Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://isdesign.info
Are you over 18 and want to see adult content?

A complete backup of https://nodle.io
Are you over 18 and want to see adult content?

A complete backup of https://zodiacfire.com
Are you over 18 and want to see adult content?

A complete backup of https://ifn.news
Are you over 18 and want to see adult content?
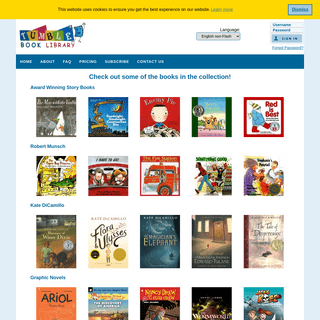
A complete backup of https://tumblebooklibrary.com
Are you over 18 and want to see adult content?

A complete backup of https://onepress.pl
Are you over 18 and want to see adult content?

A complete backup of https://marinerwealthadvisors.com
Are you over 18 and want to see adult content?

A complete backup of https://resmedjournal.com
Are you over 18 and want to see adult content?

A complete backup of https://taiwangun.com
Are you over 18 and want to see adult content?

A complete backup of https://thepaystubs.com
Are you over 18 and want to see adult content?

A complete backup of https://ruhrgebietssprache.de
Are you over 18 and want to see adult content?
A complete backup of https://purcari.wine
Are you over 18 and want to see adult content?
Favourite Annotations
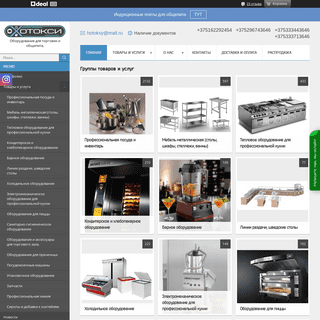
A complete backup of xn--90aijvht9b.xn--90ais
Are you over 18 and want to see adult content?
A complete backup of watchputlocker.net
Are you over 18 and want to see adult content?

A complete backup of high-octane-pictures.myshopify.com
Are you over 18 and want to see adult content?
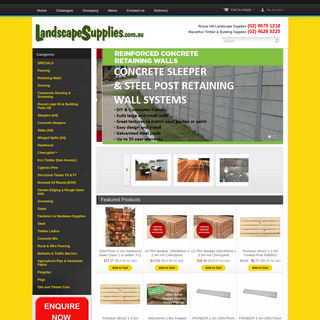
A complete backup of landscapesupplies.com.au
Are you over 18 and want to see adult content?
Text
ZAKIR DURUMERIC
I am an Assistant Professor of Computer Science at Stanford University, where my research broadly focuses on security, networking, and Internet measurement.I am interested in building systems to collect Internet data at scale and using data to better understand and improve user security and privacy as well as to curb online abuse. WHAT’S IN A NAME? EXPLORING CA CERTIFICATE CONTROL What’s in a Name? Exploring CA Certificate Control Zane Ma� Joshua Mason† Manos Antonakakis‡ Zakir Durumeric§ Michael Bailey† ‡Georgia Institute of Technology §Stanford University †University of Illinois at Urbana-Champaign Abstract TLS clients rely on a supporting PKI in which certificate authorities (CAs)—trusted organizations—validate and cryp- ALL THINGS CONSIDERED: AN ANALYSIS OF IOT DEVICES ON HOME All Things Considered: An Analysis of IoT Devices on Home Networks Deepak Kumar‡ Kelly Shen† Benton Case† Deepali Garg/ Galina Alperovich/ Dmitry Kuznetsov/ Rajarshi Gupta/ Zakir Durumeric� †Stanford University /Avast Software ‡University of Illinois Urbana-Champaign Abstract In this paper, we provide the first large-scale empirical anal- ON THE ORIGIN OF SCANNING: THE IMPACT OF LOCATION ON On the Origin of Scanning: The Impact of Location on Internet-Wide Scans Gerry Wan Stanford University Liz Izhikevich Stanford UniversityDavid Adrian
MANAGING ACTIVE DIRECTORY WITH PYTHON OPENSSL CERTIFICATE PARSING SECURITY CHALLENGES IN AN INCREASINGLY TANGLED WEB Security Challenges in an Increasingly Tangled Web Deepak Kumar� Zane Ma† Zakir Durumeric‡† Ariana Mirian‡ Joshua Mason‡ J. Alex Halderman‡ Michael Bailey† †University of Illinois, Urbana Champaign ‡University of Michigan {dkumar11, zanema2, joshm, mdbailey}@illinois.edu {zakir, amirian, jhalderm}@umich.edu TARGET GENERATION FOR INTERNET-WIDE IPV6 SCANNING Target Generation for Internet-wide IPv6 Scanning Austin Murdock1,2, Frank Li1,2, Paul Bramsen1, Zakir Durumeric2, Vern Paxson1,2 {austinmurdock, frankli, paulbramsen TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- FINDING CROSS DATABASE DEPENDENCIES Finding Cross Database Dependencies. Zakir Durumeric | June 07, 2011. We recently went through a database consolidation project for a legacy application and needed to find object dependencies across multipledatabases.
ZAKIR DURUMERIC
I am an Assistant Professor of Computer Science at Stanford University, where my research broadly focuses on security, networking, and Internet measurement.I am interested in building systems to collect Internet data at scale and using data to better understand and improve user security and privacy as well as to curb online abuse. WHAT’S IN A NAME? EXPLORING CA CERTIFICATE CONTROL What’s in a Name? Exploring CA Certificate Control Zane Ma� Joshua Mason† Manos Antonakakis‡ Zakir Durumeric§ Michael Bailey† ‡Georgia Institute of Technology §Stanford University †University of Illinois at Urbana-Champaign Abstract TLS clients rely on a supporting PKI in which certificate authorities (CAs)—trusted organizations—validate and cryp- ALL THINGS CONSIDERED: AN ANALYSIS OF IOT DEVICES ON HOME All Things Considered: An Analysis of IoT Devices on Home Networks Deepak Kumar‡ Kelly Shen† Benton Case† Deepali Garg/ Galina Alperovich/ Dmitry Kuznetsov/ Rajarshi Gupta/ Zakir Durumeric� †Stanford University /Avast Software ‡University of Illinois Urbana-Champaign Abstract In this paper, we provide the first large-scale empirical anal- ON THE ORIGIN OF SCANNING: THE IMPACT OF LOCATION ON On the Origin of Scanning: The Impact of Location on Internet-Wide Scans Gerry Wan Stanford University Liz Izhikevich Stanford UniversityDavid Adrian
MANAGING ACTIVE DIRECTORY WITH PYTHON OPENSSL CERTIFICATE PARSING SECURITY CHALLENGES IN AN INCREASINGLY TANGLED WEB Security Challenges in an Increasingly Tangled Web Deepak Kumar� Zane Ma† Zakir Durumeric‡† Ariana Mirian‡ Joshua Mason‡ J. Alex Halderman‡ Michael Bailey† †University of Illinois, Urbana Champaign ‡University of Michigan {dkumar11, zanema2, joshm, mdbailey}@illinois.edu {zakir, amirian, jhalderm}@umich.edu TARGET GENERATION FOR INTERNET-WIDE IPV6 SCANNING Target Generation for Internet-wide IPv6 Scanning Austin Murdock1,2, Frank Li1,2, Paul Bramsen1, Zakir Durumeric2, Vern Paxson1,2 {austinmurdock, frankli, paulbramsen TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- FINDING CROSS DATABASE DEPENDENCIES Finding Cross Database Dependencies. Zakir Durumeric | June 07, 2011. We recently went through a database consolidation project for a legacy application and needed to find object dependencies across multipledatabases.
PUBLICATIONS -- ZAKIR DURUMERIC On the Origin of Scanning: The Impact of Location on Internet-Wide Scans. Gerry Wan, Liz Izhikevich, David Adrian, Katsunari Yoshioka, Ralph Holz, Christian Rossow, Zakir Durumeric FTP: THE FORGOTTEN CLOUD FTP: The Forgotten Cloud Drew Springall Zakir Durumeric J. Alex Halderman University of Michigan {aaspring, zakir, jhalderm}@umich.edu Abstract—Once pervasive, the File Transfer Protocol (FTP) TARGET GENERATION FOR INTERNET-WIDE IPV6 SCANNING Target Generation for Internet-wide IPv6 Scanning Austin Murdock1,2, Frank Li1,2, Paul Bramsen1, Zakir Durumeric2, Vern Paxson1,2 {austinmurdock, frankli, paulbramsen AN INTERNET-WIDE VIEW OF ICS DEVICES An Internet-Wide View of ICS Devices Ariana Mirian† Zane Ma‡ David Adrian† Matthew Tischer‡ Thasphon Chuenchujit‡ Tim Yardley‡ Robin Berthier‡ Joshua Mason‡ Zakir Durumeric†‡ J. Alex Halderman† Michael Bailey‡ † University of Michigan ‡ University of Illinois at Urbana-Champaign Abstract—Industrial control systems have become ubiquitous, LZR: IDENTIFYING UNEXPECTED INTERNET SERVICES LZR: Identifying Unexpected Internet Services Liz Izhikevich Stanford University Renata Teixeira Inria, Paris Zakir Durumeric StanfordUniversity Abstract
USERS REALLY DO PLUG IN USB DRIVES THEY FIND 1 Users Really Do Plug in USB Drives They Find Matthew Tischer yZakir Durumericzy Sam Foster Sunny Duan Alec Mori yElie Bursztein3 Michael Bailey yUniversity of Illinois, Urbana Champaign zUniversity of Michigan 3 Google, Inc. {tischer1, sfoster3, syduan2, ajmori2, mdbailey}@illinois.edu zakir@umich.edu elieb@google.com SOK: HATE, HARASSMENT, AND THE CHANGING LANDSCAPE OF SoK: Hate, Harassment, and the Changing Landscape of Online Abuse Kurt Thomas, Devdatta Akhawe5, Michael Baileyx, Dan Boneh , Elie Bursztein, Sunny Consolvo, Nicola Dell , Zakir Durumeric , Patrick Gage Kelley, Deepak Kumarx, Damon McCoyz, Sarah Meiklejohn4, Thomas Ristenpart , Gianluca Stringhini Google Boston University Cornell Tech 5Figma, Inc. zNew York University UNDERSTANDING THE MIRAI BOTNET Understanding the Mirai Botnet Manos Antonakakis Tim April‡ Michael Bailey† Matthew Bernhard/ Elie Bursztein Jaime Cochran. Zakir Durumeric/ J. Alex Halderman/ Luca Invernizzi Michalis Kallitsis§ Deepak Kumar† Chaz Lever Zane Ma† Joshua Mason† Damian Menscher Chad Seaman‡ Nick Sullivan. Kurt Thomas Yi Zhou† ‡Akamai Technologies.Cloudflare Georgia Institute of Technology Google DOI:10.1145/3292035 IMPERFECT FORWARD SECRECY: HOW 106 COMMUNICATIONS OF THE ACM | JANUARY 2019 | VOL. 62 | NO. 1 research highlights Imperfect Forward Secrecy: How DOI:10.1145/3292035 Diffie-Hellman Fails in Practice By David Adrian, Karthikeyan Bhargavan, Zakir Durumeric, Pierrick Gaudry, Matthew Green, J. AlexHalderman,
˜ E DANGER OF USB DRIVES computer. / / computer. / / computer. / /. / /. / /ZAKIR DURUMERIC
Students and Teaching. I lead the Stanford Empirical Security Research Group where I advise several Ph.D. students and postdoctoral scholars: Liz Izhikevich , Gerry Wan , Kimberly Ruth , Hans Hanley , Catherine Han, and Deepak Kumar. I teach CS155 Computer and Network Security (2019-2021), CS356 Topics in Systems and Network Security (2018-2021 WHAT’S IN A NAME? EXPLORING CA CERTIFICATE CONTROL What’s in a Name? Exploring CA Certificate Control Zane Ma� Joshua Mason† Manos Antonakakis‡ Zakir Durumeric§ Michael Bailey† ‡Georgia Institute of Technology §Stanford University †University of Illinois at Urbana-Champaign Abstract TLS clients rely on a supporting PKI in which certificate authorities (CAs)—trusted organizations—validate and cryp- ALL THINGS CONSIDERED: AN ANALYSIS OF IOT DEVICES ON HOME All Things Considered: An Analysis of IoT Devices on Home Networks Deepak Kumar‡ Kelly Shen† Benton Case† Deepali Garg/ Galina Alperovich/ Dmitry Kuznetsov/ Rajarshi Gupta/ Zakir Durumeric� †Stanford University /Avast Software ‡University of Illinois Urbana-Champaign Abstract In this paper, we provide the first large-scale empirical anal- AN INTERNET-WIDE VIEW OF ICS DEVICES An Internet-Wide View of ICS Devices Ariana Mirian† Zane Ma‡ David Adrian† Matthew Tischer‡ Thasphon Chuenchujit‡ Tim Yardley‡ Robin Berthier‡ Joshua Mason‡ Zakir Durumeric†‡ J. Alex Halderman† Michael Bailey‡ † University of Michigan ‡ University of Illinois at Urbana-Champaign Abstract—Industrial control systems have become ubiquitous, TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute USERS REALLY DO PLUG IN USB DRIVES THEY FIND 1 Users Really Do Plug in USB Drives They Find Matthew Tischer yZakir Durumericzy Sam Foster Sunny Duan Alec Mori yElie Bursztein3 Michael Bailey yUniversity of Illinois, Urbana Champaign zUniversity of Michigan 3 Google, Inc. {tischer1, sfoster3, syduan2, ajmori2, mdbailey}@illinois.edu zakir@umich.edu elieb@google.com TARGET GENERATION FOR INTERNET-WIDE IPV6 SCANNING Target Generation for Internet-wide IPv6 Scanning Austin Murdock1,2, Frank Li1,2, Paul Bramsen1, Zakir Durumeric2, Vern Paxson1,2 {austinmurdock, frankli, paulbramsen FTP: THE FORGOTTEN CLOUD FTP: The Forgotten Cloud Drew Springall Zakir Durumeric J. Alex Halderman University of Michigan {aaspring, zakir, jhalderm}@umich.edu Abstract—Once pervasive, the File Transfer Protocol (FTP) YOU’VE GOT VULNERABILITY: EXPLORING EFFECTIVE Dataset Hosts WHOIS Abuse Contacts Hosts with WHOIS Contacts ICS 45,770 2,563 79.7% IPv6 180,611 3,536 99.8% Ampl. 83,846 5.960 92.4% Table 1: Vulnerable Hosts—We notified network oper-ZAKIR DURUMERIC
Students and Teaching. I lead the Stanford Empirical Security Research Group where I advise several Ph.D. students and postdoctoral scholars: Liz Izhikevich , Gerry Wan , Kimberly Ruth , Hans Hanley , Catherine Han, and Deepak Kumar. I teach CS155 Computer and Network Security (2019-2021), CS356 Topics in Systems and Network Security (2018-2021 WHAT’S IN A NAME? EXPLORING CA CERTIFICATE CONTROL What’s in a Name? Exploring CA Certificate Control Zane Ma� Joshua Mason† Manos Antonakakis‡ Zakir Durumeric§ Michael Bailey† ‡Georgia Institute of Technology §Stanford University †University of Illinois at Urbana-Champaign Abstract TLS clients rely on a supporting PKI in which certificate authorities (CAs)—trusted organizations—validate and cryp- ALL THINGS CONSIDERED: AN ANALYSIS OF IOT DEVICES ON HOME All Things Considered: An Analysis of IoT Devices on Home Networks Deepak Kumar‡ Kelly Shen† Benton Case† Deepali Garg/ Galina Alperovich/ Dmitry Kuznetsov/ Rajarshi Gupta/ Zakir Durumeric� †Stanford University /Avast Software ‡University of Illinois Urbana-Champaign Abstract In this paper, we provide the first large-scale empirical anal- AN INTERNET-WIDE VIEW OF ICS DEVICES An Internet-Wide View of ICS Devices Ariana Mirian† Zane Ma‡ David Adrian† Matthew Tischer‡ Thasphon Chuenchujit‡ Tim Yardley‡ Robin Berthier‡ Joshua Mason‡ Zakir Durumeric†‡ J. Alex Halderman† Michael Bailey‡ † University of Michigan ‡ University of Illinois at Urbana-Champaign Abstract—Industrial control systems have become ubiquitous, TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute USERS REALLY DO PLUG IN USB DRIVES THEY FIND 1 Users Really Do Plug in USB Drives They Find Matthew Tischer yZakir Durumericzy Sam Foster Sunny Duan Alec Mori yElie Bursztein3 Michael Bailey yUniversity of Illinois, Urbana Champaign zUniversity of Michigan 3 Google, Inc. {tischer1, sfoster3, syduan2, ajmori2, mdbailey}@illinois.edu zakir@umich.edu elieb@google.com TARGET GENERATION FOR INTERNET-WIDE IPV6 SCANNING Target Generation for Internet-wide IPv6 Scanning Austin Murdock1,2, Frank Li1,2, Paul Bramsen1, Zakir Durumeric2, Vern Paxson1,2 {austinmurdock, frankli, paulbramsen FTP: THE FORGOTTEN CLOUD FTP: The Forgotten Cloud Drew Springall Zakir Durumeric J. Alex Halderman University of Michigan {aaspring, zakir, jhalderm}@umich.edu Abstract—Once pervasive, the File Transfer Protocol (FTP) YOU’VE GOT VULNERABILITY: EXPLORING EFFECTIVE Dataset Hosts WHOIS Abuse Contacts Hosts with WHOIS Contacts ICS 45,770 2,563 79.7% IPv6 180,611 3,536 99.8% Ampl. 83,846 5.960 92.4% Table 1: Vulnerable Hosts—We notified network oper- PUBLICATIONS -- ZAKIR DURUMERIC Outsmarting Proctors with Smartwatches: A Case Study on Wearable Computing Security. Alex Migicovsky, Zakir Durumeric, Jeff Ringenberg, and J. Alex Halderman. Financial Cryptography and Data Security (Financial Crypto), March 2014. USERS REALLY DO PLUG IN USB DRIVES THEY FIND 1 Users Really Do Plug in USB Drives They Find Matthew Tischer yZakir Durumericzy Sam Foster Sunny Duan Alec Mori yElie Bursztein3 Michael Bailey yUniversity of Illinois, Urbana Champaign zUniversity of Michigan 3 Google, Inc. {tischer1, sfoster3, syduan2, ajmori2, mdbailey}@illinois.edu zakir@umich.edu elieb@google.com UNDERSTANDING THE MIRAI BOTNET Understanding the Mirai Botnet Manos Antonakakis Tim April‡ Michael Bailey† Matthew Bernhard/ Elie Bursztein Jaime Cochran. Zakir Durumeric/ J. Alex Halderman/ Luca Invernizzi Michalis Kallitsis§ Deepak Kumar† Chaz Lever Zane Ma† Joshua Mason† Damian Menscher Chad Seaman‡ Nick Sullivan. Kurt Thomas Yi Zhou† ‡Akamai Technologies.Cloudflare Georgia Institute of Technology Google MANAGING ACTIVE DIRECTORY WITH PYTHON Zakir Durumeric | March 27, 2019. I have recently received a good number of questions regarding the pyad library and I wanted to provide a brief introduction. My intent for this article is to provide a brief tutorial as to how to perform basic operations with pyad, but to also provide detail on how the library operates and the backend for users who want to directly interact with ADSI through NEITHER SNOW NOR RAIN NOR MITMAN EMPIRICAL ANALYSIS OF Neither Snow Nor Rain Nor MITM An Empirical Analysis of Email Delivery Security Zakir Durumeric† David Adrian† Ariana Mirian† James Kasten† Elie Bursztein‡ Nicolas Lidzborski‡ Kurt Thomas‡ Vijay Eranti‡ Michael Bailey§ J. Alex Halderman† † University of Michigan ‡ Google, Inc. § University of Illinois, Urbana Champaign {zakir, davadria, amirian, jdkasten, jhalderm SECURITY CHALLENGES IN AN INCREASINGLY TANGLED WEB Security Challenges in an Increasingly Tangled Web Deepak Kumar� Zane Ma† Zakir Durumeric‡† Ariana Mirian‡ Joshua Mason‡ J. Alex Halderman‡ Michael Bailey† †University of Illinois, Urbana Champaign ‡University of Michigan {dkumar11, zanema2, joshm, mdbailey}@illinois.edu {zakir, amirian, jhalderm}@umich.edu LZR: IDENTIFYING UNEXPECTED INTERNET SERVICES LZR: Identifying Unexpected Internet Services Liz Izhikevich Stanford University Renata Teixeira Inria, Paris Zakir Durumeric StanfordUniversity Abstract
SOK: HATE, HARASSMENT, AND THE CHANGING LANDSCAPE OF SoK: Hate, Harassment, and the Changing Landscape of Online Abuse Kurt Thomas, Devdatta Akhawe5, Michael Baileyx, Dan Boneh , Elie Bursztein, Sunny Consolvo, Nicola Dell , Zakir Durumeric , Patrick Gage Kelley, Deepak Kumarx, Damon McCoyz, Sarah Meiklejohn4, Thomas Ristenpart , Gianluca Stringhini Google Boston University Cornell Tech 5Figma, Inc. zNew York University ˜ E DANGER OF USB DRIVES computer. / / computer. / / computer. / /. / /. / / FINDING CROSS DATABASE DEPENDENCIES Finding Cross Database Dependencies. Zakir Durumeric | June 07, 2011. We recently went through a database consolidation project for a legacy application and needed to find object dependencies across multipledatabases.
ZAKIR DURUMERIC
ASSISTANT PROFESSOR
STANFORD COMPUTER SCIENCE ZAKIR@CS.STANFORD.EDU(650) 724-6279
PUBLICATIONS | CV | BLOG I am an Assistant Professor of Computer Science at Stanford University , where my research broadly focuses on security, networking, and Internet measurement. I am particularly interested in building systems to collect Internet data and using that data to better understand and improve user security and privacy. I'm also co-founder and Chief Scientist of Censys . STUDENTS AND TEACHING I lead the Stanford Empirical Security Research Group where I work with several students and postdoctoral scholars: Liz Izhikevich, Gerry Wan
, Kimberly Ruth , and Deepak Kumar . I teach CS155 Computer and Network Security and CS356 Topics in Systems and Network Security .SELECT PUBLICATIONS
LET'S ENCRYPT: AN AUTOMATED CERTIFICATE AUTHORITY TO ENCRYPT THEENTIRE WEB
* Josh Aas, Richard Barnes, Benton Case, Zakir Durumeric, Peter Eckersley, Alan Flores-Lopez, * J. Alex Halderman, Jacob Hoffman-Andrews, James Kasten, Eric Rescorla, Seth Schoen, Brad Warren * _ACM Conference on Computer and Communications Security_ (CCS),November 2019
TRACKING CERTIFICATE MISISSUANCE IN THE WILD * Deepak Kumar, Zhengping Wang, Matthew Hyder, Joseph Dickinson, Gabrielle Beck, David Adrian, * Joshua Mason, Zakir Durumeric, J. Alex Halderman, Michael Bailey * _IEEE Symposium on Security and Privacy_ ("Oakland"), May 2018 UNDERSTANDING THE MIRAI BOTNET * Manos Antonakakis, Tim April, Michael Bailey, Matt Bernhard, Elie Bursztein, Jaime Cochran * Zakir Durumeric, J. Alex Halderman, Luca Invernizzi, Michalis Kallitsis, Deepak Kumar, Chaz Lever, * Zane Ma, Joshua Mason, Damian Menscher, Chad Seaman, Nick Sullivan, Kurt Thomas, Yi Zhou * _USENIX Security Symposium_, August 2017 NEITHER SNOW NOR RAIN NOR MITM... AN EMPIRICAL ANALYSIS OF EMAILDELIVERY SECURITY
* Zakir Durumeric, David Adrian, Ariana Mirian, James Kasten, Kurt Thomas, Vijay Eranti, * Nicholas Lidzborski, Elie Bursztein, Michael Bailey, and J. AlexHalderman
* _ACM Internet Measurement Conference_ (IMC), October 2015 * IETF APPLIED NETWORKING RESEARCH PRIZE (ANRP) IMPERFECT FORWARD SECRECY: HOW DIFFIE-HELLMAN FAILS IN PRACTICE * David Adrian, Karthikeyan Bhargavan, Zakir Durumeric, Pierrick Gaudry, Matthew Green, * J. Alex Halderman, Nadia Heninger, Drew Springall, Emmanuel Thomé, Luke Valenta, * Benjamin VanderSloot, Eric Wustrow, Santiago Zanella-Beguelin, andPaul Zimmermann
* _ACM Computer and Communications Security_ (CCS), October 2015* BEST PAPER AWARD
THE MATTER OF HEARTBLEED * Zakir Durumeric, Frank Li, James Kasten, Johanna Amann, Jethro Beekman, Mathias Payer, * Nicolas Weaver, David Adrian, Vern Paxson, Michael Bailey, and J.Alex Halderman
* _ACM Internet Measurement Conference_ (IMC), November 2014* BEST PAPER AWARD
ZMAP: FAST INTERNET-WIDE SCANNING AND ITS SECURITY APPLICATIONS * Zakir Durumeric, Eric Wustrow, and J. Alex Halderman * _USENIX Security Symposium_, August 2013 MINING YOUR PS AND QS: DETECTION OF WIDESPREAD WEAK KEYS IN NETWORKDEVICES
* Nadia Heninger, Zakir Durumeric, Eric Wustrow, and J. AlexHalderman
* _USENIX Security Symposium_, August 2012* BEST PAPER AWARD
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0