Are you over 18 and want to see adult content?
More Annotations

A complete backup of freeamazongiftcardsnow.com
Are you over 18 and want to see adult content?

A complete backup of zxepersonalloansonlinesmall.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://jonentine.com
Are you over 18 and want to see adult content?

A complete backup of https://7da.club
Are you over 18 and want to see adult content?

A complete backup of https://mines.gov.in
Are you over 18 and want to see adult content?
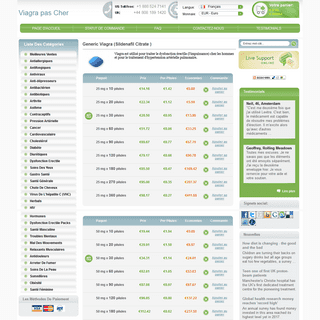
A complete backup of https://viagrapascherfr.com
Are you over 18 and want to see adult content?
A complete backup of https://cnr.org.br
Are you over 18 and want to see adult content?

A complete backup of https://goldco.com
Are you over 18 and want to see adult content?
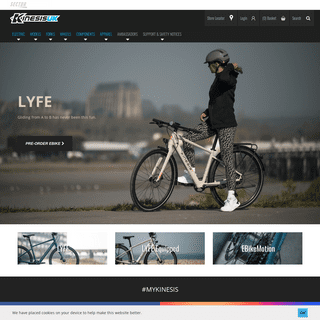
A complete backup of https://kinesisbikes.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://ridgid.eu
Are you over 18 and want to see adult content?

A complete backup of https://lovelifefixer.com
Are you over 18 and want to see adult content?
A complete backup of https://sunnyway.com
Are you over 18 and want to see adult content?

A complete backup of https://bihealth.org
Are you over 18 and want to see adult content?

A complete backup of https://miningcrusher.pw
Are you over 18 and want to see adult content?
Text
TONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evilTONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evil THE DEATH OF BITCOIN The Death of Bitcoin. The road of innovation is paved with the corpses of outmoded technologies. Throughout history there are countless examples of a technology presumed to be the “next big thing” starting to gain traction, only to find itself outmoded in the lightof a
"DCI" IN RUBY IS COMPLETELY BROKEN • TONY ARCIERI Far and away, the main pattern we see described as “DCI” in Ruby works by using a mix-in on an individual instance. This pattern is what I will be referring to from now on as “DCI”: Let’s look at what’s happening here. First, we’re mixing the “Fool” module into the metaclass of the “rubyist” object. Since this is an ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A GENTLE INTRODUCTION TO NIO4R: LOW-LEVEL PORTABLE July 12, 2016 A gentle introduction to nio4r: low-level portable asynchronous I/O for Ruby. Rails 5.0 was recently released, and with it came ActionCable, a new part of the framework to put WebSockets “on Rails”.ActionCable has had something of a sordid history, from taking Rails Core developer Aaron Patterson by surprise when he first heard of it at a RailsConf keynote to at one point INTRODUCING TJSON, A STRICTER, TYPED FORM OF JSON Now read this CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL� attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. CREAM: THE SCARY SSL ATTACK YOU’VE PROBABLY NEVER HEARD OF CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL † attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. Apple’s SecureTransport, used by both iOS and OS X, went down next with the “goto fail” vulnerability. VOLAPÜK: A CAUTIONARY TALE FOR ANY LANGUAGE COMMUNITY Volapük was a hit! Volapük clubs started popping up throughout Europe. Large conventions were held first in Friedrichshafen in 1884, then Munich in 1887, and finally Paris in 1889. The first two conventions were held in German, but by the third conference, everyone was speaking in Volapük, even the waiters! Kerckhoffs, who was anearly
IMPERFECT FORWARD SECRECY: THE COMING CRYPTOCALYPSE Imperfect Forward Secrecy: The Coming Cryptocalypse. If the Snowden debacle has accomplished anything, it’s raising public awareness in cryptography. This has spawned some sort of meme that if we use “perfect forward secrecy”, our communications are protected from the NSA! Various blog posts and articles in major newspapers haveconferred
AN OPEN LETTER TO MATZ ON RUBY TYPE SYSTEMS April 29, 2015 An open letter to Matz on Ruby type systems. Hi Matz, I really enjoyed your keynote at RubyConf 2014.The most interesting part of it to me was where you talked about how Ruby 3.0 might include some sort of type system. THE CLOUD ISN’T DEAD. IT JUST NEEDS TO EVOLVE June 11, 2013. The cloud isn’t dead. It just needs to evolve. At my previous job my daily commute took me past 611 Folsom Street in San Francisco. This building is infamous for being the home of Room 641A, where a whistleblower, Mark Klein, revealed that the NSA had created a secret room and placed beam splitters on fiber optic cablesTONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evilTONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evil THE DEATH OF BITCOIN The Death of Bitcoin. The road of innovation is paved with the corpses of outmoded technologies. Throughout history there are countless examples of a technology presumed to be the “next big thing” starting to gain traction, only to find itself outmoded in the lightof a
"DCI" IN RUBY IS COMPLETELY BROKEN • TONY ARCIERI Far and away, the main pattern we see described as “DCI” in Ruby works by using a mix-in on an individual instance. This pattern is what I will be referring to from now on as “DCI”: Let’s look at what’s happening here. First, we’re mixing the “Fool” module into the metaclass of the “rubyist” object. Since this is an ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A GENTLE INTRODUCTION TO NIO4R: LOW-LEVEL PORTABLE July 12, 2016 A gentle introduction to nio4r: low-level portable asynchronous I/O for Ruby. Rails 5.0 was recently released, and with it came ActionCable, a new part of the framework to put WebSockets “on Rails”.ActionCable has had something of a sordid history, from taking Rails Core developer Aaron Patterson by surprise when he first heard of it at a RailsConf keynote to at one point INTRODUCING TJSON, A STRICTER, TYPED FORM OF JSON Now read this CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL� attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. CREAM: THE SCARY SSL ATTACK YOU’VE PROBABLY NEVER HEARD OF CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL † attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. Apple’s SecureTransport, used by both iOS and OS X, went down next with the “goto fail” vulnerability. VOLAPÜK: A CAUTIONARY TALE FOR ANY LANGUAGE COMMUNITY Volapük was a hit! Volapük clubs started popping up throughout Europe. Large conventions were held first in Friedrichshafen in 1884, then Munich in 1887, and finally Paris in 1889. The first two conventions were held in German, but by the third conference, everyone was speaking in Volapük, even the waiters! Kerckhoffs, who was anearly
IMPERFECT FORWARD SECRECY: THE COMING CRYPTOCALYPSE Imperfect Forward Secrecy: The Coming Cryptocalypse. If the Snowden debacle has accomplished anything, it’s raising public awareness in cryptography. This has spawned some sort of meme that if we use “perfect forward secrecy”, our communications are protected from the NSA! Various blog posts and articles in major newspapers haveconferred
AN OPEN LETTER TO MATZ ON RUBY TYPE SYSTEMS April 29, 2015 An open letter to Matz on Ruby type systems. Hi Matz, I really enjoyed your keynote at RubyConf 2014.The most interesting part of it to me was where you talked about how Ruby 3.0 might include some sort of type system. THE CLOUD ISN’T DEAD. IT JUST NEEDS TO EVOLVE June 11, 2013. The cloud isn’t dead. It just needs to evolve. At my previous job my daily commute took me past 611 Folsom Street in San Francisco. This building is infamous for being the home of Room 641A, where a whistleblower, Mark Klein, revealed that the NSA had created a secret room and placed beam splitters on fiber optic cablesTONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evilTONY ARCIERI
Introducing Miscreant: a multi-language misuse resistant encryption library. For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic THE TETHER CONUNDRUM: A QUICK BACKSTORY • TONY ARCIERI The Tether Conundrum: A Quick Backstory. NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so takethat
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS The Tether Conundrum Part 2: The Plot Thickens. NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacingmuch
RUST IN 2019: SECURITY, MATURITY, STABILITY Rust in 2019: Security, Maturity, Stability. I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if youactually
A TALE OF TWO CRYPTOCURRENCIES: ETHEREUM AND BITCOIN’S A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. It’s been one of the most interesting months in the history of cryptocurrency. The price of Bitcoin has soared up to nearly $800 (then dropped to $675 as $19 million in BTC hit the THE DEATH OF BITCOIN A QUICK TOUR OF RUST’S TYPE SYSTEM PART 1: SUM TYPES (A.KRUST CHARACTER TYPERUST DATA TYPESRUST GET TYPERUST GET TYPE OF VARIABLERUST REFERENCE TYPERUST TYPE VARIABLE November 10, 2016 A quick tour of Rust’s Type System Part 1: Sum Types (a.k.a. Tagged Unions) Rust is one of those hip new programming languages you might get tired of hearing about on the Hacker News, but talking with people who have heard of Rust but haven’t actually looked into it in depth, I feel like what Rust actually offers you as a programmer is often poorly communicated. WHAT’S WRONG WITH IN-BROWSER CRYPTOGRAPHY? December 30, 2013 What’s wrong with in-browser cryptography? Above image taken from Douglas Crockford’s Principles of Security talk. If you’re reading this, then I hope that sometime somebody or some web site told you that doing cryptography in a web browser is a bad idea. ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS January 8, 2018 A short statement regarding Ashley Williams’ abusers. It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team.. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evil THE DEATH OF BITCOIN The Death of Bitcoin. The road of innovation is paved with the corpses of outmoded technologies. Throughout history there are countless examples of a technology presumed to be the “next big thing” starting to gain traction, only to find itself outmoded in the lightof a
"DCI" IN RUBY IS COMPLETELY BROKEN • TONY ARCIERI Far and away, the main pattern we see described as “DCI” in Ruby works by using a mix-in on an individual instance. This pattern is what I will be referring to from now on as “DCI”: Let’s look at what’s happening here. First, we’re mixing the “Fool” module into the metaclass of the “rubyist” object. Since this is an ALL THE CRYPTO CODE YOU’VE EVER WRITTEN IS PROBABLY BROKEN Most of the cryptographic APIs you’ve ever encountered have probably made you run a gambit of choices for how you want to encrypt data. You might think AES-256 is the way to go, but by default your crypto API might select ECB mode, which is so bad and terribly insecure it isn’t even worth talking about. Perhaps you select CBC or CTR mode A GENTLE INTRODUCTION TO NIO4R: LOW-LEVEL PORTABLE July 12, 2016 A gentle introduction to nio4r: low-level portable asynchronous I/O for Ruby. Rails 5.0 was recently released, and with it came ActionCable, a new part of the framework to put WebSockets “on Rails”.ActionCable has had something of a sordid history, from taking Rails Core developer Aaron Patterson by surprise when he first heard of it at a RailsConf keynote to at one point INTRODUCING TJSON, A STRICTER, TYPED FORM OF JSON Now read this CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL� attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. CREAM: THE SCARY SSL ATTACK YOU’VE PROBABLY NEVER HEARD OF CREAM: the scary SSL attack you’ve probably never heard of. 2014 was a year packed full of the discovery of new SSL † attacks. First we found Java was vulnerable to a new type of “Bleichenbacher” attack. Apple’s SecureTransport, used by both iOS and OS X, went down next with the “goto fail” vulnerability. VOLAPÜK: A CAUTIONARY TALE FOR ANY LANGUAGE COMMUNITY Volapük was a hit! Volapük clubs started popping up throughout Europe. Large conventions were held first in Friedrichshafen in 1884, then Munich in 1887, and finally Paris in 1889. The first two conventions were held in German, but by the third conference, everyone was speaking in Volapük, even the waiters! Kerckhoffs, who was anearly
IMPERFECT FORWARD SECRECY: THE COMING CRYPTOCALYPSE Imperfect Forward Secrecy: The Coming Cryptocalypse. If the Snowden debacle has accomplished anything, it’s raising public awareness in cryptography. This has spawned some sort of meme that if we use “perfect forward secrecy”, our communications are protected from the NSA! Various blog posts and articles in major newspapers haveconferred
AN OPEN LETTER TO MATZ ON RUBY TYPE SYSTEMS April 29, 2015 An open letter to Matz on Ruby type systems. Hi Matz, I really enjoyed your keynote at RubyConf 2014.The most interesting part of it to me was where you talked about how Ruby 3.0 might include some sort of type system. THE CLOUD ISN’T DEAD. IT JUST NEEDS TO EVOLVE June 11, 2013. The cloud isn’t dead. It just needs to evolve. At my previous job my daily commute took me past 611 Folsom Street in San Francisco. This building is infamous for being the home of Room 641A, where a whistleblower, Mark Klein, revealed that the NSA had created a secret room and placed beam splitters on fiber optic cablesSvbtle Menu
* Tony Arcieri is writing on the Svbtle network.* @bascule
* rss feed
*
-------------------------* about svbtle
* sign up
Tony Arcieri
TONY ARCIERI
HI THERE. THESE DAYS I DABBLE IN CRYPTOGRAPHY, BUT IN THE PAST MADE THE CELLULOID ACTOR FRAMEWORK FOR RUBY AND THE REIA PROGRAMMINGLANGUAGE
* @bascule
READ THIS FIRST
RUST 2020: TOWARDS A 1.0 CRATE ECOSYSTEM The Rust language itself went 1.0 in 2015. And yet, almost 5 years later, at least in my anecdotal assessment talking to and reading things written by current or potential users, there is still a sense that the language is still in some way unfinished and a bit rougharound the edges.
I sympathize with these concerns. There are various language-level issues which are partly to blame for this. The absence of a comprehensive story around asynchronous I/O and event-driven programs in general has been one of them, but that all changes… today… with the long awaited stabilization of async/await in the Rust 1.39 release along with the release of futures v0.3.0earlier this week.
There are other core features which many desire. In my Rust in 2019 blog post I wrote about const generics as the 1 in my top 3, along with async/await and Pin, which both shipped this year. Others long for even... Continue reading → -------------------------Nov 5, 2019
FACTUAL INACCURACIES OF “FACEBOOK LIBRA IS ARCHITECTURALLYUNSOUND”
A post by Stephen Diehl about Facebook Libra is making the rounds this morning. It makes a number of claims about flaws in the software. Many of these claims are factually inaccurate. I consider it to be a gish gallop that bombards you with a bunch of negative claims, many of which are false or at best, specious. For context, I am a contributor to OpenLibra, a group independent of Facebook (or should I say “FACEBOOK”) who are experimenting with operating the Libra software. My company also operates other BFT-based cryptocurrencies, such as the Cosmos Network which is based on Tendermint BFT. Prior to that I worked extensively in credit card processing at companies like Square and LivingSocial, also doing card processing integrations at several companies before that. This post, like the original, is intended to be purely technical, and if it were to talk about my opinions of a... Continue reading → -------------------------Jan 15, 2019
RUST IN 2019: SECURITY, MATURITY, STABILITY _NOTE: This is a work-in-progress I have put online a bit early. Check back later for the complete version_ I’ve been a day-to-day Rust user for nearly 5 years now. In that time I’ve perpetually felt like Rust is “the language that will be awesome tomorrow”. Rust has always felt like it had so much promise and potential, but if you actually sat down and tried to use it, the result was akin to trying to assemble a complex mechanism but you were always missing a few pieces. I managed to suffer through it in the long long ago of 2014, and each year it’s gotten better, until in 2018 I could confidently say “Now’s a great time to start learning Rust”. But how about actually writing a real-world Rust application and deploying it toproduction?
2018 marked my second year as a full-time Rust developer, and I’m happy to say it’s the first year I shipped production Rust applications (not just... Continue reading → -------------------------Jun 26, 2018
THE TETHER CONUNDRUM PART 2: THE PLOT THICKENS _NOTE: For more background including a brief introduction to Tether itself, see part 1 of this series: The Tether Conundrum: A Quick Backstory. This post will largely assume you have read that first, or are at least familiar with the material it covers. Also thanks to Bitfinex'ed for surfacing much of the material covered in this post._ There have been plenty of developments surrounding Tether in the months since I wrote the first post in this series in January: * Tether’s previous “auditor” (who never completed an audit), Friedman LLP, removed all mentions of Tether from their web site. Shortly thereafter Tether would announce that they are dissolving their relationship with Friedman. Despite claims of “frequent professional audits” on their web site, to date Tether has nevercompleted an audit.
* The US Commodity Futures Trading Commission (CFTC) sent subpoenas to Bitfinex and Tether... Continue reading → -------------------------Jan 19, 2018
THE TETHER CONUNDRUM: A QUICK BACKSTORY _NOTE: This post is fourth in a series I’ve written about Bitcoin, including The Death of Bitcoin, On the dangers of a blockchain monoculture, and A tale of two cryptocurrencies: Ethereum and Bitcoin’s ongoing challenges. I am a former HODLer, present nocoiner, and perpetual Bitcoin bear, so take that for what you will. Well, the nocoiner part is a bit of a lie: I have a JPCoin._ Figure 1: If we correlate the declining murder rate with web browser usage, we can deduce that Internet Explorer was the major causal factor in homicide rates. Thank you Mozilla and Chrome Team, you aredoing God’s work.
Bitcoin has certainly been on a roller coaster ride over the past several months, with several people questioning “Bitcoin? Is it good? Should I buy it? The price keeps going up like magic and never crashes, at least for long anyway. Buy the dip, and HODL!”. Where Bitcoin bulls say it’s on... Continue reading → -------------------------Jan 8, 2018
A SHORT STATEMENT REGARDING ASHLEY WILLIAMS’ ABUSERS It seems there is some drama in the Rust community regarding Ashley Williams’ recent appointment to the Rust Community Team. Did Ashley violate the Node.js Code of Conduct, and is there an active censorship effort underway by the Rust Core Team to silence any dissenting voices and appoint Ashley as evil demon goddess overlord for life? It’s a Rust Conspiracy! The accusers are applauding those who have a “skeptical” view about this situation: The sheeple arewoke!.
I see things a bit differently. The people cheering on abusers and perpetuating a cycle of abuse. “Maybe if we follow her around the Internet endlessly harassing her, it will prove our point how that one thing she tweeted one time could possibly be in violation of a Code of Conduct.” There’s a word for people like that: Gamergaters. In my book, following someone around the Internet engaging in a harassment campaign forfeits... Continue reading → -------------------------Oct 17, 2017
INTRODUCING MISCREANT: A MULTI-LANGUAGE MISUSE RESISTANT ENCRYPTIONLIBRARY
For the past several months I have been hacking on not just one, but five encryption libraries in five different languages (Go, Python, Ruby, Rust, and TypeScript). Tall order, I know. And worse, these libraries implement what I believe is a novel cryptographic construction. Are you terrified yet? Yes, I’m implementing novel cryptography, in several languages at that, but I’d like to convince you it’s not as scary as it sounds. Why? Because I’m implementing algorithms originally created by a cryptographer, Phil Rogaway, whose decades of work is just starting to receive the mainstream attention it deserves. These algorithms are extremely simple and designed to be easy-to-implement. Finally, they’re all built atop otherwise standard AES modes. The library is Miscreant, and it’s available on GitHub in the form of a multi-language monorepo at: https://github.com/miscreant/miscreantTHE
...
Continue reading → -------------------------Mar 28, 2017
IT’S TIME FOR A MEMORY SAFETY INTERVENTION Memory safety won’t fix shell escaping bugs. Memory safety won’t fix logic bugs. Memory safety will not prevent an attacker who has obtained your HMAC key from forging a malicious credential that, when deserialized, can call arbitrary Ruby methods (yes, this was a real vulnerability in older versions of Rails). Memory safety will not prevent a federated identity system which uses XML-based credentials from accidentally running attacker controlled commands due to external entity processing (yes, this was a real vulnerability in certain implementations of SAML). A language which provides a memory safe model but binds to unsafe code is still vulnerable when calling intounsafe code.
Nobody disputes these things. Now that we have that out of the way… Programming in C means you are using an unsafe memory model 100% of the time. It is the programming equivalent of trying to walk a... Continue reading → -------------------------Jan 14, 2017
KEY ROTATION, USER EXPERIENCE, AND CRYPTO REPORTING WhatsApp was the subject of a recent Guardian article making claims of a “backdoor” stemming from a “bug” in the way WhatsApp handles key rotations for users. The problem? WhatsApp will automatically transmit messages after the recipient’s key has changed without first asking the sender to confirm the new key is genuine. Far from being a “bug” or “backdoor” (a claim so wrong I am sure hoping the original author of the story Samuel Gibbs will issue a retraction), handling key rotation seamlessly is a difficult problem with a long-storied history, along with many attempts to surface such information to the user in order to ask them to make a security decision, such as in the SSH screenshot above. Clearly an in-person exchange of key fingerprints is the most secure option for establishing a secure channel, but is inconvenient, often impractical, and doesn’t provide a good means for... Continue reading → -------------------------Nov 22, 2016
4 FATAL FLAWS IN DETERMINISTIC PASSWORD MANAGERS Wouldn’t it be nice if your password manager didn’t need a database? Instead of synchronizing a password vault between your devices, you could use the magic of cryptography to magically transform a master password into a unique password for each site. There have been a numerous and ever growing implementations of this idea. Much of the marketing material for these tools talks about how using a deterministic scheme allows “sync-free” operation, is “more secure” than a password vault, and often that it’s a newer idea than encrypted password vaults. In this post, I will argue that you can’t practically provide “sync-free” operation without making your password manager unusable, how using a deterministic scheme harms security, and how it’s actually an old idea which never caught on for good reasons. Deterministic password derivation schemes date back to at least 2003: Stanford PwdHash and... Continue reading →Next →
* @bascule
Svbtle
TONY ARCIERI
Svbtle Terms •
Privacy • PromiseDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0