: CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO AMP NAMING CONVENTIONS Find the samples of the naming convention patterns of threats collected in AMP to help with threat analysis that protect organizations before, during, and after an attack. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP Cisco Talos is happy to announce the upcoming changes to our Content and Threat Category lists. Our goal is to provide you with sufficient intelligence details to allow you to make informed decisions to protect your network without disrupting your organization’sproductivity.
CISCO TALOS INTELLIGENCE GROUP CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. MBR FILTER - A SIMPLE DISK FILTER THAT BLOCKS WRITE ACCESS MBR Filter. MBR Filter is a simple disk filter designed by Cisco Talos to block write access to the Master Boot Record (MBR). The MBR is used to store information related to how the storage device is partitioned, as well as details regarding the filesystem configuration on thedevice.
BEERS WITH TALOS PODCASTS || CISCO TALOS INTELLIGENCE Joe Marshall from the Talos Outreach group joins to share his insights on the space and how donuts are the ultimate career track switching tool. Oh- and Matt’s cat discovers jerky. Full show notes on the Talos blog. Hosted By: Mitch Neff @MitchNeff. Special Guest: Joe Marshall @ImmortanJo3. Featuring: CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO AMP NAMING CONVENTIONS Find the samples of the naming convention patterns of threats collected in AMP to help with threat analysis that protect organizations before, during, and after an attack. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP Cisco Talos is happy to announce the upcoming changes to our Content and Threat Category lists. Our goal is to provide you with sufficient intelligence details to allow you to make informed decisions to protect your network without disrupting your organization’sproductivity.
CISCO TALOS INTELLIGENCE GROUP LIBRARY || CISCO TALOS INTELLIGENCE GROUP Threat Spotlight: Cisco Talos Thwarts Access to Massive International Exploit Kit Generating $60M Annually From Ransomware Alone. Nick Biasini with contributions from Joel Esler, Warren Mercer, Melissa Taylor, and Craig Williams. 2015-10-06. CISCO TALOS INCIDENT RESPONSE || CISCO TALOS INTELLIGENCE Cisco Talos Incident Response (CTIR) provides a full suite of proactive and emergency services to help you prepare, respond and recover from a breach. CTIR enables 24 hour emergency response capabilities and direct access to Cisco Talos, the world's largest threat intelligence and research group. CISCO TALOS INTELLIGENCE GROUP By Jon Munshaw, with contributions from Edmund Brumaghin. Microsoft released its monthly security update Tuesday, disclosing 51 vulnerabilities across its suite of products, breaking last month’s 16-month record of the fewest vulnerabilities disclosed in a month by the company.. There are only four critical vulnerabilities patched in this month, while all the other ones are considered TALOS-2020-1216 || CISCO TALOS INTELLIGENCE GROUP The Cosori Smart Air Fryer is a WiFi-enabled kitchen appliance that allows user to activate the device remotely, look up recipe guides and monitor cooking status via the mobile application. During the initial setup phase, the embedded ESP-01E-based device functions as a WiFi access point that must be associated with before the mobile CISCO TALOS INTELLIGENCE GROUP Description: VMware issued a warning Friday alerting users to protect against exploitation of a severe vulnerability in its vSphere Client’s Virtual SAN Health Check plug-in, which is enabled by default in vCenter Server.An attacker with network access to this service can exploit this vulnerability to gain remote code execution on the affected vCenter Server. IMMUNET - OPEN SOURCE, REAL-TIME ANTIVIRUS PROTECTION THAT Immunet is a malware and antivirus protection system that utilizes cloud computing to provide enhanced community-based security. Keep your security always up-to-date against the latest malware including viruses, spyware, bots, worms, trojans, and keyloggers. CISCO TALOS INTELLIGENCE GROUP By David Liebenberg and Caitlin Huey.. While the security community made a great effort to warn users of the exploitation of several Microsoft Exchange Server zero-day vulnerabilities, it was still the biggest threat Cisco Talos Incident Response (CTIR) saw this past quarter. These vulnerabilities, tracked as CVE-2021-26855, CVE-2021-26857, CVE-2021-26858 and CVE-2021-27065, comprised CISCO TALOS INTELLIGENCE GROUP Threat Breakdown Win.Ransomware.Cerber-9142650-0 Indicators of Compromise. IOCs collected from dynamic analysis of 19 samples CISCO TALOS INTELLIGENCE GROUP By Neil Jenkins and Matthew Olney. Note: Our guest co-author, Neil Jenkins, is the Chief Analytic Officer at the Cyber Threat Alliance.He leads the CTA's analytic efforts, focusing on the development of threat profiles, adversary playbooks and other CISCO TALOS INTELLIGENCE GROUP Coverage. The following SNORTⓇ rules will detect exploitation attempts. Note that additional rules may be released at a future date and current rules are subject to CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. CISCO TALOS INTELLIGENCE GROUP Threat Breakdown Win.Ransomware.Cerber-9142650-0 Indicators of Compromise. IOCs collected from dynamic analysis of 19 samples CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.Razy-9807129-0 Packed Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypts the data, and sends it to a command and control (C2) server. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP One of the simpler ways to identify malware-infected machines communicating with their command and control servers is to watch for known malicious User-Agent strings in HTTP requests. CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. CISCO TALOS INTELLIGENCE GROUP Threat Breakdown Win.Ransomware.Cerber-9142650-0 Indicators of Compromise. IOCs collected from dynamic analysis of 19 samples CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.Razy-9807129-0 Packed Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypts the data, and sends it to a command and control (C2) server. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP One of the simpler ways to identify malware-infected machines communicating with their command and control servers is to watch for known malicious User-Agent strings in HTTP requests. CISCO TALOS INTELLIGENCE GROUP By Jon Munshaw, with contributions from Edmund Brumaghin. Microsoft released its monthly security update Tuesday, disclosing 51 vulnerabilities across its suite of products, breaking last month’s 16-month record of the fewest vulnerabilities disclosed in a month by the company.. There are only four critical vulnerabilities patched in this month, while all the other ones are considered TALOS-2020-1181 || CISCO TALOS INTELLIGENCE GROUP Summary. A use-after-free vulnerability exists in the JavaScript engine of Foxit Software’s PDF Reader, version 10.1.0.37527. A specially crafted PDF document can trigger the reuse of previously free memory which can lead to arbitrary code execution. CISCO TALOS INTELLIGENCE GROUP Coverage. The following SNORTⓇ rules will detect exploitation attempts. Note that additional rules may be released at a future date and current rules are subject to TALOS-2020-1122 || CISCO TALOS INTELLIGENCE GROUP Talos Vulnerability Report TALOS-2020-1122 SoftPerfect RAM Disk spvve.sys 0x222024 information disclosure vulnerability August 4, 2020CVE Number
BEERS WITH TALOS PODCASTS || CISCO TALOS INTELLIGENCE Security Stories Ep. 27: Dealing with stress, burnout and mental health in the threat intelligence industry. This is a very different episode in that it isn’t really a BWT episode at all. GHIDA - GHIDRA DECOMPILER FOR IDA PRO || CISCO TALOS GhIDA is an IDA Pro plugin that integrates the Ghidra decompiler in the IDA workflow, providing improved navigation and giving users the ability to rename and highlight symbols. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.Razy-9807129-0 Packed Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypts the data, and sends it to a command and control (C2) server. SENIOR INCIDENT RESPONSE CONSULTANT What You’ll Do. The Cisco Talos Incident Response Consultant will work within established methodologies to perform a variety of incident response-related activities for Cisco customers. SENIOR INCIDENT RESPONSE COMMANDER What You’ll Do. Work within established methodologies to perform a variety of incident response-related activities for Cisco customers. This will include emergency response to cyber incidents. CISCO TALOS INTELLIGENCE GROUP In this document, we’ll outline a collection of risk mitigation strategies. While none of these methods are new, when combined, these defensive techniques and methods allow resiliency against initial access, and the ability to contain the threat if an adversary successfully gains initial access. CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. TALOS-2020-1122 || CISCO TALOS INTELLIGENCE GROUP SoftPerfect RAM Disk is a high-performance RAM disk application that lets the user store a disk from their computer stored on the device’s memory. The spvve.sys driver creates a device object Device\SoftPerfectVolume that is accessible to any user on the system so any user sending specially crafted I/O request packet (IRP) cancause
CISCO TALOS INTELLIGENCE GROUP Threat Breakdown Win.Ransomware.Cerber-9142650-0 Indicators of Compromise. IOCs collected from dynamic analysis of 19 samples CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.Razy-9807129-0 Packed Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypts the data, and sends it to a command and control (C2) server. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP As the leading technology security company, Cisco brings credibility to share with our guidance on proactive measures and reactive considerations. However, ransomware prevention and remediation are complex topics and there is no “one-size-fits-all” approach. In this document, we’ll outline a collection of risk mitigationstrategies.
CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. TALOS-2020-1122 || CISCO TALOS INTELLIGENCE GROUP SoftPerfect RAM Disk is a high-performance RAM disk application that lets the user store a disk from their computer stored on the device’s memory. The spvve.sys driver creates a device object Device\SoftPerfectVolume that is accessible to any user on the system so any user sending specially crafted I/O request packet (IRP) cancause
CISCO TALOS INTELLIGENCE GROUP Threat Breakdown Win.Ransomware.Cerber-9142650-0 Indicators of Compromise. IOCs collected from dynamic analysis of 19 samples CISCO TALOS INTELLIGENCE GROUP We also had Patch Tuesday this week, which featured some more vulnerabilities in Microsoft Exchange Server.Here is a full breakdown of the issues you should know about and Snort rules to keep users protected from exploitation. Cisco Talos researchers specifically discovered multiple vulnerabilities in Azure Sphere that were patchedthis month.
CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.Razy-9807129-0 Packed Razy is oftentimes a generic detection name for a Windows trojan. It collects sensitive information from the infected host and encrypts the data, and sends it to a command and control (C2) server. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Trojan.DarkComet-9847204-1 Trojan DarkComet and related variants are a family of remote access trojans designed to provide an CISCO TALOS INTELLIGENCE GROUP As the leading technology security company, Cisco brings credibility to share with our guidance on proactive measures and reactive considerations. However, ransomware prevention and remediation are complex topics and there is no “one-size-fits-all” approach. In this document, we’ll outline a collection of risk mitigationstrategies.
CISCO TALOS INTELLIGENCE GROUP By Jon Munshaw, with contributions from Edmund Brumaghin. Microsoft released its monthly security update Tuesday, disclosing 51 vulnerabilities across its suite of products, breaking last month’s 16-month record of the fewest vulnerabilities disclosed in a month by the company.. There are only four critical vulnerabilities patched in this month, while all the other ones are considered TALOS-2020-1181 || CISCO TALOS INTELLIGENCE GROUP A use-after-free vulnerability exists in the JavaScript engine of Foxit Software’s PDF Reader, version 10.1.0.37527. A specially crafted PDF document can trigger the reuse of previously free memory which can lead to arbitrary code execution. An attacker needs to trick the user to open the malicious file to trigger this vulnerability. FIRST - FUNCTION IDENTIFICATION AND RECOVERY SIGNATURE First. The Function Identification and Recover Signature Tool (FIRST) developed by Talos, is an IDA Pro plugin that allows reverse engineers to more quickly complete static analysis. TALOS-2020-1122 || CISCO TALOS INTELLIGENCE GROUP SoftPerfect RAM Disk is a high-performance RAM disk application that lets the user store a disk from their computer stored on the device’s memory. The spvve.sys driver creates a device object Device\SoftPerfectVolume that is accessible to any user on the system so any user sending specially crafted I/O request packet (IRP) cancause
CISCO TALOS INTELLIGENCE GROUP By Neil Jenkins and Matthew Olney. Note: Our guest co-author, Neil Jenkins, is the Chief Analytic Officer at the Cyber Threat Alliance.He leads the CTA's analytic efforts, focusing on the development of threat profiles, adversary playbooks and other BEERS WITH TALOS PODCASTS || CISCO TALOS INTELLIGENCE Joe Marshall from the Talos Outreach group joins to share his insights on the space and how donuts are the ultimate career track switching tool. Oh- and Matt’s cat discovers jerky. Full show notes on the Talos blog. Hosted By: Mitch Neff @MitchNeff. Special Guest: Joe Marshall @ImmortanJo3. Featuring: CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO TALOS INTELLIGENCE GROUP Coverage. The following SNORTⓇ rules will detect exploitation attempts. Note that additional rules may be released at a future date and current rules are subject to SENIOR INCIDENT RESPONSE CONSULTANT What You’ll Do. The Cisco Talos Incident Response Consultant will work within established methodologies to perform a variety of incident response-related activities for Cisco customers. SENIOR INCIDENT RESPONSE COMMANDER What You’ll Do. Work within established methodologies to perform a variety of incident response-related activities for Cisco customers. This will include emergency response to cyber incidents. CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. MBR FILTER - A SIMPLE DISK FILTER THAT BLOCKS WRITE ACCESSCISCO TALOS IPCISCO TALOS LOOKUPCISCO TALOS REPUTATION CHECKTALOS INTELLIGENCE BLOGTALOS INTELLIGENCE REPUTATIONTALOS INTELLIGENCE SPAM MBR Filter. MBR Filter is a simple disk filter designed by Cisco Talos to block write access to the Master Boot Record (MBR). The MBR is used to store information related to how the storage device is partitioned, as well as details regarding the filesystem configuration on thedevice.
TALOS FILE REPUTATION LOOKUP || CISCO TALOS INTELLIGENCE The Cisco Talos Intelligence Group maintains a reputation disposition on billions of files. This reputation system is fed into the AMP, FirePower, ClamAV, and Open-Source Snort product lines. The tool below allows you to do casual lookups against the Talos File Reputation system. This system limits you to one lookup at a time, and is limitedto
CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO AMP NAMING CONVENTIONS Find the samples of the naming convention patterns of threats collected in AMP to help with threat analysis that protect organizations before, during, and after an attack. CISCO TALOS INTELLIGENCE GROUP There is a compiled version of scdbg available, but it is probably better to compile it from the source code because of the new API emulations. Covenant Covenant is a relatively new C#-based command and control framework that also allows an attacker (or a red team member) to create payloads based on several infection vectors, including MSBuild. The skeleton code for the MSBuild loader is EMAIL AND SPAM DATA || CISCO TALOS INTELLIGENCE GROUP IP Address Hostname Network Owner The organization name for some larger corporate and educational networks. If organization is a small business or is unavailable, the Internet Service Provider name is CISCO TALOS INTELLIGENCE GROUP Cisco Talos Intelligence Group is one of the largest commercial threat intelligence teams in the world. Comprised of world-class cyber security researchers, analysts and engineers and supported by unrivaled telemetry, Talos defends Cisco customers against known and emerging threats, discovers new vulnerabilities in common software, and interdicts threats in the wild before they can further IP AND DOMAIN REPUTATION CENTER || CISCO TALOS IP & Domain Reputation Center. The Talos IP and Domain Reputation Center is the world’s most comprehensive real-time threat detectionnetwork.
REPUTATION CENTER
IP and Domain Reputation Center. Talos’ IP and Domain Data Center is the world’s most comprehensive real-time threat detection network. The data is made up of daily security intelligence across millions of deployed web, email, firewall and IPS appliances. MBR FILTER - A SIMPLE DISK FILTER THAT BLOCKS WRITE ACCESSCISCO TALOS IPCISCO TALOS LOOKUPCISCO TALOS REPUTATION CHECKTALOS INTELLIGENCE BLOGTALOS INTELLIGENCE REPUTATIONTALOS INTELLIGENCE SPAM MBR Filter. MBR Filter is a simple disk filter designed by Cisco Talos to block write access to the Master Boot Record (MBR). The MBR is used to store information related to how the storage device is partitioned, as well as details regarding the filesystem configuration on thedevice.
TALOS FILE REPUTATION LOOKUP || CISCO TALOS INTELLIGENCE The Cisco Talos Intelligence Group maintains a reputation disposition on billions of files. This reputation system is fed into the AMP, FirePower, ClamAV, and Open-Source Snort product lines. The tool below allows you to do casual lookups against the Talos File Reputation system. This system limits you to one lookup at a time, and is limitedto
CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Dropper.Qakbot-9146336-0 Dropper Qakbot, aka Qbot, has been around since at least 2008. Qbot primarily targets sensitive information like banking credentials but can also steal FTP credentials and spread across a network using SMB. CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO AMP NAMING CONVENTIONS Find the samples of the naming convention patterns of threats collected in AMP to help with threat analysis that protect organizations before, during, and after an attack. CISCO TALOS INTELLIGENCE GROUP There is a compiled version of scdbg available, but it is probably better to compile it from the source code because of the new API emulations. Covenant Covenant is a relatively new C#-based command and control framework that also allows an attacker (or a red team member) to create payloads based on several infection vectors, including MSBuild. The skeleton code for the MSBuild loader is EMAIL AND SPAM DATA || CISCO TALOS INTELLIGENCE GROUP IP Address Hostname Network Owner The organization name for some larger corporate and educational networks. If organization is a small business or is unavailable, the Internet Service Provider name is CISCO TALOS INCIDENT RESPONSE || CISCO TALOS INTELLIGENCE Cisco Talos Incident Response (CTIR) provides a full suite of proactive and emergency services to help you prepare, respond and recover from a breach. CTIR enables 24 hour emergency response capabilities and direct access to Cisco Talos, the TALOS FILE REPUTATION LOOKUP || CISCO TALOS INTELLIGENCE The Cisco Talos Intelligence Group maintains a reputation disposition on billions of files. This reputation system is fed into the AMP, FirePower, ClamAV, and Open-Source Snort product lines. The tool below allows you to do casual lookups against the Talos File Reputation system. This system limits you to one lookup at a time, and is limitedto
CISCO TALOS INTELLIGENCE GROUP By Neil Jenkins and Matthew Olney. Note: Our guest co-author, Neil Jenkins, is the Chief Analytic Officer at the Cyber Threat Alliance.He leads the CTA's analytic efforts, focusing on the development of threat profiles, adversary playbooks and other CISCO TALOS INTELLIGENCE GROUP The version released on May 18 also included Python versions of EternalBlue (CVE-2017-0144) and EternalRomance (CVE-2017-0147) exploits with a Windows download command line as the payload.The addition of new exploits shows that the actor is actively developing new methods of spreading and following the latest vulnerabilities withpublished PoCs.
CISCO TALOS INTELLIGENCE GROUP By Aleksandar Nikolich. Executive summary. Cisco Talos recently discovered multiple vulnerabilities in macOS’s implementation of SMB server. An adversary could exploit these vulnerabilities to carry out a variety of malicious actions, including revealing sensitive information on the server, bypassing certain cryptographic checks, causing a denial of service or execute remote code on the CISCO TALOS INTELLIGENCE GROUP Cisco Talos recently discovered several vulnerabilities in multiple products from the company WAGO. WAGO produces a line of automationsoftware called
GHIDA - GHIDRA DECOMPILER FOR IDA PRO || CISCO TALOS GhIDA is an IDA Pro plugin that integrates the Ghidra decompiler in the IDA workflow, providing improved navigation and giving users the ability to rename and highlight symbols. SENIOR INCIDENT RESPONSE CONSULTANT What You’ll Do. The Cisco Talos Incident Response Consultant will work within established methodologies to perform a variety of incident response-related activities for Cisco customers. SENIOR INCIDENT RESPONSE COMMANDER What You’ll Do. Work within established methodologies to perform a variety of incident response-related activities for Cisco customers. This will include emergency response to cyber incidents. CISCO TALOS INTELLIGENCE GROUP Threat Name Type Description; Win.Packed.BlackNet-9866245-1 Packed BlackNet is an open-source remote access trojan (RAT) written in VB.NET that is capable of keylogging, capturing credentials stored by web browsers, and taking screenshots of the infected machine.* Software
*
Vulnerability
Information
*
VULNERABILITY INFORMATION* BACK
* Vulnerability Reports * Microsoft Advisories*
Reputation
Center
*
REPUTATION CENTER
* BACK
* IP & Domain Reputation * Talos File Reputation * Reputation Support * AMP Threat Naming Conventions * IP Blacklist Download* AWBO Exercises
* Categories
* Library
*
Support
Communities
*
SUPPORT COMMUNITIES
* BACK
* Snort Community
* ClamAV Community
* SpamCop
* Reputation Center Support* Careers
* Blog
* About
* Cisco Login
Search by IP, domain, or network owner for real-time threat data. EMAIL TRAFFIC OVERVIEW As of: Tue Oct 15 2019 10:02:36 GMT+0000 (Coordinated Universal Time)35
4
5
2
2
4
45
2
2
3
2
3
2
59
5
4
2
10
11
2
2
Map Data
Map data ©2019
Map DataMap data ©2019Map data ©2019
Terms of Use
Legitimate EmailSpamMalware Click on a marker to see more information.Report a map error
500 km
Average daily spam volume for September 2019: 409.51 Billion Spam volume change from previous month: -2% Listen to Talos security experts as they dive into emerging threats, forcing the bad guys to innovate, hacking refrigerators, and other security issues, all with beer.Listen to Podcast
TALOS THREATSOURCE NEWSLETTERS Talos ThreatSource is a regular intelligence update from Cisco Talos, highlighting the biggest threats each week and other security news.View Archives
Subscribe
LATEST VULNERABILITY REPORTS NEW ZERO-DAY REPORTSTALOS REPORT ID
VENDOR
REPORT DATE
TALOS-2019-0915
Foxit
2019-10-07
TALOS-2019-0916
LEADTOOLS
2019-10-07
TALOS-2019-0913
AMD ATI
2019-10-01
TALOS-2019
Microsoft
2019-09-23
TALOS-2019-0899
WAGO
2019-09-20
NEW DISCLOSED VULNERABILITIES REPORTSTALOS REPORT ID
VENDOR
CVE NUMBER
TALOS-2019-0815
NitroPDF
CVE-2019-5046
TALOS-2019-0816
NitroPDF
CVE-2019-5047
TALOS-2019-0814
NitroPDF
CVE-2019-5045
TALOS-2019-0819
NitroPDF
CVE-2019-5050
TALOS-2019-0817
NitroPDF
CVE-2019-5048
All Vulnerability ReportsTALOS BLOG
CHECKRAIN FAKE IOS JAILBREAK LEADS TO CLICK FRAUD OCTOBER 15, 2019 8:33 AMWARREN MERCER
By Warren Mercer andPaul Rascagneres .
INTRODUCTION
Attackers are capitalizing on the recent discovery of a new vulnerability that exists across legacy iOS hardware. Cisco Talos recently discovered a malicious actor using a fake website that claims to give iPhone users the ability to jailbreak their phones. However, this site just prompts users to download a malicious profile which allows the attacker to conduct click-fraud.Checkm8
is a vulnerability in the bootrom of some legacy iOS devices that allows users to control the boot process. The vulnerability impacts all legacy models of the iPhone from the 4S through the X. Thecampaign we'll c...
Read More
Share
*
*
*
*
*
*
* Software
* Reputation Center
* Vulnerability Information * Microsoft Advisory Snort Rules*
* IP Blacklist Download * AMP Naming Conventions * Talos File Reputation* AWBO Exercises
*
*
* Library
* Support Communities* About
* Careers
*
* Blog
* ThreatSource Newsletter * Beers with Talos PodcastCONNECT WITH US
*
*
*
� 2019 Cisco Systems, Inc. and/or its affiliates. All rights reserved. View our Privacy Policyhere.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0