Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://devilsmmo.com
Are you over 18 and want to see adult content?
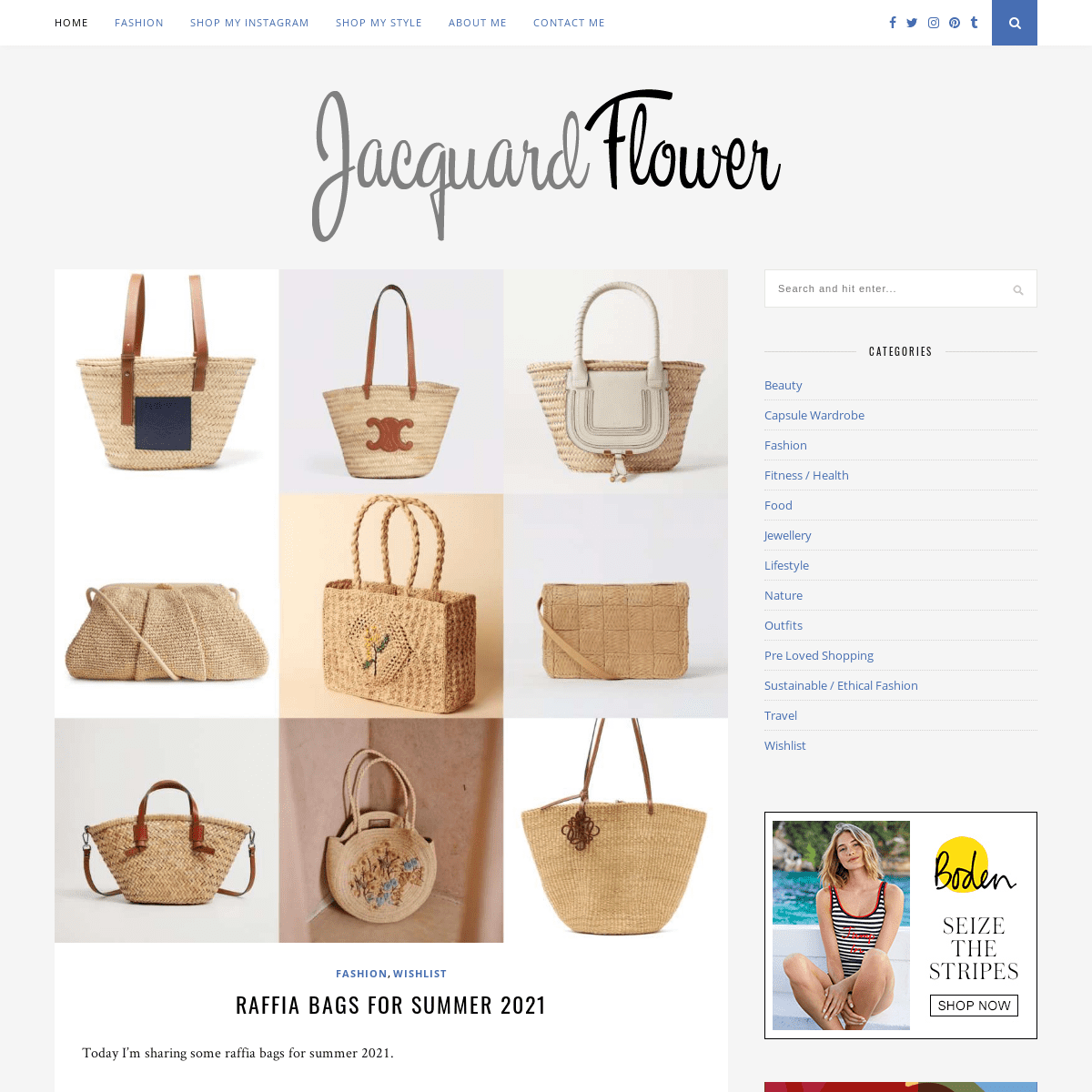
A complete backup of https://www.jacquardflower.uk
Are you over 18 and want to see adult content?
A complete backup of https://minnano-av.com
Are you over 18 and want to see adult content?
A complete backup of https://kiamel.cy
Are you over 18 and want to see adult content?
A complete backup of https://cmsa.org
Are you over 18 and want to see adult content?

A complete backup of https://friv-games.com
Are you over 18 and want to see adult content?

A complete backup of https://hutchchamber.com
Are you over 18 and want to see adult content?

A complete backup of https://rosconmarket.ru
Are you over 18 and want to see adult content?
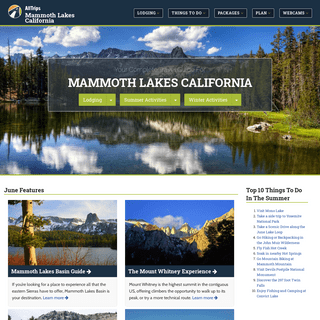
A complete backup of https://allmammoth.com
Are you over 18 and want to see adult content?

A complete backup of https://senperfect.com
Are you over 18 and want to see adult content?

A complete backup of https://yunkong56.com
Are you over 18 and want to see adult content?
A complete backup of https://dominicana.pro
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://canonlawmadeeasy.com
Are you over 18 and want to see adult content?
A complete backup of https://islandcruiser.info
Are you over 18 and want to see adult content?

A complete backup of https://kinofanonline.ru
Are you over 18 and want to see adult content?
A complete backup of https://riseproject.ro
Are you over 18 and want to see adult content?

A complete backup of https://gabrielledouglas.com
Are you over 18 and want to see adult content?

A complete backup of https://atkinsfarms.com
Are you over 18 and want to see adult content?
A complete backup of https://alfapeople.com
Are you over 18 and want to see adult content?
A complete backup of https://urbisbaiamare.ro
Are you over 18 and want to see adult content?

A complete backup of https://householdadvice.net
Are you over 18 and want to see adult content?
A complete backup of https://redapes.org
Are you over 18 and want to see adult content?
A complete backup of https://abcya11.us
Are you over 18 and want to see adult content?

A complete backup of https://emmikochteinfach.de
Are you over 18 and want to see adult content?
Text
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only)I2P SERVICES
HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select I2P BROWSER SETUP TUTORIAL ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slowHOW TO USE I2P
4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
IS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called. THE TIN HATTUTORIALSARTICLESABOUTADD-ONSALTERNATIVESDARKNETS Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only)I2P SERVICES
HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select I2P BROWSER SETUP TUTORIAL ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slowHOW TO USE I2P
4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
IS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select TAHOE-LAFS TUTORIAL (PART 1) And indeed, Tahoe-LAFS is powerful, well-designed software. This tutorial is the first of three parts. This part focuses on explaining what Tahoe-LAFS is and the broad mechanics of how it works as simply as possible, without losing too much important detail. Indeed, while you could likely get the gist of Tahoe-LAFS across in a few sentences,to
HOW SECURE IS EMAIL? Improving Email Security. Without going into too much detail, there are several ways that you can boost your email security. First of all, turn on two factor authentication, which will make your account vastly more difficult to hack. Second, try out PGP encryption. Although it is a bit difficult to use, PGP will encrypt all your emails end-toTOR AND VPN
Tor To VPN. Computer > Encrypt w/ VPN > Tor Entry > Tor Exit > Decrypt w/ VPN > Destination. This configuration, to me, brings a greater degree of advantage to running both Tor and a VPN than the previous configuration does. Routing your traffic through Tor to your VPN has the major benefit of hiding traffic from malicious exit nodes. HTTPS-EVERYWHERE TUTORIAL Created by the Electronic Frontier Foundation, HTTPS Everywhere is a Firefox and Chrome add-on that enables HTTPS whenever it is available, and fixes those problematic links. The beauty of this is that it stomps all over the misconception that encryption is complicated and cumbersome. All you have to do is install the add-on and a largeportion
CHOOSING PRIVATE & SECURE EMAIL I've said it before and I'll say it again, email is one of the most important online services that we use. It is the hub to which most of our online accounts are linked; it is where we receive receipts from purchases; it is where we communicate with others, and so much more. IN DEFENSE OF BROWSER-BASED EMAIL ENCRYPTION ‘Why would I ever use browser-based email encryption?’ This statement summarizes a position I held for quite some time. The idea that anyone would trust their private communications to browser-based encryption seemed ridiculous, especially when we consider what happened to Hushmail users.I’m not alone in this either, as I’ve seen a number of comments posted online preaching the THE BEST VPN KILL SWITCH FOR LINUX USING EASY FIREWALL RULES I’ve written previously about the dangers of your VPN dropping and ways to prevent it from being disastrous. Indeed, while many VPN clients have drop protection built in, Linux users often are forced to use their built in Network Manager to connect to a VPN, which notably lacks drop protection. THE TIN HATTUTORIALSARTICLESABOUTADD-ONSALTERNATIVESDARKNETS Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. SelectI2P SERVICES
ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. I2P BROWSER SETUP TUTORIALHOW TO USE I2P
4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slow THE TIN HATTUTORIALSARTICLESABOUTADD-ONSALTERNATIVESDARKNETS Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. SelectI2P SERVICES
ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. I2P BROWSER SETUP TUTORIALHOW TO USE I2P
4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slowALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW SECURE IS EMAIL? Improving Email Security. Without going into too much detail, there are several ways that you can boost your email security. First of all, turn on two factor authentication, which will make your account vastly more difficult to hack. Second, try out PGP encryption. Although it is a bit difficult to use, PGP will encrypt all your emails end-to CHOOSING PRIVATE & SECURE EMAIL I've said it before and I'll say it again, email is one of the most important online services that we use. It is the hub to which most of our online accounts are linked; it is where we receive receipts from purchases; it is where we communicate with others, and so much more.TORBIRDY TUTORIAL
TorBirdy is a Mozilla Thunderbird add-on (meaning it also works for IceDove) which makes a few security optimizations to Thunderbird, and reroutes your mail through the Tor network. Routing your mail through Tor means that your emails will be bounced around three different computers across the globe before finally being sent to your emailservice.
QUBES OS | MY EXPERIENCE SO FAR Qubes OS | My Experience So Far. About three weeks ago I moved from Fedora 20 to QubesOS, and so far the best way to describe it is as a bumpy road that's surrounded by four foot thick concrete walls. If you've read all about Qubes already, skip on down to the next section. If you're new to Qubes, it's an operating system with a very intense I2P-BOTE INTRODUCTION AND TUTORIAL I2P-Bote is a messaging platform that operates over the the I2P network. It functions similarly to email, however it has a few fundamental properties which set it into a class of its own. These properties are security, anonymity, and resilience. THE BEST VPN KILL SWITCH FOR LINUX USING EASY FIREWALL RULES I’ve written previously about the dangers of your VPN dropping and ways to prevent it from being disastrous. Indeed, while many VPN clients have drop protection built in, Linux users often are forced to use their built in Network Manager to connect to a VPN, which notably lacks drop protection. THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS The privacy failings of the internet of things get worse when we realize its inevitable health applicationsIS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
THE TIN HAT
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select I2P BROWSER SETUP TUTORIAL ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor.I2P SERVICES
HOW TO USE I2P
TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slowTOR AND VPN
Tor To VPN. Computer > Encrypt w/ VPN > Tor Entry > Tor Exit > Decrypt w/ VPN > Destination. This configuration, to me, brings a greater degree of advantage to running both Tor and a VPN than the previous configuration does. Routing your traffic through Tor to your VPN has the major benefit of hiding traffic from malicious exit nodes.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
THE TIN HAT
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select I2P BROWSER SETUP TUTORIAL ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor.I2P SERVICES
HOW TO USE I2P
TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slowTOR AND VPN
Tor To VPN. Computer > Encrypt w/ VPN > Tor Entry > Tor Exit > Decrypt w/ VPN > Destination. This configuration, to me, brings a greater degree of advantage to running both Tor and a VPN than the previous configuration does. Routing your traffic through Tor to your VPN has the major benefit of hiding traffic from malicious exit nodes.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ALL ARTICLES
A list of all the articles available on The Tin HatABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only)DARKNET TUTORIALS
19 Jan 2014. Learn when to use Tor or a VPN with this guide. This tutorial teaches you how each of them works, and whether one is betteror worse.
WHAT IS RANSOMWARE AND HOW DO I PROTECT AGAINST IT? Ransomware is everywhere, and it seems like it’s destroying everything. It’s attacking schools, hospitals, and businesses of all sizes, forcing them to pay tens of thousands of dollars in the hopes that they won’t lose all of their precious data.. Modern ransomware works by infecting a computer, encrypting all of its files so that nobody can read them without a secret key, and then HOW SECURE IS EMAIL? Improving Email Security. Without going into too much detail, there are several ways that you can boost your email security. First of all, turn on two factor authentication, which will make your account vastly more difficult to hack. Second, try out PGP encryption. Although it is a bit difficult to use, PGP will encrypt all your emails end-toVPN KILL SWITCH
Check out my new VPN kill switch guide that uses simple firewall rules to better protect against VPN drops!. VPNs are a good way to increase your privacy, but it's not uncommon for them to disconnect. Unfortunately, when this happens it can completely nullify the I2P-BOTE INTRODUCTION AND TUTORIAL I2P-Bote is a messaging platform that operates over the the I2P network. It functions similarly to email, however it has a few fundamental properties which set it into a class of its own. These properties are security, anonymity, and resilience.TORBIRDY TUTORIAL
TorBirdy is a Mozilla Thunderbird add-on (meaning it also works for IceDove) which makes a few security optimizations to Thunderbird, and reroutes your mail through the Tor network. Routing your mail through Tor means that your emails will be bounced around three different computers across the globe before finally being sent to your emailservice.
NEW I2P PORTAL FOR THETINHAT TheTinHat has moved to a new server, with a new I2P hidden service toaccompany it.
THE TIN HAT
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. SelectHOW TO USE I2P
TOR AND VPN
Tor To VPN. Computer > Encrypt w/ VPN > Tor Entry > Tor Exit > Decrypt w/ VPN > Destination. This configuration, to me, brings a greater degree of advantage to running both Tor and a VPN than the previous configuration does. Routing your traffic through Tor to your VPN has the major benefit of hiding traffic from malicious exit nodes. TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slow 4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS The privacy failings of the internet of things get worse when we realize its inevitable health applicationsIS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.THE TIN HAT
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. 07 Apr 2017. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. SelectHOW TO USE I2P
TOR AND VPN
Tor To VPN. Computer > Encrypt w/ VPN > Tor Entry > Tor Exit > Decrypt w/ VPN > Destination. This configuration, to me, brings a greater degree of advantage to running both Tor and a VPN than the previous configuration does. Routing your traffic through Tor to your VPN has the major benefit of hiding traffic from malicious exit nodes. TOR VS VPN | WHEN TO USE WHICH When To Use a VPN. At this point you're probably thinking that Tor is better due to the anonymity that it provides. However, Tor's anonymity comes at the cost of speed, as it is generally much slower than a VPN. While it's still usually fast enough for browsing static sites, downloading torrents or watching HD videos is not only painfully slow 4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES There are two ways that this happens. First, Brave will send a significant portion (55%) of the money it gets from advertisers purchasing ad space on its ad network to the publisher in the form of Bitcoin. To fund Brave’s development, it will keep 15%, and 15% willbe
THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS The privacy failings of the internet of things get worse when we realize its inevitable health applicationsIS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE First, head over to Vuze’s website and download and install the Vuze client. Next, open Vuze and head to the Tools menu, navigate to Plugins, and finally the Installation Wizard. Select By List, click Next, and scroll down until you find the I2PHelper plugin. Select ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. TAHOE-LAFS TUTORIAL (PART 1) And indeed, Tahoe-LAFS is powerful, well-designed software. This tutorial is the first of three parts. This part focuses on explaining what Tahoe-LAFS is and the broad mechanics of how it works as simply as possible, without losing too much important detail. Indeed, while you could likely get the gist of Tahoe-LAFS across in a few sentences,to
HOW SECURE IS EMAIL? Improving Email Security. Without going into too much detail, there are several ways that you can boost your email security. First of all, turn on two factor authentication, which will make your account vastly more difficult to hack. Second, try out PGP encryption. Although it is a bit difficult to use, PGP will encrypt all your emails end-to CHOOSING PRIVATE & SECURE EMAIL I've said it before and I'll say it again, email is one of the most important online services that we use. It is the hub to which most of our online accounts are linked; it is where we receive receipts from purchases; it is where we communicate with others, and so much more. THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS If you’re reading this blog, there’s a good chance that you have more control than the average person over your privacy. You’re probably using Tor or a VPN, or an adblocker at the very least. WHAT IS TWO FACTOR AUTHENTICATION (2FA) AND WHY USE IT? Unless, of course, you’ve used two factor authentication. Indeed, right now two factor authentication (2FA) is the best practical way to protect yourself from all of these threats. All 2FA entails is simply having a second factor, something other than your WHY I SUPPORT TOR AND I2P I2P and Tor are this third option, allowing us to reap the benefits of the internet, without the cost of privacy. Moreover, the agency of anonymizing networks permeates far deeper than a first world choice between power and privacy. In countries who’s oppressive governments not only heavily surveil the internet, but censor it, Tor and I2P areTHE TIN HAT
Is Bitcoin Actually Private? A primer on privacy and Bitcoin, why it matters for fungibility, and what cryptocurrencies are trying to fixit.
ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREEHOW TO MAKE UTORRENT ANONYMOUSTORRENT ANONYMOUS FREEWAYS TO DOWNLOAD TORRENTS Learn the pros and cons of using a VPN to torrent, as well as how to use I2P to anonymously torrent for free!HOW TO USE I2P
TOR VS VPN | WHEN TO USE WHICH Tor and VPNs often get compared side-by-side, but unfortunately they are often conflated and treated as competing products. However, in reality neither is necessarily better than the other. 4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YESBRAVE BROWSER DOWNLOAD PCBRAVE WEB BROWSER REVIEW I want you to use the Brave browser.Scratch that. I really want you to use the Brave browser.Why? To start, because I’m selfish. Indeed, as a small-scale publisher who doesn’t believe in using third-party, privacy-crushing advertisements, you using Brave actually helps memake money.
TOR AND VPN
Using both Tor and a VPN can be tricky, and even dangerous if done improperly. Routing VPN traffic through Tor or vice versa has certain major benefits, as well as disadvantages, depending on your threatmodel.
THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS The privacy failings of the internet of things get worse when we realize its inevitable health applicationsIS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.THE TIN HAT
Is Bitcoin Actually Private? A primer on privacy and Bitcoin, why it matters for fungibility, and what cryptocurrencies are trying to fixit.
ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREEHOW TO MAKE UTORRENT ANONYMOUSTORRENT ANONYMOUS FREEWAYS TO DOWNLOAD TORRENTS Learn the pros and cons of using a VPN to torrent, as well as how to use I2P to anonymously torrent for free!HOW TO USE I2P
TOR VS VPN | WHEN TO USE WHICH Tor and VPNs often get compared side-by-side, but unfortunately they are often conflated and treated as competing products. However, in reality neither is necessarily better than the other. 4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YESBRAVE BROWSER DOWNLOAD PCBRAVE WEB BROWSER REVIEW I want you to use the Brave browser.Scratch that. I really want you to use the Brave browser.Why? To start, because I’m selfish. Indeed, as a small-scale publisher who doesn’t believe in using third-party, privacy-crushing advertisements, you using Brave actually helps memake money.
TOR AND VPN
Using both Tor and a VPN can be tricky, and even dangerous if done improperly. Routing VPN traffic through Tor or vice versa has certain major benefits, as well as disadvantages, depending on your threatmodel.
THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS The privacy failings of the internet of things get worse when we realize its inevitable health applicationsIS TOR SAFE?
One of the most common questions asked about Tor is whether it is safe enough to be relied upon. While this is a perfectly useful question that should be encouraged, unfortunately it often results in battle-flags being raised and the cavalry being called.ALL TUTORIALS
Tahoe-LAFS Tutorial (Part 1) | Decentralized Cloud Storage. Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics ofTahoe-LAFS
ABOUT THE TIN HAT
The Tin Hat uses Piwik Analytics. This means that the following information is recorded when you visit the site: An Anonymized IP Address (first two octets only) HOW TO ACTUALLY TORRENT PRIVATELY & ANONYMOUSLY FOR FREE Learn the pros and cons of using a VPN to torrent, as well as how to use I2P to anonymously torrent for free! ZERONET | INTRODUCTION & SETUP TUTORIAL The ability to host hidden services is the hallmark feature of both Tor and I2P.For those that haven’t ventured into ‘the darknet’, hidden services are essentially websites that can’t be seen on the regular internet, are often run by anonymous operators, are end to end encrypted, and, because of these features, are very hard to censor. TAHOE-LAFS TUTORIAL (PART 1) Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS If you’re reading this blog, there’s a good chance that you have more control than the average person over your privacy. You’re probably using Tor or a VPN, or an adblocker at the very least. CHOOSING PRIVATE & SECURE EMAIL I've said it before and I'll say it again, email is one of the most important online services that we use. It is the hub to which most of our online accounts are linked; it is where we receive receipts from purchases; it is where we communicate with others, and so much more. WHAT IS TWO FACTOR AUTHENTICATION (2FA) AND WHY USE IT? What 2FA is, why you should use it, and why we need FIDO U2F. HOW SECURE IS EMAIL? Not very, but to understand why we need to unpack the various points at which email could be intercepted. Imagine sending someone an email. First, the email needs to travel from your computer to your email provider (Gmail, for example). WHY I SUPPORT TOR AND I2P ‘The Darknet’: an underground cacophony of criminal activity, where fiber optic cables transmit a buzzing white noise of narcotics and pornographic material, all of which is protected under the veil of the most arcane techno-black-magic-munition, cryptography.*
* Tutorials
* All
* Add-ons
* Alternatives
* Darknets
* Messaging
* Other
* Articles
* About
WELCOME TO THE TIN HAT EXPLORE ONLINE PRIVACY THROUGH:Tutorials Articles
LATEST POSTS
IS BITCOIN ACTUALLY PRIVATE?23 Jul 2017
A primer on privacy and Bitcoin, why it matters for fungibility, and what cryptocurrencies are trying to fix it. SLANTWISE ACTION | HOW WHATSAPP, SIGNAL, AND STEEMIT ARE FEEDING THERESISTANCE
14 Jul 2017
Can people meaningfully resist surveillance without knowing it? THE INTERNET OF THINGS ISN'T JUST ABOUT NETWORKED JUICERS | PRIVACY, HEALTH, & TECHNOLOGY26 May 2017
The privacy failings of the internet of things get worse when we realize its inevitable health applications BUT THE DATA SAYS SO | WHY DATA CAN'T EXIST IN A SOCIAL VACUUM19 May 2017
Some people still don't grasp that data can't be removed from society (and it's racist tendencies) TAHOE-LAFS TUTORIAL (PART 3) | RUNNING A STORAGE NODE ON I2P12 May 2017
Learn how to contribute to Tahoe-LAFS on I2P by running your ownstorage node!
WHAT IS RANSOMWARE AND HOW DO I PROTECT AGAINST IT?05 May 2017
Learn how ransomware is shutting down entire institutions, and how you can defend against it HOW SECURE IS EMAIL?05 May 2017
A primer on email security. Learn where email is weak and how to makeit stronger.
TAHOE-LAFS TUTORIAL (PART 2) | RUNNING TAHOE-LAFS ON I2P22 Apr 2017
Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial shows you how to run Tahoe-LAFS using I2P on Linux TAHOE-LAFS TUTORIAL (PART 1) | DECENTRALIZED CLOUD STORAGE07 Apr 2017
Tahoe-LAFS offers decentralized, resilient, and secure storage. This tutorial is the first in a three part series that teaches you the basics of Tahoe-LAFS HOW DO I START AN ANONYMOUS BLOG?31 Mar 2017
If you want to start an anonymous blog, there's a lot of considerations. This primer will point you to the tools and tips you need to get started. PRIVACY IN AMERICA NOW STARTS WITH A VPN | A BRIEF NOTE ON THREAT MODELLING AND LESSER EVILS23 Mar 2017
American ISPs are now selling your data, and despite controversy, a VPN isn't necessarily a bad idea. 4 REASONS TO DITCH YOUR BROWSER AND USE BRAVE (AND YES, ONE OF THEM ISBITCOIN)
17 Mar 2017
Brave is disrupting the entire online advertising model for the better. Learn what it can do for you. IS TOR SAFE? | ASSESSING 5 CLAIMS ABOUT TOR’S SECURITY09 Mar 2017
Is Tor funded by the US government? Can it be hacked? Can it be broken by mere statistics? This article unpacks those claims. ZERONET | INTRODUCTION & SETUP TUTORIAL03 Mar 2017
Discover how ZeroNet could revolutionize Tor and I2P's hidden services, before learning how to install it yourself WHY LOCATION PRIVACY MATTERS24 Feb 2017
Location data says a lot about us, with or without Stingrays at work. We need to take it more seriously. WHAT IS DEVICE FINGERPRINTING?17 Feb 2017
Learn what browser fingerprinting is and how it canb e used to trackyou online.
WHAT IS THE TIN HAT? Privacy is hard. With ever-increasing amounts of data being collected about us through an ever-widening set of methods, fighting back against surveillance often seems like a lost cause. The goal of this site is to convince you otherwise; it is to show that meaningful privacy is both achievable and desirable. Through tutorials walking you through privacy-preserving technologies, and articles discussing issues surrounding privacy, surveillance, big-data, and technology, TheTinHat.com is a site that helps you find shelter from surveillance.Learn More
* Contact
* Privacy Policy
* RSS Feed
* Support Me
* Hidden Services:
* Tor
* I2P
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0
